

CSO
US AI experts targeted in cyberespionage campaign using SugarGh0st RAT
Threat actors use phishing techniques to obtain non-public information about generative artificial intelligence.


CSO
Threat actors use phishing techniques to obtain non-public information about generative artificial intelligence.


Bleeping Computer
Microsoft has shared a temporary fix for a known issue preventing Microsoft 365 customers from replying to encrypted emails using the Outlook Desktop client.


Bleeping Computer
Security researchers discovered two previously unseen backdoors dubbed LunarWeb and LunarMail that were used to compromise a European government's diplomatic institutions abroad.


DarkReading
When abused by threat actors with sophisticated social-engineering chops, remote-access tools demand that enterprises remain sharp in both defense strategy and employee-awareness training.


SC Magazine
Threat actors use the remote management tool and social engineering to access victims’ systems and install malware.


DarkReading
Cybercriminals are trafficking DocuSign assets that allow for easy extortion and business email compromise.


The Cyber Express
Santander, one of the largest banks in the eurozone, confirmed that an unauthorized party had gained access to a database


Security Magazine
A sophisticated phishing campaign is bypassing multi-factor authentication in order to target Meta business accounts.

Cyber Security News
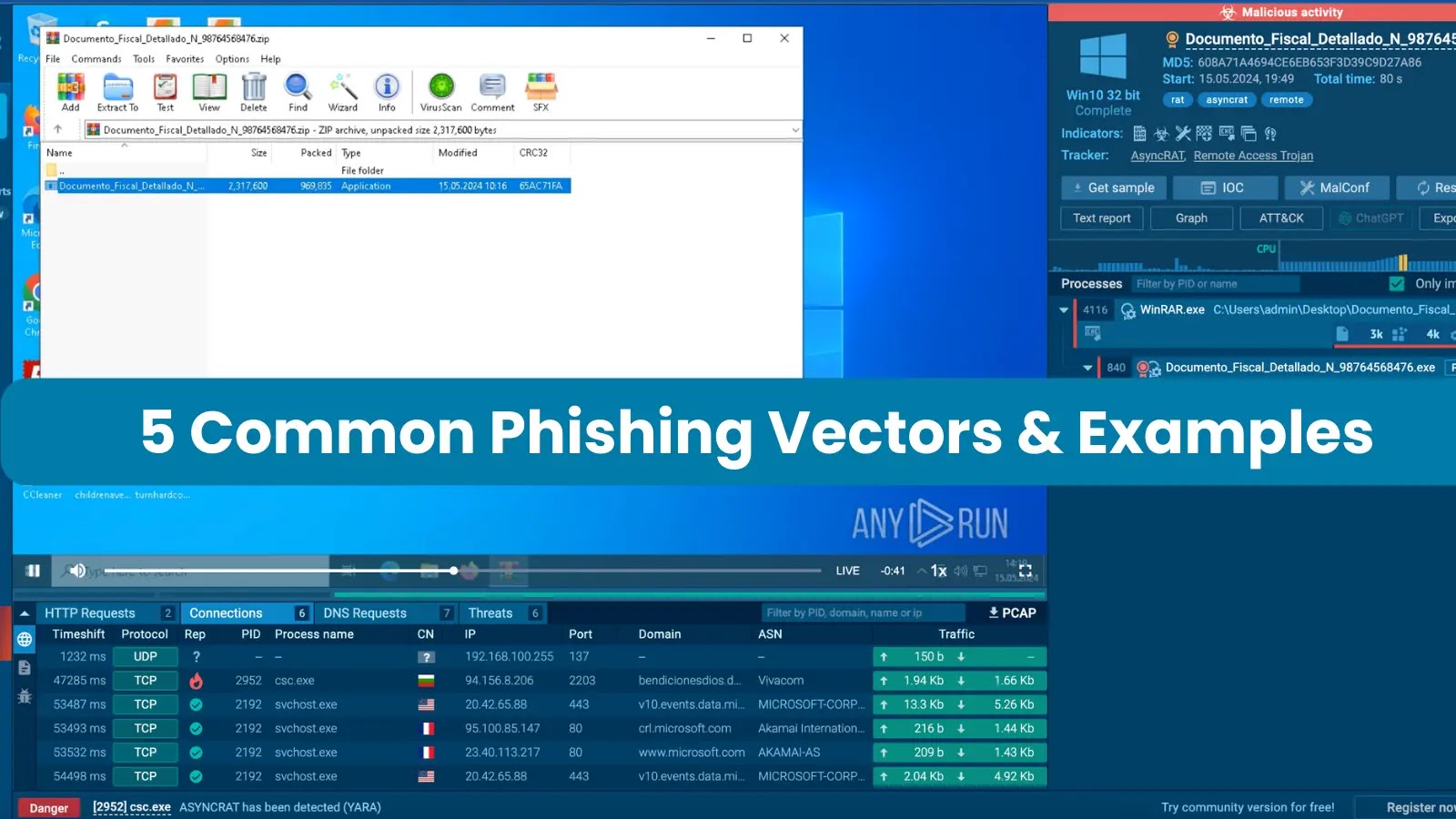
Phishing attacks can be executed through various means, such as SMS and phone calls, but the most prevalent method involves sending victims emails containing malicious attachments.

