

CSO
US AI experts targeted in cyberespionage campaign using SugarGh0st RAT
Threat actors use phishing techniques to obtain non-public information about generative artificial intelligence.


CSO
Threat actors use phishing techniques to obtain non-public information about generative artificial intelligence.


Ars Technica
Alleged $6.8M conspiracy involved "laptop farm," identity theft, and résumé coaching.


The Hacker News
Kimsuky hackers launch new social engineering attack using fake Facebook accounts. Learn how they target activists via Messenger and deliver malware.


CSO
Official telegram channels operated by BreachForums members confirm law enforcement seizures and arrest.

%20(1).webp)
Cyber Security News
Earth Hundun, a notable Asia-Pacific malware organization, uses Waterbear and Deuterbear, first encountered Deuterbear.


Infosecurity News
The FBI claims to have seized the domain and servers of hacking forum BreachForums


Trend Micro
This report describes how Waterbear and Deuterbear — two of the tools in Earth Hundun's arsenal — operate, based on a campaign from 2024.


Ars Technica
An earlier iteration of the site was taken down last year; now its reincarnation is gone.

Ars Technica
Ebury backdoors SSH servers in hosting providers, giving the malware extraordinary reach.


Bleeping Computer
The FBI has seized the notorious BreachForums hacking forum used to leak and sell stolen corporate data to other cybercriminals.


SecurityWeek
Russian-speaking threat actors are caught abusing a GitHub profile to distribute information stealers posing as legitimate software.


SC Magazine
The infamous data leak site’s domain and Telegram account were seized Wednesday morning.


Bleeping Computer
Today is Microsoft's May 2024 Patch Tuesday, which includes security updates for 61 flaws and three actively exploited or publicly disclosed zero days.


Infosecurity News
GCHQ chief warns China's cyber actions threaten global internet security, while Russia and Iran pose immediate risks


Infosecurity News
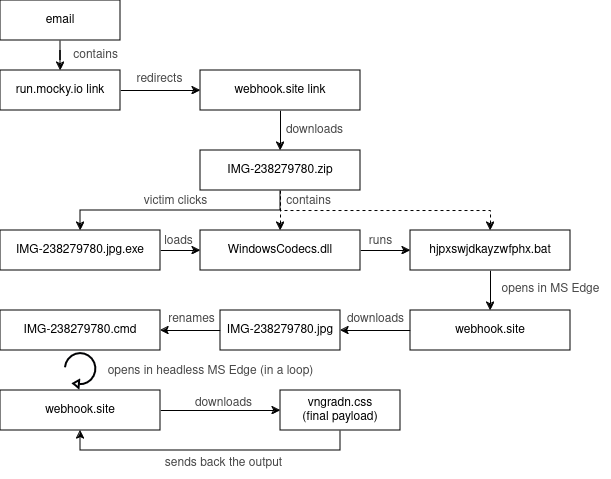
Recorded Future details a novel campaign that abuses legitimate internet services to deploy multiple malware variants for credential theft

HACKRead
DNS tunneling is being used to bypass security filters by hiding malicious traffic in DNS packets, allowing hackers to steal stolen data.


DarkReading
Several campaigns are leveraging the evasive tactic to provide useful insights into victims' online activities, and find new ways to compromise organizations.


SecurityWeek
Threat actors are using DNS tunneling to track victims’ interaction with spam and to scan network infrastructures.


Latest Hacking News
Torrance, California, May 13th, 2024, CyberNewsWireCriminal IP, a renowned Cyber Threat Intelligence (CTI) search engine developed by AI SPERA, has recently signed a technology partnership to exchange threat intelligence data based on domains and potentially

Security Affairs
Experts reported that since April, the Phorpiex botnet sent millions of phishing emails to spread LockBit Black ransomware


CSO
The odds of attacks are growing as attackers can now easily access code modification and reverse engineering tools.


Ars Technica
Threat group has targeted 500 organizations. One is currently struggling to cope.


