

The Hacker News
North Korean Hackers Exploit Facebook Messenger in Targeted Malware Campaign
Kimsuky hackers launch new social engineering attack using fake Facebook accounts. Learn how they target activists via Messenger and deliver malware.


The Hacker News
Kimsuky hackers launch new social engineering attack using fake Facebook accounts. Learn how they target activists via Messenger and deliver malware.


The Cyber Express
Microsoft patched a zero-day vulnerability exploited by attackers to distribute QakBot and other malware payloads on susceptible Windows systems. Identified


SC Magazine
In this month’s release, Redmond patched 60 CVEs including two other zero-days and a SharePoint Server remote code execution vulnerability rated critical.

Bleeping Computer
Microsoft has fixed a zero-day vulnerability exploited in attacks to deliver QakBot and other malware payloads on vulnerable Windows systems.


Latest Hacking News
Torrance, California, May 13th, 2024, CyberNewsWireCriminal IP, a renowned Cyber Threat Intelligence (CTI) search engine developed by AI SPERA, has recently signed a technology partnership to exchange threat intelligence data based on domains and potentially

%20(1).webp)
Cyber Security News
"Our partnership with Quad9 is a recognition of the accuracy of Criminal IP's data," stated Byungtak Kang, CEO of AI SPERA.


Bleeping Computer
The Criminal IP Threat Intelligence (CTI) search engine to integrate with Quad9's threat-blocking service. Learn more from Criminal IP about how this integration can help you.


HACKRead
Torrance, California, May 13th, 2024, CyberNewsWire


SC Magazine
The “requests-darwin-lite” package was downloaded more than 400 times before its removal.


The Cyber Express
Google has brought together its Gemini AI model with its Mandiant cybersecurity unit and VirusTotal threat Intelligence to enhance threat


CSO
The new addition to Google Cloud Security is designed to give security teams information to inform approaches to protecting against external threats, managing attack surfaces, and mitigating digital risks.


SC Magazine
Large language models (LLM) provide context that could expose overlooked threats.


SecurityWeek
Google rolls out new threat-intel and security operations products and looks to the magic of AI to tap into the booming cybersecurity market.

.webp)
Cyber Security News
A new variant of the notorious Adload malware has been discovered to bypass the latest updates to Apple's built-in antivirus, XProtect.


The Hacker News
Are you confident your vulnerability scanner isn't leaving blind spots in your attack surface? Uncover the limitations of relying on a single scanner

The Hacker News
Researchers have uncovered a new Android malware called Wpeeper that uses compromised WordPress sites to hide its true command-and-control servers.


SecurityWeek
Chinese cybersecurity firm QAX XLab uncovered an Android trojan that hides its command-and-control server behind compromised WordPress sites.

.webp)
Cyber Security News
This sophisticated backdoor Trojan to infiltrate Android systems & execute a malicious commands, posing a threat to unsuspecting users.


Cyber Security News
Google has introduced Gemini 1.5 Pro for malware analysis, an advanced AI tool capable of processing up to 1 million tokens.