Ars Technica
Ebury backdoors SSH servers in hosting providers, giving the malware extraordinary reach.


DarkReading
A vulnerability in the HNAP login request protocol that affects a family of devices gives unauthenticated users root access for command execution.


Bleeping Computer
Organizations need to detect and remove intruders quickly to prevent data loss and minimize the impact of lateral movement attacks. Learn more from Specops Software on blocking lateral movement in networks.

.webp)
Cyber Security News
The well-known advanced persistent threat (APT) group Turla, which is based in Russia, is said to be going after the European Ministry.


The Hacker News
Two new backdoors, LunarWeb and LunarMail, have targeted a European ministry of foreign affairs and its diplomatic missions in the Middle East


SecurityWeek
The Spanish bank Santander said customers in Chile, Spain and Uruguay are affected by a data breach at a third-party provider.


The Cyber Express
Santander, one of the largest banks in the eurozone, confirmed that an unauthorized party had gained access to a database


Cyber Security News
Best Network Security Providers for the Healthcare Industry - 1. Perimeter 81, 2. Palo Alto Networks, 3. Fortinet, 4. Cisco, 5. Trend Micro


The Cyber Express
Cyble Research and Intelligence Labs (CRIL) researchers have uncovered a new SideCopy campaign. The threat actor group has previously been


Cyber Security News
Alert Triage is a process of recognizing the important alerts from a huge pool of security alerts and allocating the resources accurately.


The Record
In a data breach notice about the incident, which is still affecting numerous city services, the municipality said hackers copied files from its network.


The Record
“We've got to do a better job of making sure Americans of all political stripes understand what is very probably coming their way over the next less than six months,” Senate Intelligence Chair Mark Warner told leaders from ODNI, CISA and the FBI.


HACKRead
A new Android malware poses as popular applications like WhatsApp, Instagram, and Snapchat to steal user data, including login credentials.

HACKRead
DNS tunneling is being used to bypass security filters by hiding malicious traffic in DNS packets, allowing hackers to steal stolen data.


DarkReading
Several campaigns are leveraging the evasive tactic to provide useful insights into victims' online activities, and find new ways to compromise organizations.


SecurityWeek
Threat actors are using DNS tunneling to track victims’ interaction with spam and to scan network infrastructures.


The Cyber Express
A threat actor using the alias qpwomsx has claimed responsibility for an alleged data breach affecting the popular Indian online


The Hacker News
A new social engineering campaign is targeting enterprises with spam emails to gain initial access. The threat actor overwhelms users' email and calls


Infosecurity News
Palo Alto Networks warns threat actors are using DNS tunneling techniques to probe for network vulnerabilities


Cyber Security News
Recent email campaigns distribute DanaBot malware through two document types: those using equation editor exploits and those containing

.webp)
Cyber Security News
A threat actor has reportedly put up for sale a RCE 0-day exploit targeting various versions of Microsoft Outlook..

