

DarkReading
US AI Experts Targeted in SugarGh0st RAT Campaign
Researchers believe the attacker is likely China-affiliated, since a previous version of the malware was used by a China nation-state attack group.


DarkReading
Researchers believe the attacker is likely China-affiliated, since a previous version of the malware was used by a China nation-state attack group.


SecurityWeek
Network infrastructure as-a-service Alkira has raised $100 million in a Series C funding round led by Tiger Global Management.


DarkReading
In a first-ever move, the commission's enforcement bureau has high hopes that official classification will allow law enforcement partners to better combat these kinds of threats.


Bleeping Computer
The North Korean hacker group Kimsuki has been using trojanized software packages to deliver a new Linux malware called Gomir in cyberespionage campaigns against targets in South Korea.


Bleeping Computer
The North Korean hacker group Kimsuki has been using a new Linux malware called Gomir that is a version of the GoBear backdoor delivered via trojanized software installers.


The Cyber Express
Researchers recently uncovered two new backdoors implanted within the infrastructure of a European Ministry of Foreign Affairs (MFA) and its

%20(1)%20(1).webp)
Cyber Security News
A newly disclosed vulnerability, identified as CVE-2024-22026, has been found in Ivanti EPMM, formerly known as MobileIron Core.


Infosecurity News
UK organizations are less likely than their European peers to have known exploited bugs but take longer to fix them

%20(1).webp)
Cyber Security News
Earth Hundun, a notable Asia-Pacific malware organization, uses Waterbear and Deuterbear, first encountered Deuterbear.


Trend Micro
This report describes how Waterbear and Deuterbear — two of the tools in Earth Hundun's arsenal — operate, based on a campaign from 2024.


SecurityWeek
Russian-speaking threat actors are caught abusing a GitHub profile to distribute information stealers posing as legitimate software.

.webp)
Cyber Security News
The well-known advanced persistent threat (APT) group Turla, which is based in Russia, is said to be going after the European Ministry.


The Hacker News
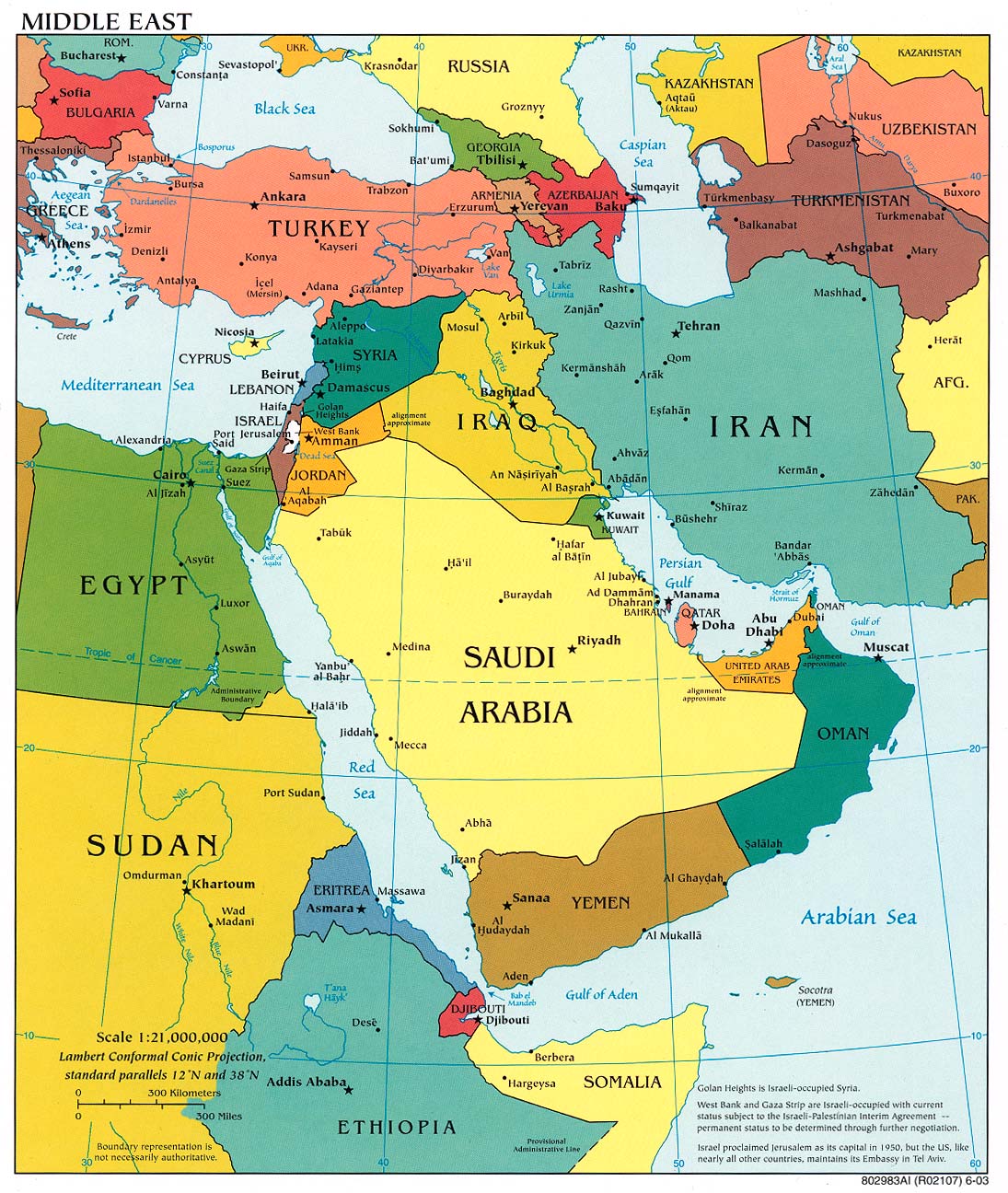
Two new backdoors, LunarWeb and LunarMail, have targeted a European ministry of foreign affairs and its diplomatic missions in the Middle East


