

SecurityWeek
Botnet Disrupted by FBI Still Used by Russian Spies, Cybercriminals
A botnet dismantled in January and used by Russia-linked APT28 consisted of more than just Ubiquiti Edge OS routers.


SecurityWeek
A botnet dismantled in January and used by Russia-linked APT28 consisted of more than just Ubiquiti Edge OS routers.

Ars Technica
How and why nation-state hackers and cybercriminals coexist in the same router botnet.


Trend Micro
This blog entry aims to highlight the dangers of internet-facing routers and elaborate on Pawn Storm's exploitation of EdgeRouters, complementing the FBI's advisory from February 27, 2024.


The Hacker News
Cybersecurity researchers have uncovered a targeted cyber attack against Ukraine that leveraged a 7-year-old Microsoft Office flaw to deploy Cobalt St


Cyber Security News
Researchers identified a cyberattack by the Sandworm group targeting critical infrastructure in Ukraine in March 2024, which aimed to disrupt

Bleeping Computer
Russian hacker group Sandworm aimed to disrupt operations at around 20 critical infrastructure facilities in Ukraine, according to a report from the Ukrainian Computer Emergency Response Team (CERT-UA).


The Hacker News
Xeno RAT, a new player in the malware scene, boasts alarming features for remote system exploitation. Learn more about its impact on Windows systems.

.webp)
Cyber Security News
A new sophisticated malware has been discovered which is written in C# and has sophisticated functionalities.

The Hacker News
North Korean APT Kimsuky caught using new Golang-based info stealer "Troll Stealer" and malware "GoBear," both signed with stolen certificates.


SecurityWeek
Researchers at Qualys call attention to a vulnerability in Linux’s GNU C Library (glibc) that allows full root access to a system.


Trend Micro
Based on our estimates, from approximately April 2022 until November 2023, Pawn Storm attempted to launch NTLMv2 hash relay attacks through different methods, with huge peaks in the number of targets and variations in the government departments that it targeted.


The Hacker News
Cybersecurity experts reveal the inner workings of SystemBC's command-and-control (C2) server, a dangerous malware available on the dark web.


The Cyber Express
The Cybersecurity and Infrastructure Security Agency (CISA) has published three advisories addressing security issues, vulnerabilities, and potential exploits in Industrial


The DFIR Report
This report is a little different than our typical content. We were able to analyze data from a perspective we typically don’t get to see… a threat actor’s host! In … Read More


Cyber Security News
Best security solutions for Marketers: 1. Perimeter 81 2. Surfshark3. Private Internet Access 4. Malwarebytes 5. CyberGhost 6. GoodAccess

Bleeping Computer
A proxy botnet called 'Socks5Systemz' has been infecting computers worldwide via the 'PrivateLoader' and 'Amadey' malware loaders, currently counting 10,000 infected devices.


Bleeping Computer
An updated version of the MATA backdoor framework was spotted in attacks between August 2022 and May 2023, targeting oil and gas firms and the defense industry in Eastern Europe.


The Hacker News
Ukraine's CERT-UA discovered threat actors targeting 11 telecom providers between May and September 2023. The attacks caused service interruptions.


Bleeping Computer
The state-sponsored Russian hacking group tracked as 'Sandworm' has compromised eleven telecommunication service providers in Ukraine between May and September 2023.


Bleeping Computer
curl 8.4.0 has been released to patch and release details on a hyped up high-severity security vulnerability (CVE-2023-38546), easing week-long concerns regarding the flaw's severity.


Cyber Security News
Curl command line tool posted a pre-announcement regarding two vulnerabilities that affected both the curl tool and the libcurl library.