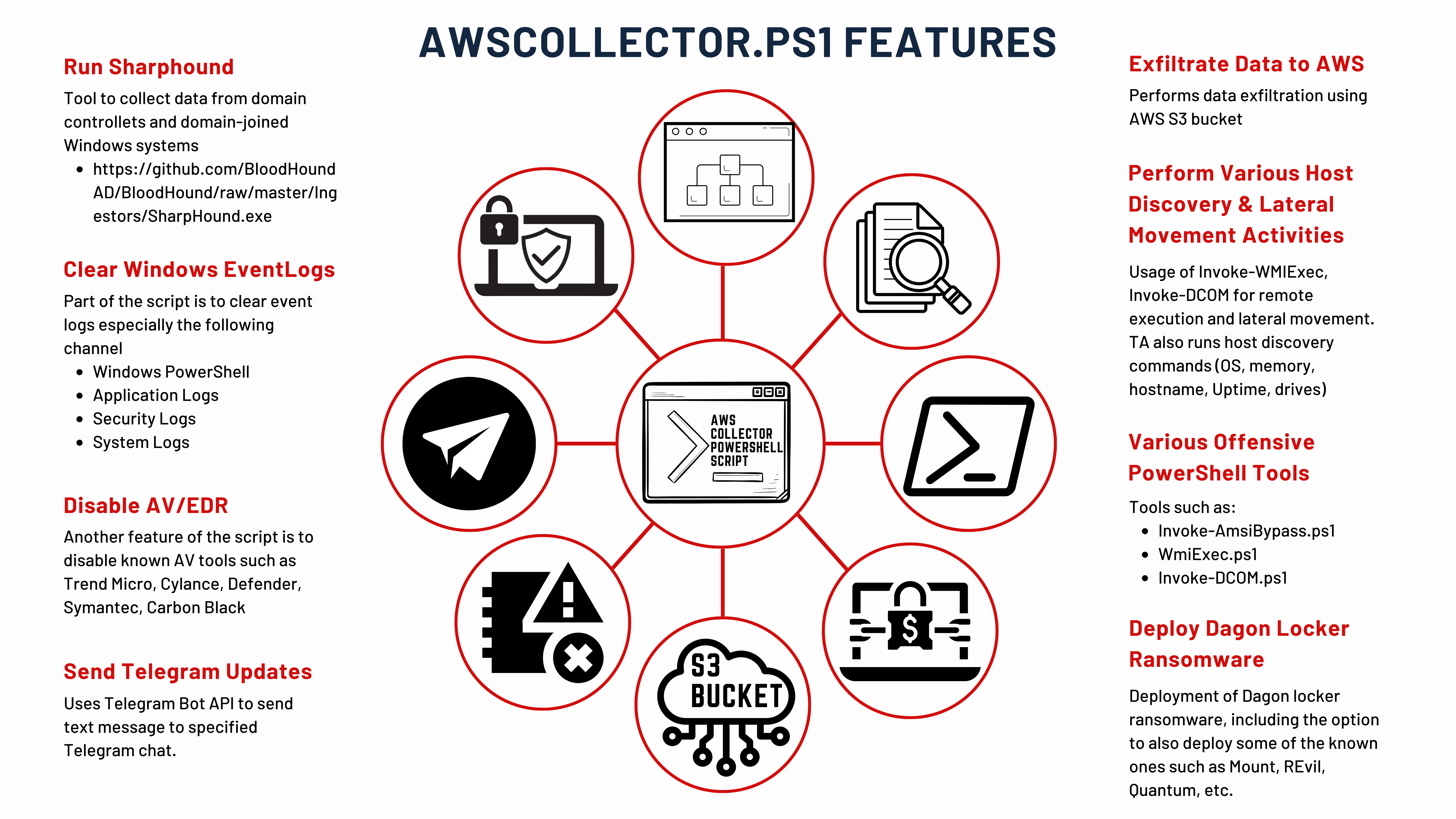
The DFIR Report
Key Takeaways In August 2023, we observed an intrusion that started with a phishing campaign using PrometheusTDS to distribute IcedID. IcedID dropped and executed a Cobalt Strike beacon, which was … Read More

Security Affairs
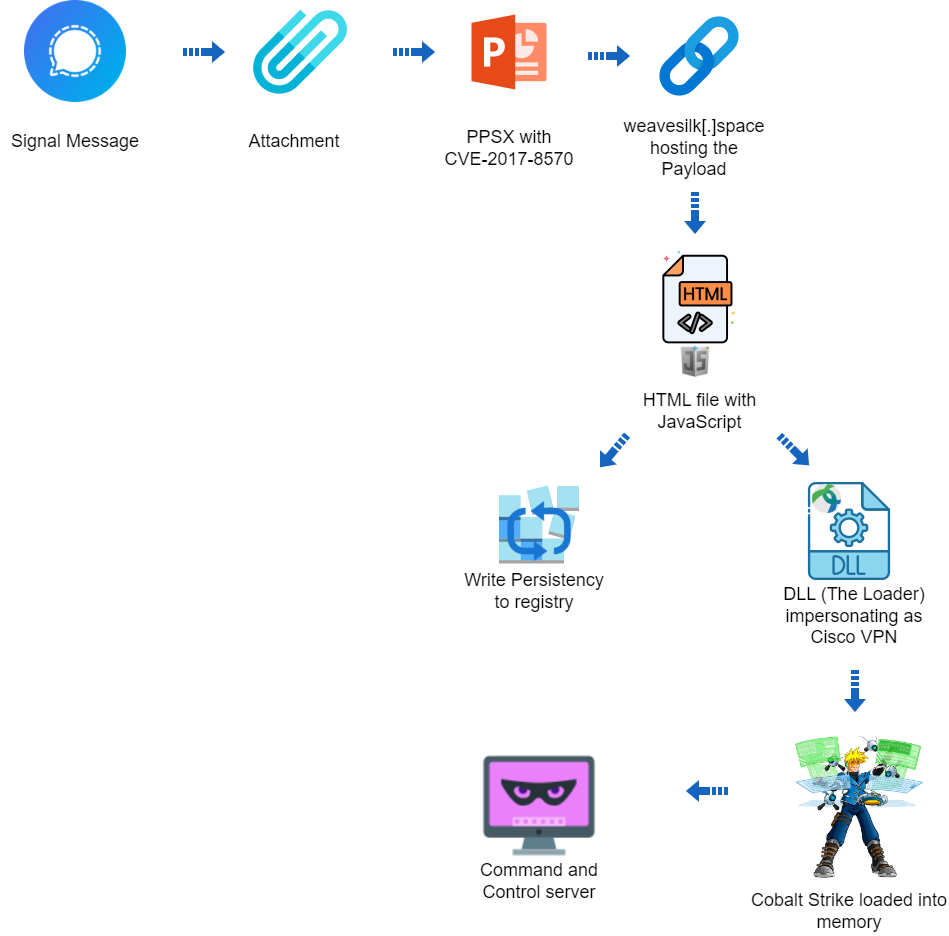
A hacking campaign targeted Ukraine exploiting a seven-year-old vulnerability in Microsoft Office to deliver Cobalt Strike.