Infosecurity News
Trend Micro research claims CISOs are often ignored or dismissed as “nagging” by their board

SecurityWeek
Several ICS vendors have released advisories on Tuesday to inform customers about vulnerabilities found in their products.


The Cyber Express
Cyble Research and Intelligence Labs (CRIL) researchers have uncovered a new SideCopy campaign. The threat actor group has previously been


CSO
CISA advisory includes indicators of compromise and TTPs that can be used for threat hunting.


The Record
Researchers with cybersecurity company ESET have labeled two new pieces of suspected Russian malware as LunarWeb and LunarMail.


SecurityWeek
Threat actors are using DNS tunneling to track victims’ interaction with spam and to scan network infrastructures.


Infosecurity News
Palo Alto Networks warns threat actors are using DNS tunneling techniques to probe for network vulnerabilities


Cyber Security News
Recent email campaigns distribute DanaBot malware through two document types: those using equation editor exploits and those containing


SecurityWeek
The FCC has issued a public notice on robocall scammer group ‘Royal Tiger’, the first designated threat actor.


Infosecurity News
In a first, the FCC has designated “Royal Tiger” as a malicious robocall threat group

.webp)
Cyber Security News
According to the FCC, the Royal Tiger Group and the people who work with it are a C-Communications Information Services Threat (C-CIST).


SC Magazine
The FCC has smacked the group with a first-of-its-kind threat classification for its persistent, fraudulent activity.


Bleeping Computer
The Federal Communications Commission (FCC) has named its first officially designated robocall threat actor 'Royal Tiger,' a move aiming to help international partners and law enforcement more easily track individuals and entities behind repeat robocall campaigns.


SecurityWeek
Weakening liberal democracies and weakening the NATO alliance are conjoined in the hybrid war that Russia is conducting against Ukraine.

The Record
A robocall group labeled Royal Tiger is the first classified as a Consumer Communications Information Services Threat (C-CIST) by the FCC.


