

HACKRead
Shadow IT: Personal GitHub Repos Expose Employee Cloud Secrets
Shadow IT involves employees using IT systems without proper security controls, often installing unauthorized software on company computers.


HACKRead
Shadow IT involves employees using IT systems without proper security controls, often installing unauthorized software on company computers.

%20(1)%20(1).webp)
Cyber Security News
A newly disclosed vulnerability, identified as CVE-2024-22026, has been found in Ivanti EPMM, formerly known as MobileIron Core.


SecurityWeek
Russian-speaking threat actors are caught abusing a GitHub profile to distribute information stealers posing as legitimate software.


Bleeping Computer
Alexey Pertsev, one of the main developers of the Tornado Cash cryptocurrency tumbler has been sentenced to 64 months in prison for his part in helping launder more than $2 billion worth of cryptocurrency.

.webp)
Cyber Security News
Cybercriminals have been exploiting GitHub, a platform widely trusted by developers, to host malicious infrastructure.


Bleeping Computer
Today is Microsoft's May 2024 Patch Tuesday, which includes security updates for 61 flaws and three actively exploited or publicly disclosed zero days.


HACKRead
A new Android malware poses as popular applications like WhatsApp, Instagram, and Snapchat to steal user data, including login credentials.


Infosecurity News
Recorded Future details a novel campaign that abuses legitimate internet services to deploy multiple malware variants for credential theft

The Hacker News
12 security flaws addressed, including two critical issues leading to remote code execution. Update to version 1.2.27 now to stay protected


CyberNews
AWS has released a statement saying that S3 will no longer charge for several HTTP error codes if initiated from outside.

.png)
Cyber Security News
Staying informed is the key in this dynamic battle of cybersecurity, and due to this, the weekly news recap provides you with the newest trends, weaknesses, infringements found, and some possible defense mechanisms.


The Hacker News
Fake Android apps mimicking popular platforms like Google & WhatsApp are stealing user data.


Security Affairs
Citrix urges customers to manually address a PuTTY SSH client flaw that could allow attackers to steal a XenCenter admin's private SSH key.


Cyber Security News
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has announced a new initiative called "Vulnrichment" aimed at enriching Common Vulnerabilities and Exposures (CVE) records with additional metadata to help organizations better prioritize vulnerability remediation efforts.


SecurityWeek
CISA’s Vulnrichment project is adding important information to CVE records to help improve vulnerability management processes.


The Record
CISA Director Jen Easterly said the voluntary pledge by software companies is important because of widespread nation-state hacking campaigns, including the Volt Typhoon operation attributed to China.


Infosecurity News
CISA launched a new software vulnerability enrichment program to fill the gap left by NIST’s National Vulnerability Database backlog


DarkReading
Patch now: CVE-2023-49606 in the open source, small-footprint proxy server can potentially lead to remote code execution.


Bleeping Computer
Nearly 52,000 internet-exposed Tinyproxy instances are vulnerable to CVE-2023-49606, a recently disclosed critical remote code execution (RCE) flaw.


SecurityWeek
Hundreds of companies are showcasing their products and services this week at the 2024 edition of the RSA Conference in San Francisco.


The Hacker News
Critical unpatched flaw (CVE-2023-49606) in Tinyproxy could lead to remote code execution. Over 50% of 90K+ exposed hosts are vulnerable.


The Hacker News
New findings suggest the ArcaneDoor cyber espionage campaign targeting network devices from Cisco (CVE-2024-20353, CVE-2024-20359).