The Cyber Express
CRIL Researchers observed a new android banking trojan 'Brokewell,' being distributed through a phishing site disguised as the official Chrome


The Hacker News
A sophisticated malware called GuptiMiner has been leveraging a flaw in eScan antivirus updates to spread backdoors and crypto miners across corporate


Bleeping Computer
Criminal IP is integrating its Threat Intelligence (CTI) search platform in SUMO Logic's cloud security platforms in a new partnership. Learn more from Criminal IP about how this integration can help SUMO Logic customers.


Bleeping Computer
You rarely root for a cybercriminal, but a new malware campaign targeting child exploiters doesn't make you feel bad for the victims.


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


The Hacker News
Ukrainian government networks have been compromised by the OfflRouter malware since 2015. This malware is causing sensitive documents to be exposed.

The Record
Researchers have discovered more than 100 Ukrainian documents uploaded to a public repository which were infected with malicious code.

CyberScoop
A virus dating to 2015 is still hitting targets in Ukraine, showing its enduring power.


The Record
Researchers are WithSecure have provided more detail on a backdoor they call Kapeka, which Russian state-backed hackers have been using since 2022.

Security Affairs
Researchers warn of a renewed cyber espionage campaign targeting users in South Asia with the Apple iOS spyware LightSpy


The Hacker News
A sophisticated cyber-espionage campaign has re-emerged, targeting South Asia with an iOS spyware implant called LightSpy.

Security Affairs
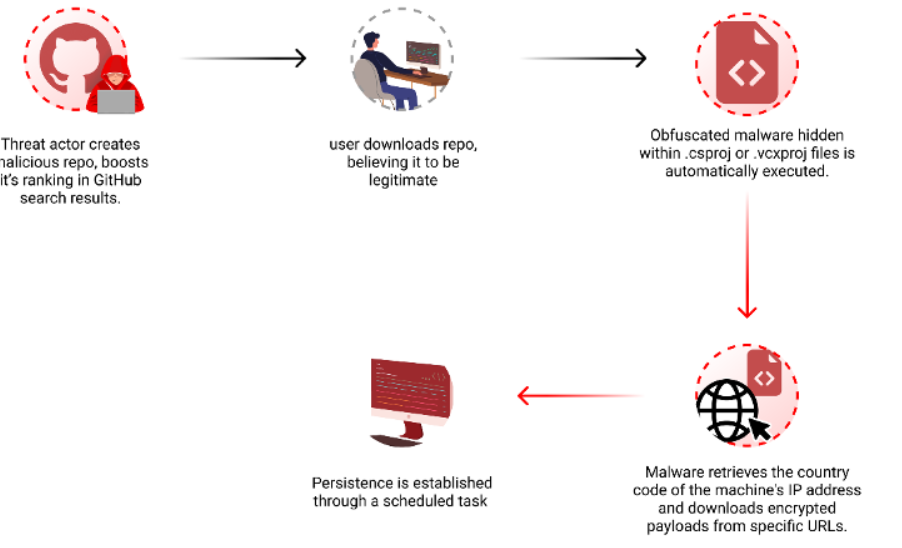
Researchers warn threat actors are manipulating GitHub search results to target developers with persistent malware.


DarkReading
But just how the government differentiates its platform from similar private-sector options remains to be seen.


