

Trend Micro
Tracking the Progression of Earth Hundun's Cyberespionage Campaign in 2024
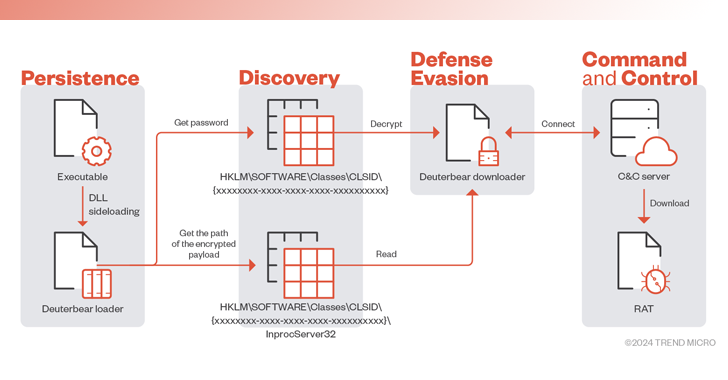
This report describes how Waterbear and Deuterbear — two of the tools in Earth Hundun's arsenal — operate, based on a campaign from 2024.


Trend Micro
This report describes how Waterbear and Deuterbear — two of the tools in Earth Hundun's arsenal — operate, based on a campaign from 2024.

Cyber Security News
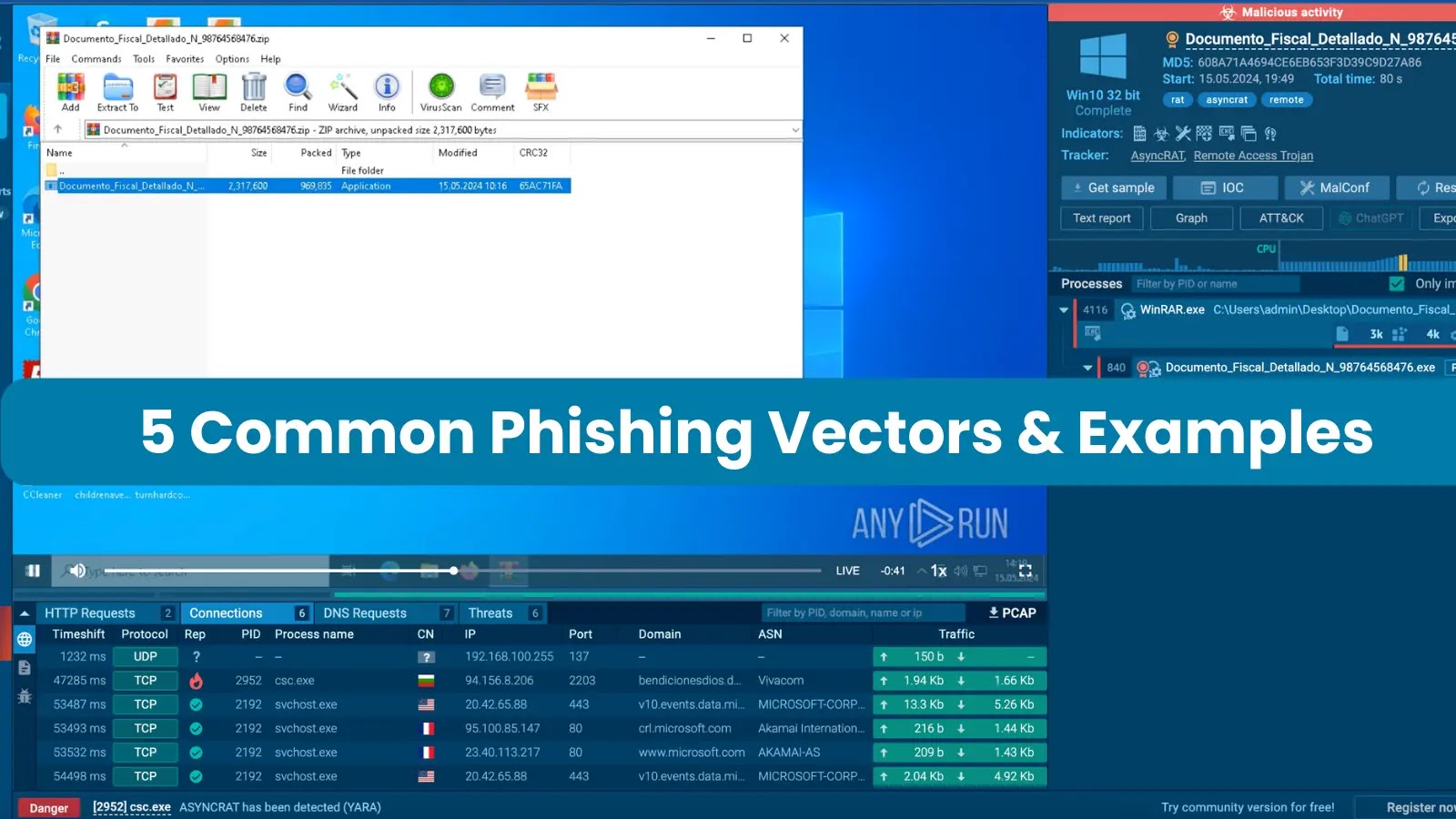
Phishing attacks can be executed through various means, such as SMS and phone calls, but the most prevalent method involves sending victims emails containing malicious attachments.

.webp)
Cyber Security News
The well-known advanced persistent threat (APT) group Turla, which is based in Russia, is said to be going after the European Ministry.