%20(1).webp)
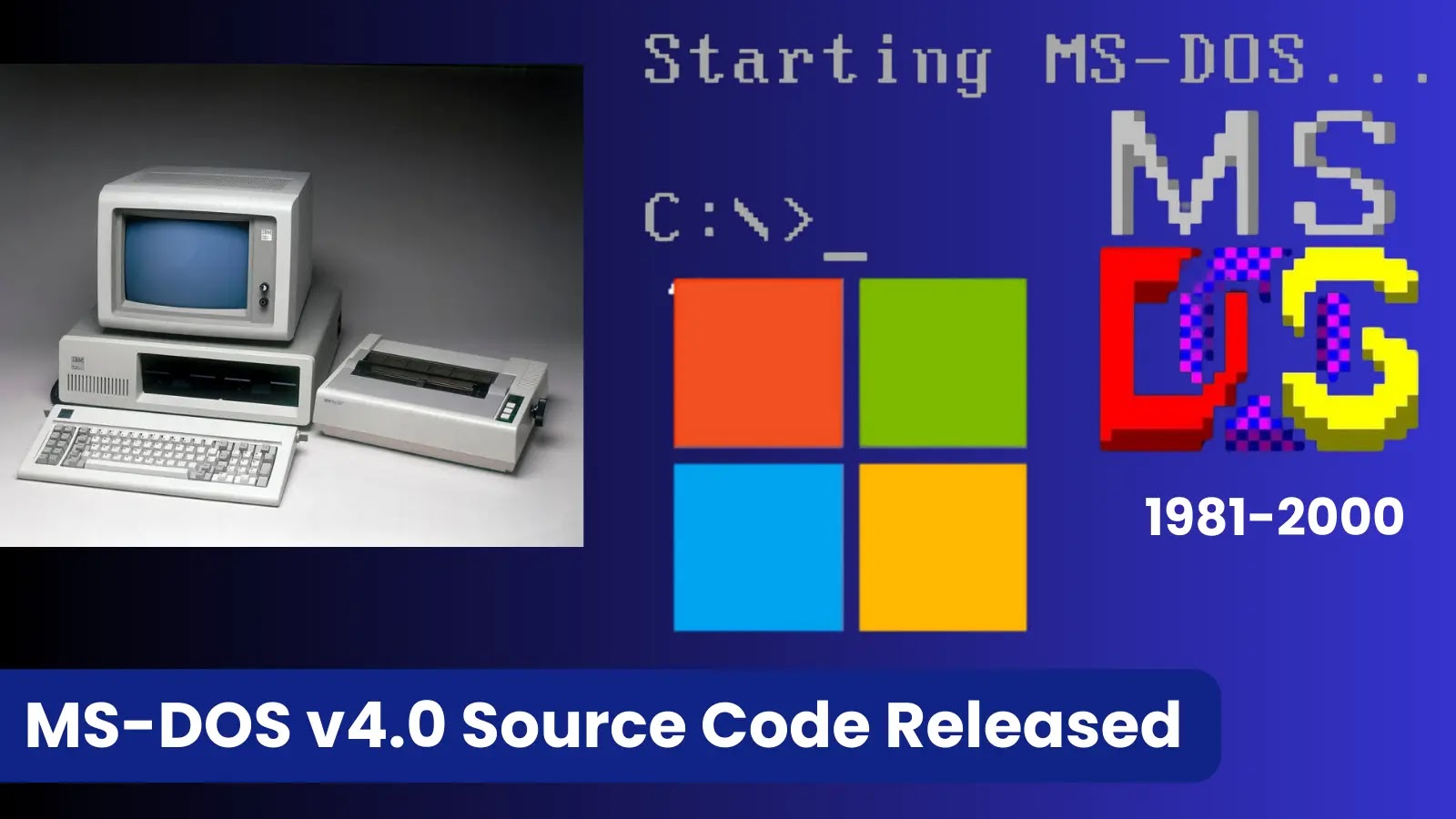
Cyber Security News
Two vulnerabilities have been identified in pgAdmin of PostgreSQL which were associated with Cross-Site Scripting and Multi-Factor


SC Magazine
Taking a sober look at where and how offensive and defensive GenAI is being used to keep security professionals on their toes.

.png)
Cyber Security News
The weekly news summary keeps you up to date with what’s happening in cybersecurity, including developments, vulnerabilities, breaches, threats, and defensive strategies. Knowing about new cyber risks and attack vectors helps you put up safeguards and preventive measures as soon as possible to protect your systems. Remaining constantly aware gives you a holistic view of […]


SecurityWeek
An analysis of IoCs suggests that a Chinese threat group may be behind the recent ArcaneDoor espionage campaign targeting Cisco firewalls.