Bleeping Computer
Since April, millions of phishing emails have been sent through the Phorpiex botnet to conduct a large-scale LockBit Black ransomware campaign.


Bleeping Computer
Threat actors are using Domain Name System (DNS) tunneling to track when their targets open phishing emails and click on malicious links, and to scan networks for potential vulnerabilities.


HACKRead
Encrypted email services like ProtonMail and Wire promise privacy, but can they guarantee anonymity? A recent case in Spain has users questioning the limitations of encryption when law enforcement steps in.


Infosecurity News
Analyzing Mallox samples, Sekoia identified two distinct affiliates using different approaches

%20(1).webp)
Cyber Security News
"Our partnership with Quad9 is a recognition of the accuracy of Criminal IP's data," stated Byungtak Kang, CEO of AI SPERA.


Bleeping Computer
The Criminal IP Threat Intelligence (CTI) search engine to integrate with Quad9's threat-blocking service. Learn more from Criminal IP about how this integration can help you.


HACKRead
Torrance, California, May 13th, 2024, CyberNewsWire


The Cyber Express
As the Central Board of Secondary Education (CBSE) in India released the CBSE results 2024 for its class 10th and

.jpg?height=635&t=1713982088&width=1200)
Security Magazine
The Federal Trade Commission (FTC) has ordered Cerebral, Inc. to restrict how the company can use and/or disclose sensitive consumer data.


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.

.png)
Cyber Security News
Staying informed is the key in this dynamic battle of cybersecurity, and due to this, the weekly news recap provides you with the newest trends, weaknesses, infringements found, and some possible defense mechanisms.


Bleeping Computer
Have I Been Pwned has added the information for 26,818,266 people whose data was leaked in a recent hack of The Post Millennial conservative news website.

Security Affairs
CERT Polska warns of a large-scale malware campaign against Polish government institutions conducted by Russia-linked APT28.