The Cyber Express
Cyble Research and Intelligence Labs (CRIL) researchers have uncovered a new SideCopy campaign. The threat actor group has previously been


Infosecurity News
Recorded Future details a novel campaign that abuses legitimate internet services to deploy multiple malware variants for credential theft


The Hacker News
A new social engineering campaign is targeting enterprises with spam emails to gain initial access. The threat actor overwhelms users' email and calls

Security Affairs
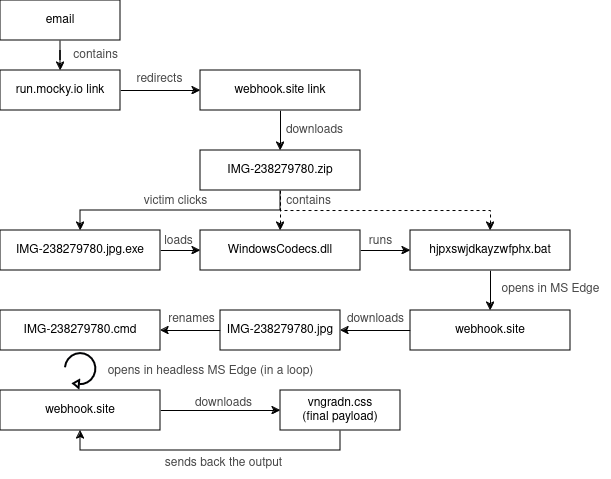
CERT Polska warns of a large-scale malware campaign against Polish government institutions conducted by Russia-linked APT28.


Bleeping Computer
Poland says a state-backed threat group linked to Russia's military intelligence service (GRU) has been targeting Polish government institutions throughout the week.


The Hacker News
Russia-Linked APT28 Strikes Poland with Malware Campaign Polish government bodies were hit by a sophisticated malware attack orchestrated by the infam


Cyber Security News
HijackLoader, a modular malware loader observed in 2023, is evolving with new evasion techniques, as it is a variant using a PNG image to

%20(1).webp)
Cyber Security News
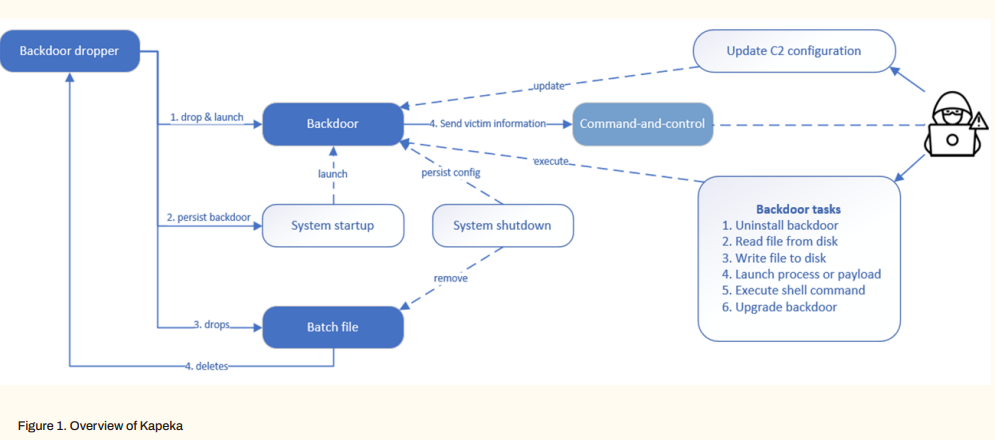
Kapeka, also known as KnuckleTouch, is a sophisticated backdoor malware that has been making waves in the cybersecurity world.


The Hacker News
Nation-state hackers have a new trick - turning Microsoft's own cloud services into secret command centers to launch attacks undetected.


Bleeping Computer
Latrodectus malware is now being distributed in phishing campaigns using Microsoft Azure and Cloudflare lures to appear legitimate while making it harder for email security platforms to detect the emails as malicious.


Cyber Security News
In the rapidly evolving, complex threat landscape EDR companies constantly race against new vectors.As recently Helvio Benedito Dias de