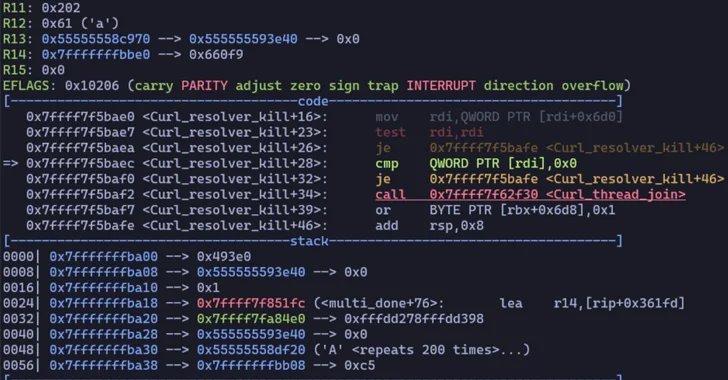
The Hacker News
Security Advisory : Two major security flaws in the Curl data transfer library exposed.

CyberScoop
The flaw in the widely used open source software package was expected to be the next great catastrophe in computer security.


DarkReading
Touted for days as potentially catastrophic, the curl flaws only impact a narrow set of deployments.

Infosecurity News
The flaw impacts curl and libcurl, causing SOCKS5 proxy handshake to suffer heap buffer overflow


SecurityWeek
Flaw poses a direct threat to the SOCKS5 proxy handshake process in cURL and can be exploited remotely in some non-standard configurations.


CyberSecurity Dive
The widely used tool has a vulnerability that can be exploited to cause a heap-based buffer overflow issue.


Bleeping Computer
In a new HiatusRAT malware campaign, threat actors have targeted a server belonging to the U.S. Department of Defense in what researchers described as a reconnaissance attack.


Security Affairs
Threat actors employed a new variant of the SystemBC malware, named DroxiDat, in attacks aimed at African critical infrastructure. Researchers from Kaspersky’s Global Research and Analysis Team (GReAT) reported that an unknown threat actor used a new variant of the SystemBC proxy malware, named DroxiDat, in an attack against a power generation company in southern Africa. SystemBC was […]


The Hacker News
Russian threat actors suspected in cyber attack on South African power company using a new variant of the SystemBC malware called DroxiDat


Security Affairs
The AVRecon botnet relies on compromised small office/home office (SOHO) routers since at least May 2021. In early July, researchers from Lumen Black Lotus Labs discovered the AVRecon botnet that targets small office/home office (SOHO) routers and infected over 70,000 devices from 20 countries. Threat actors behind the campaign aimed at building a botnet to […]


Cyber Security News
Surprisingly, Microsoft remains unaware of how Chinese hackers acquired an inactive Microsoft account signing key to breach Exchange Online and Azure AD accounts.


Cyber Security News
Best Business VPN (VPN for Business): 1. Perimeter81 2. ExpressVPN 3. NordVPN 4. Surfshark 5. CyberGhost 6. Private Internet Access (PIA)


Cyber Security News
After an internet-exposed router is compromised, a loader script is deployed to deliver GobRAT, which disguises itself as the Apache daemon process (apached) to avoid being detected.


Security Affairs
A new Golang remote access trojan (RAT), tracked as GobRAT, is targeting Linux routers in Japan, the JPCERT Coordination Center warns. JPCERT/CC is warning of cyberattacks against Linux routers in Japan that have been infected with a new Golang remote access trojan (RAT) called GobRAT. Threat actors are targeting Linux routers with publicly exposed WEBUI to execute […]

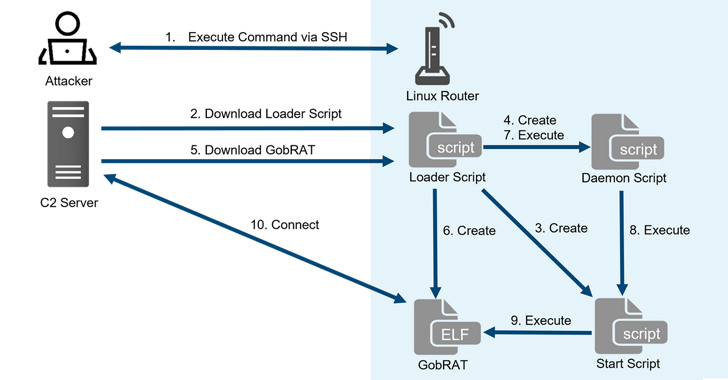
The Hacker News
Linux routers in Japan are under attack by a sneaky new villain named GobRAT.