Cyber Security News
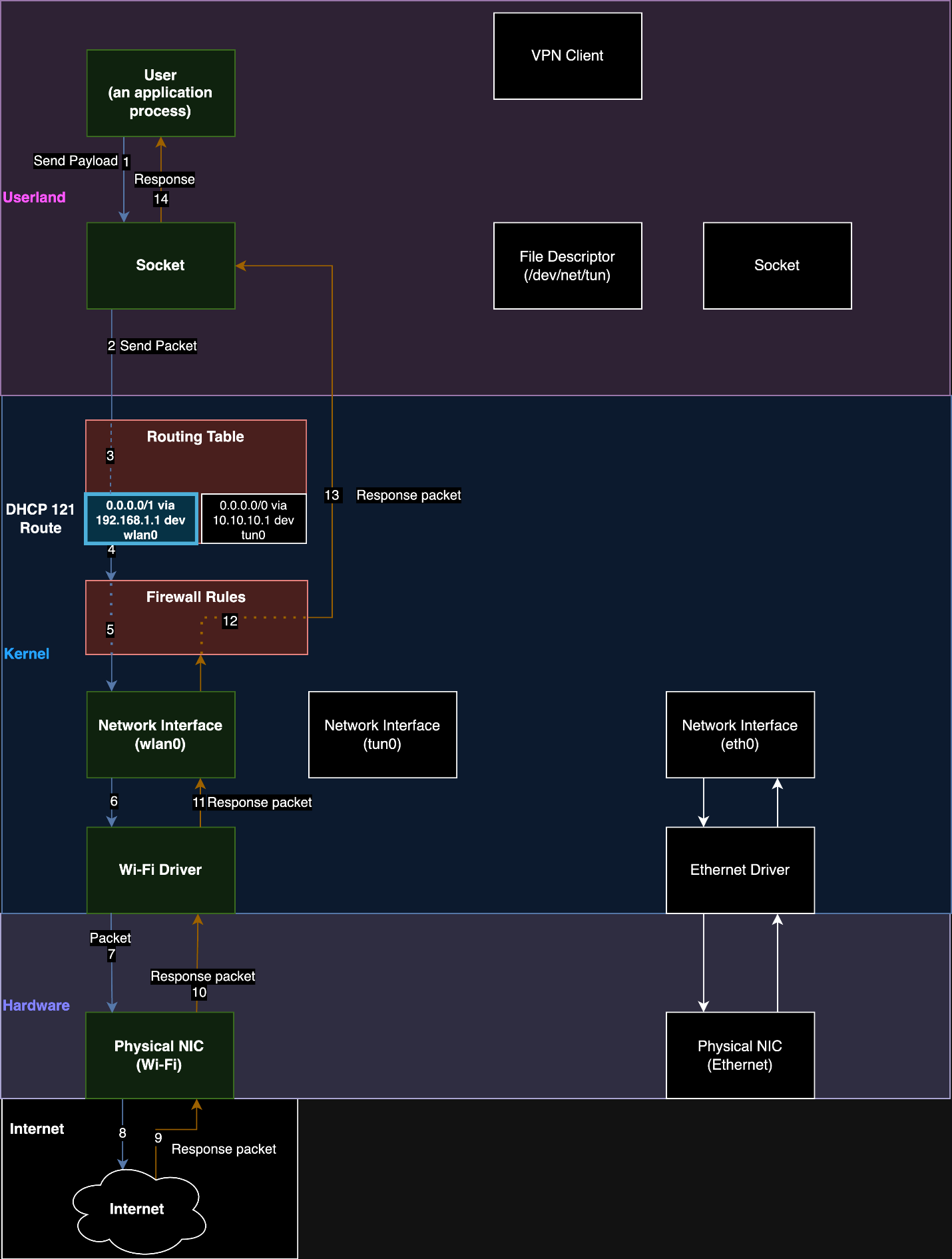
Security researchers have uncovered a new technique called "TunnelVision" that exposes a fundamental flaw in routing-based Virtual Private Networks (VPNs),

.webp)
Cyber Security News
A sophisticated malware campaign has been identified, specifically targeting Windows and Microsoft Office users through cracked software.


Cyber Security News
F5 Big IP has been discovered with two critical vulnerabilities that could potentially allow a threat actor to take full administrative


CyberNews
Cloud security company Zscaler is continuing an investigation into an alleged breach.


The Record
Okta Chief Security Officer David Bradbury discusses lessons from the incident, how nation-state threats are evolving, and how AI is already influencing identity-based attacks.


The Record
The Kremlin’s "hybrid war" on Moldova — featuring disinformation, cyberattacks and influence operations — aims to manipulate three consequential votes in Moldova this year and next.


Bleeping Computer
Poland says a state-backed threat group linked to Russia's military intelligence service (GRU) has been targeting Polish government institutions throughout the week.


DarkReading
F5 customers should patch immediately, though even that won't protect them from every problem with their networked devices.


Bleeping Computer
AT&T's email servers are blocking connections from Microsoft 365 due to a "high volume" spam wave originating from Microsoft's service.


The Hacker News
Researchers have uncovered a vulnerability (CVE-2024-3661) that allows threat actors to snoop on your VPN traffic.


DarkReading
China-based cybercriminal group "BogusBazaar" created tens of thousands of fraudulent online stores based on expired domains to steal payment credentials.


The Cyber Express
Security researchers have revealed new critical vulnerabilities in F5’s Next Central Manager, posing severe risks to organizational cybersecurity. These Next


SecurityWeek
BetterHelp customers have started receiving refund notices from a $7.8 million data privacy settlement, the FTC says.


