
The Hacker News
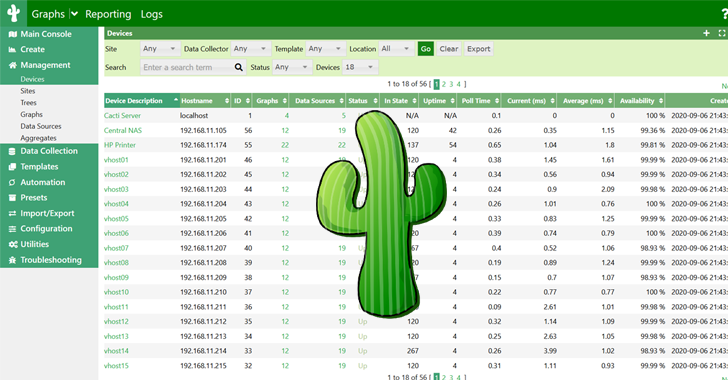
Critical Flaws in Cacti Framework Could Let Attackers Execute Malicious Code
12 security flaws addressed, including two critical issues leading to remote code execution. Update to version 1.2.27 now to stay protected

The Hacker News
12 security flaws addressed, including two critical issues leading to remote code execution. Update to version 1.2.27 now to stay protected


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


HACKRead
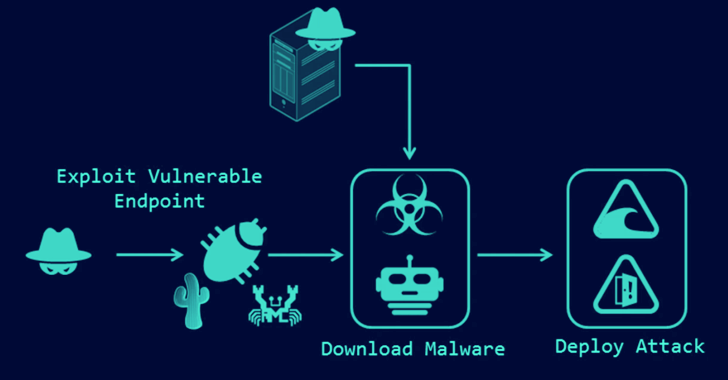
A new botnet called Goldoon targets D-Link routers and NAS devices putting them at risk of DDoS attacks and more. Learn how weak credentials leave you vulnerable and how to secure your network. pen_spark

Security Affairs
The Ubiquiti EdgeRouter botnet is still used by Russia-linked group APT28 and cybercriminals organizations.


The Hacker News
A new botnet called Goldoon is targeting D-Link routers with a critical vulnerability from 2015 (CVE-2015-2051).

Ars Technica
How and why nation-state hackers and cybercriminals coexist in the same router botnet.


CyberSecurity Dive
State-linked actors are using a custom tool for post exploitation activity of a vulnerability in Windows Print Spooler, which could result in credential theft and backdoor installs.


DarkReading
Moobot, Miori, AGoent, and a Gafgyt variant have joined the infamous Mirai botnet in attacking unpatched versions of vulnerable Wi-Fi routers.

Bleeping Computer
At least six distinct botnet malware operations are hunting for TP-Link Archer AX21 (AX1800) routers vulnerable to a command injection security issue reported and addressed last year.

.webp)
Cyber Security News
Exploitation of a critical vulnerability in TP-Link Archer routers, leading to the proliferation of various botnet threats.


The Hacker News
Researchers alert of a global rise in brute-force attacks from TOR nodes targeting VPNs, web interfaces, and SSH services

The Record
The bug affects the the Archer AX21, a popular router model manufactured by TP-Link.


SC Magazine
An attacker could gain remote access to network-attached storage and execute arbitrary commands.


Cyber Security News
Threat actors hijack routers to gain unauthorized access to network traffic. This enables them to monitor, manipulate, or intercept sensitive


SecurityWeek
The US government says Russia’s APT28 group compromised Ubiquiti EdgeRouters to run cyberespionage operations worldwide.


HACKRead
Russian hackers from APT28 are using hacked Ubiquiti EdgeRouters to build extensive botnets, steal credentials and other malicious activities.


Security Affairs
Russian cyberspies are compromising Ubiquiti EdgeRouters to evade detection, warns a joint advisory published by authorities.