Ars Technica
Following in the footsteps of VPNFilter, new firmware obscures hackers' endpoints.


Security Affairs
US Cybersecurity and Infrastructure Security Agency (CISA) added seven new flaws to its Known Exploited Vulnerabilities catalog. U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added the following three new issues to its Known Exploited Vulnerabilities Catalog: CVE-2023-25717 – Ruckus Wireless Access Point (AP) software contains an unspecified vulnerability in the web services component. If the […]

The Hacker News
A nascent botnet called Andoryu is now exploiting a critical (CVE-2023-25717) vulnerability to hijack Ruckus Wireless AP devices.


Infosecurity News
Tracked CVE-2023-25717, the flaw was recently exploited by the AndoryuBot botnet, says Fortinet


Security Affairs
A DDoS botnet dubbed AndoryuBot has been observed exploiting an RCE, tracked as CVE-2023-25717, in Ruckus access points. FortiGuard Labs researchers have recently observed a spike in attacks attempting to exploit the Ruckus Wireless Admin remote code execution vulnerability tracked as CVE-2023-25717. The activity is associated with a known DDoS botnet tracked as AndoryuBot that […]


Trend Micro
After months of dormancy, Earth Longzhi, a subgroup of advanced persistent threat (APT) group APT41, has reemerged using new techniques in its infection routine. This blog entry forewarns readers of Earth Longzhi’s resilience as a noteworthy threat.


Security Affairs
An ALPHV/BlackCat ransomware affiliate was spotted exploiting vulnerabilities in the Veritas Backup solution. An affiliate of the ALPHV/BlackCat ransomware gang, tracked as UNC4466, was observed exploiting three vulnerabilities in the Veritas Backup solution to gain initial access to the target network. Unlike other ALPHV affiliates, UNC4466 doesn’t rely on stolen credentials for initial access to victim environments. Mandiant […]


Bleeping Computer
An ALPHV/BlackCat ransomware affiliate was observed exploiting three vulnerabilities impacting the Veritas Backup product for initial access to the target network.


DarkReading
Two novel malware binaries, including "HiatusRAT," offer unique capabilities that point to the need for better security for companies' router infrastructure.


Bleeping Computer
An ongoing hacking campaign called 'Hiatus' targets DrayTek Vigor router models 2960 and 3900 to steal data from victims and build a covert proxy network.


Bleeping Computer
An ongoing hacking campaign called 'Hiatus' targets DrayTek Vigor router models 2960 and 3900 to steal data from victims and build a covert proxy network.


Trend Micro
In 2022, we discovered Earth Zhulong, a hacking group that has been targeting Vietnam's telecom, technology, and media sectors similar to another well-known threat actor. In this article, we unravel their new tactics, techniques and procedures that they apply on their misdeeds.


Trend Micro
In 2022, we discovered Earth Zhulong, a hacking group that has been targeting Asian firms similar to another well-known threat actor. In this article, we unravel their new tactics, techniques and procedures that they apply on their misdeeds.

Bleeping Computer
A previously unknown threat group has been targeting the customer service platforms of online gaming and gambling companies using social engineering to drop its custom implant.


Bleeping Computer
An Android banking malware named 'Godfather' has been targeting users in 16 countries, attempting to steal account credentials for over 400 online banking sites and cryptocurrency exchanges.


Trend Micro
This report examines the infection chain and the pieces of malware used by malicious actors in supply-chain attacks that leveraged trojanized installers of chat-based customer engagement platforms.


