

Cyber Security News
Top 10 Best Managed Service Providers (MSP) for CISO, CTO & IT Managers - 2024
Best MSP for CISO, CTO & IT Managers - 1. Perimeter 812. Secureworks 3. IBM 4. Trustwave 5. Wipro 6. Verizon 7. Sophos 8. Symantec.


Cyber Security News
Best MSP for CISO, CTO & IT Managers - 1. Perimeter 812. Secureworks 3. IBM 4. Trustwave 5. Wipro 6. Verizon 7. Sophos 8. Symantec.


Bleeping Computer
The North Korean hacker group Kimsuki has been using trojanized software packages to deliver a new Linux malware called Gomir in cyberespionage campaigns against targets in South Korea.


Bleeping Computer
The North Korean hacker group Kimsuki has been using a new Linux malware called Gomir that is a version of the GoBear backdoor delivered via trojanized software installers.


Cyber Security News
Best Network Security Providers for the Healthcare Industry - 1. Perimeter 81, 2. Palo Alto Networks, 3. Fortinet, 4. Cisco, 5. Trend Micro

%20(1).webp)
Cyber Security News
Cybersecurity experts have identified a new malware, dubbed WaveStealer, being actively distributed through popular messaging platforms.


HACKRead
A new Android malware poses as popular applications like WhatsApp, Instagram, and Snapchat to steal user data, including login credentials.

.png)
Cyber Security News
Staying informed is the key in this dynamic battle of cybersecurity, and due to this, the weekly news recap provides you with the newest trends, weaknesses, infringements found, and some possible defense mechanisms.

The Hacker News
The notorious FIN7 hacking group is at it again! This time, they're using malicious Google ads to trick users into downloading malware disguised as le


The Hacker News
North Korean hackers have unleashed a new Golang malware called "Durian" in targeted attacks against South Korean crypto firms.

.webp)
Cyber Security News
A sophisticated malware campaign has been identified, specifically targeting Windows and Microsoft Office users through cracked software.


The Hacker News
Fake Android apps mimicking popular platforms like Google & WhatsApp are stealing user data.


The Hacker News
Russia-Linked APT28 Strikes Poland with Malware Campaign Polish government bodies were hit by a sophisticated malware attack orchestrated by the infam


SecurityWeek
Healthcare cybersecurity company Blackwell Security has raised $13 million and appointed Geyer Jones as its first CEO.


The Hacker News
A newer version of the Hijack Loader malware has been observed with updated anti-analysis techniques to evade detection.


The Hacker News
Nation-state hackers have a new trick - turning Microsoft's own cloud services into secret command centers to launch attacks undetected.


SC Magazine
Microsoft Graph API has become popular with hackers because running criminal ops on widely used cloud services raises less suspicion.


DarkReading
Weaponizing Microsoft's own services for command-and-control is simple and costless, and helps attackers better avoid detection.

The DFIR Report
Key Takeaways In August 2023, we observed an intrusion that started with a phishing campaign using PrometheusTDS to distribute IcedID. IcedID dropped and executed a Cobalt Strike beacon, which was … Read More


The Hacker News
Multiple critical vulnerabilities discovered in Brocade SANnav SAN management application, impacting all versions up to 2.3.0.


Cyber Security News
Threat actors exploit fake Android apps primarily for several illicit reasons such as stealing sensitive and personal information from


Cyber Security News
Hackers primarily use ransomware to gain financially from their victims, by blackmailing them for payments to recover their encrypted files


The Hacker News
North Korea's state-linked hackers are enhancing their operations with advanced artificial intelligence tools.


SecurityWeek
TrojAI, a provider of enterprise AI security solutions, announced a $5.75 million funding round of additional seed capital.


The Hacker News
Financial organizations in APAC & MENA are under attack. A sophisticated threat dubbed JSOutProx combines JavaScript & .NET to infiltrate systems.