Bleeping Computer
Bitwarden, the creator of the popular open-source password manager, has just launched a new authenticator app called Bitwarden Authenticator, which is available for iOS and Android devices.


SecurityWeek
Israeli AI security firm Apex has received $7 million in seed funding for its detection, investigation, and response platform.


SecurityWeek
Cybersecurity startups Insane Cyber, Resonance Security, RunReveal and StepSecurity announce pre-seed, early-stage, and seed funding rounds.


Security Affairs
Threat actors breached the Dropbox Sign production environment and accessed customer email addresses and hashed passwords


The Cyber Express
Cloud storage and file sharing company Dropbox disclosed a security breach that resulted in an unauthorized access to sensitive information,


The Hacker News
Dropbox Sign Breached! Unidentified hackers accessed user emails, usernames, and account settings for all Dropbox Sign users.


Bleeping Computer
Cloud storage firm DropBox says hackers breached production systems for its DropBox Sign eSignature platform and gained access to authentication tokens, MFA keys, hashed passwords, and customer information.


Cyber Security News
Live secrets from 183 different SaaS and cloud providers, including giants like AWS, GCP, OpenAI, GitHub, and Postman itself, were found leaking on the platform.


The Record
The company told federal regulators that it discovered unauthorized access to the production environment of its Dropbox Sign product.


Trend Micro
This blog entry aims to highlight the dangers of internet-facing routers and elaborate on Pawn Storm's exploitation of EdgeRouters, complementing the FBI's advisory from February 27, 2024.


Bleeping Computer
A new vulnerability has been discovered in the R programming language that allows arbitrary code execution upon deserializing specially crafted RDS and RDX files.


SecurityWeek
A vulnerability (CVE-2024-27322) in the R programming language implementation can be exploited to execute arbitrary and be used as part of a supply chain attack.


The Hacker News
Multiple vulnerabilities have been discovered in the popular Judge0 online code execution system, putting users at risk of complete system compromise.

Cyber Security News
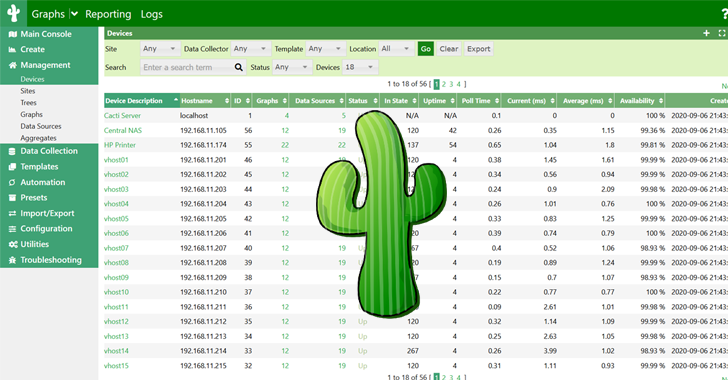
Within ANY.RUN YARA Search also allows you to write, edit, test, download, and manage your rules seamlessly, using your existing TI Lookup quota for searches.

The DFIR Report
Key Takeaways In August 2023, we observed an intrusion that started with a phishing campaign using PrometheusTDS to distribute IcedID. IcedID dropped and executed a Cobalt Strike beacon, which was … Read More


The Hacker News
Hackers are disguising Python backdoors as legitimate npm packages to target developers during fake job interviews.


Bleeping Computer
A new campaign tracked as "Dev Popper" is targeting software developers with fake job interviews in an attempt to trick them into installing a Python remote access trojan (RAT).

