

Infosecurity News
NIST Confusion Continues as Cyber Pros Complain CVE Uploads Stopped
Several software security experts have told Infosecurity that no new vulnerabilities have been added to the US NVD since May 9


Infosecurity News
Several software security experts have told Infosecurity that no new vulnerabilities have been added to the US NVD since May 9


Cyber Security News
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has announced a new initiative called "Vulnrichment" aimed at enriching Common Vulnerabilities and Exposures (CVE) records with additional metadata to help organizations better prioritize vulnerability remediation efforts.


Infosecurity News
CISA launched a new software vulnerability enrichment program to fill the gap left by NIST’s National Vulnerability Database backlog


SecurityWeek
Horizon3.ai's AISaaS-based, AI-assisted penetration service allows proactive defensive action against exploitation of new vulnerabilities.

Infosecurity News
The growth of software supply chain attacks pushed vulnerability exploits to the third most used initial access method, Verizon found


The Record
Sens. Mark Warner and Thom Tillis want to see changes in the federal NVD to reflect how different AI systems can be from traditional software and hardware.


SecurityWeek
VulnCheck banks $8 million in early stage capital to build 'exploit intelligence' technologies and services.

Infosecurity News
An open letter signed by 50 cybersecurity practitioners requires the US Congress to support NIST in restoring operations at the National Vulnerability Database


The Hacker News
Discover the implications for software developed with tools like GitHub Copilot. Learn more about securing your code against AI vulnerabilities.


SecurityWeek
A critical vulnerability in multiple programming languages allows attackers to inject commands in Windows applications.


The Cyber Express
An active exploitation of critical vulnerabilities in D-Link Network Attached Storage (NAS) devices has raised concerns for D-Link users exposing


CyberSecurity Dive
CVE overload and a lengthy backlog has meant the federal government’s repository of vulnerability data can’t keep up with today’s threat landscape.


The Cyber Express
Security researchers recently discovered LG WebOS vulnerabilities, potentially exposing millions of LG smart TVs to exploitation. The vulnerabilities, ranging from


DarkReading
Our collection of the most relevant reporting and industry perspectives for those guiding cybersecurity strategies and focused on SecOps. Also included: Dealing with a Ramadan cyber spike; funding Internet security; and Microsoft's Azure AI changes.


SecurityWeek
The CVE List and the National Vulnerability Database (NVD) can no longer be considered a single central source of vulnerability truth.


DarkReading
The National Vulnerability Database can't keep up, and the agency is calling for a public-private partnership to manage it going forward.


The Cyber Express
A critical vulnerability has been discovered within the XZ Utils library (a command line tool for compressing and decompressing XZ


The Cyber Express
A critical security flaw, identified as CVE-2023-50969, has recently been discovered in Imperva SecureSphere, a popular on-premise Web Application Firewall


Cyber Security News
A backdoor was recently discovered in the xz-utils package versions 5.6.0 to 5.6.1, shocking the Linux community. This poses a significant threat to the security of Linux distributions, including Kali Linux.


SC Magazine
NIST says it has asked partner agencies for assistance as it works on a long-term solution to keeping the vital CVE database up to date.


SecurityWeek
Vulnerability (CVE-2024-28085) in core Linux system utilities package util-linux allows attackers to leak user passwords using fake prompts.

The Record
As a backlog in the National Vulnerability Database has grown, industry experts have sounded the alarm about changes to an "integral" piece of cybersecurity infrastructure.

CyberScoop
The National Vulnerability Database has ceased some of its work, but some experts fear the formation of a consortium to address its problems lacks sufficient urgency.


Infosecurity News
After months of speculation, NIST has finally confirmed its intention to establish an industry consortium to develop the NVD in the future


SecurityWeek
In just the first two months of 2024, threat intelligence firm Flashpoint has logged dramatic increases in all major cyber threat indicators.


SecurityWeek
Disputed Ray AI framework vulnerability exploited to steal information and deploy cryptominers on hundreds of clusters.