Bleeping Computer
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has released a new version of "Malware Next-Gen," now allowing the public to submit malware samples for analysis by CISA.


DarkReading
North Korean hackers break ground with new exploitation techniques for Windows and macOS.


DarkReading
North Korean hackers break ground with new exploitation techniques for Windows and macOS.

Infosecurity News
Distribution vectors of the Raspberry Robin worm now include Windows Script Files (WSF) alongside other methods like USB drives


Security Affairs
Microsoft addressed two zero-day vulnerabilities (CVE-2024-29988 and CVE-2024-26234) actively exploited by threat actors to deliver malware


The Hacker News
Researchers uncover a fresh wave of the Raspberry Robin campaign spreading malware through malicious Windows Script Files (WSFs) since March 2024.


Bleeping Computer
Threat actors are abusing GitHub automation features and malicious Visual Studio projects to push a new variant of the "Keyzetsu" clipboard-hijacking malware and steal cryptocurrency payments.


CyberNews
Google is integrating generative AI into the Google Cloud to assist users across its various products and platforms – including its new Gemini-driven security platform.


Bleeping Computer
A Romanian botnet group named 'RUBYCARP' is leveraging known vulnerabilities and performing brute force attacks to breach corporate networks and compromise servers for financial gain.


CSO
The group was discovered recently through Sysdig honeypots as it attempted to exploit a Laravel vulnerability.


DarkReading
A Babuk variant has been involved in at least four attacks on VMware EXSi servers, in one case demanding $140 million from a Chilean data center company.

.webp)
Cyber Security News
StrelaStealer malware identified, targeting Spanish-speaking users with the primary aim of pilfering email account credentials.


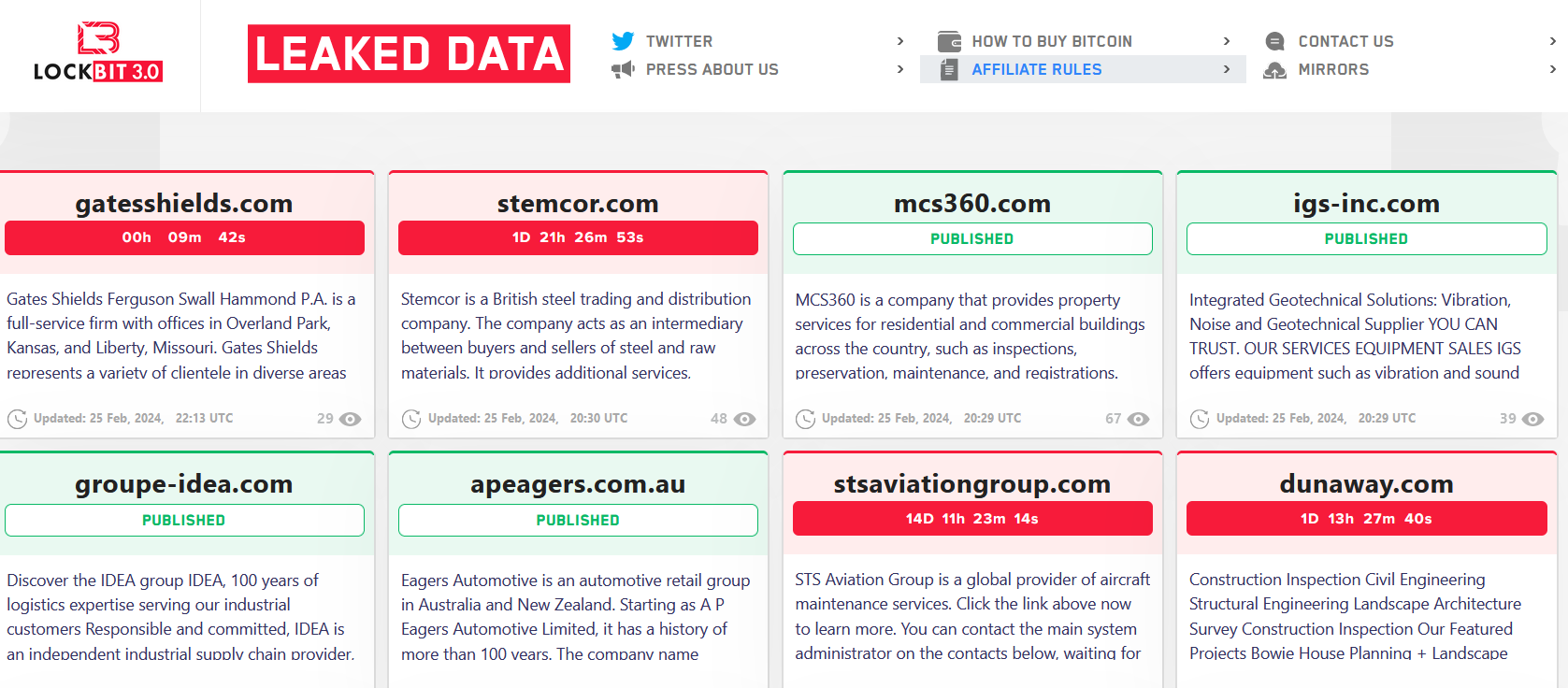
Trend Micro
Our new article provides key highlights and takeaways from Operation Cronos' disruption of LockBit's operations, as well as telemetry details on how LockBit actors operated post-disruption.