The Hacker News
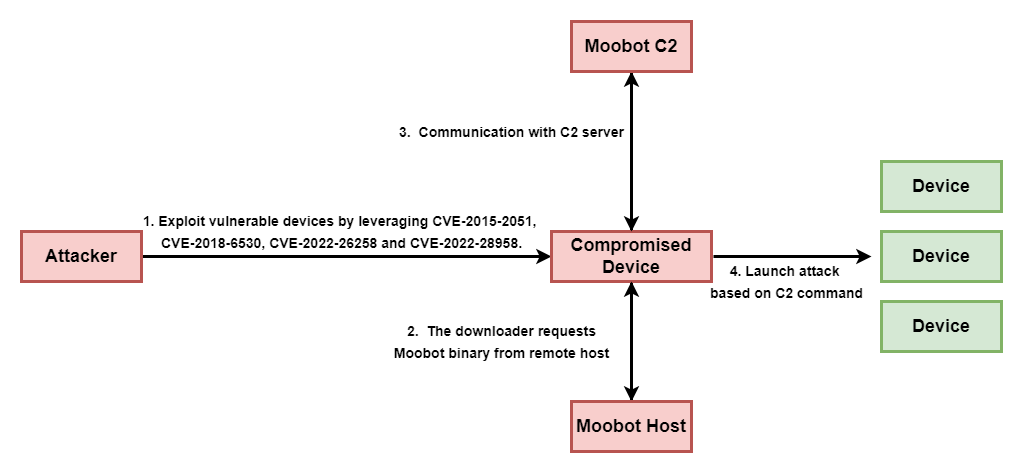
Ivanti Connect Secure (ICS) devices are under attack! Two critical vulnerabilities are being exploited to deploy the notorious Mirai botnet.


SecurityWeek
F5 has patched two potentially serious vulnerabilities in BIG-IP Next that could allow an attacker to take full control of a device.


Infosecurity News
Researchers discover 75,000+ domains hosting fraudulent e-commerce sites, in a campaign dubbed BogusBazaar


Security Affairs
Two high-severity vulnerabilities in BIG-IP Next Central Manager can be exploited to gain admin control and create hidden accounts on any managed assets.

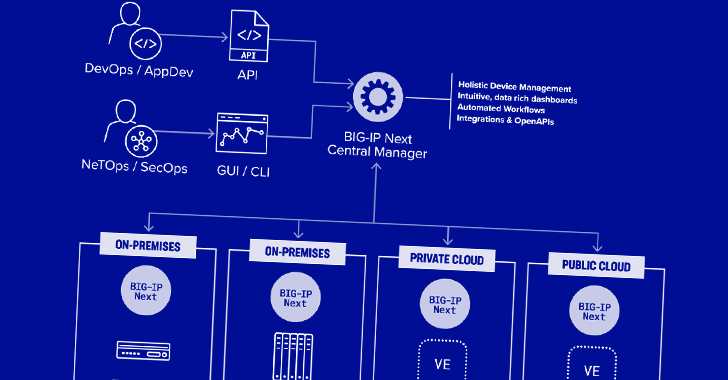
The Hacker News
Two critical vulnerabilities have been discovered in F5 Next Central Manager that could grant attackers full admin control.


CSO
Two high-risk vulnerabilities could be exploited to allow attackers to gain full administrative control on devices via leaked password hashes.


The Record
A phishing campaign against Polish institutions was the work of Russia’s military intelligence agency, the GRU, according to CERT-PL.


SC Magazine
A panel of experts unpack the art of cyber insurance here at RSA Conference and share what's new in coverage and claims.


The Record
The wide-ranging hacking campaign by the state-backed group Volt Typhoon is seen as a prelude of what's to come.


Ars Technica
Hackers can exploit them to gain full administrative control of internal devices.


Bleeping Computer
F5 has fixed two high-severity BIG-IP Next Central Manager vulnerabilities, which can be exploited to gain admin control and create rogue accounts on any managed assets.

Security Affairs
TunnelVision is a new VPN bypass technique that enables threat actors to spy on users’ traffic bypassing the VPN encapsulation.