Cyber Security News
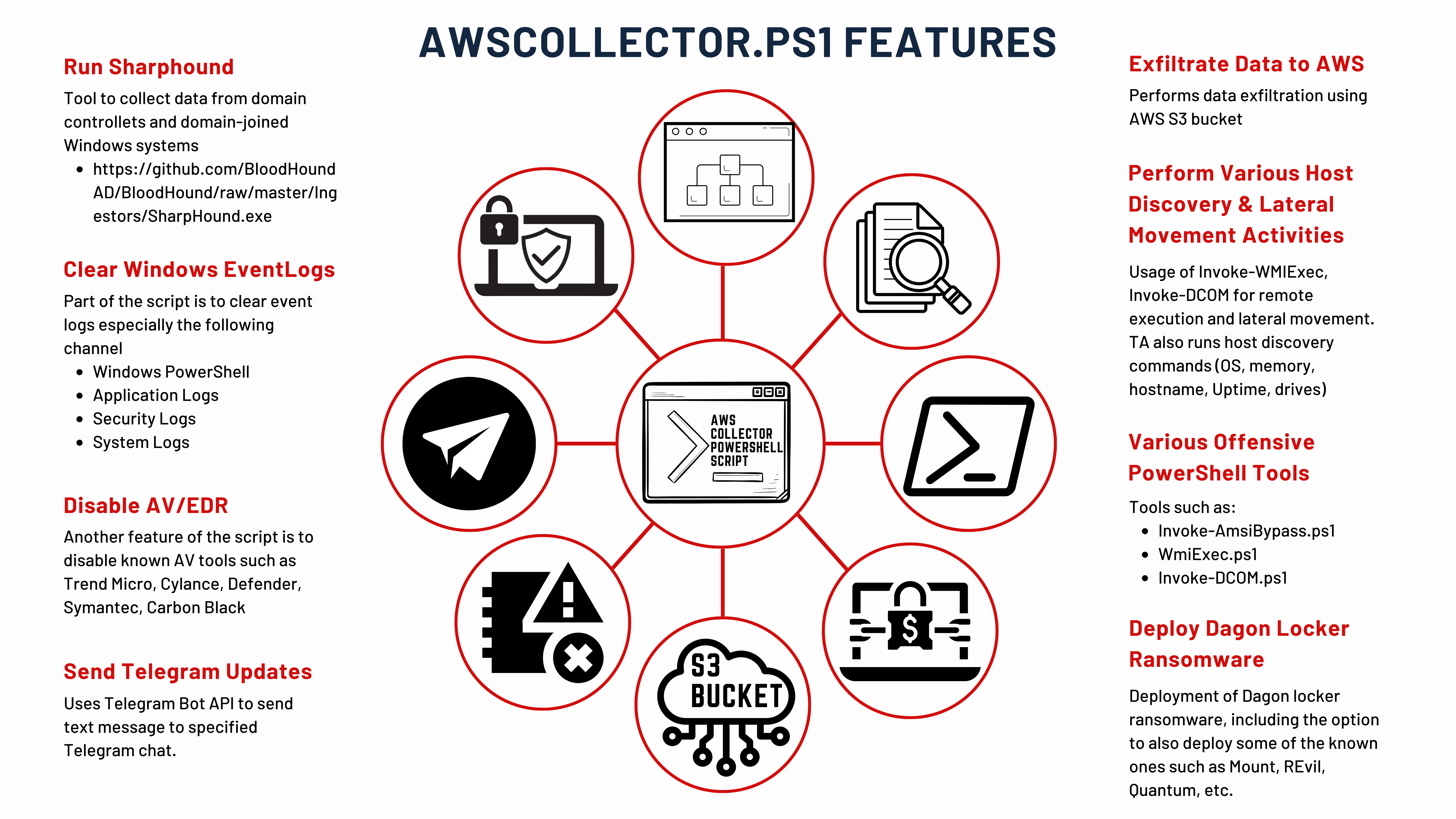
Microsoft has made the source code for MS-DOS 4.0 publicly available. This decision marks the accessibility of historical software


Cyber Security News
A critical vulnerability was addressed by Progress last week which was associated with unauthenticated Command injection on the Progress


DarkReading
An exploit for the vulnerability allows attackers to escape a virtual file system sandbox to download system files and potentially achieve RCE.


