

CSO
Most attacks affecting SMBs target five older vulnerabilities
Attackers target flaws for a reason: Even years after they are discovered, they still work.


CSO
Attackers target flaws for a reason: Even years after they are discovered, they still work.


The Hacker News
Popular Linux compression tool XZ Utils found with backdoor. Threat actors can remotely execute code on your machine, bypassing authentication.


The Hacker News
CISOs globally are turning to Cato SSE 360 for seamless SASE and SSE transitions, achieving top results in visibility, threat prevention, and data sov

The Record
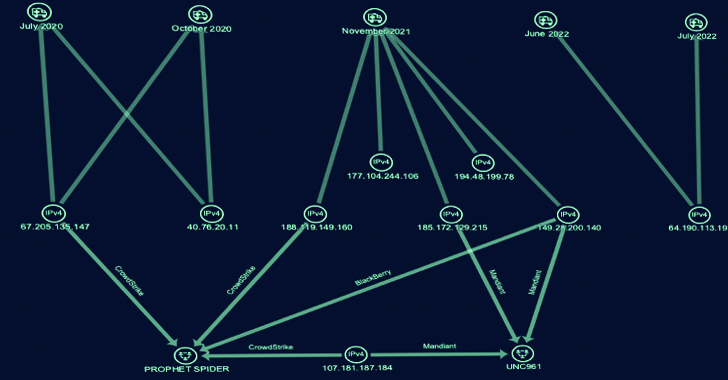
Researchers at Akamai say the FritzFrog botnet, first spotted in 2020, has a new variant that looks for ways to get deeper into networks.


The Record
Katie Moussouris talks with the Click Here podcast team about China's vulnerability disclosure rules, how an EU proposal has similar aspects, and why she believes these kinds of regulations will only make the internet less safe for everyone.


CSO
The company warns that HTTP/2 Rapid Reset is emerging as significant new vulnerability.


Computerworld
In its annual overview of online trends, Cloudflare reports Google remains the most popular site, while OpenAI takes the lead in generative AI services.


Bleeping Computer
The notorious North Korean hacking group known as Lazarus continues to exploit CVE-2021-44228, aka "Log4Shell," this time to deploy three previously unseen malware families written in DLang.


The Hacker News
Lazarus Group launched a new global campaign involves exploiting security flaws in Log4j to deploy previously...


The Record
Hackers connected to North Korea’s Lazarus Group have been exploiting the Log4j vulnerability in a campaign...


The Record
The terms of the settlement are not yet public. Plaintiffs had sued Clearview AI under Illinois' biometric privacy law.


Bleeping Computer
Roughly 38% of applications using the Apache Log4j library are using a version vulnerable to security...


The Hacker News
Don't Rely on Antivirus Alone. Discover why proactive web security is crucial in the ever-changing digital landscape.


The Hacker News
🚨 Bitcoin wallets created from 2011 to 2015 vulnerable to "Randstorm" exploit, potentially allowing unauthorized access by recovering passwords.


Trend Micro
Explore the world of zero day threats and gain valuable insight into the importance of proactive detection and remediation.


Bleeping Computer
The Iranian hacking group tracked as MuddyWater (aka APT34 or OilRig) breached at least twelve computers belonging to a Middle Eastern government network and maintained access for eight months between February and September 2023.


The Record
Cybersecurity firm Symantec attributed the campaign to a group it calls Crambus but others refer to as APT34, OilRig or MuddyWater.


Ars Technica
More than 8 years after the adoption of HTTP/2, DDoSers devise rapid reset attack.


Trend Micro
This entry delves into threat actors' intricate methods to implant malicious payloads within seemingly legitimate applications and codebases.


The Record
Hackers targeted a Middle Eastern telecom organization and an Asian government in a recent spying operation, according to a report published Thursday.

The Record
Initial alerts about a bug in the obscure but widely used libwebp library have expanded into concerns that it affects not only web browsers like Chrome, but also many other common pieces of software.

The Hacker News
Dive into the world of cyber threats with our Network Effect Threat Report. Learn about multi-customer attacks and which industries are most targeted.


CSO
Sysdig also announced a new cloud inventory and agentless scanning capabilities to tackle cloud security risks.

