

CSO
US AI experts targeted in cyberespionage campaign using SugarGh0st RAT
Threat actors use phishing techniques to obtain non-public information about generative artificial intelligence.


CSO
Threat actors use phishing techniques to obtain non-public information about generative artificial intelligence.


The Cyber Express
The U.S. federal prosecutors on Thursday revealed charges against a North Korean job fraud nexus that ran its fraudulent scheme


DarkReading
Researchers believe the attacker is likely China-affiliated, since a previous version of the malware was used by a China nation-state attack group.


Bleeping Computer
The Norwegian National Cyber Security Centre (NCSC) recommends replacing SSLVPN/WebVPN solutions with alternatives due to the repeated exploitation of related vulnerabilities in edge network devices to breach corporate networks.


DarkReading
Thankfully, GE ultrasounds aren't Internet-facing. Exploiting most of the bugs to cause serious damage to patients would require physical device access.


Bleeping Computer
Constant training is key to staying current on the changing world of cybersecurity. This instant cybersecurity training library lets you fit in the training you need for $24.97, $95 off the $120 MSRP now through the end of May 22th.


Bleeping Computer
Electronic prescription provider MediSecure in Australia has shut down its website and phone lines following a ransomware attack believed to originate from a third-party vendor.


DarkReading
In a first-ever move, the commission's enforcement bureau has high hopes that official classification will allow law enforcement partners to better combat these kinds of threats.

Bleeping Computer
Growth in AI use is widespread, evolving, and showing no signs of slowing, and with it comes risks ranging from competitive and legal concerns to a slew of security implications. Here's how Nudge Security can help you discover and manage AI security risks.


Infosecurity News
Nearly six out of ten surveyed ClubCISO members are confident AI is used securely in their organizations


SecurityWeek
Honoring my father's memory by translating his timeless life lessons into practical wisdom for the cybersecurity profession.


Cyber Security News
Best MSP for CISO, CTO & IT Managers - 1. Perimeter 812. Secureworks 3. IBM 4. Trustwave 5. Wipro 6. Verizon 7. Sophos 8. Symantec.


SecurityWeek
Nissan North America determined recently that a ransomware attack launched last year resulted in employee personal information compromise.


CSO
Application Security Posture Management tools need to integrate with other security tools to do their job.


CSO
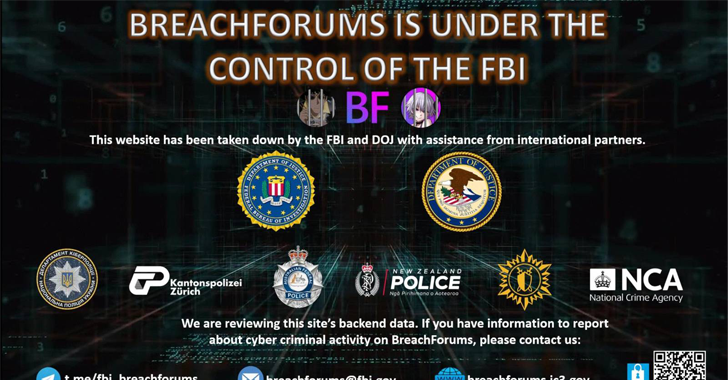
Official telegram channels operated by BreachForums members confirm law enforcement seizures and arrest.


Bleeping Computer
Turning your data into floor plans, diagrams, flow charts, and other visualizations should be an efficient process. This Microsoft Visio 2021 Professional instant download for Windows gives you all the tools you need for $19.97, $230 off the $250 MSRP now through the end of May 22nd.