Bleeping Computer
The U.S. Department of Homeland Security's Cyber Safety Review Board (CSRB) has released a scathing report on how Microsoft handled its 2023 Exchange Online attack, warning that the company needs to do better at securing data and be more truthful about how threat actors stole an Azure signing key.


The Hacker News
Vultur Android banking trojan is back, stronger than ever. It steals sensitive data and remotely controls your phone.

The Hacker News
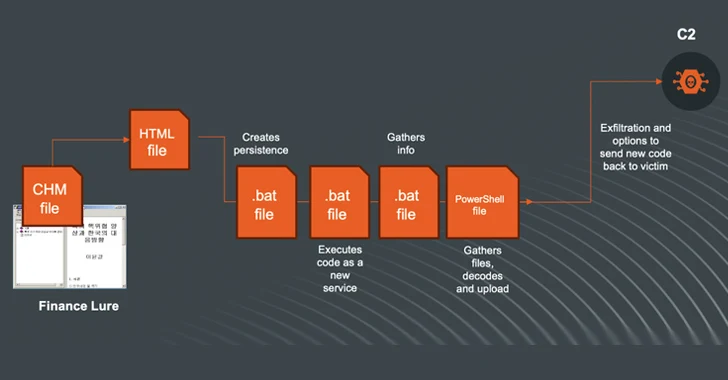
Kimsuky shifts tactics, now using CHM files to deliver malware, targeting sensitive data globally.


The Hacker News
Researchers at Palo Alto Networks Unit 42 uncover a new wave of phishing attacks delivering StrelaStealer malware, impacting over 100 organizations in


The Hacker News
Multiple threat actors exploit security flaws in JetBrains TeamCity to deploy ransomware, crypto miners, Cobalt Strike beacons, and Spark RAT

%20(1).webp)
Cyber Security News
This sophisticated attack distributes malicious APK packages to compromise personal and financial information.

.webp)
Cyber Security News
Cybersecurity circles are abuzz with the latest campaign involving the notorious Remote Control System (RAT), Remcos.

%20(1)%20(1).webp)
Cyber Security News
Broadcom has taken a step by merging Carbon Black and Symantec, the most innovative and engineering-driven brands in the cybersecurity space.


SecurityWeek
Fresh off its $69 billion acquisition of VMware, Broadcom creates an Enterprise Security Group unit that merges Symantec and Carbon Black.


The Hacker News
China-backed hackers, Evasive Panda, target Tibetan users in watering hole & supply chain attacks.

DarkReading
The nation-state group compromised the website of a Tibetan festival and a software application to target user systems in Asia.

The Hacker News
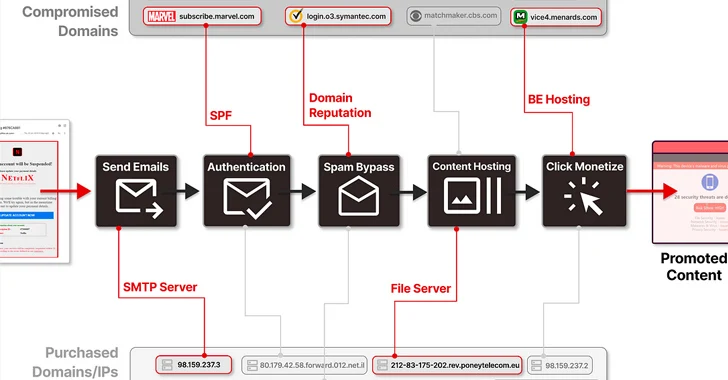
Over 8,000 subdomains belonging to recognized brands and organizations are being exploited for malicious email distribution.


Bleeping Computer
A massive ad fraud campaign named "SubdoMailing" is using over 8,000 legitimate internet domains and 13,000 subdomains to send up to five million emails per day to generate revenue through scams and malvertising.