Cyber Security News
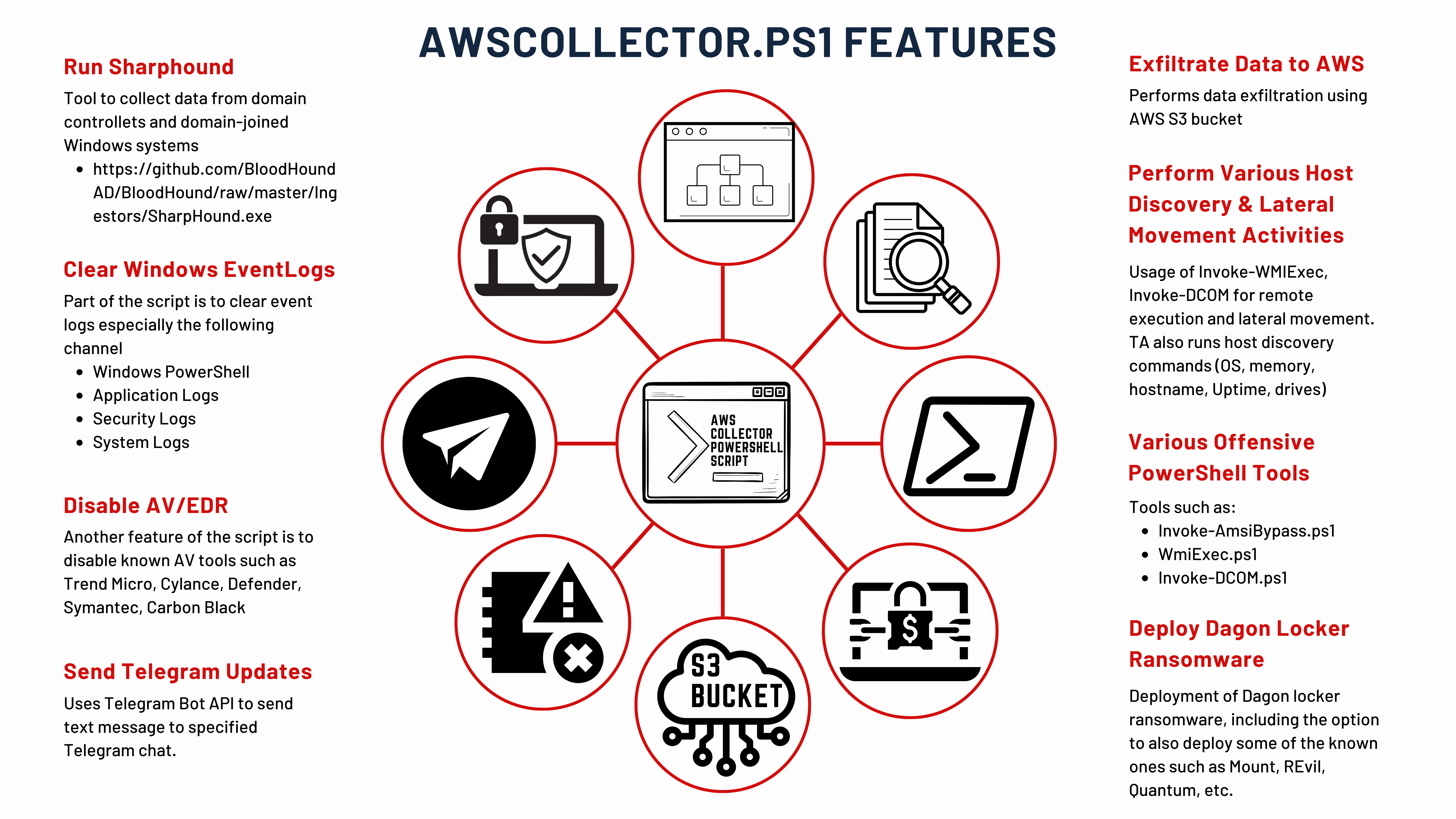
In a sophisticated cyberattack that unfolded over 29 days, cybersecurity analysts have meticulously traced the steps of threat actors from the initial infection with IcedID malware to the eventual deployment of Dagon Locker ransomware. The detailed account of this cyber intrusion provides a chilling example of how quickly and stealthily cybercriminals can compromise an organization’s […]

The DFIR Report
Key Takeaways In August 2023, we observed an intrusion that started with a phishing campaign using PrometheusTDS to distribute IcedID. IcedID dropped and executed a Cobalt Strike beacon, which was … Read More

Security Affairs
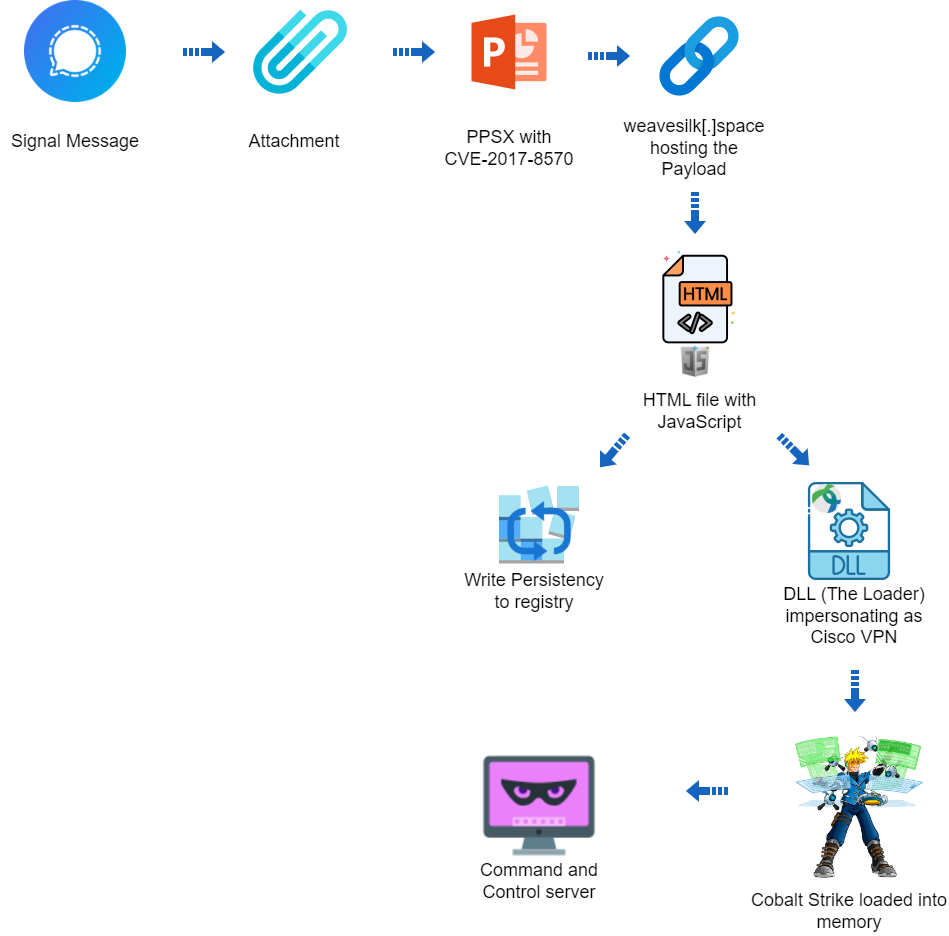
A hacking campaign targeted Ukraine exploiting a seven-year-old vulnerability in Microsoft Office to deliver Cobalt Strike.