SecurityWeek
Apple has released iOS 17.4.1 and macOS Sonoma 14.4.1 with patches for an arbitrary code execution vulnerability.


The Cyber Express
Threat actor Hunt3rkill3rs1 is offering a CVE-2024-21762 exploit sale on a dark web forum. The exploit is designed to capitalize

DarkReading
NVD may be in peril and while alternatives exist, enterprise security managers will need to plan accordingly to stay on top of new threats.


CSO
Over 300,000 internet systems running on UDP protocols are potential victims of the loop DoS attacks.


The Hacker News
Atlassian has issued patches for over 25 security issues, including a critical SQL injection bug (CVE-2024-1597) in Bamboo Data Center & Server.


The Cyber Express
Unknown hackers exploited vulnerabilities in Ivanti software to infiltrate the Cybersecurity and Infrastructure Security Agency (CISA), leading to a significant


Trend Micro
Jenkins, a popular open-source automation server, was discovered to be affected by a file read vulnerability, CVE-2024-23897.


HACKRead
A disruption at the National Institute of Standards and Technology (NIST) is causing problems for organizations that rely on its National Vulnerability Database (NVD).


SC Magazine
Crucial enrichment data is not being added to NVD entries as NIST works through a “transition” process.


Infosecurity News
Vulnerability data has stopped being added to the most widely used software vulnerability database for over a month, putting organizations at risk – and nobody knows why


SecurityWeek
Fortinet has released patches for critical code execution vulnerabilities in FortiOS, FortiProxy, and FortiClientEMS.


SecurityWeek
Use of AI to help vulnerability prioritization approaches suggests an exciting future for AI-assisted methods to vulnerability triaging.


The Cyber Express
In a recent security advisory, VMware has urgently recommended the removal of the enhanced authentication plug-in (EAP) due to the


The Hacker News
CISA has identified a medium-severity security flaw affecting Roundcube email software, categorized as CVE-2023-43770.


SC Magazine
The FortiOS bug was patched a day after Volt Typhoon exploitation of past bugs was revealed.


Infosecurity News
The flaw allows the installation of malware that operates at the firmware level

DarkReading
However, not everyone agrees with the NVD's assessment of CVE-2023-40547 being a near-maximum severity bug.


Bleeping Computer
It turns out that critical Fortinet FortiSIEM vulnerabilities tracked as CVE-2024-23108 and CVE-2024-23109 are not new and have been published this year in error.


DarkReading
Security holes in a big data tool can open the door to big data compromises.


The Hacker News
Learn how SecurityHQ's innovative SHQ Response Platform is revolutionizing risk management, with insights from Deodatta Wandhekar.


The Hacker News
Chrome Zero-Day Alert! Update NOW to patch a critical flaw exploited by hackers. This memory leak bug lets attackers steal your secrets.


DarkReading
A printer bug could lead to much worse, in IT networks without proper segmentation.


The Hacker News
A zero-day security flaw discovered in Apache OfBiz ERP system could allow unauthorized access.


HACKRead
Flashpoint’s latest report redefines the Vulnerability Management system and challenges the current standards set by CVE.


Cyber Security News
Trend Micro researchers recently revealed Apache ActiveMQ vulnerability (CVE-2023-46604) was actively exploited.


Cyber Security News
Welcome to the Cyber Security News Recap, a weekly publication by Cyber Writes. Our aim is to bring you up-to-date information on the latest developments in the field of cybersecurity.


Cyber Security News
Google Chrome Stable Channel Update for Desktop version 119.0.6.45.159 for Mac and Linux and 119.0.6045.159/.160 for Windows.

Bleeping Computer
This article takes a deep dive into the OWASP Top 10 and advises on how to test your web applications for susceptibility to these security risks.


DarkReading
The latest vulnerability severity scoring system addresses gaps in the previous version; here's how to get the most out of it.