HACKRead
WordPress websites are under attack with a surge of malicious JavaScript being injected using vulnerable versions of the LiteSpeed Cache plugin.


SecurityWeek
A new technique named TunnelVision allows attackers to bypass the VPN and redirect traffic through the local network.


Security Affairs
Threat actors are exploiting a high-severity vulnerability in the LiteSpeed Cache plugin for WordPress to take over web sites

The Hacker News
The cloud promises agility, but opens a Pandora's box of cyber risks if not secured properly. Understand your responsibility under the shared responsi


Cyber Security News
WordPress plugins make WordPress more useful, but most of these have flaws that hackers may try to take advantage of to get unauthorized


The Cyber Express
A new VPN vulnerability has emerged on the internet, compromising the very essence of online privacy and data protection. The


SC Magazine
Security pros warn that this flaw could affect just about every IP-routing based VPN.


SC Magazine
Zero trust, access certification campaigns and regular AD risk assessments are more critical than ever.


Bleeping Computer
Hackers have been targeting WordPress sites with an outdated version of the LiteSpeed Cache plugin to create administrator users and gain control of the websites.

Bleeping Computer
We need to stay connected in our lives, but that shouldn't require taking risks with our privacy. Guard your data with three years of the Windscribe VPN Pro Plan for $69.97, $137 off the $207 MSRP now through May 12th.


Bleeping Computer
BetterHelp has agreed to pay $7.8 million in a settlement agreement with the U.S. Federal Trade Commission (FTC) over allegations of misusing and sharing consumer health data for advertising purposes.


SecurityWeek
Niobium raises $5.5 million in seed funding for a fully homomorphic encryption (FHE) hardware accelerator designed for zero trust computing.


Security Affairs
MITRE published more details on the recent security breach, including a timeline of the attack and attribution evidence.


Cyber Security News
In a concerning development for cybersecurity, over 150 SSH accounts with root access are currently being advertised for sale on various


Ars Technica
TunnelVision vulnerability has existed since 2002 and may already be known to attackers.


SecurityWeek
Synopsys is selling its Software Integrity Group to private equity firms Clearlake Capital and Francisco Partners in a $2.1 billion deal.


The Hacker News
New findings suggest the ArcaneDoor cyber espionage campaign targeting network devices from Cisco (CVE-2024-20353, CVE-2024-20359).


Cyber Security News
Best Active Directory Management Tools: 1. Microsoft AD Explorer 2. SolarWinds Permissions Analyzer 3. Netwrix 4.ManageEngine ADAudit Plus.


The Hacker News
A new malware called "Cuckoo" is on the loose, targeting both Intel and ARM-based Macs.


The Cyber Express
By Eyal Arazi, senior security solutions lead for Radware The cybersecurity landscape evolved rapidly in 2023. In particular, there was


Krebs on Security
Virtual private networking (VPN) companies market their services as a way to prevent anyone from snooping on your Internet usage. But new research suggests this is a dangerous assumption when connecting to a VPN via an untrusted network, because attackers…

.png)
Cyber Security News
The weekly news summary keeps you up to date with what’s happening in cybersecurity, including developments, vulnerabilities, breaches, threats, and defensive strategies. Knowing about new cyber risks and attack vectors helps you put up safeguards and preventive measures as soon as possible to protect your systems. Remaining constantly aware gives you a holistic view of […]


Ars Technica
ZTDNS brings the best of both worlds to DNS: encryption and fine-grained control.


Bleeping Computer
A Mullvad VPN user has discovered that Android devices leak DNS queries when switching VPN servers even though the "Always-on VPN" feature was enabled with the "Block connections without VPN" option.


Bleeping Computer
A Mullvad VPN user has discovered that Android devices leak DNS queries when switching VPN servers even though the "Always-on VPN" feature was enabled with the "Block connections without VPN" option.

Security Affairs
The Ubiquiti EdgeRouter botnet is still used by Russia-linked group APT28 and cybercriminals organizations.