Security Affairs
Experts reported that since April, the Phorpiex botnet sent millions of phishing emails to spread LockBit Black ransomware


SC Magazine
Emails from “Jenny Green” delivered LockBit Black through attached ZIP files.


DarkReading
Ransomware groups have always created problems for their victims that only they could solve. Black Basta is taking that core idea in a creative, new direction.


Ars Technica
Threat group has targeted 500 organizations. One is currently struggling to cope.


Bleeping Computer
Since April, millions of phishing emails have been sent through the Phorpiex botnet to conduct a large-scale LockBit Black ransomware campaign.


Bleeping Computer
Threat actors are using Domain Name System (DNS) tunneling to track when their targets open phishing emails and click on malicious links, and to scan networks for potential vulnerabilities.


DarkReading
Europe's cross-border law enforcement agency says the well-known hacking outfit, contrary to claims, did not access operational data.

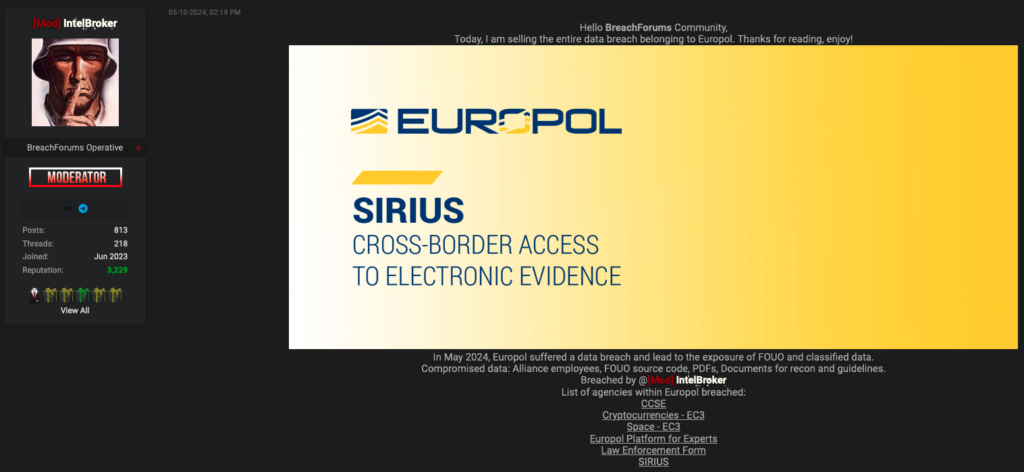
SecurityWeek
Europol is investigating a data breach, but says no core systems are impacted and no operational data has been compromised.

Latest Hacking News
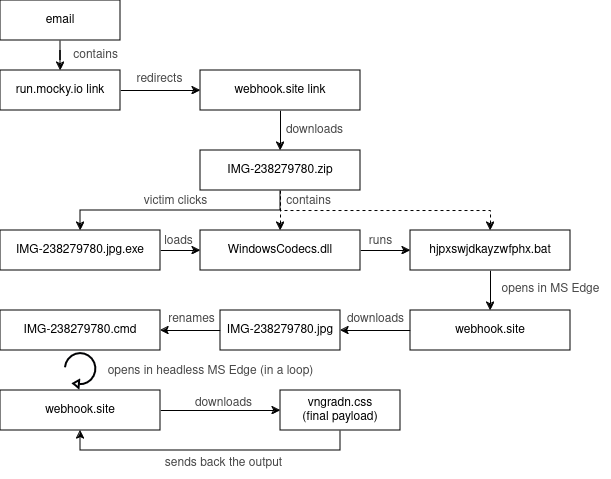
Dell customers need to stay cautious as the vendors admit a data breach impacting their customers. What makes this breach notable is its root cause, which turns out to be a Dell API exploit by


The Hacker News
Are your browser extensions safe? 33% in most orgs aren't! Learn to protect your data with insights from the 2024 Browser Security Report.


CyberNews
The San Francisco division of the FBI is warning individuals and organizations to be aware of AI used by cybercriminals.


The Cyber Express
This week on TCE Cyberwatch we’re covering the different data breaches and vulnerabilities faced by different companies. Along with this,


The Record
An infiltrator posted a breaking news story titled "PERVOKLASSNIY RUSSIAN HACKERS ATTACK" on websites owned by Newsquest Media Group.