Bleeping Computer
A massive ad fraud campaign named "SubdoMailing" is using over 8,000 legitimate internet domains and 13,000 subdomains to send up to five million emails per day to generate revenue through scams and malvertising.


Cyber Security News
Network security providers for the government: 1. Perimeter81 2. Cisco 3. Palo Alto Networks 4. Fortinet 5. Symantec 6. Trend Micro.


The Cyber Express
Researchers at Cyble recently found the Malware-as-a-Service Infostealer ObserverStealer operating under a new identity. The ObserverStealer was rebranded and revamped


Bleeping Computer
Security researchers analyzing the Alpha ransomware payload and modus operandi discovered overlaps with the now-defunct Netwalker ransomware operation.


Cyber Security News
Best Network Security Providers for Education: 1. Perimeter81 2. Cisco Systems 3. Palo Alto Networks 5. Sophos 6. McAfee 7. Symantec.


SC Magazine
Ransomware expert warns public disclosure gives Rhysida opportunity to strengthen encryption.


Cyber Security News
Best ISO 27001 Compliant Companies: 1. Perimeter 81 2. ISOvA 3. Eramba 4. OrgISMS online 5. ComplianceForge 6. LogicGate 7. Resolver.


SecurityWeek
Guidance on secure use of AI, HHS grant money stolen by hackers, CISA director Jen Easterly target of swatting.


The Cyber Express
In an era where cybersecurity has become an integral part of organizations, the role of Chief Information Security Officers (CISOs)


Cyber Security News
Data Security Solutions for Insurance Providers: 1. Perimeter 81 2. Bitdefender 3. SecureWorks 4. Splunk 5. Symantec DLP 6. McAfee DLP


Cyber Security News
Security analysts at Intrinsic recently discovered ThreeAM (aka 3 AM, ThreeAMtime) ransomware which has been actively attacking small and medium companies.


Cyber Security News
Best Data Security Providers for Finance Services: 1. Perimeter81 2. Symantec 3. McAfee 4. Varonis 5. Forcepoint 6. Gen Digital 7. Palo Alto.


Bleeping Computer
Security researchers analyzing the activity of the recently emerged 3AM ransomware operation uncovered close connections with infamous groups, such as the Conti syndicate and the Royal ransomware gang.


SecurityWeek
Seattle analytics and network detection and response firm secures $100 million in growth funding and adds to its executive team.


SecurityWeek
No amount of new security tools, security personnel or compliance requirements can substitute for proper incident response preparation.


Bleeping Computer
In the wake of the MGM Resorts service desk hack, it's clear that organizations need to rethink their approach to securing their help desks. Learn more from Specops Software on how to prevent such incidents.