DarkReading
An utterly innocuous feature in popular Git CDNs allows anyone to conceal malware behind brand names, without those brands being any the wiser.


Bleeping Computer
North Korean hackers have been exploiting the updating mechanism of the eScan antivirus to plant backdoors on big corporate networks and deliver cryptocurrency miners through GuptiMiner malware.


HACKRead
McAfee cybersecurity researchers have discovered a malicious scheme exploiting GitHub's comment section to spread malware.


SC Magazine
Arbitrary code in Lambda Layers may be unsafely executed in older versions of Keras.


Bleeping Computer
BleepingComputer recently reported how a GitHub flaw, or possibly a design decision, is being abused by threat actors to distribute malware using URLs associated with Microsoft repositories, making the files appear trustworthy. It turns out, GitLab is also affected by this issue and could be abused in a similar fashion.


The Hacker News
North Korea's state-linked hackers are enhancing their operations with advanced artificial intelligence tools.


The Hacker News
A new variant of the RedLine Stealer malware has been discovered, utilizing Lua bytecode for stealth and effectiveness.


Bleeping Computer
A GitHub flaw, or possibly a design decision, is being abused by threat actors to distribute malware using URLs associated with a Microsoft repository, making the files appear trustworthy.

The Hacker News
How attackers are hacking organizations without touching the endpoint by targeting cloud identities.


Cyber Security News
Proof of Concept (PoC) exploit has been released for a critical vulnerability in Cisco's Integrated Management Controller (IMC).


Bleeping Computer
A new info-stealing malware linked to Redline poses as a game cheat called 'Cheat Lab,' promising downloaders a free copy if they convince their friends to install it too.


Cyber Security News
Redline Stealer is a powerful information-stealing malware and hackers often exploit this stealthy stealer to gain unauthorized access to a


Cyber Security News
The latest release, version 124.0.6367.60/.61 for Windows and Mac and version 124.0.6367.60 for Linux, addresses 23 security vulnerabilities.


SecurityWeek
Cisco has observed an increase in brute-force attacks targeting web application authentication, VPNs, and SSH services.

.webp)
Cyber Security News
Attackers tried to take over the JavaScript project from OpenJS Foundation, which is home to JavaScript projects utilized by billions of