Bleeping Computer
A previously unknown Chinese APT (advanced persistent threat) hacking group dubbed 'Earth Longzhi' targets organizations in East Asia, Southeast Asia, and Ukraine.


Trend Micro
We looked into the campaigns deployed by a new subgroup of advanced persistent threat (APT) group APT41, Earth Longzhi. This entry breaks down the technical details of the campaigns in full as presented at HITCON PEACE 2022 in August.

SecurityWeek
New Maggie backdoor targeting MSSQL servers has already been found on hundreds of servers worldwide.


Security Affairs
Hundreds of Microsoft SQL servers all over the world have been infected with a new piece of malware tracked as Maggie. Security researchers Johann Aydinbas and Axel Wauer from the DCSO CyTec have spotted a new piece of malware, named Maggie, that has already infected over 250 Microsoft SQL servers worldwide. Most of the infected instances […]


Bleeping Computer
Security researchers have found a new piece of malware targeting Microsoft SQL servers. Named Maggie, the backdoor has already infected hundreds of machines all over the world.

SecurityWeek
Part of the Cicada group, Witchetty has been observed progressively updating its toolset in recent attacks against Middle Eastern and African targets.


Bleeping Computer
The BlackCat ransomware (aka ALPHV) isn't showing any signs of slowing down, and the latest example of its evolution is a new version of the gang's data exfiltration tool used for double-extortion attacks.


Trend Micro
Play is a new ransomware that takes a page out of Hive and Nokoyawa's playbook. The many similarities among them indicate that Play, like Nokoyawa, may be a Hive affiliate.

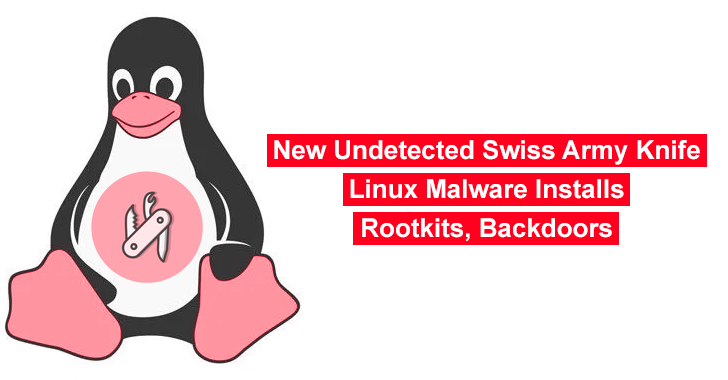
Cyber Security News
The Lightning Framework is a new malware that has previously gone undetected and targets Linux systems with its malicious code. Infected devices can be backdoored using SSH using this program as well as multiple types of rootkits can be deployed with it.


CSO
The Operation CuckooBees campaign used zero-day exploits to compromise networks and leveraged Windows' Common Log File System to avoid detection.


Bleeping Computer
A new BitRAT malware distribution campaign is underway, exploiting users looking to activate pirated Windows OS versions for free using unofficial Microsoft license activators.


The Hacker News
A new "B1txor20" Linux botnet has been discovered that spreads via the Log4J vulnerability and uses DNS tunnels for covert C2 communications.

Bleeping Computer
A recently discovered botnet under active development targets Linux systems, attempting to ensnare them into an army of bots ready to steal sensitive info, installing rootkits, creating reverse shells, and acting as web traffic proxies.


Bleeping Computer
"No logs" VPN provider TorGuard has reached a legal settlement with over two dozen movie studios that sued the company for encouraging piracy and copyright infringement. In the settlement, TorGuard has agreed to block BitTorrent traffic for its users.


Bleeping Computer
A group of hackers that security researchers call LightBasin has been compromising mobile telecommunication systems across the world for the past five years.


Bleeping Computer
A ransomware targeting an Israeli company has led researchers to track a portion of a ransom payment to a website promoting sensual massages.