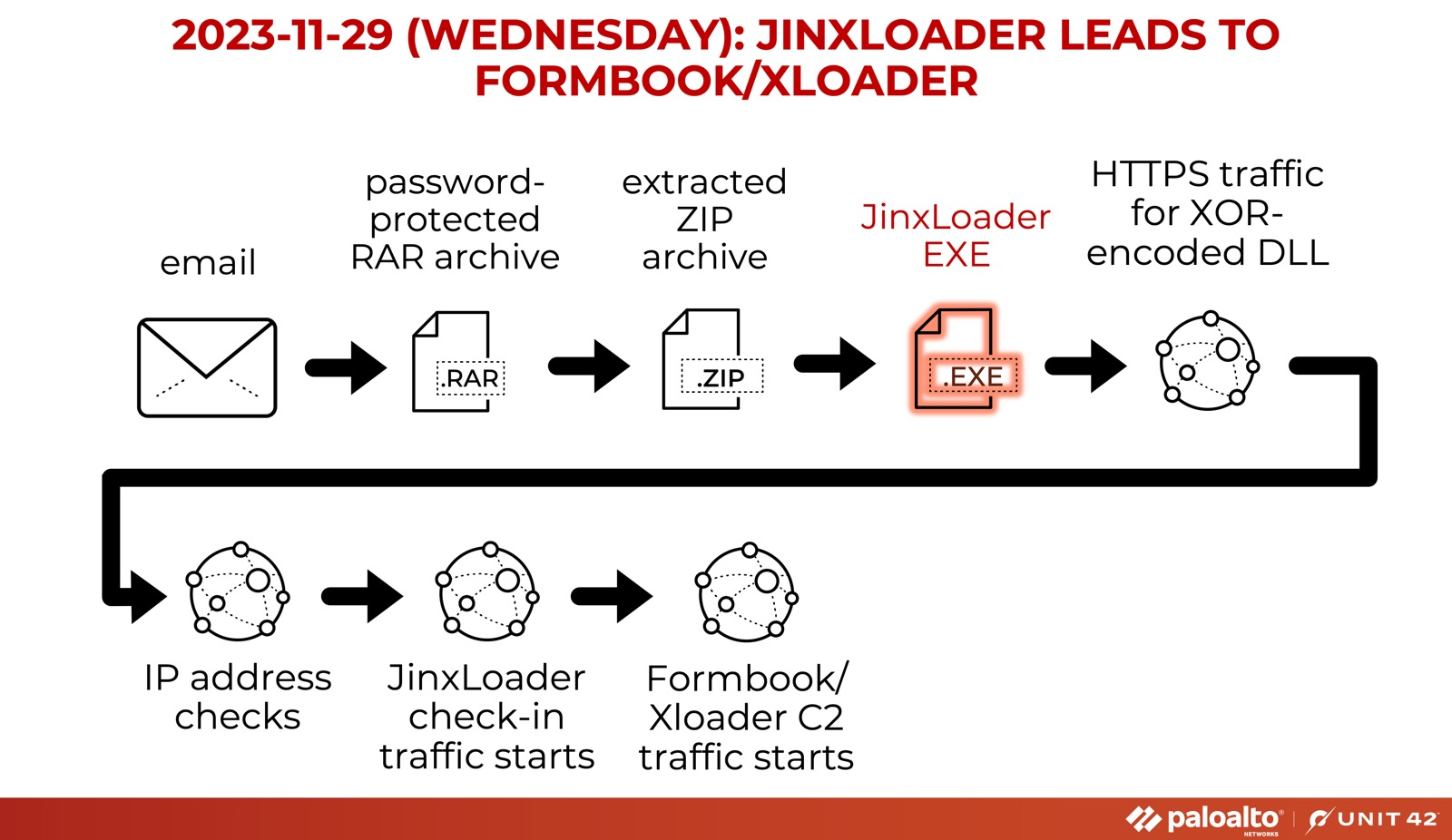
Security Affairs
JinxLoader is a new Go-based loader that was spotted delivering next-stage malware such as Formbook and XLoader.


The Hacker News
A new malware loader called JinxLoader is being used by threat actors to deliver payloads such as Formbook and XLoader.


DarkReading
Seedworm, aka MuddyWater, drops PowerShell-based malware on victims using living-off-the-land techniques.


The Hacker News
Iranian cyber espionage group MuddyWater targets telecom sectors in Egypt, Sudan, and Tanzania using the MuddyC2Go framework.


The Record
It appears to be the first time a group tracked as MuddyWater has attempted cyber-espionage outside of the Middle East, researchers said.


The Cyber Express
The significance of cloud security has risen dramatically in the past few years. As businesses move towards digitalization, safeguarding applications


Bleeping Computer
Consumer traffic rises sharply during the holidays, as do the scope and severity of cyberattacks. Learn more from Specops Software on how to protect your service or help desk from social engineering attacks during the holiday season.


Ars Technica
Broadcom hasn't said how many people will be affected, or much of anything else.

The Record
Hackers believed to be based in China are targeting the Uzbekistan Ministry of Foreign Affairs, as well as people in South Korea, with a strain of malware called SugarGh0st, according to a new report.