The Hacker News
Gold Melody, the financially motivated cyber group, is selling access to compromised organizations for ransomware attacks.


The Hacker News
Discover how supply chain vulnerabilities can compromise your business.


CSO
Orca Security’s new search tool takes natural language queries to hunt for Log4j-like vulnerabilities...


The Hacker News
CISA Warns of Nation-State Cyber Threats. Numerous actors leveraging vulnerabilities in Fortinet FortiOS SSL-VPN and Zoho.


CSO
New research also shows old CVEs are still exploited en masse with HTTP anomalies the most common API attack vector.

The Hacker News
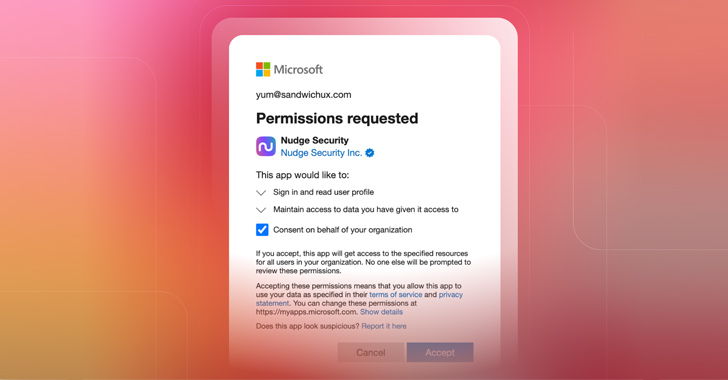
Learn best practices for assessing OAuth risks in your organization.


Bleeping Computer
The Department of Homeland Security's Cyber Safety Review Board (CSRB) has announced plans to conduct an in-depth review of cloud security practices following recent Chinese hacks of Microsoft Exchange accounts used by US government agencies.


The Record
The China-linked attack on Microsoft email services will get a full review by the Cyber Safety Review Board, the Department of Homeland Security announced.


The Record
The White House and a handful of government agencies on Thursday called for experts to help them create policies around the cybersecurity of open source software and promote the use of more security programming languages.


The Record
In its latest report, the Cyber Safety Review Board called on the FCC and FTC to strengthen their oversight and enforcement activities around SIM swapping.

The Record
A leading U.S. senator asked the Justice Department and several other agencies to investigate a recent hack of Microsoft-provided email accounts used by top government officials.


The Record
Researchers at Checkmarx said they investigated two separate incidents involving banks that appear to be the first of their kind.


Bleeping Computer
Attackers behind an ongoing series of proxyjacking attacks are hacking into vulnerable SSH servers exposed online to monetize them through services that pay for sharing unused Internet bandwidth.


CSO
PhonyC2 was used to exploit the log4j vulnerability in the Israeli software SysAid, the attack against...


Bleeping Computer
Security analysts have discovered a previously undocumented remote access trojan (RAT) named 'EarlyRAT,' used by Andariel, a sub-group of the Lazarus North Korean state-sponsored hacking group.


The Hacker News
Andariel, affiliated with North Korea's Lazarus Group, strikes with EarlyRat malware exploiting Log4j...


Trend Micro
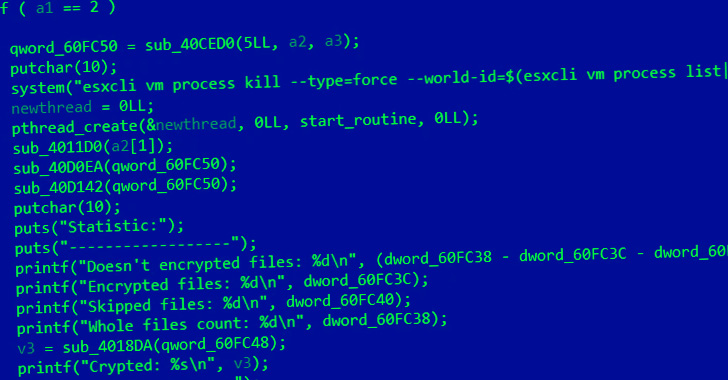
In March and April 2023, we observed a type of ransomware targeting its victims via a minimalistic approach with tools that leave only a minimal footprint behind. Our findings revealed many of the preparations made by the perpetrators and how quickly they managed to carry out the ransomware attack.