Security Affairs
Experts warn of info stealer malware, including Atomic Stealer, targeting Apple macOS users via malicious ads and rogue websites.


The DFIR Report
Key Takeaways We provide a range of services, one of which is our Threat Feed, specializing in monitoring Command and Control frameworks like Cobalt Strike, Metasploit, Sliver, Viper, Mythic, Havoc, … Read More

.webp)
Cyber Security News
Hackers have been found leveraging weaponized virtual hard disk (VHD) files to deploy the notorious Remote Control Software (RAT), Remcos.


Bleeping Computer
A new hacking campaign dubbed "ShadowRay" targets an unpatched vulnerability in Ray, a popular open-source AI framework, to hijack computing power and leak sensitive data from thousands of companies.


DarkReading
Companies trust lawyers with the most sensitive information they've got. Attackers are aiming to exploit that bond to deliver malware.

Security Affairs
A new variant of the Russia-linked wiper AcidRain, tracked as AcidPour, was spotted targeting Linux x86 devices.


Bleeping Computer
A new destructive malware named AcidPour was spotted in the wild, featuring data-wiper functionality and targeting Linux x86 IoT and networking devices.

Security Affairs
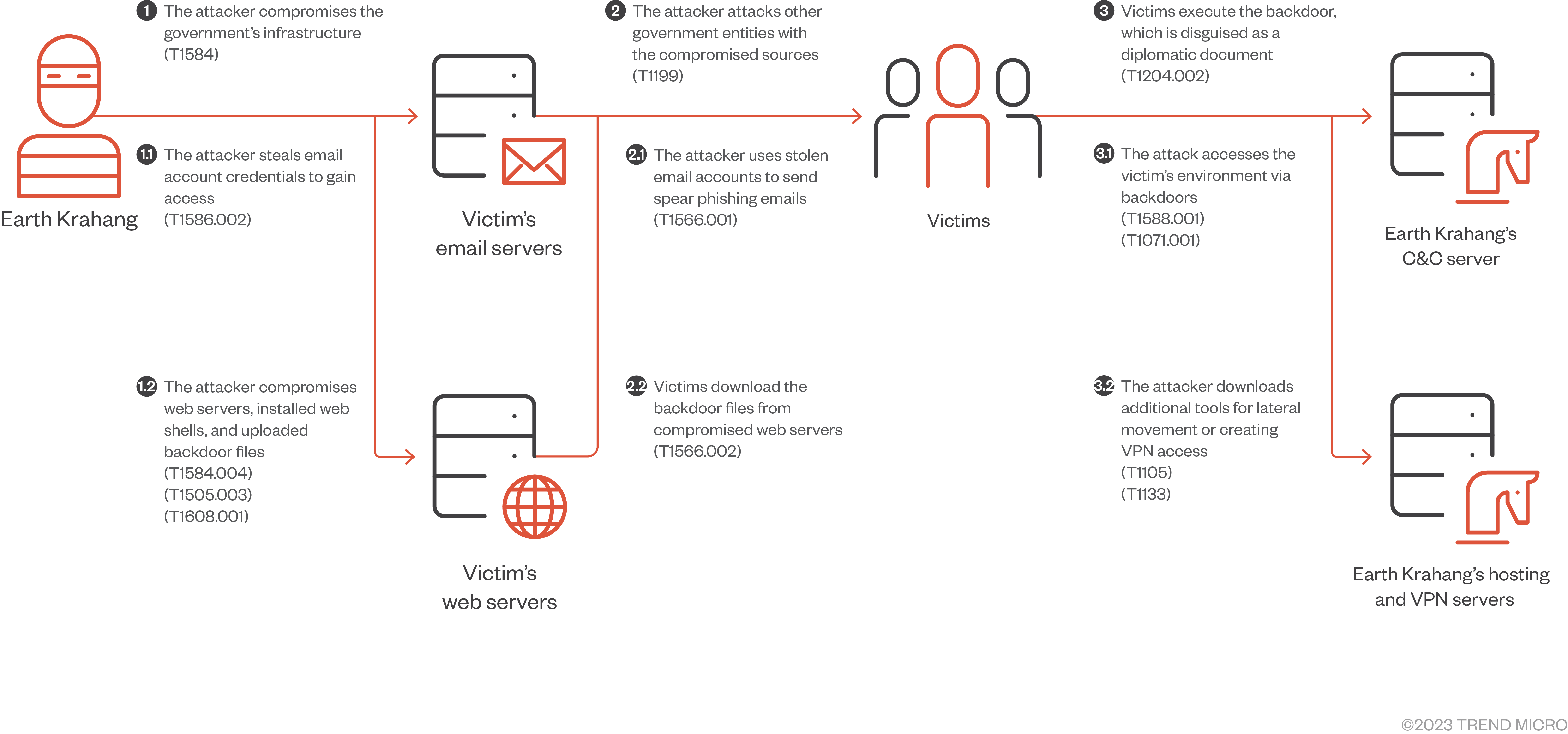
Trend Micro uncovered a sophisticated campaign conducted by Earth Krahang APT group that breached 70 organizations worldwide.