SecurityWeek
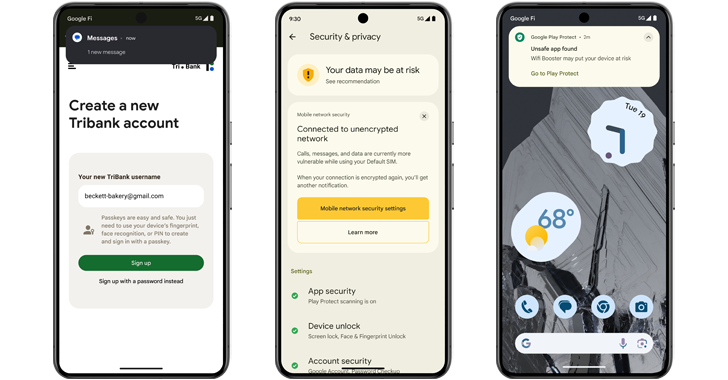
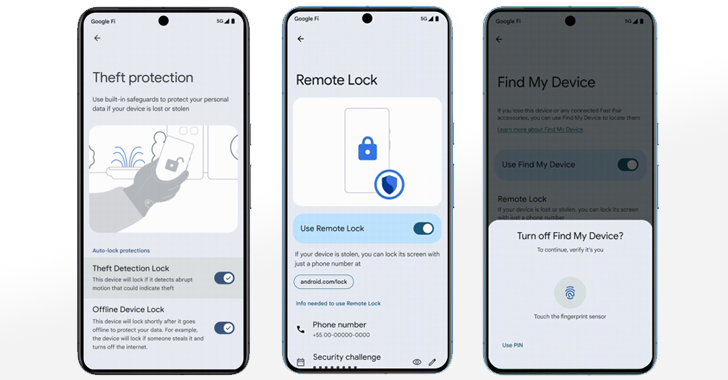
Google is boosting fraud and malware protections in Android 15 with live threat detection and expanded restricted settings.


SecurityWeek
The City of Wichita says files containing personal information were exfiltrated in a recent ransomware attack.


Infosecurity News
UK organizations are less likely than their European peers to have known exploited bugs but take longer to fix them


Infosecurity News
The FBI claims to have seized the domain and servers of hacking forum BreachForums


The Cyber Express
A ransomware attack has compromised MediSecure, a leading Australian script provider facilitating electronic prescribing and dispensing of prescriptions. The MediSecure


Cyber Security News
LogRhythm and Exabeam, two leading cybersecurity companies to create a powerful force in the security operations and analytics market.


SecurityWeek
The hacking forum BreachForums is displaying a notice claiming that the website is under the control of the FBI.

Cyber Security News
The Wireshark team has announced the release of Wireshark 4.2.5, a maintenance update to the popular network protocol analyzer.


SecurityWeek
US officials raised concerns on China’s “misuse of AI” while Beijing’s representatives rebuked the US over “restrictions and pressure” on AI.


The Record
According to the State Department, a U.S. national named Christina Chapman helped four people fraudulently obtain work as remote software and applications developers with companies in a range of sectors and industries, earning millions of dollars for the North Korean regime.


Trend Micro
This report describes how Waterbear and Deuterbear — two of the tools in Earth Hundun's arsenal — operate, based on a campaign from 2024.


SC Magazine
GenAI, API and identity risks are key concerns, as well as conflicts between DevOps and SecOps.


The Record
The National Cyber Security Centre worked with the U.K.'s insurance industry on new guidelines for organizations facing ransomware attacks.


Ars Technica
An earlier iteration of the site was taken down last year; now its reincarnation is gone.


Ars Technica
Google's video synthesis model creates minute-long 1080p videos from written prompts.


DarkReading
Cybercriminals are trafficking DocuSign assets that allow for easy extortion and business email compromise.


Bleeping Computer
Google is introducing multiple anti-theft and data protection features later this year, some available only for Android 15+ devices, while others will roll out to billions of devices running Android 10 and later.

Bleeping Computer
Today, Google announced new security features coming to Android 15 and Google Play that will help block scams, fraud, and malware apps on users' devices.

Bleeping Computer
Today, Google announced new security features coming to Android 15 and Google Play Protect that will help block scams, fraud, and malware apps on users' devices.


Bleeping Computer
For a limited time, you can get the complete Microsoft Tech Certification Bundle for $59.97 (reg. $429).

The Hacker News
BreachForums, a notorious online bazaar for stolen data, has been seized by law enforcement agencies for the second time in a year.


SecurityWeek
Financial terms were not released but it's likely a hefty price tag with Exabeam’s most recent valuation pegged at $2.5 billion.


Infosecurity News
Despite this setback, the auction house said bids can still be placed by phone and in-person

The Hacker News
Android 15 introduces new features to prevent malicious apps from capturing your sensitive data. Find out more about these crucial updates:

The Hacker News
Google just unveiled new "private space" feature lets you keep your sensitive apps hidden and locked with a separate PIN.