The Hacker News
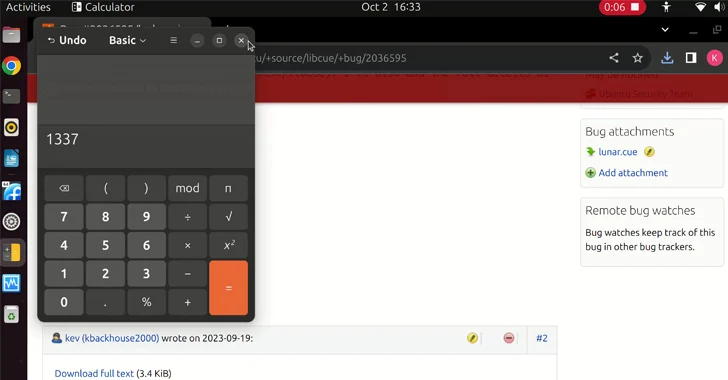
Heads up, Linux users! A new critical vulnerability in the libcue library exposes GNOME Linux systems to remote code execution (RCE) attacks.

Cyber Security News
Apple has discovered a Zero-day vulnerability affecting iOS and iPadOS versions earlier than 17.0.3 which could allow threat actors to elevate their privileges.


Cyber Security News
Google Chrome version 117.0.5938.132 for Windows, Mac, and Linux has been set to release with multiple bug fixes and features.


DarkReading
One of the already-patched flaws enables elevation of privilege, while the other enables remote code execution.


Cyber Security News
Google released a security fix for a critical vulnerability that affected Google Chrome for Windows, macOS, and Linux.

The Hacker News
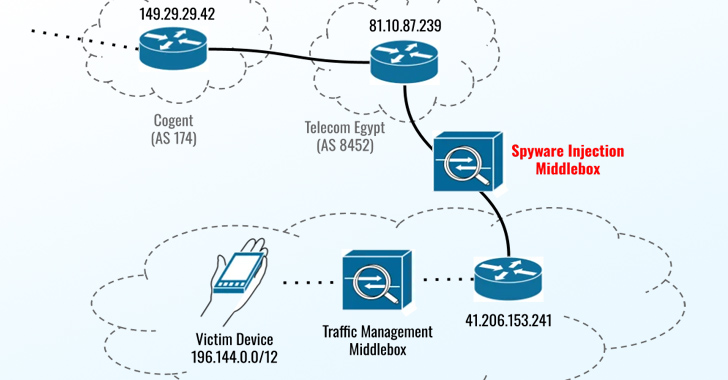
iPhone spyware attack! Former Egyptian parliament member Ahmed Eltantawy targeted by Predator spyware using 3 recent zero-day vulnerabilities.


Cyber Security News
Three new vulnerabilities have been discovered in multiple Apple products, including iPhone (iOS), iPadOS, watchOS, Safari, macOS and multiple versions of these products. These vulnerabilities have been confirmed as a Zero-Day by Apple.

Cyber Security News
Two vulnerabilities have been identified on three Atos Unify OpenScape products, SBC, Branch, and BCF, which are associated with Missing authentication.


Cyber Security News
Recent reports indicate that an arbitrary code execution vulnerability has been discovered in a third-party Antivirus uninstaller module of Trend Micro Apex One.


The Hacker News
Mozilla is also rushing to fix a zero-day vulnerability (CVE-2023-4863) that is actively exploited in browsers.


Cyber Security News
Citrix ShareFile is a cloud-based platform used by organizations to store and share large files. It also allows users to create branded, password-protected files through their services.


Cyber Security News
Ivanti Avalanche has been reported with several vulnerabilities ranging between Medium to High severity. Vulnerabilities include Arbitrary file upload remote code execution.


Infosecurity News
Tracked as CVE-2023-34034, the flaw has a CVSS score of 9.8


CSO
The ML-based Exploit Prediction Scoring System overcomes limitations of legacy vulnerability scoring systems, helping security teams identify systems at greatest risk of attack.

Cyber Security News
The Zenbleed vulnerability that is documented recently puts more than 60 percent of AWS environments at risk, impacting AMD Zen 2 processors.