CSO
With the two new services, Google aims to help minimize risk from malicious code in the software supply chain.


The Hacker News
Discover the limitations of honeypots, CDN providers & EDR/XDR in cybersecurity intelligence.


The Hacker News
Penetration testing is an essential tool for identifying, analyzing, and mitigating security risks.


CSO
While open source software is the bedrock of modern software development, it is also the weakest link in the software supply chain, according to a report by Endor Labs.


The Record
The EU's cybersecurity agency says several Chinese military hacking groups are targeting European businesses and other organizations.


The Hacker News
North Korea is conducting ransomware attacks against healthcare and critical infrastructure facilities to fund illicit activities.


The Hacker News
Stay ahead of the game with the latest predictions for 2022's most concerning cybersecurity breaches, attacker tactics, and techniques.


The Record
Microsoft says the data breach of Charlie Hebdo was retaliation for the satire publication's call for drawings of Iran's leader, Ali Khamenei.

Bleeping Computer
Microsoft has addressed a false positive triggered by a buggy Microsoft Defender ASR rule that would delete application shortcuts from the desktop, the Start menu, and the taskbar and, in some cases, render existing shortcuts unusable as they couldn't be used to launch the linked apps.


The Record
Researchers in China are claiming a breakthrough in quantum computing, figuring out how to break the RSA public-key encryption system.

CSO
Log4Shell is likely to remain a favored vulnerability to exploit as organizations lack visibility into their software supply chains.


Ars Technica
MCCrash is specially designed to take down Minecraft servers and performs other DDoSes.


CSO
Cybersecurity initiatives included in the US National Defense Authorization Act for 2023 include increased funding for Cybercom’s hunt-forward operations.

ZDNet
That requires a strong focus on operational technology security, since generic cyber hygiene practices will not address risks specific to each of these critical sectors.


The Hacker News
Google on Tuesday announced the open source availability of OSV-Scanner, a scanner that aims to offer easy access to vulnerability information about v


The Hacker News
Iranian nation-state hackers are using a new custom malware dubbed Drokbk that uses GitHub as a dead drop resolver to exfiltrate data from an infected


ZDNet
We know the problems and the answers. So why do so few organisations act?


The Record
The Homeland Security Department on Friday announced its cyber review board would investigate a series of high-profile breaches attributed to the Lapsus$ group, a prolific global data extortion gang run by teenagers.


ZDNet
Almost a year on from Log4j's disclosure, a joint alert by CISA and the FBI warns organizations that if they haven't protected their systems against it yet, they really need to now.


The Hacker News
Iranian government-sponsored hackers have been blamed for compromising a U.S. federal agency by exploiting the Log4Shell vulnerability.


The Record
The director of the FBI warned Congress about the ways the Chinese government may weaponize the popularity of TikTok.


ZDNet
Today's security problems are still to be fixed. But evolving technologies and a fast-changing world mean there are new challenges, too.


The Record
Microsoft accused state-backed hackers in China of abusing the country’s vulnerability disclosure requirements to develop zero-day exploits.


Trend Micro
We discuss the importance of traceability in the world of mobile operating systems.


Trend Micro
In our 2022 midyear roundup, we examine the most significant trends and incidents that influenced the cybersecurity landscape in the first half of the year.


The Hacker News
Researchers have detected active exploitation attempts targeting the recently disclosed critical RCE vulnerability (CVE-2022-42889) in Apache Commons


Bleeping Computer
NSA, CISA, and the FBI revealed today the top security vulnerabilities most exploited by hackers backed by the People's Republic of China (PRC) to target U.S. government and critical infrastructure networks.


Bleeping Computer
The Cheerscrypt ransomware has been linked to a Chinese hacking group named 'Emperor Dragonfly,' known to frequently switch between ransomware families to evade attribution.

The Hacker News
Researchers have attributed a recently discovered Linux-based ransomware known as Cheerscrypt to "Emperor Dragonfly," a Chinese cyber espionage group.


The Record
The Senate Homeland Security Committee on Wednesday easily approved legislation to better secure open-source software.