The Hacker News
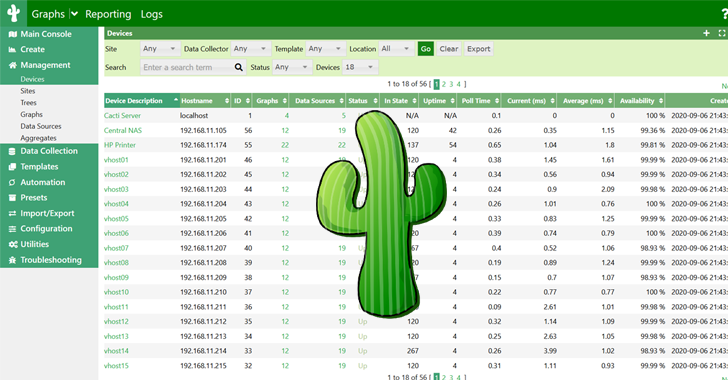
Nations unite to warn against the MooBot botnet threat targeting Ubiquiti EdgeRouters.

The Record
U.S. and international authorities on Tuesday urged owners of routers used in a Russian botnet operation to ensure the devices cannot still be exploited by malicious actors.


Ars Technica
Six years on, routers remain a favorite post for concealing malicious activities.

Bleeping Computer
Russian APT28 military hackers are using compromised Ubiquiti EdgeRouters to evade detection, the FBI says in a joint advisory issued with the NSA, the U.S. Cyber Command, and international partners.


The Cyber Express
In a world where cyber threats loom large and state-sponsored actors continually probe for vulnerabilities, the recent revelation of the


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


Ars Technica
Feds once again fix up compromised retail routers under court order.


CyberNews
The Department of Justice (DoJ) says it has taken down a global botnet controlled by Russia’s military intelligence agency, the GRU.


CyberSecurity Dive
Russia’s GRU-backed group exploited hundreds of vulnerable routers to conduct spear phishing and credential harvesting attacks against U.S. targets.


The Hacker News
U.S. government disrupted a botnet comprised of SOHO routers used by the Russia-linked APT28 group for malicious activities.


SC Magazine
For the second time this year, U.S. authorities neutralize a botnet of SOHO routers run by nation-state threat actors.

DarkReading
The feds have disrupted a Russian intelligence SOHO router botnet notable for being built with Moobot malware rather than custom code.


Security Affairs
The US authorities dismantled the Moobot botnet, which was controlled by the Russia-linked cyberespionage group APT28


PCMag
The Kremlin's notorious 'Fancy Bear' hacking group gained access to the routers by working with another Russian cybercriminal gang, the FBI says.


SecurityWeek
The US government says it has neutralized a network of hundreds of Ubiquiti Edge OS routers under the control of the notorious APT28 group.


Bleeping Computer
The FBI took down a botnet of small office/home office (SOHO) routers used by Russia's Main Intelligence Directorate of the General Staff (GRU) in spearphishing and credential theft attacks targeting the United States and its allies.


The Record
The court-authorized operation in January neutralized a botnet of routers “used to conceal and otherwise enable a variety of crimes," the Department of Justice said.


HACKRead
The potential involvement of Sandworm, the wider threat beyond attribution, the vulnerability of Zyxel firewalls and the focus on European energy firms call for improved cybersecurity posture and threat intelligence.


The Hacker News
Denmark's energy sector hit by massive cyberattack! In May 2023, 22 Danish energy sector companies were simultaneously targeted.


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. CISA adds Veritas Backup Exec flaws to its Known Exploited Vulnerabilities catalog Apple addressed two actively exploited zero-day flaws MSI confirms security breach after Money Message ransomware attack […]


Security Affairs
Microsoft addressed a misconfiguration flaw in the Azure Active Directory (AAD) identity and access management service. Microsoft has addressed a misconfiguration issue impacting the Azure Active Directory (AAD) identity and access management service that exposed multiple Microsoft applications, including the Bing management portal, to unauthorized access. The vulnerability was discovered by Wiz Research which determined […]