Krebs on Security
Last week, the United States joined the U.K. and Australia in sanctioning and charging a Russian man named Dmitry Yuryevich Khoroshev as the leader of the infamous LockBit ransomware group. LockBit's leader "LockBitSupp" claims the feds named the wrong guy,…

Ars Technica
Exploit code for critical "use-after-free" bug is circulating in the wild.


The Hacker News
North Korean hackers have unleashed a new Golang malware called "Durian" in targeted attacks against South Korean crypto firms.


Cyber Security News
Hackers take advantage of sponsored Google Ads as they provide an excellent chance to quickly reach a large audience.


DarkReading
The latest round of investment prices the fast-growing cloud native application protection platform (CNAPP) at $12 billion with a simple mandate: Grow quickly through acquisition.


Infosecurity News
The award recognises Khan's outstanding contributions to the field and his role in shaping the cybersecurity industry


Infosecurity News
US government officials discussed plans on how to incentivize security by design principles in the software manufacturing process during RSA


Latest Hacking News
Heads up, Android users! If you’re using a VPN, it’s time to meddle with your device settings to deal with the DNS leak vulnerability that sneakily affects Android devices. This vulnerability keeps leaking the DNS


Latest Hacking News
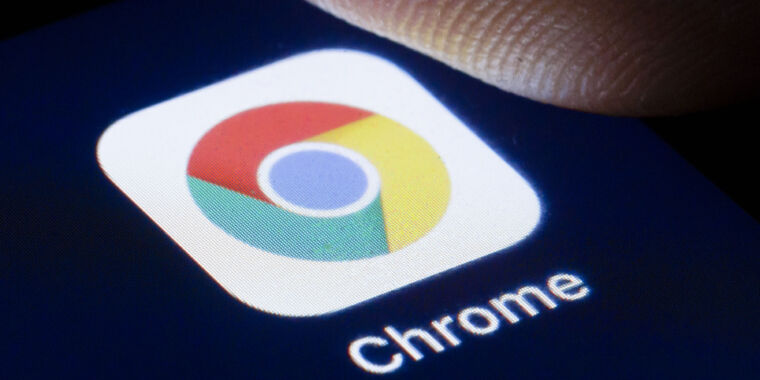
Android mobile users must stay wary of new malware, “Brokewell,” ready to break their banks. As observed, Brokewell is a potent banking trojan that lures victims into downloading it by faking Chrome browser updates. Brokewell Malware


The Hacker News
APT42, an Iranian state-backed hacking group, is leveling up its social engineering tactics. They're posing as journalists and event organizers to bui


SecurityWeek
Hundreds of companies are showcasing their products and services this week at the 2024 edition of the RSA Conference in San Francisco.


SecurityWeek
Iranian state-sponsored group APT42 is targeting NGOs, government, and intergovernmental organizations with two new backdoors.

.png)
Cyber Security News
However, a significant communication gap within organizations is increasingly a vulnerability, exposing to sophisticated cyber threats.


CyberSecurity Dive
Do you know what’s in your code? These five considerations should help you drive your security activities and identify weak points in your software supply chain.


CyberSecurity Dive
Do you know what’s in your code? These 5 considerations should help you drive your security activities and identify weak points in your software supply chain.


Bleeping Computer
The Iranian state-backed threat actor tracked as APT42 is employing social engineering attacks, including posing as journalists, to breach corporate networks and cloud environments of Western and Middle Eastern targets.


The Hacker News
Czechia and Germany reveal they were targets of a massive cyber espionage campaign by Russia-linked APT28 hacker group.


Cyber Security News
Android's operating system has identified a critical vulnerability that allows DNS traffic to leak during VPN server switches, potentially exposing users' internet activity to cybercriminals.


Bleeping Computer
A Mullvad VPN user has discovered that Android devices leak DNS queries when switching VPN servers even though the "Always-on VPN" feature was enabled with the "Block connections without VPN" option.


Bleeping Computer
A Mullvad VPN user has discovered that Android devices leak DNS queries when switching VPN servers even though the "Always-on VPN" feature was enabled with the "Block connections without VPN" option.