The Record
Despite having taken “significant steps” to strengthen the country's defenses against digital threats, the progress must be a "prelude" to further changes, the Cyberspace Solarium Commission urged Wednesday.


The Record
The White House told agencies this week that they have 90 days to create a full inventory of the products they use.


The Record
The U.S. government unveiled a slate of sanctions, charges and bounties related to a group of Iranian nationals accused of launching ransomware attacks in the U.S. and abroad.

CSO
Lazarus has used the new remote access Trojan in campaigns that exploit the Log4Shell vulnerability and target energy companies.


The Hacker News
Microsoft warns of a subgroup of the Iranian threat actor Phosphorus that has been conducting ransomware attacks as a "form of moonlighting."


The Hacker News
Google has introduced a new bug bounty program for open source projects, with payouts ranging from $100 to $31,337 to tackle supply chain attacks.


The Record
Google announced on Tuesday that it is launching an open source software vulnerability bug bounty program, offering rewards from $100 to $31,337.

The Hacker News
Iranian state-sponsored actors are leveraging unpatched Log4j systems to target Israeli entities....


Bleeping Computer
Hackers continue to exploit the Log4j vulnerability in vulnerable applications, as shown by the Iranian...


The Record
According to the U.S Government Accountability Office, the rate of businesses getting cyber insurance has doubled recently, from 26% in 2016 to 47% in 2020.


ThreatPost
‘Summer Camp’ for hackers features a compromised satellite, a homecoming for hackers and cyberwarfare warnings.


The Record
The controversy and concern around Log4j is far from over, according to the chair of Homeland Security's...


The Hacker News
Conflicting business requirements is a common problem – and you find it in every corner of an organization, including in information technology.


ThreatPost
Vulnerability—for which a proof-of-concept is forthcoming—is one of a string of flaws the company fixed that could lead to an attack chain.


ThreatPost
Recent LofyLife campaign steals tokens and infects client files to monitor various user actions, such as log-ins, password changes and payment methods.


Bleeping Computer
Security analysts have observed an affiliate of the LockBit 3.0 ransomware operation abusing a Windows Defender command line tool to decrypt and load Cobalt Strike beacons on the target systems.


Bleeping Computer
Security analysts have observed an affiliate of the LockBit 3.0 ransomware operation abusing a Windows Defender command line tool to decrypt and load Cobalt Strike beacons on the target systems.


CSO
The CSRB report predicts the Log4J risk will continue for years and offers best practices for mitigating...


Trend Micro
How to secure your private 5G networks; The challenge of complex ecosystem in DX.


ThreatPost
CISA warns that threat actors are ramping up attacks against unpatched Log4Shell vulnerability in VMware servers.


Trend Micro
We analyzed cases of a Log4Shell vulnerability being exploited in certain versions of the software VMware Horizon. Many of these attacks resulted in data being exfiltrated from the infected systems. However, we also found that some of the victims were infected with ransomware days after the data exfiltration.

ThreatPost
Joseph Carson, Chief Security Scientist and Advisory CISO at Delinea, explores why gamified platforms and hacking esports are the future.


The Hacker News
This article will go in-depth on the strengths and weaknesses of each approach, agent-based and network-based vulnerability scanning.


CSO
Attendees are urged to improve asset management, use SBOMs, and collaborate with government cybersecurity agencies to better ensure software integrity.

The Hacker News
Researchers have discovered a new cyberattack campaign targeting Russian government entities with at least four separate spear phishing campaigns.


Bleeping Computer
Hackers are targeting Russian government agencies with phishing emails that pretend to be Windows security updates and other lures to install remote access malware.


ThreatPost
Mohit Tiwari, CEO of Symmetry Systems, explores Zero Trust, data objects and the NIST framework for cloud and on-prem environments.


ZDNet
Acknowledging that 2021 was a tough year, SolarWinds CEO says it has bolstered its build model and expanded its systems monitoring capabilities so customers can better manage the complexities of hybrid cloud environments.


ThreatPost
Daniel Kaar, global director application security engineering at Dynatrace, highlights the newfound respect for AppSec-enabled observability in the wake of Log4Shell.


ThreatPost
More than 380,000 of the 450,000-plus servers hosting the open-source container-orchestration engine for managing cloud deployments allow some form of access.