The Hacker News
Cybersecurity researchers have uncovered a targeted cyber attack against Ukraine that leveraged a 7-year-old Microsoft Office flaw to deploy Cobalt St


DarkReading
The targeted operation utilized CVE-2017-8570 as the initial vector and employed a notable custom loader for Cobalt Strike, yet attribution to any known threat actor remains elusive.

SecurityWeek
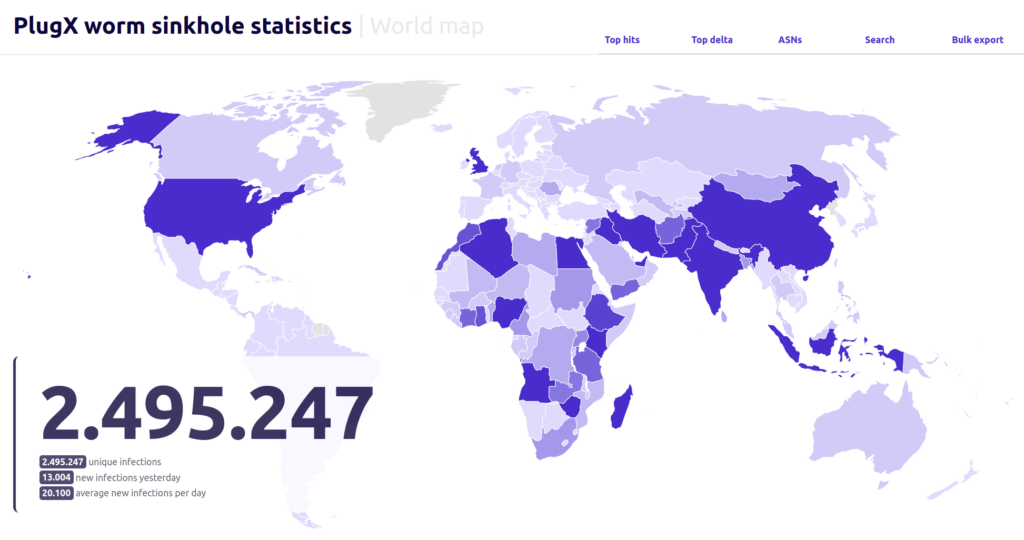
More than 90,000 unique IPs are still infected with a PlugX worm variant that spreads via infected flash drives.

Cyber Security News
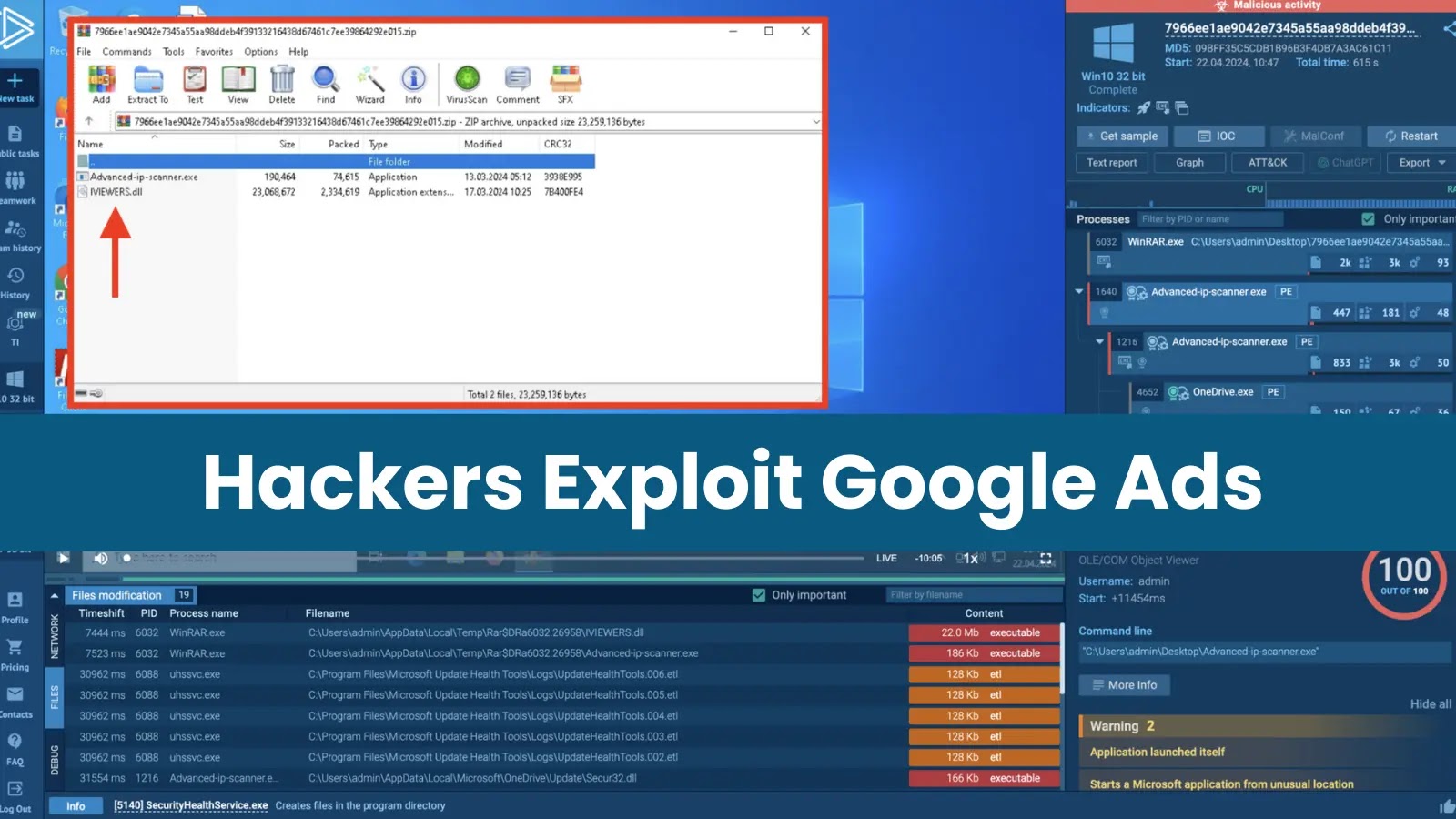
Malicious actors are distributing a new backdoor, MadMxShell, through a Google Ads campaign that impersonates an IP scanner.