Ars Technica
Andrej Karpathy muses about sending a LLM binary that could "wake up" and answer questions.

Security Affairs
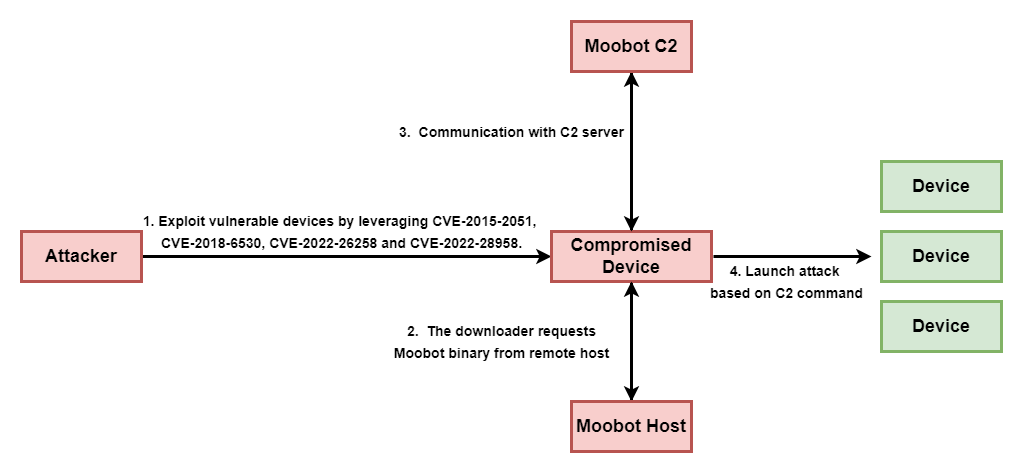
The Ubiquiti EdgeRouter botnet is still used by Russia-linked group APT28 and cybercriminals organizations.


The Hacker News
Nation-state hackers have a new trick - turning Microsoft's own cloud services into secret command centers to launch attacks undetected.


SecurityWeek
A botnet dismantled in January and used by Russia-linked APT28 consisted of more than just Ubiquiti Edge OS routers.


SecurityWeek
Horizon3.ai's AISaaS-based, AI-assisted penetration service allows proactive defensive action against exploitation of new vulnerabilities.


Bleeping Computer
In our increasingly mobile world, you shouldn't be chained to a power port. The 25,000mAh capacity power bank keeps you going for $199.97, $119 off the $319 MSRP.


Infosecurity News
Dynatrace research claims global CISOs are concerned AI is driving advanced app security threats and poor developer practices

.webp)
Cyber Security News
A new variant of the notorious Adload malware has been discovered to bypass the latest updates to Apple's built-in antivirus, XProtect.


CSO
Mandiant observed several malicious campaigns with threat actors impersonating journalists and harvesting the victim’s cloud environment credentials.

Ars Technica
How and why nation-state hackers and cybercriminals coexist in the same router botnet.


SecurityWeek
Chinese cybersecurity firm QAX XLab uncovered an Android trojan that hides its command-and-control server behind compromised WordPress sites.


Trend Micro
This blog entry aims to highlight the dangers of internet-facing routers and elaborate on Pawn Storm's exploitation of EdgeRouters, complementing the FBI's advisory from February 27, 2024.


Cyber Security News
Google has introduced Gemini 1.5 Pro for malware analysis, an advanced AI tool capable of processing up to 1 million tokens.


CSO
In the written testimony before the House Energy and Commerce Committee, CEO Andrew Witty said after gaining access, the threat actor moved laterally within the systems using sophisticated methods and exfiltrated data.


SecurityWeek
An analysis conducted by Honeywell shows that much of the USB-borne malware targeting industrial organizations can still cause OT disruption.