Cyber Security News
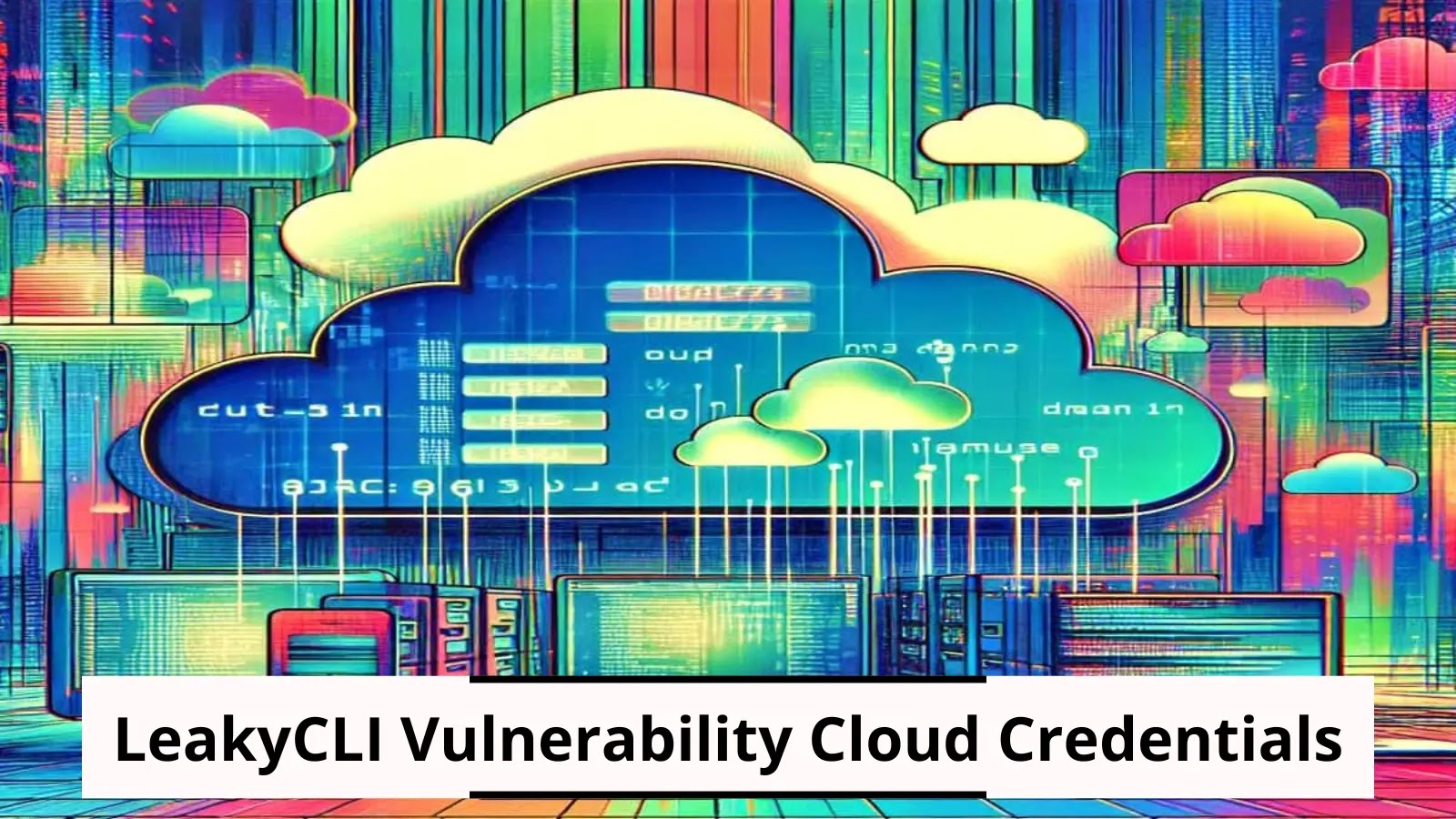
Multiple Cloud Service providers like Google Cloud, AWS and Azure have been discovered with a new vulnerability that has been termed as


SecurityWeek
Chrome and Firefox security updates resolve over 35 vulnerabilities, including a dozen high-severity bugs.


The Hacker News
GenAI isn't just hype—it's a toolbox revolutionizing how we develop software, manage emails, and create content.


Cyber Security News
Multiple vulnerabilities have been identified in PHP that are associated with Command Injection, Cookie Bypass, Account takeover and Denial


CyberNews
A new advisory warns of an uptick in brute force attacks targeting VPNs, SSH services, and other services.

Security Affairs
The PuTTY Secure Shell (SSH) and Telnet client are impacted by a critical vulnerability that could be exploited to recover private keys.


Bleeping Computer
Cisco warns about a large-scale credential brute-forcing campaign targeting VPN and SSH services on Cisco, CheckPoint, Fortinet, SonicWall, and Ubiquiti devices worldwide.


The Hacker News
Security researchers uncover a "credible" takeover attempt on the OpenJS Foundation, mirroring a recent incident with XZ Utils.


Bleeping Computer
A vulnerability tracked as CVE-2024-31497 in PuTTY 0.68 through 0.80 could potentially allow attackers with access to 60 cryptographic signatures to recover the private key used for their generation.


SecurityWeek
Cloud security specialists found data exposure risk associated with Azure, AWS, and Google Cloud command-line tools.


The Hacker News
Popular cloud CLI tools (AWS, Google Cloud, Azure) have a vulnerability ("LeakyCLI") exposing sensitive data in build logs.


HACKRead
The OpenSSF issued alerts for social engineering takeovers of open-source projects after hackers tried to gain control of an OpenJS-hosted project.


CyberSecurity Dive
Federal officials are said to be investigating potential links between the recent XZ Utils campaign and new threat activity against JavaScript project maintainers.