Trend Micro
Since early 2022, we have been monitoring an APT campaign that targets several government entities worldwide, with a strong focus in Southeast Asia, but also seen targeting Europe, America, and Africa.


The Cyber Express
In the final week of January 2024, CGSI (Cyble Global Sensor Intelligence) uncovered a potential exploitation of an Aiohttp vulnerability


SecurityWeek
Restoro and Reimage agree to a $26 million settlement after selling fake antivirus and tech services to undercover FTC agents.


SC Magazine
The variant performs 65 million data copies as a delay tactic and employs dynamic API resolution.


Bleeping Computer
Tech support companies Restoro and Reimage will pay $26 million to settle charges that they used scare tactics to trick their customers into paying for unnecessary computer repair services.

.png)
Cyber Security News
Threat actors target Notepad++ as it is a widely used text editor among developers and users, offering a large potential victim pool.


Ars Technica
Discovery means that NerbianRAT is cross-platform used by for-profit threat group.


Cyber Security News
COM (Component Object Model) hijacking is a technique in which threat actors exploit the core architecture of Windows by adding a new value on

Security Affairs
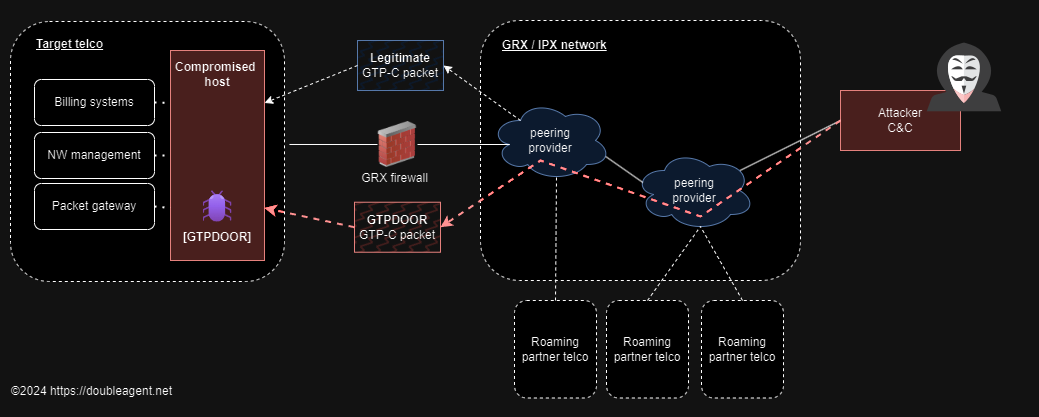
Researcher HaxRob discovered a previously undetected Linux backdoor named GTPDOOR, designed to target telecom carrier networks.

Bleeping Computer
Security researcher HaxRob discovered a previously unknown Linux backdoor named GTPDOOR, designed for covert operations within mobile carrier networks.


HACKRead
It is worth noting that the notorious Bifrost RAT, also known as Bifrose, was originally identified two decades ago in 2004.