The DFIR Report
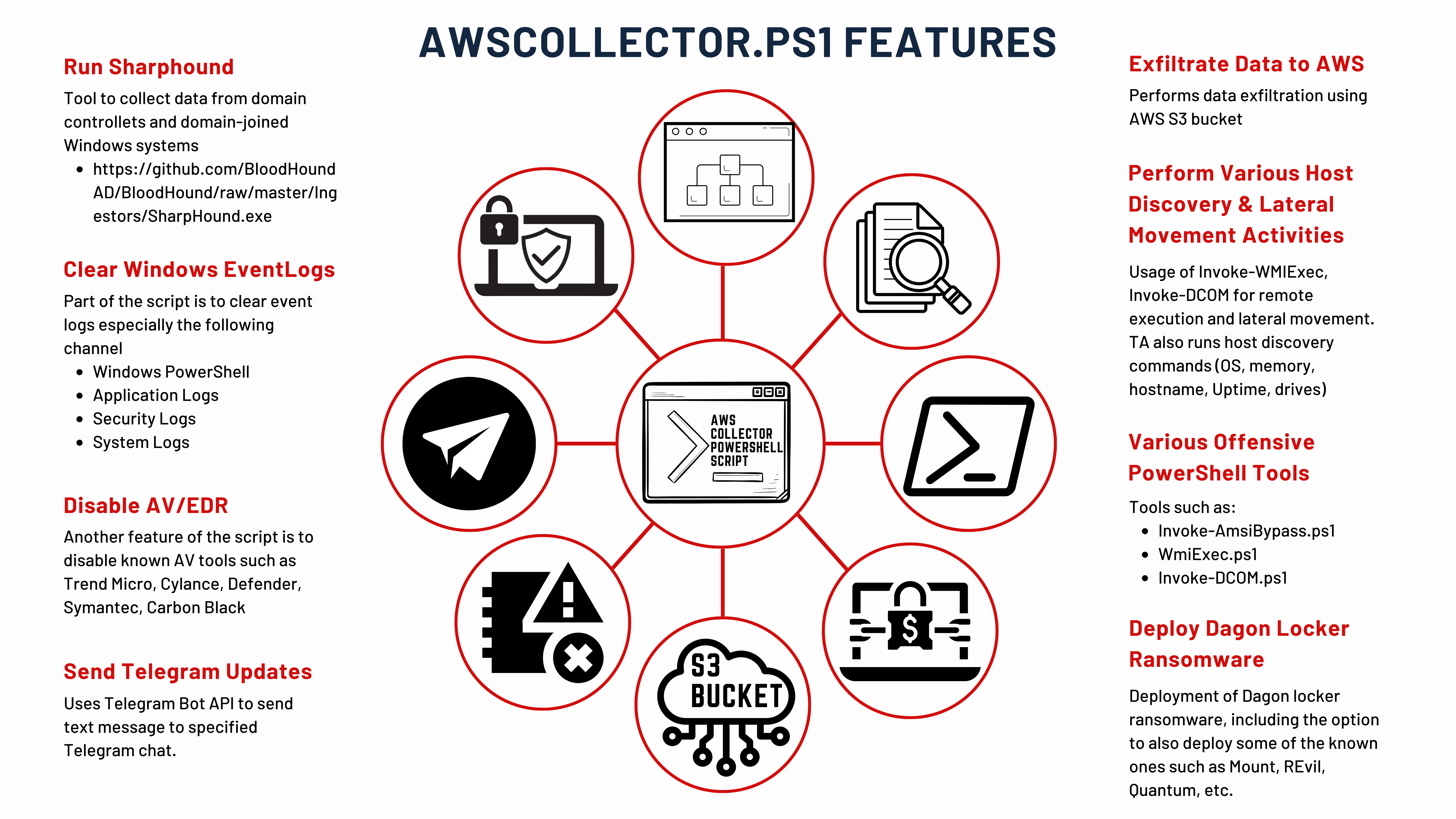
Key Takeaways In August 2023, we observed an intrusion that started with a phishing campaign using PrometheusTDS to distribute IcedID. IcedID dropped and executed a Cobalt Strike beacon, which was … Read More