The Hacker News
North Korean hackers used fake job offers to deliver a new Trojan called Kaolin RAT. It can change file timestamps and load malware.


Cyber Security News
Black hat SEO methods are used by hackers to manipulate search engine rankings and make malicious or fraudulent websites more visible.


SecurityWeek
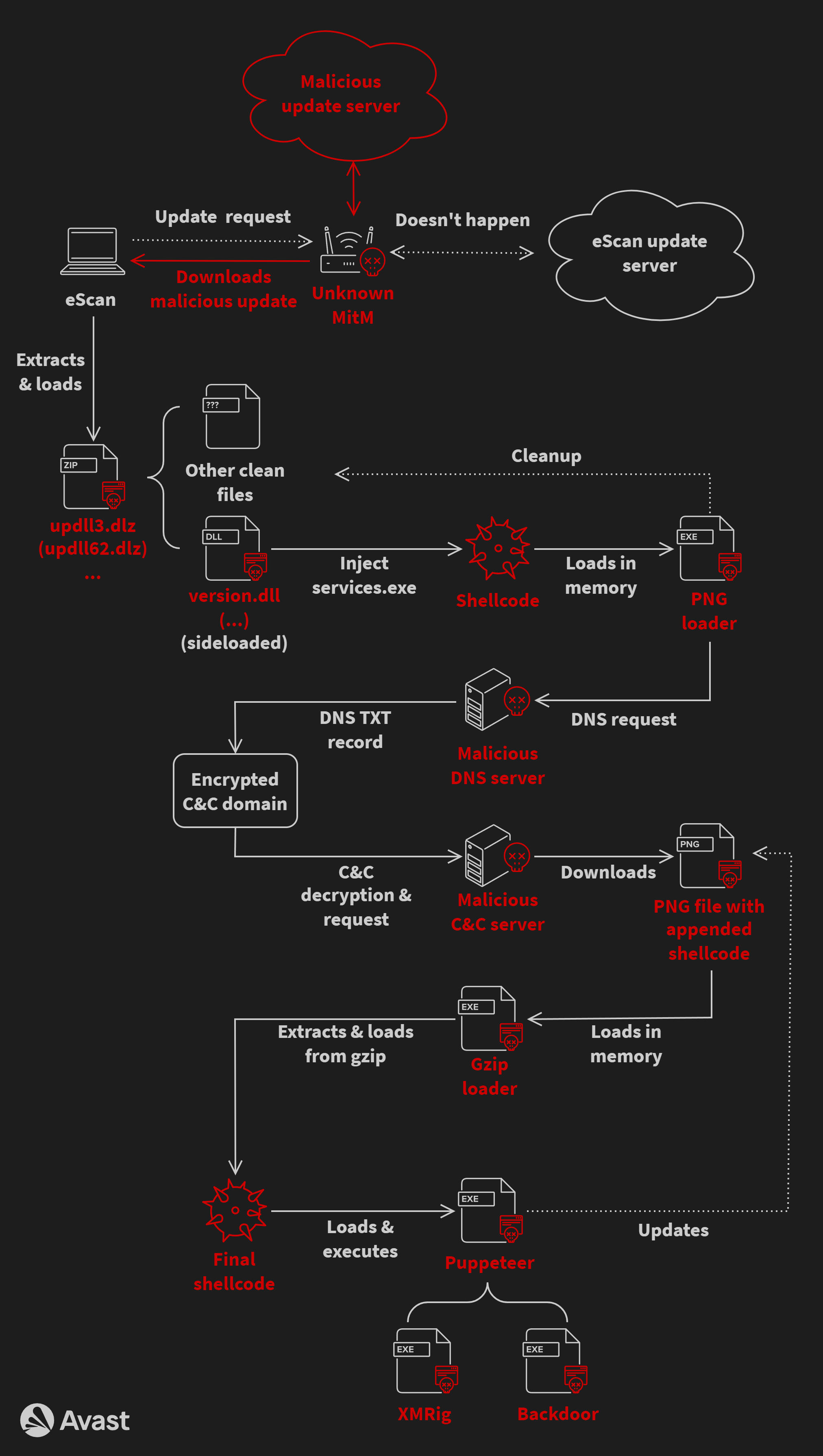
A North Korea-linked threat actor hijacked the update mechanism of eScan antivirus to deploy backdoors and cryptocurrency miners.

Security Affairs
A malware campaign has been exploiting the updating mechanism of the eScan antivirus to distribute backdoors and cryptocurrency miners.


The Hacker News
A sophisticated malware called GuptiMiner has been leveraging a flaw in eScan antivirus updates to spread backdoors and crypto miners across corporate


Ars Technica
eScan AV updates were delivered over HTTP for five years.