Cyber Security News
A directory traversal vulnerability (CVE-2024-23334) was identified in aiohttp versions before 3.9.2, allowing remote attackers to


SecurityWeek
A botnet dismantled in January and used by Russia-linked APT28 consisted of more than just Ubiquiti Edge OS routers.


SecurityWeek
An analysis of IoCs suggests that a Chinese threat group may be behind the recent ArcaneDoor espionage campaign targeting Cisco firewalls.


DarkReading
Organizations can go a long way toward preventing spoofing attacks by changing one basic parameter in their DNS settings.


DarkReading
Two years after a warrant went out for his arrest, Aleksanteri Kivimäki finally has been found guilty of thousands of counts of aggravated attempted blackmail, among other charges.


Ars Technica
The threat is potentially grave because it could be used in supply chain attacks.


DarkReading
DMARC adoption is more important than ever following Google's and Yahoo's latest mandates for large email senders. This Tech Tip outlines what needs to be done to enable DMARC on your domain.


Infosecurity News
The US and its allies claim Russian hacktivists are disruptive operations in water, energy, food and agriculture sectors

.webp)
Cyber Security News
Cybersecurity communities are on high alert as threat actors have begun selling RDP access on various underground hacker forums.


The Hacker News
Attention SOHO router users! A new malware called Cuttlefish is on the prowl, stealthily monitoring your traffic and stealing authentication data.

Ars Technica
How and why nation-state hackers and cybercriminals coexist in the same router botnet.

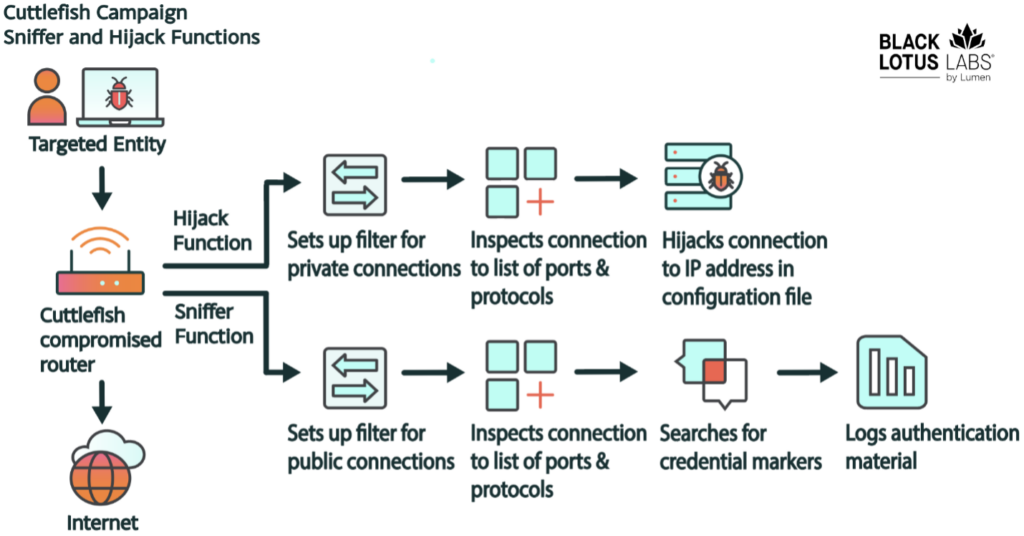
Security Affairs
Cuttlefish malware targets enterprise-grade and small office/home office (SOHO) routers to harvest public cloud authentication data.


DarkReading
The newly discovered malware, which has so far mainly targeted Turkish telcos and has links to HiatusRat, infects routers and performs DNS and HTTP hijacking attacks on connections to private IP addresses


HACKRead
Uncover the "Muddling Meerkat," a China-linked threat actor manipulating the DNS. Infoblox research reveals a sophisticated group with deep DNS expertise and potential ties to the Great Firewall. Learn their tactics and how to stay protected.
Loading more articles....