Security Affairs
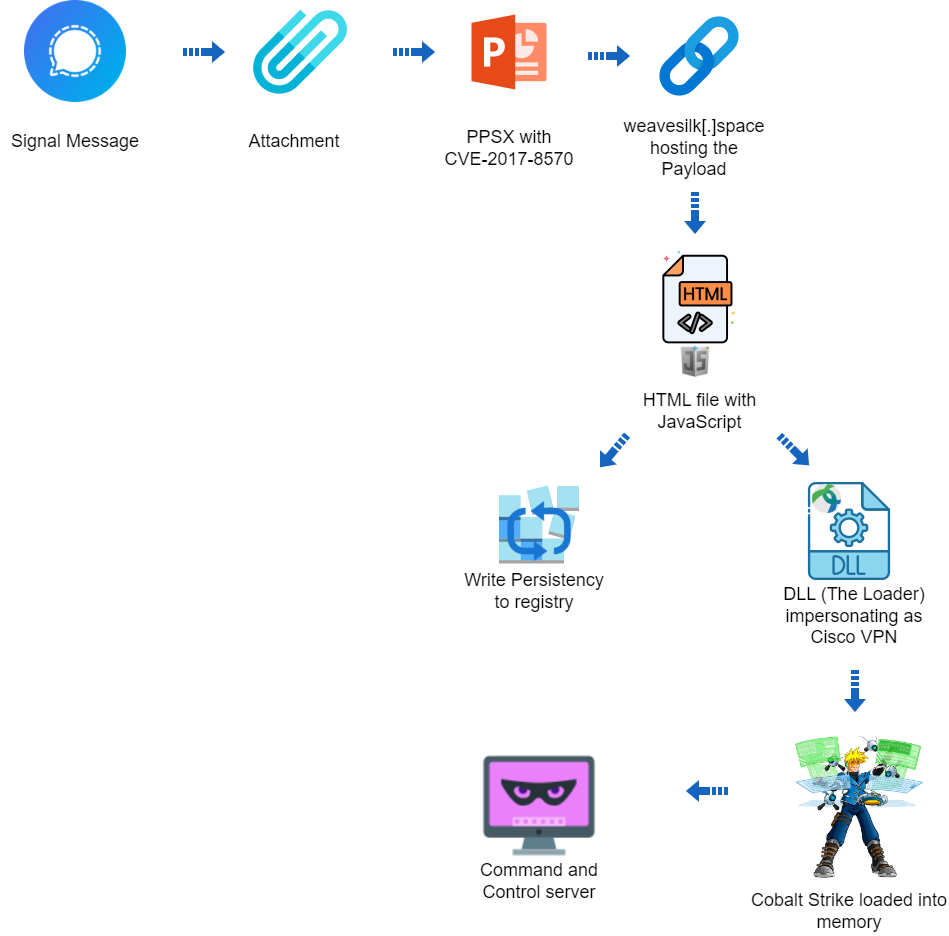
A hacking campaign targeted Ukraine exploiting a seven-year-old vulnerability in Microsoft Office to deliver Cobalt Strike.


The Cyber Express
CRIL Researchers observed a new android banking trojan 'Brokewell,' being distributed through a phishing site disguised as the official Chrome


The Hacker News
Cybersecurity researchers have uncovered a targeted cyber attack against Ukraine that leveraged a 7-year-old Microsoft Office flaw to deploy Cobalt St


HACKRead
A recent attack exploited vulnerabilities in systems running outdates Microsoft Office to deliver Cobalt Strike malware. Learn how to protect yourself!


SecurityWeek
A new Android trojan named Brokewell can steal user’s sensitive information and allows attackers to take over devices.