Krebs on Security
Last week, the United States joined the U.K. and Australia in sanctioning and charging a Russian man named Dmitry Yuryevich Khoroshev as the leader of the infamous LockBit ransomware group. LockBit's leader "LockBitSupp" claims the feds named the wrong guy,…


The Cyber Express
A state or state-sponsored actor orchestrated the "sophisticated" cyberattacks against the British Columbia government networks, revealed the head of B.C.’s


Bleeping Computer
The threat actor behind the recent Dell data breach revealed they scraped information of 49 million customer records using an partner portal API they accessed as a fake company.


The Hacker News
North Korean hackers have unleashed a new Golang malware called "Durian" in targeted attacks against South Korean crypto firms.

Security Affairs
CERT Polska warns of a large-scale malware campaign against Polish government institutions conducted by Russia-linked APT28.


CyberSecurity Dive
CISA Director Jen Easterly pointed to Microsoft’s decision to link security to executive compensation as a meaningful signal of its priorities.


CSO
The company says the breach compromised non-critical customer data and involved no sensitive personal or financial information.

Cyber Security News
Dell Technologies is investigating a data breach incident involving a company portal containing limited customer information related to purchases.


The Record
Okta Chief Security Officer David Bradbury discusses lessons from the incident, how nation-state threats are evolving, and how AI is already influencing identity-based attacks.


Bleeping Computer
Poland says a state-backed threat group linked to Russia's military intelligence service (GRU) has been targeting Polish government institutions throughout the week.


Bleeping Computer
Project management platform Monday.com has removed its "Share Update" feature after threat actors abused it in phishing attacks.


Bleeping Computer
AT&T's email servers are blocking connections from Microsoft 365 due to a "high volume" spam wave originating from Microsoft's service.


Infosecurity News
Afghanistan, Turkmenistan and Tajikistan victims experienced the highest share of banking Trojans

Bleeping Computer
Dell is warning customers of a data breach after a threat actor claimed to have stolen information for approximately 49 million customers.


The Hacker News
Russia-Linked APT28 Strikes Poland with Malware Campaign Polish government bodies were hit by a sophisticated malware attack orchestrated by the infam


The Cyber Express
The International Baccalaureate Organization (IBO) confirmed a hacking incident, while clarifying that no ongoing exam papers were leaked despite claims


CyberNews
The emerging industry of “digital afterlives” will cause social and psychological harm, University of Cambridge researchers have warned.


SecurityWeek
BetterHelp customers have started receiving refund notices from a $7.8 million data privacy settlement, the FTC says.


HACKRead
The future of cybersecurity awareness lies in training programs. Discover the future of phishing email training, including gamification and AI.


The Record
A phishing campaign against Polish institutions was the work of Russia’s military intelligence agency, the GRU, according to CERT-PL.


DarkReading
An attacker accessed personal information of over 225,000 active, reserve, and former UK military members from third-party payroll processing system.


SecurityWeek
A new technique named TunnelVision allows attackers to bypass the VPN and redirect traffic through the local network.


DarkReading
At least a portion of executive compensation going forward will be tied to meeting security goals and metrics.


The Cyber Express
MedStar Health, a prominent non-profit healthcare provider disclosed a data breach that impacts more than 183,000 patients from its hundreds


CyberSecurity Dive
Researchers have not identified any AI-engineered cyberattack campaigns, yet, but they say it’s only a matter of time before an AI system is dominant enough in the market to draw attention.


Infosecurity News
MedStar Health and DocGo have become the latest US healthcare providers to announce cybersecurity incidents


The Hacker News
APT42, an Iranian state-backed hacking group, is leveling up its social engineering tactics. They're posing as journalists and event organizers to bui


Cyber Security News
HijackLoader, a modular malware loader observed in 2023, is evolving with new evasion techniques, as it is a variant using a PNG image to


SecurityWeek
Germany recalled its ambassador to Russia for consultations in Berlin following an alleged hacker attack on Chancellor Olaf Scholz’s party.