The Cyber Express
Infamous Play ransomware group has extended its list of victims by adding 17 new names of companies based in the


Infosecurity News
Security agency wants to resume critical CFATS inspections


SecurityWeek
Broadcom has cleared all regulatory hurdles and will complete its $69 billion acquisition of cloud technology company VMware.


Bleeping Computer
Learn more from Specops Software about the benefits of self-service password resets and ways to accomplish this with on-premises Active Directory.


SecurityWeek
Over 250 organizations take part in GridEx VII, the largest North American exercise focusing on the security of the electrical grid.

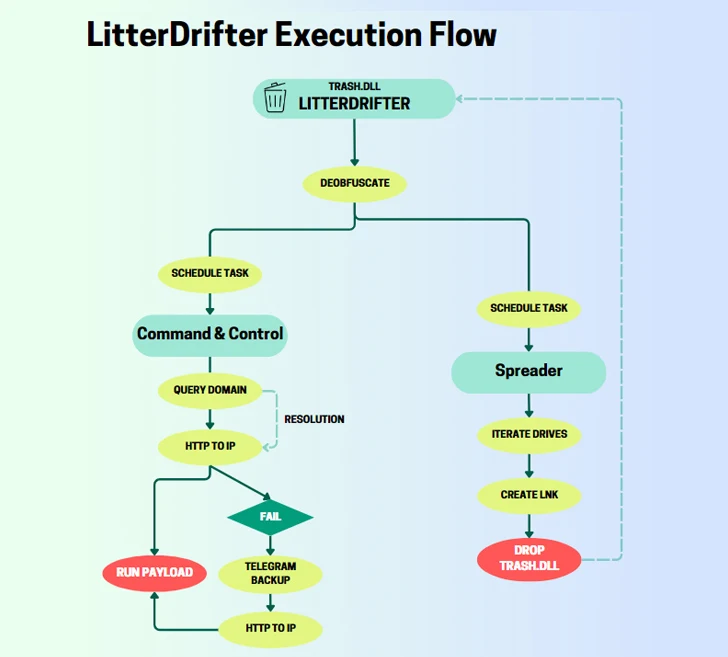
Security Affairs
Russia-linked cyberespionage group Gamaredon has been spotted propagating a worm called LitterDrifter via USB.


The Hacker News
Russian cyber espionage group linked to the FSB are using a USB worm called LitterDrifter to target Ukrainian organizations.


CyberNews
The Play ransomware gang claims to have successfully hit the maximum-security Donald W. Wyatt Detention Facility, located in the City of Central Falls, Rhode Island.


Cyber Security News
Best Network Security Vendors for SaaS : 1. Perimeter 81 2. Palo Alto Networks 3. Fortinet 4. Symantec 5. Check Point 6. McAfee 7. Okta.


Cyber Security News
Best Cloud Access Security Broker (CASB) Software: 1. DoControl CASB 2. Microsoft Cloud App Security 3. Forcepoint 4. Palo Alto Networks.


Cyber Security News
The Crambus espionage group, formally known as OilRig or APT34, has a lengthy history and a great deal of experience conducting prolonged attack.

SecurityWeek
Iran-linked hacking group Crambus spent eight months inside a compromised network of a Middle Eastern government


Bleeping Computer
The Iranian hacking group tracked as MuddyWater (aka APT34 or OilRig) breached at least twelve computers belonging to a Middle Eastern government network and maintained access for eight months between February and September 2023.


DarkReading
The state-sponsored threat actors (aka APT34, Crambus, Helix Kitten, or OilRig) spent months seemingly taking whatever government data they wished, using never-before-seen tools.


The Hacker News
Iran-linked cyber threat group, OilRig, conducted an extensive 8-month-long campaign targeting a Middle East government


The Record
Cybersecurity firm Symantec attributed the campaign to a group it calls Crambus but others refer to as APT34, OilRig or MuddyWater.