Ars Technica
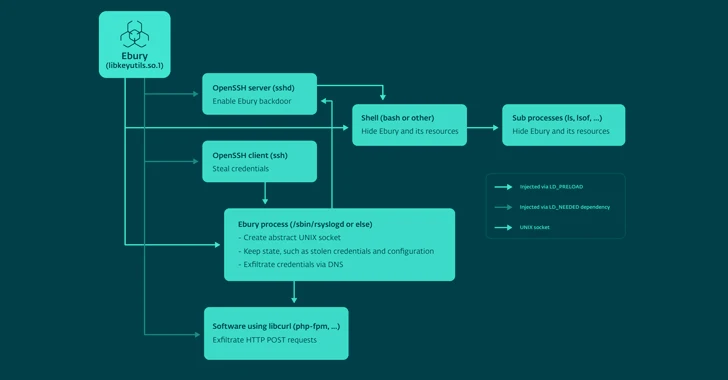
Ebury backdoors SSH servers in hosting providers, giving the malware extraordinary reach.


Infosecurity News
CPR said exploit builders in .NET and Python have been employed to deploy this malware


DarkReading
A vulnerability in the HNAP login request protocol that affects a family of devices gives unauthenticated users root access for command execution.


The Cyber Express
The notorious BreachForums seized for the second time in a year. The U.S. law enforcement today seized the clear web


Infosecurity News
The National Cyber Security Centre launches an opt-in Personal Internet Protection service to safeguard individuals from cyber threats during the upcoming election


Bleeping Computer
Organizations need to detect and remove intruders quickly to prevent data loss and minimize the impact of lateral movement attacks. Learn more from Specops Software on blocking lateral movement in networks.

.webp)
Cyber Security News
The well-known advanced persistent threat (APT) group Turla, which is based in Russia, is said to be going after the European Ministry.


Infosecurity News
Google DeepMind’s SynthID can now be used to watermark AI-generated images, audio, text and video


CSO
The health care provider has dramatically increased its estimate of the number of patients affected by the August 2023 attack.


The Cyber Express
The notorious DragonForce ransomware group has expanded its list of victims, adding two new names to their dark web portal

The Hacker News
CVSS v4.0 evaluates vulnerabilities using a revised scoring system, emphasizing environmental and threat metrics.

Bleeping Computer
As our gadgets multiply and our jobs grow in complexity, we need file storage that's friendly on the wallet and easy to use. Get 1TB of fast file storage with FolderFort for $79.99, $171 off the $251 MSRP.


Infosecurity News
NCSC CTO argues current market rewards prioritize cost over security, hindering the development of secure technology

The Hacker News
Ebury malware botnet has compromised an estimated 400,000 servers since 2009. Learn how to protect your systems from this advanced threat.


The Hacker News
Moving to the cloud just got easier. Discover how Zerto simplifies your VMware vSphere to Microsoft Azure migration.

SecurityWeek
Senators are recommending that Congress spend at least $32 billion over the next three years to develop AI and place safeguards around it.


The Cyber Express
Microsoft patched a zero-day vulnerability exploited by attackers to distribute QakBot and other malware payloads on susceptible Windows systems. Identified


Cyber Security News
Best Network Security Providers for the Healthcare Industry - 1. Perimeter 81, 2. Palo Alto Networks, 3. Fortinet, 4. Cisco, 5. Trend Micro


Cyber Security News
Alert Triage is a process of recognizing the important alerts from a huge pool of security alerts and allocating the resources accurately.

Security Affairs
The Singing River Health System revealed that the ransomware attack that hit the organization in August 2023 impacted 895,204 people.


The Cyber Express
A dark web actor named DuckyMummy claimed responsibility for an alleged data breach at Frotcom International, a prominent player in


Ars Technica
CEO Altman: "OpenAI would not be what it is without him."


SecurityWeek
Vermont passed a bill that prohibits the sale of data, such as social security and drivers’ license numbers, financial or health information.


DarkReading
The nation amends its Cybersecurity Act, giving its primary cybersecurity agency more power to regulate critical infrastructure and third parties, and requiring cyber incidents be reported.


SC Magazine
The infamous data leak site’s domain and Telegram account were seized Wednesday morning.


SC Magazine
In this month’s release, Redmond patched 60 CVEs including two other zero-days and a SharePoint Server remote code execution vulnerability rated critical.