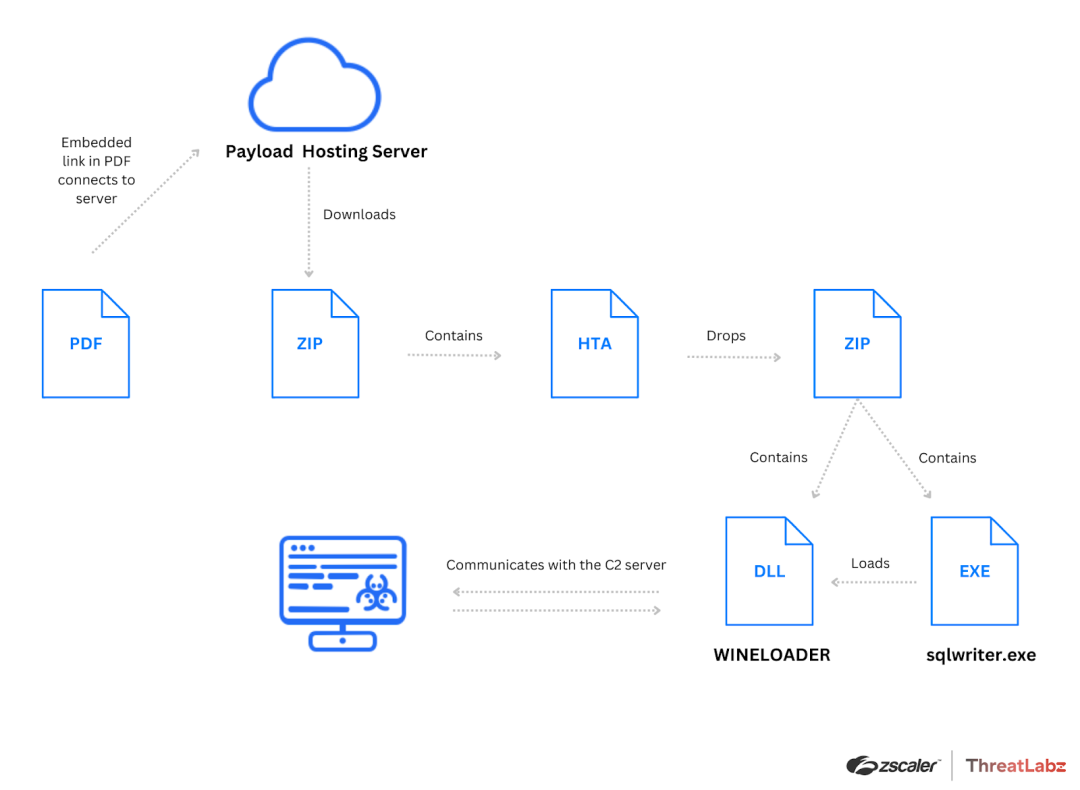
Security Affairs
A new threat actor, tracked as dubbed SPIKEDWINE, has been observed targeting officials in Europe with a previously undetected backdoor.


The Hacker News
Discover the Stealthy New Malware Targeting Telecom Networks! GTPDOOR uses GPRS Tunnelling Protocol for unseen levels of control.

Security Affairs
Experts warn that the LockBit ransomware group has started using updated encryptors in new attacks, after recent law enforcement operation.


The Hacker News
SPIKEDWINE cyber group targets European officials with sophisticated WINELOADER backdoor.


Bleeping Computer
The LockBit ransomware gang is once again conducting attacks, using updated encryptors with ransom notes linking to new servers after last week's law enforcement disruption.


DarkReading
A targeted attack aiming to exploit geopolitical relations between India and Europe delivers previously undocumented, uniquely evasive backdoor malware.


HACKRead
Bitdefender researchers have discovered a new variant of the AMOS Stealer, one of the most prevalent threats for macOS users in the last year.


HACKRead
Discover the latest cybersecurity revelation: KONNI malware, linked to North Korea, targets the Russian Ministry of Foreign Affairs.


Cyber Security News
Dormant Python module Index (PyPI) module Django-log-tracker was suddenly upgraded to distribute NovaSentinel stealer malware, revealing a sophisticated hack.


DarkReading
First Brad and Jennifer, now Kim and Putin? Romance truly is dead, as North Korea is caught spying (again) on its partner to the north with the Konni malware.


The Hacker News
SOC Automation Capability Matrix revolutionizes how teams respond to incidents. Discover a new era of cybersecurity! Dive in for a transformative appr


DarkReading
Operation Texonto spanned several months, using various Russian propaganda lures and spear-phishing to misinform and trick users into giving up Microsoft 365 credentials.