SecurityWeek
A previously unknown APT group is targeting organizations in biomedical, IT, and manufacturing sectors in Taiwan.

Infosecurity News
Symantec highlights distinctive DLL sideloading technique


The Hacker News
A New APT Emerges: Grayling, an unknown player, targets IT, manufacturing, and biomedical sectors in Taiwan.


The Record
A previously unknown government-backed hacking group is targeting organizations in the manufacturing, IT, and biomedical sectors, according to new research from Symantec.

The Hacker News
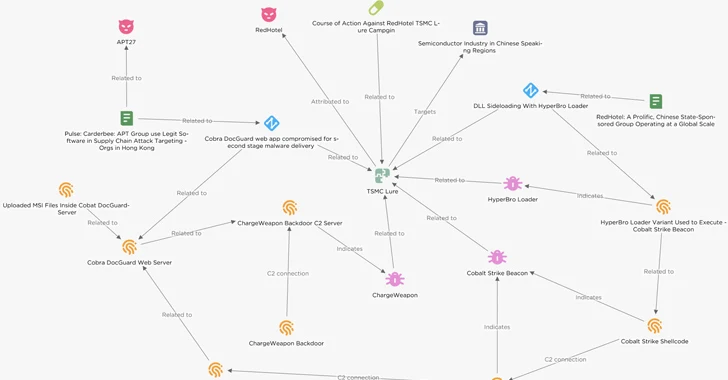
Semiconductor companies in East Asia are under attack. Threat actors posing as TSMC deploy Cobalt Strike beacons via HyperBro backdoor

Bleeping Computer
Hackers engaging in cyber espionage have targeted Chinese-speaking semiconductor companies with TSMC-themed lures that infect them with Cobalt Strike beacons.

The Hacker News
FBI Alert: Dual ransomware attacks are surging, targeting U.S. businesses with multiple variants.


The Record
Hackers with Lazarus used a spearphishing campaign to infiltrate the unnamed company.


Infosecurity News
Symantec explained that the attack leveraged a new variant of Budworm’s SysUpdate backdoor


Bleeping Computer
A Chinese cyber-espionage hacking group tracked as Budworm has been observed targeting a telecommunication firm in the Middle East and a government entity in Asia using a new variant of its custom 'SysUpdate' backdoor.


CyberSecurity Dive
A longstanding group, identified as BlackTech, uses custom malware to evade detection and hack into international subsidiaries of U.S. and Japanese firms.


The Hacker News
Budworm, a China-linked group, strikes again with updated malware tools, targeting government and telecom entities.


The Record
Hackers targeted a Middle Eastern telecom organization and an Asian government in a recent spying operation, according to a report published Thursday.


CyberSecurity Dive
How to Guard Against SMS Phishing In Your Organization with Secure Service Desk Verification.


The Hacker News
Telecom providers in the Middle East face a stealthy cyber threat called ShroudedSnooper. It uses HTTPSnoop to exploit Windows HTTP kernel drivers.


DataBreaches
One of the newer ransomware groups to open a leak site is “ThreeAM.” Bleeping Computer recently reported that the ThreeAM malware is written in...


SecurityWeek
A LockBit affiliate has deployed the new 3AM ransomware family on a victim’s network, after LockBit’s execution was blocked.


Infosecurity News
Symantec says it was used in a failed LockBit attack


DarkReading
Nothing good happens after 2 a.m., they say, especially when hackers have two kinds of ransomware at their disposal.


Bleeping Computer
A new ransomware strain called 3AM has been uncovered after a threat actor used it in an attack that failed to deploy LockBit ransomware on a target network.


The Hacker News
A new ransomware, 3AM, has emerged! It's written in Rust and aims to encrypt files while deleting Volume Shadow copies.


SecurityWeek
Symantec warns that the Redfly APT appears to be focusing exclusively on targeting critical national infrastructure organizations.
Loading more articles....