Infosecurity News
Two open source organizations have revealed attempts to socially engineer project takeovers


The Hacker News
Discover the implications for software developed with tools like GitHub Copilot. Learn more about securing your code against AI vulnerabilities.


CyberSecurity Dive
The attempted malicious backdoor may have been part of a wider campaign using social engineering techniques, the open source community warned.


The Record
The thwarted social engineering attempts highlight the urgent need to address weaknesses in the management of open source software.

Security Affairs
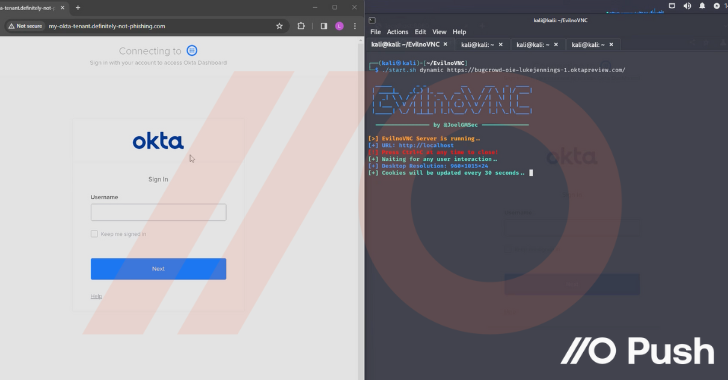
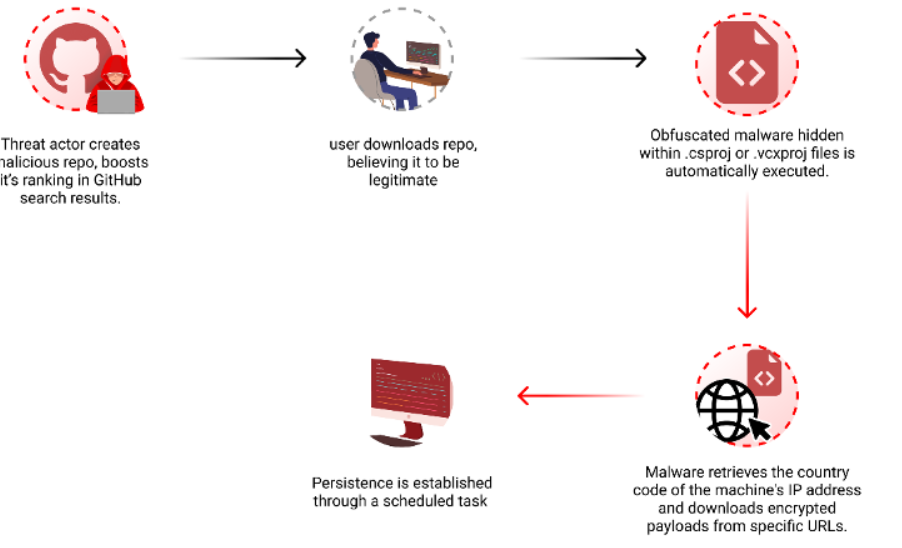
Researchers warn threat actors are manipulating GitHub search results to target developers with persistent malware.


HACKRead
Critical 'BatBadBut' Flaw in Windows Lets Hackers Inject Commands (Patch Now!)


CSO
Researcher that helped compile the knowledge base of common misconfigurations in SCCM releases scanner MisconfigurationManager.ps1.


The Hacker News
Malicious "test files" linked to the XZ Utils backdoor found in popular Rust crate liblzma-sys, downloaded over 21,000 times.


SecurityWeek
Checkmarx warns of a new attack relying on GitHub search manipulation to deliver malicious code.


The Cyber Express
An active exploitation of critical vulnerabilities in D-Link Network Attached Storage (NAS) devices has raised concerns for D-Link users exposing


Trend Micro
Delve into the crucial practice of file scanning within uploader applications, and learn defensive measures to safeguards against malicious threats like malware.


CyberScoop
A report from Binarly finds that a silently patched bug in a popular web server will likely live on in several major end-of-life products.