Security Affairs
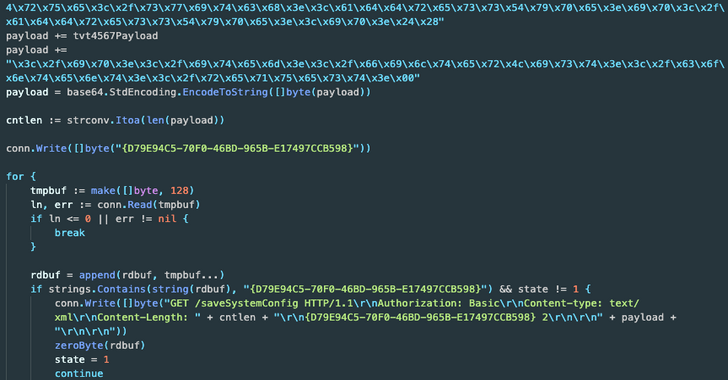
The Moobot botnet is actively exploiting critical vulnerabilities in Cacti, and Realtek in attacks in the wild. FortiGuard Labs researchers observed an ongoing hacking campaign targeting Cacti (CVE-2022-46169) and Realtek (CVE-2021-35394) vulnerabilities to spread ShellBot and Moobot malware. The ShellBot, also known as PerlBot, is a Perl-based DDoS bot that uses IRC protocol for C2 communications. The […]

The Hacker News
Critical security flaws in Cacti, Realtek, and IBM Aspera Faspex are being exploited by hackers! Unpatched systems are at risk.

Bleeping Computer
Multiple malware botnets actively target Cacti and Realtek vulnerabilities in campaigns detected between January and March 2023, spreading ShellBot and Moobot malware.


Bleeping Computer
CISA has added 12 more security flaws to its list of bugs exploited in attacks, including two critical D-Link vulnerabilities and two (now-patched) zero-days in Google Chrome and the Photo Station QNAP software.


CyberSecurity Dive
Attackers are leveraging vulnerabilities in the devices to build botnets and launch DDoS attacks, according to Palo Alto Networks research.


Security Affairs
The Moobot botnet is behind a new wave of attacks that started in early August and that target vulnerable D-Link routers. Palo Alto Network’s Unit 42 researchers reported a new wave of attacks launched by the Moobot botnet that target vulnerable D-Link routers. The Mirai-based Moobot botnet was first documented by Palo Alto Unit 42 researchers in February […]


The Hacker News
MooBot, a new variant of the Mirai botnet, has been spotted exploiting unpatched D-Link devices to include them in its army of denial-of-service bots.


Bleeping Computer
The Mirai malware botnet variant known as 'MooBot' has re-emerged in a new attack wave that started early last month, targeting vulnerable D-Link routers with a mix of old and new exploits.

SecurityWeek
Cybersecurity firm Cyfirma has identified more than 80,000 Hikvision cameras still affected by a critical code execution vulnerability patched in September 2021.


Cyber Security News
A command injection flaw that is present in over 80,000 Hikvision camera models has been discovered by security researchers at CYFIRMA


Security Affairs
Experts warn that over 80,000 Hikvision cameras are vulnerable to a critical command injection vulnerability. Security researchers from CYFIRMA have discovered over 80,000 Hikvision cameras affected by a critical command injection vulnerability tracked as CVE-2021-36260. The Chinese vendor addressed the issue in September 2021, but tens of thousands of devices are yet to be patched. […]


Bleeping Computer
Security researchers have discovered over 80,000 Hikvision cameras vulnerable to a critical command injection flaw that's easily exploitable via specially crafted messages sent to the vulnerable web server.

The Hacker News
A new variant of an IoT botnet called BotenaGo has emerged in the wild, specifically targeting Lilin security camera DVR devices with malware.

Bleeping Computer
The number of malware infections on Linux-based IoT (internet of things) devices rose by 35% in 2021 compared to the previous year's numbers. The principal goal was recruiting devices to be part of DDoS (distributed denial of service) attacks.

Bleeping Computer
The botnet known as Dark Mirai (aka MANGA) has been observed exploiting a new vulnerability on the TP-Link TL-WR840N EU V5, a popular inexpensive home router released in 2017.


ThreatPost
Attackers are milking unpatched Hikvision video systems to drop a DDoS botnet, researchers warned.


Bleeping Computer
A Mirai-based botnet called 'Moobot' is spreading aggressively via exploiting a critical command injection flaw in the webserver of many Hikvision products.