Infosecurity News
Attackers could covertly gain remote control of devices


SecurityWeek
CISA adds 6 Samsung mobile device flaws to its known exploited vulnerabilities catalog and they have been exploited by a spyware vendor.


SecurityWeek
Use-after-free and OS command injection vulnerabilities reach the top five most dangerous software weaknesses in the 2023 CWE Top 25 list.


Infosecurity News
CWE Top 25 list is calculated from two years of vulnerability data

The Hacker News
Attention all software developers and programmers! MITRE's Top 25 list of dangerous software weaknesses for 2023 is here.


Bleeping Computer
MITRE shared today this year's list of the top 25 most dangerous weaknesses plaguing software during the previous two years.


Naked Security
Lots to learn this week – listen now! (Full transcript inside.)


Naked Security
“Do as we say, not as we do!” – The patches took ages to come out, but don’t let that lure you into taking ages to install them.


Infosecurity News
Volume of new vulnerabilities has increased three-fold in a decade


The Hacker News
Google has released a security update to fix a new high-severity zero-day vulnerability in Chrome browser that is being actively exploited by hackers


DataBreaches
In July 2021, Professional Business Systems, Inc. d/b/a Practicefirst Medical Management Solutions and PBS Medcode Corp., a medical management company that...


The Hacker News
Google rolls out emergency fixes to tackle another high-severity zero-day flaw in Chrome web browser.


Infosecurity News
Palo Alto report warns of an expanding cloud attack surface


The Hacker News
Google addresses actively exploited Chrome zero-day flaw (CVE-2023-2033) in an out-of-band update


CSO
Mandiant Proactive Exposure Management combines a suite of capabilities to effect exposure hunting, threat correlation, penetration testing, and real-time intrusion defense.


CSO
Mandiant Proactive Exposure Management combines a suite of capabilities to effect exposure hunting, threat correlation, penetration testing, and real-time intrusion defense.


The Hacker News
Wazuh open-source platform combines XDR & SIEM capabilities to protect businesses from evolving threats.


DarkReading
Differences in how the National Vulnerability Database (NVD) and vendors score bugs can make patch prioritization harder, study says.


Cyber Security News
Updates for QNAP's network-attached storage (NAS) systems have been released to address a critical security flaw that might allow arbitrary code injection.


Infosecurity News
Vulnerability affects QTS and QuTS Hero firmware


The Hacker News
QNAP has released security updates to address a critical vulnerability (CVE-2022-27596 / CVSS 9.8) in the NAS devices.


Bleeping Computer
Regular penetration testing is an important step in developing secure web applications. Outpost24 PTaaS solution is an on-demand, pay-as-you-go service that provides access to specialist external pen testers and tools that work as extensions of your in-house SecOps team.

DarkReading
The critical flaw in BackupBuddy is one of thousands of security issues reported in recent years in products that WordPress sites use to extend functionality.


Infosecurity News
The research also found that vendor self-disclosures increased by 69%

CyberScoop
The debate is over whether the provision is unrealistic or if it's a game changing move to cut down on software vulnerabilities.


The Hacker News
Software vulnerabilities are a major threat to organizations today. Taking the Risk-Based Approach to Vulnerability Patching


Security Affairs
The MITRE organization published the 2022 CWE Top 25 most dangerous software weaknesses. The MITRE shared the list of the 2022 top 25 most common and dangerous weaknesses, it could help organizations to assess internal infrastructure and determine their surface of attack. The presence of these vulnerabilities within the infrastructure of an organization could potentially expose it to […]


Bleeping Computer
MITRE shared this year's top 25 most common and dangerous weaknesses impacting software throughout the previous two calendar years.


Latest Hacking News
Researchers discovered a critical vulnerability affecting the Apple Game Center that allowed authentication bypass. The bug typically existed in the Parse Server, exposing it to remote attacks. Apple Game Center Vulnerability According to a recent advisory on


Infosecurity News
Ivanti observed a 7.6% rise in the number of vulnerabilities tied to ransomware, most of which were exploited by Conti
Loading more articles....