SecurityWeek
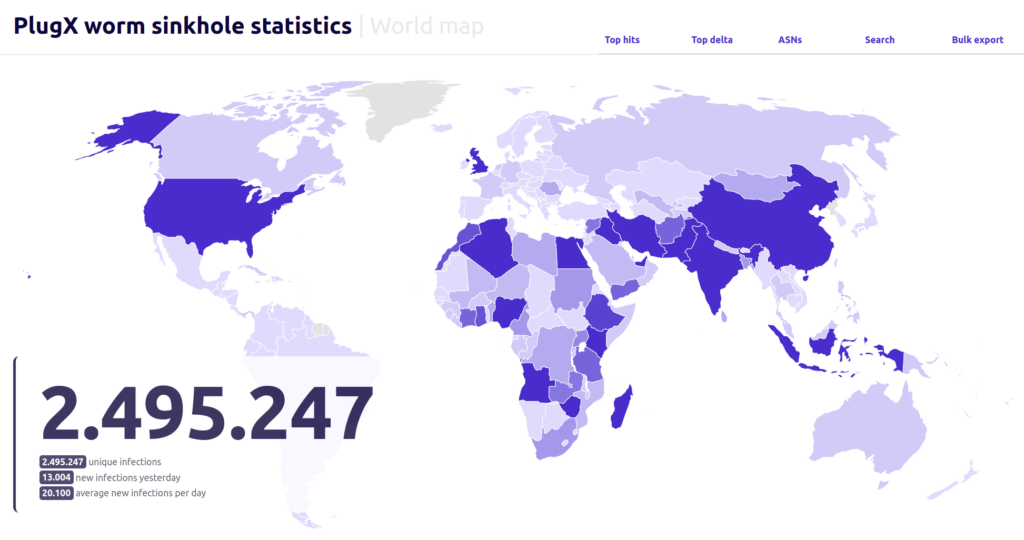
More than 90,000 unique IPs are still infected with a PlugX worm variant that spreads via infected flash drives.


SecurityWeek
Zero trust endpoint security company ThreatLocker has announced a $115 million Series D funding round that brings the total to $240 million.


Ars Technica
Panel of eight judges confronts deep-faking AI tech that may undermine legal trials.


Cyber Security News
Researchers identified a cyberattack by the Sandworm group targeting critical infrastructure in Ukraine in March 2024, which aimed to disrupt


The Hacker News
A sophisticated malware called GuptiMiner has been leveraging a flaw in eScan antivirus updates to spread backdoors and crypto miners across corporate

Trend Micro
In this blog entry, we discuss Trend Micro's contributions to an Interpol-coordinated operation to help Brazilian and Spanish law enforcement agencies analyze malware samples of the Grandoreiro banking trojan.


Ars Technica
eScan AV updates were delivered over HTTP for five years.


Bleeping Computer
The Department of State has started imposing visa restrictions on mercenary spyware makers and peddlers, prohibiting their entry into the United States, as announced earlier in February.


DarkReading
The infamous Russian threat actor has created a custom tool called GooseEgg to exploit CVE-2022-38028 in cyberespionage attacks against targets in Ukraine, Western Europe, and North America.


SecurityWeek
Russia-linked APT28 deploys the GooseEgg post-exploitation tool against numerous US and European organizations.


The Cyber Express
The United States government took a significant step in countering the spread and misuse of commercial spyware. The Department of


Cyber Security News
Hackers abuse Windows Print Spooler vulnerabilities because it runs with elevated SYSTEM privileges which allows privilege escalation.


Ars Technica
Microsoft didn't disclose the in-the-wild exploits by Kremlin-backed group until now.

Cyber Security News
A new backdoor named "Kapeka" has been identified to be attacking victims in Eastern Europe since mid-2022.

Bleeping Computer
Russian hacker group Sandworm aimed to disrupt operations at around 20 critical infrastructure facilities in Ukraine, according to a report from the Ukrainian Computer Emergency Response Team (CERT-UA).


The Hacker News
With enterprises using 53 different security solutions, why are breaches still a frequent reality? Unpack the paradox in our latest report.


CyberSecurity Dive
Programs are typically sponsored by C-suite executives, while the CISO is often tasked with execution, according to Gartner.


CyberNews
Researchers observe a flood of crude and amateurish ransomware. But it’s cheap, difficult to trace, and comes in many flavors.