CyberScoop
A report from Binarly finds that a silently patched bug in a popular web server will likely live on in several major end-of-life products.


Infosecurity News
A new cyber espionage campaign, called ‘eXotic Visit,’ targeted Android users in South Asia via seemingly legitimate messaging apps


The Hacker News
Exposed secrets on GitHub and PyPI are more prevalent than you think. GitGuardian's latest report reveals shocking numbers. Dive into the details here


The Hacker News
Exposed secrets on GitHub and PyPI are more prevalent than you think. GitGuardian's latest report reveals shocking numbers. Dive into the details here


Infosecurity News
Checkmarx warns of GitHub search result manipulation designed to promote malicious repositories


The Cyber Express
A significant data leak, purportedly affecting tech giant Microsoft, has been uncovered by cybersecurity researchers. The leak allegedly exposed sensitive


Security Affairs
Microsoft addressed two zero-day vulnerabilities (CVE-2024-29988 and CVE-2024-26234) actively exploited by threat actors to deliver malware


The Hacker News
Active Android spyware campaign 'eXotic Visit' targeting users in India and Pakistan.


Infosecurity News
A flaw in the Rust standard library exposes Windows systems to command injection attacks


The Hacker News
Hackers are exploiting GitHub's search feature to spread malware. Popular repositories are being cloned and infected.


Bleeping Computer
Threat actors are abusing GitHub automation features and malicious Visual Studio projects to push a new variant of the "Keyzetsu" clipboard-hijacking malware and steal cryptocurrency payments.


Bleeping Computer
Threat actors can exploit a security vulnerability in the Rust standard library to target Windows systems in command injection attacks.

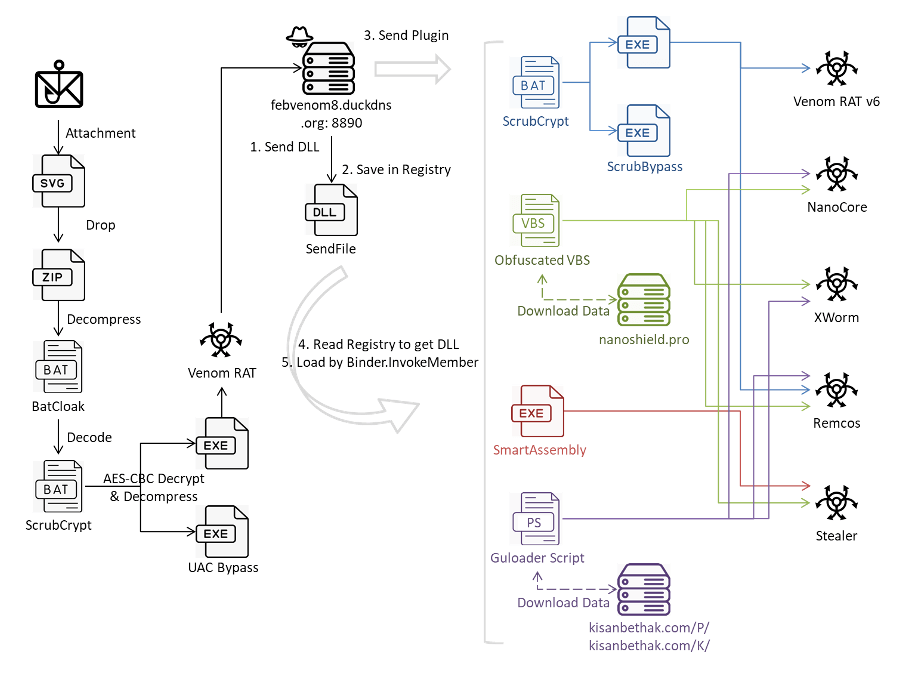
Security Affairs
Researchers discovered a sophisticated multi-stage attack that leverages ScrubCrypt to drop VenomRAT along with many malicious plugins.


DarkReading
The company is asking users to retire several network-attached storage (NAS) models to avoid compromise through a publicly available exploit that results in backdooring.
Loading more articles....