The Record
The major Washington, D.C., and Maryland health network says the personal data of tens of thousands of people was likely exposed when an outsider accessed emails and files belonging to three employees.


HACKRead
Cybersecurity researchers from Mac security provider, Kandji, have discovered a new malware dubbed "Cuckoo" targeting macOS users.


SecurityWeek
Google rolls out new threat-intel and security operations products and looks to the magic of AI to tap into the booming cybersecurity market.


SecurityWeek
CyberNut has emerged from stealth mode with a K-12-focused security awareness training solution and $800k in pre-seed funding.

%20(1).webp)
Cyber Security News
MedStar Health, a major healthcare provider in the U.S, has reported a data breach involving unauthorized access to the email accounts.


The Cyber Express
Six Australian Members of the Parliament confirmed today that they were targeted by Chinese-state hackers APT31 in a brazen cyberattack


CyberNews
The American healthcare service MedStar has suffered a breach, with attackers gaining access to the personal information of 183,000 patients.


CSO
The attacks by Russia-backed Fancy Bear used an Outlook exploit to compromise several German officials’ accounts.


SC Magazine
Taking a sober look at where and how offensive and defensive GenAI is being used to keep security professionals on their toes.

.png)
Cyber Security News
The weekly news summary keeps you up to date with what’s happening in cybersecurity, including developments, vulnerabilities, breaches, threats, and defensive strategies. Knowing about new cyber risks and attack vectors helps you put up safeguards and preventive measures as soon as possible to protect your systems. Remaining constantly aware gives you a holistic view of […]


Bleeping Computer
The Iranian state-backed threat actor tracked as APT42 is employing social engineering attacks, including posing as journalists, to breach corporate networks and cloud environments of Western and Middle Eastern targets.


SecurityWeek
Germany was joined by NATO and fellow European countries in warning that Russia’s cyberespionage would have consequences.


CyberNews
Cyber scams targeting seniors have risen 11% since 2022, costing those over 60 more than $3.4 billion in losses, a new FBI Elderly Fraud report states.


Bleeping Computer
The NSA and FBI warned that the APT43 North Korea-linked hacking group exploits weak email Domain-based Message Authentication Reporting and Conformance (DMARC) policies to mask spearphishing attacks.


SecurityWeek
Microsoft security chief Charlie Bell pledges significant reforms and a strategic shift to put security above all other product features.


CyberSecurity Dive
The company will enhance management roles under the CISO and partially tie compensation to security performance.


DarkReading
Patch now: Cyberattackers are exploiting CVE-2023-7028 (CVSS 10) to take over and lock users out of GitLab accounts, steal source code, and more.


Infosecurity News
The US warns that the North Korea-linked Kimsuky group is exploiting poorly configured DMARC protocols to spoof legitimate domains in espionage phishing campaigns


SecurityWeek
The US government warns of a North Korean threat actor abusing weak email DMARC settings to hide spear-phishing attacks.


Cyber Security News
Solutions for each challenge are explained in more depth by Cynet’s new guide, “Top 10 Cybersecurity Challenges Faced by K-12 Institutions.”


SecurityWeek
A botnet dismantled in January and used by Russia-linked APT28 consisted of more than just Ubiquiti Edge OS routers.


The Hacker News
Beware of "Shadow SaaS" - a hidden threat to organizations. Learn more: click the link for a must-read guide.

The Hacker News
U.S. government warns of North Korean hackers sending spoofed emails to gather intelligence.


CSO
The company has appointed new product security chiefs as well as a customer-facing CISO as it continues to respond to high-profile attacks on its products and own network.


The Record
The FBI, NSA are warning that the group labeled Kimsuky is exploiting improperly configured instances of DMARC, an email security tool, to send messages intended to trick recipients into thinking they came from legitimate sources.


SC Magazine
The state-sponsored group is exploiting weak DMARC policies to impersonate legitimate domains.


The Record
“The emergence of new actors suggests a deliberate strategy by Russia to diversify its cyberwarfare arsenal,” according to an official with Ukraine's cyber agency.


DarkReading
Organizations can go a long way toward preventing spoofing attacks by changing one basic parameter in their DNS settings.
Loading more articles....