Bleeping Computer
North Korean hackers have been exploiting the updating mechanism of the eScan antivirus to plant backdoors on big corporate networks and deliver cryptocurrency miners through GuptiMiner malware.


DarkReading
The infamous Russian threat actor has created a custom tool called GooseEgg to exploit CVE-2022-38028 in cyberespionage attacks against targets in Ukraine, Western Europe, and North America.


SecurityWeek
Russia-linked APT28 deploys the GooseEgg post-exploitation tool against numerous US and European organizations.


Cyber Security News
Hackers abuse Windows Print Spooler vulnerabilities because it runs with elevated SYSTEM privileges which allows privilege escalation.


The Hacker News
Hackers linked to Russia have been exploiting a Windows bug for YEARS to deploy GooseEgg malware for escalating attack access.


Security Affairs
Russia-linked APT28 group used a previously unknown tool, dubbed GooseEgg, to exploit Windows Print Spooler service flaw.


Ars Technica
Microsoft didn't disclose the in-the-wild exploits by Kremlin-backed group until now.


Bleeping Computer
Microsoft warns that the Russian APT28 threat group exploits a Windows Print Spooler vulnerability to escalate privileges and steal credentials and data using a previously unknown hacking tool called GooseEgg.


Bleeping Computer
Microsoft warns that the Russian APT28 threat group exploits a Windows Print Spooler vulnerability to escalate privileges and steal credentials and data using a previously unknown hacking tool called GooseEgg.

Cyber Security News
A new backdoor named "Kapeka" has been identified to be attacking victims in Eastern Europe since mid-2022.


HACKRead
Cybersecurity researchers at Zscaler ThreatLabz believe that the primary target of the MadMxShell backdoor seems to be IT professionals.


The Hacker News
North Korea's state-linked hackers are enhancing their operations with advanced artificial intelligence tools.

Security Affairs
Threat actors target government entities in the Middle East with a new backdoor dubbed CR4T as part of an operation tracked as DuneQuixote.

The Hacker News
China-linked hacking group Earth Hundun is targeting Asia-Pacific tech, research, and government sectors with advanced malware, including "Waterbear"


The Hacker News
A new threat, 'DuneQuixote', targets Middle East governments with sophisticated evasion tactics.


Bleeping Computer
A new info-stealing malware linked to Redline poses as a game cheat called 'Cheat Lab,' promising downloaders a free copy if they convince their friends to install it too.


Infosecurity News
Zscaler also confirmed MadMxShell uses DLL sideloading and DNS tunneling for C2 communication


Cyber Security News
Redline Stealer is a powerful information-stealing malware and hackers often exploit this stealthy stealer to gain unauthorized access to a

Security Affairs
Russia-linked APT Sandworm employed a previously undocumented backdoor called Kapeka in attacks against Eastern Europe since 2022.

.webp)
Cyber Security News
Security researchers uncovered a sophisticated malvertising campaign targeting IT professionals, particularly those in security.


The Hacker News
Hackers are using fake domains of popular IP scanners like Advanced IP Scanner & ManageEngine in a Google Ads malvertising scheme to spread malware.


SC Magazine
Security pros say using Windows backdoor in a malvertising campaign could expose companies to other malware attacks.


Bleeping Computer
The financially motivated threat actor FIN7 targeted a large U.S. car maker with spear-phishing emails for employees in the IT department to infect systems with the Anunak backdoor.

SecurityWeek
Kapeka is a new backdoor that may be a new addition to Russia-link Sandworm’s malware arsenal and possibly a successor to GreyEnergy.


The Hacker News
A new stealthy backdoor malware called Kapeka, likely created by Russia's APT group Sandworm, has been targeting Eastern Europe.


Infosecurity News
WithSecure researchers said it is likely Russian state group Sandworm has added a novel backdoor dubbed ‘Kapeka’ to its arsenal