CyberSecurity Dive
With increased expectations and a prime position in the spotlight, AppSec teams need reliable tools that can act as a force multiplier for their AppSec programs.

Security Affairs
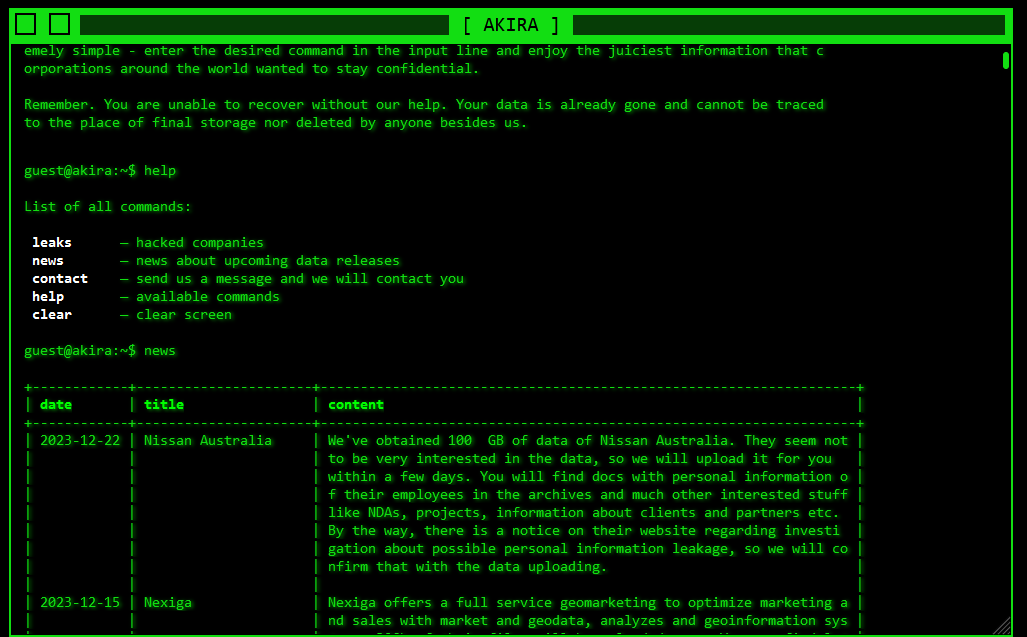
Government agencies revealed that Akira ransomware has breached over 250 entities worldwide and received over $42 million in ransom payments.


Bleeping Computer
You rarely root for a cybercriminal, but a new malware campaign targeting child exploiters doesn't make you feel bad for the victims.

Security Affairs
Threat actors target government entities in the Middle East with a new backdoor dubbed CR4T as part of an operation tracked as DuneQuixote.


The Hacker News
A new variant of the RedLine Stealer malware has been discovered, utilizing Lua bytecode for stealth and effectiveness.


Bleeping Computer
A GitHub flaw, or possibly a design decision, is being abused by threat actors to distribute malware using URLs associated with a Microsoft repository, making the files appear trustworthy.


The Cyber Express
TransparentTribe is an Advanced Persistent Threat (APT) group with a large appetite for targeting Indian government organizations, military personnel, and


SecurityWeek
Akira ransomware has hit over 250 organizations worldwide and received over $42 million in ransom payments.


Infosecurity News
A joint advisory from Europol and US and Dutch government agencies estimated that Akira made around $42m in ransomware proceeds from March 2023 to January 2024


The Hacker News
Akira Ransomware group has already extorted roughly $42 million from over 250 victims globally. They are now targeting both Windows and Linux systems.


Cyber Security News
Proof of Concept (PoC) exploit has been released for a critical vulnerability in Cisco's Integrated Management Controller (IMC).

DarkReading
Malformed DOS paths in file-naming nomenclature in Windows could be used to conceal malicious content, files, and processes.


CyberNews
In less than a year of operations, the Akira Ransomware gang, known for multi-extortion tactics, has claimed approximately $42 million in ransomware proceeds.
Loading more articles....