Infosecurity News
ESET researchers reveal a Russian threat actor has targeted Ukrainian citizens with PYSOPs messages warning of impacts such as food and medicine shortages from the war


Trend Micro
In this blog entry, we focus on Earth Preta's campaign that employed a variant of the DOPLUGS malware to target Asian countries.


Cyber Security News
Google has introduced Magika, an AI-powered file-type identification system, that assists in detecting binary and textual file formats.


SecurityWeek
Google’s new AI Cyber Defense Initiative focuses on boosting cybersecurity through artificial intelligence.


Cyber Security News
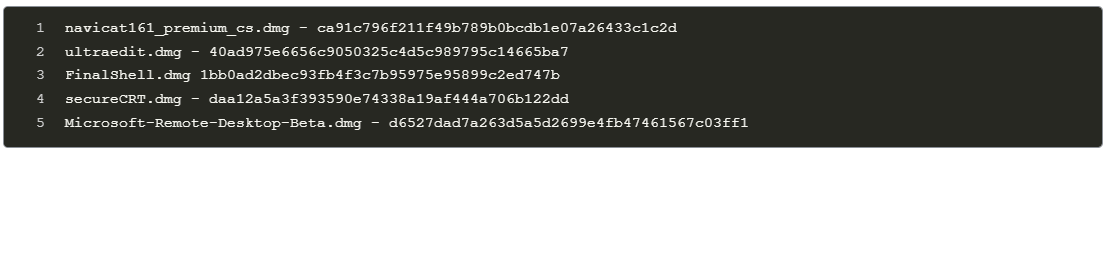
The attacker seizes control of inactive YouTube channels using leaked old credentials. Then, they upload a distinct short video that differs from the channel's previous content by enticing victims with promises of cracked software.


Bleeping Computer
AI SPERA, a leader in Cyber Threat Intelligence (CTI)-based solutions, today announced that Criminal IP ASM (Attack Surface Management) is now available on the Microsoft Azure Marketplace.


The Hacker News
Discover how Cato Networks is revolutionizing cybersecurity with their SASE-based XDR platform! Learn how they simplify threat detection and response.

DarkReading
Threat actor behind the Activator macOS backdoor is using pirated apps to distribute the malware in what could be a botnet-building operation.


Trend Micro
Based on our estimates, from approximately April 2022 until November 2023, Pawn Storm attempted to launch NTLMv2 hash relay attacks through different methods, with huge peaks in the number of targets and variations in the government departments that it targeted.


The Hacker News
Chinese hackers Mustang Panda caught red-handed targeting Myanmar's Ministry of Defence and Foreign Affairs


HACKRead
The cybersecurity researchers at Huntress have issued a warning about a recent surge in cyber attacks, highlighting a new strategy employed by cybercriminals who are exploiting TeamViewer to deploy LockBit ransomware.

Security Affairs
Researchers warned that pirated applications have been employed to deliver a backdoor to Apple macOS users.


Bleeping Computer
Security researchers analyzing the activity of the recently emerged 3AM ransomware operation uncovered close connections with infamous groups, such as the Conti syndicate and the Royal ransomware gang.

Bleeping Computer
Ransomware actors are again using TeamViewer to gain initial access to organization endpoints and attempt to deploy encryptors based on the leaked LockBit ransomware builder.


DarkReading
Modified malware from the Khepri open source project that shares similarities with the ZuRu data stealer harvests data and drops additional payloads.


CyberNews
MacOS knock-offs are being put up on Chinese pirating sites to lure victims and compromise their devices, cybersecurity firm Jamf Threat Labs warns.


DarkReading
Emerging malware variants can evade various static-signature detection engines, including XProtect, as attackers rapidly evolve to challenge defense systems.


Bleeping Computer
Cyber Threat Intelligence (CTI) search engine Criminal IP has established a technical partnership with Tenable. Learn more from Criminal IP about how this partnership can assist in real-time vulnerability and maliciousness scans.


The Cyber Express
As the New Year festivities unfold, cyber threats take on a deceptive facade, with malicious actors exploiting the celebratory spirit


The Hacker News
Cybersecurity experts unveil SpectralBlur, a new macOS backdoor with ties to North Korean malware.


SecurityWeek
SpectralBlur is a new macOS backdoor that shows similarities with North Korean hacking group’s KandyKorn malware.


Bleeping Computer
Downfall, a fan expansion for the popular Slay the Spire indie strategy game, was breached on Christmas Day to push Epsilon information stealer malware using the Steam update system.
Loading more articles....