Cyber Security News
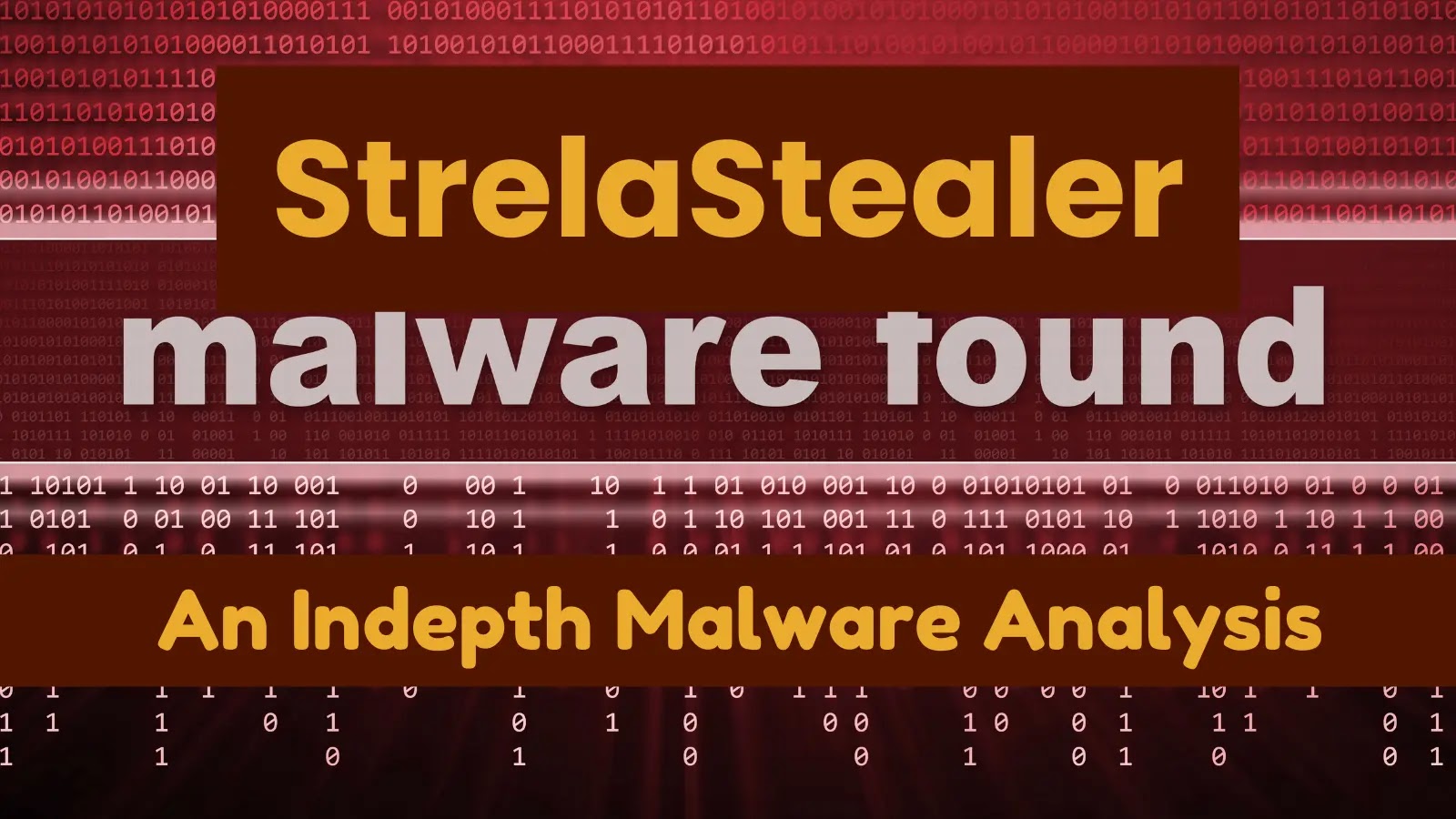
we’ll dissect a timely example of credential theft—StrelaStealer—to identify the malware’s characteristics and capabilities.


Cyber Security News
The weekly cybersecurity news wrap-up provides readers with the latest information on emerging risks, vulnerabilities, ways to reduce them, and harmful schemes to help make defensive measures proactive.


The Cyber Express
Researchers have discovered a sophisticated phishing campaign meticulously crafted to target cryptocurrency users. This elaborate scheme, equipped with the notorious


The Hacker News
MuddyWater, linked to Iran's MOIS, strikes again with DarkBeatC2. Our latest blog unpacks the latest tactics in cyber warfare.


DarkReading
North Korean hackers break ground with new exploitation techniques for Windows and macOS.


DarkReading
North Korean hackers break ground with new exploitation techniques for Windows and macOS.


Trend Micro
Our blog entry provides an in-depth analysis of Earth Hundun's Waterbear and Deuterbear malware.


The Hacker News
Researchers uncover a fresh wave of the Raspberry Robin campaign spreading malware through malicious Windows Script Files (WSFs) since March 2024.

.webp)
Cyber Security News
By displaying sponsored search results for utilities like PuTTY and FileZilla, the attackers can lure in their victims.


Infosecurity News
Fortinet said the malware functions identified include screen monitoring, screen capturing, cryptomining and more


The Hacker News
'Latrodectus' strikes via phishing emails. This powerful downloader can execute commands, evade detection, and pave the way for further attacks.


Cyber Security News
Law enforcement dismantled the Qakbot botnet's servers in 2023's Operation Duck Hunt, but researchers identified its reemergence with a


Cyber Security News
Welcome to the Cyber Security News Weekly Round-Up. Each week, we will explore the latest cyber threats, vulnerabilities, and notable stories that have shaped the cybersecurity landscape.


Cyber Security News
Hackers have manipulated a popular Notepad++ plugin, injecting malicious code that compromises users' systems upon execution.


Cyber Security News
PDF files weaponized by hackers are commonly used as an attack vector since PDFs are highly trusted and shared documents.


HACKRead
Cybersecurity firm Fortinet alerts users of a phishing scam campaign distributing the Byakugan malware which targets Windows users.

The Hacker News
Watch out for FAKE Adobe Acrobat Reader installers. They carry a nasty malware called Byakugan that steals your data.


Bleeping Computer
A relatively new malware called Latrodectus is believed to be an evolution of the IcedID loader, seen in malicious email campaigns since November 2023.


The Hacker News
Banking trojan Mispadu expands from Latin America, now targets users in Italy, Poland & Sweden. Finance, automotive, legal & commercial entities at ri


DarkReading
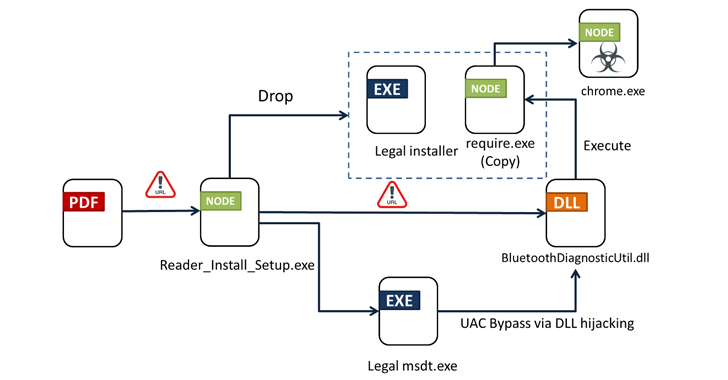
UNAPIMON works by meticulously disabling hooks in Windows APIs for detecting malicious processes.


Bleeping Computer
The Chinese 'Winnti' hacking group was found using a previously undocumented malware called UNAPIMON to let malicous processes run without being detected.


The Hacker News
Notorious threat group Earth Freybug uses new malware UNAPIMON to evade detection. This China-linked group is known for espionage and financial attack


Trend Micro
This article provides an in-depth look into two techniques used by Earth Freybug actors: dynamic-link library (DLL) hijacking and application programming interface (API) unhooking to prevent child processes from being monitored via a new malware we’ve discovered and dubbed UNAPIMON.


The Hacker News
Traditional defense tactics don't always apply to cyber warfare. With EventSentry, bolster your network's defense with prevention, detection, and ongo


The DFIR Report
Key Takeaways We provide a range of services, one of which is our Threat Feed, specializing in monitoring Command and Control frameworks like Cobalt Strike, Metasploit, Sliver, Viper, Mythic, Havoc, … Read More

.png)
Cyber Security News
This weekly cybersecurity news recap keeps you informed about the latest threats, exposures, mitigation techniques, and emerging malicious tactics that could compromise systems.

.webp)
Cyber Security News
Hackers have been found leveraging weaponized virtual hard disk (VHD) files to deploy the notorious Remote Control Software (RAT), Remcos.


The Cyber Express
WarzoneRAT, the notorious Remote Administration Tool (RAT) malware, made a comeback despite the FBI's efforts to dismantle its operations earlier


SecurityWeek
Two Chinese cyberespionage groups have been targeting entities and member countries affiliated with ASEAN.

%20(1).webp)
Cyber Security News
Mispadu, a banking trojan targeting Latin America, attacks Europe, stealing credentials through phishing emails and malicious URLs.


The Hacker News
Latest Cybersecurity reports unveil two China-linked APT groups targeting ASEAN nations in cyberespionage campaign over the past 3 months.


The Hacker News
Suspicious NuGet package 'SqzrFramework480' discovered, potentially targeting devs using Chinese industrial tech. Package may be linked to industrial


SecurityWeek
Suspicious NuGet package targets developers working with technology from Chinese firm Bozhon in possible industrial espionage campaign.


DarkReading
A .NET package available for download right now is either a stealthy industrial systems backdoor or nothing at all.


SecurityWeek
More than 100 organizations in the US and EU have been targeted in recent StrelaStealer infostealer campaigns.

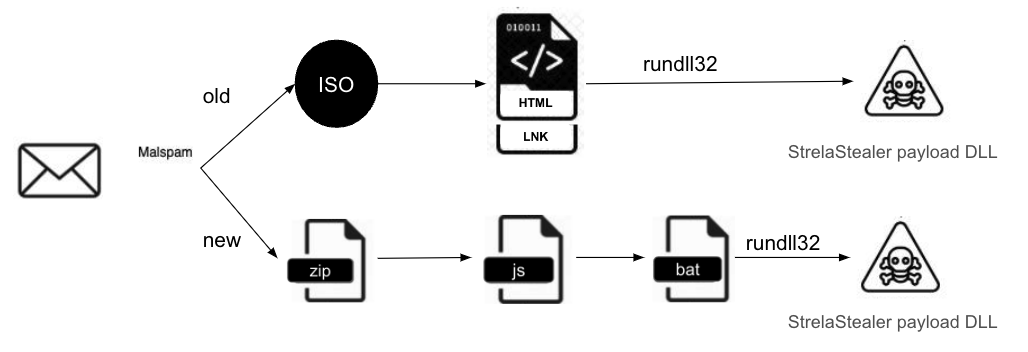
Security Affairs
Researchers reported that over 100 organizations in Europe and US were targeted by a wave of large-scale StrelaStealer campaigns


SC Magazine
Security pros say StrelaStealer uses control flow obfuscation — a technique that lets the threat actor better evade detection and reverse engineering.


Bleeping Computer
A new large-scale StrelaStealer malware campaign has impacted over a hundred organizations across the United States and Europe, attempting to steal email account credentials.

.png)
Cyber Security News
cybersecurity news will keep you posted on the latest developments, exposures, advances, occurrences, threats, and narratives in this field.


Security Affairs
Russia-linked threat actors employ the WINELOADER backdoor in recent attacks targeting German political parties.


The Hacker News
ybersecurity firm Mandiant links recent cyber attacks on diplomatic entities to Midnight Blizzard, a group with ties to Russia's SVR.

Bleeping Computer
Researchers are warning that a notorious hacking group linked to Russia's Foreign Intelligence Service (SVR) is targeting political parties in Germany for the first time, shifting their focus away from the typical targeting of diplomatic missions.


The Hacker News
Researchers at Palo Alto Networks Unit 42 uncover a new wave of phishing attacks delivering StrelaStealer malware, impacting over 100 organizations in


The Hacker News
New threat: BunnyLoader 3.0 malware variant emerges with advanced modules for data theft, keylogging, and evasion tactics.


Cyber Security News
Hackers use stealers to gather sensitive information for example login credentials, financial data or personal details from victims’ devices.


The Hacker News
New cyberattack campaign, DEEP#GOSU, uses PowerShell & VBScript to target Windows systems.

Latest Hacking News
The Patch Tuesday update bundle for March 2024 carries some important security fixes for various Microsoft products. Nonetheless, no specific zero days were reported for this month’s fix. Microsoft March 2024 Patch Tuesday Overview With March updates,
Loading more articles....