SC Magazine
Security pros believe the incident may be a “smash and grab” attack, where the threat actors go in, grab what data they can find, then try to sell it on the dark web.


The Record
In a data breach notice about the incident, which is still affecting numerous city services, the municipality said hackers copied files from its network.


DarkReading
CVE-2024-30051 is the most concerning out of this month's Patch Tuesday offerings, and is already under active exploit by several QakBot actors.

Bleeping Computer
Microsoft has fixed a zero-day vulnerability exploited in attacks to deliver QakBot and other malware payloads on vulnerable Windows systems.


Bleeping Computer
Ethical hacking gets deep into your networks to find problems before criminals can exploit them. For a limited time start learning how with these 18 cybersecurity courses for $39.97, $1058 off the $1098 MSRP.


Bleeping Computer
Microsoft has released the KB5037768 cumulative update for Windows 10 21H2 and Windows 10 22H2 with twenty changes, including account notifications in the Start Menu and Widgets on the lock screen.


Security Affairs
The non-profit technology organization MITRE released the EMB3D threat model for embedded devices used in critical infrastructure.


Infosecurity News
The 15-year-old Ebury botnet is more active than ever, as ESET found 400,000 Linux servers compromised for cryptocurrency theft and financial gain

Bleeping Computer
A malware botnet known as 'Ebury' has infected almost 400,000 Linux servers since 2009, with roughly 100,000 still compromised as of late 2023.


Security Magazine
A global consumer research study reveals consumer attitudes about generative AI, showing that many are concerned about being fooled by deepfakes.


Infosecurity News
Several software security experts have told Infosecurity that no new vulnerabilities have been added to the US NVD since May 9


Infosecurity News
GCHQ chief warns China's cyber actions threaten global internet security, while Russia and Iran pose immediate risks


Infosecurity News
Infosecurity Europe research highlights significant challenges faced by organisations in staying up to speed with increasing compliance requirements


Bleeping Computer
On Monday, Apple and Google jointly announced a new privacy feature that warns Android and iOS users when an unknown Bluetooth tracking device travels with them.


Bleeping Computer
VMware fixed four security vulnerabilities in the Workstation and Fusion desktop hypervisors, including three zero-days exploited during the Pwn2Own Vancouver 2024 hacking contest.


Ars Technica
"It’s easier to manage a team that’s happy.”


Ars Technica
Rare bitcoin fragments are worth many times their face value.


DarkReading
Several campaigns are leveraging the evasive tactic to provide useful insights into victims' online activities, and find new ways to compromise organizations.


The Hacker News
Google has released emergency fixes for a new zero-day vulnerability (CVE-2024-4761) that has been actively exploited in the wild.


SecurityWeek
VMware has patched three critical and high-severity vulnerabilities exploited earlier this year at the Pwn2Own hacking competition.


SecurityWeek
Ron Reiter was a childhood hacker in Israel and recruited into the IDF’s Unit 8200. Now he is CTO and co-founder of cybersecurity firm Sentra.


SecurityWeek
Threat actors are using DNS tunneling to track victims’ interaction with spam and to scan network infrastructures.


The Cyber Express
A threat actor using the alias qpwomsx has claimed responsibility for an alleged data breach affecting the popular Indian online


Bleeping Computer
Cloud technology is changing how IT departments function, and getting certified in it can help advance your career. These nine Microsoft Azure exam prep courses put you on the path for $39.99, $77 off the $117 MSRP.


The Hacker News
Advanced authentication: The key to addressing the weakest link in cybersecurity - human users. Learn how to fortify your organization's defenses.


The Cyber Express
Hackers exploited an unpatched remote access server vulnerability in the Helsinki education division data breach to scour through records of


Infosecurity News
In a first, the FCC has designated “Royal Tiger” as a malicious robocall threat group


The Cyber Express
The IntelBroker hacker has allegedly leaked a database belonging to the National Parent Teacher Association (PTA), a cornerstone of child


CyberSecurity Dive
The detail and speed with which companies share information after an attack can prevent future pain. But businesses aren’t always keen on transparency.


Bleeping Computer
Google has released emergency security updates for the Chrome browser to address a high-severity zero-day vulnerability tagged as exploited in attacks.


Latest Hacking News
Chrome users must ensure that their devices are updated with the latest browser release. Google addressed an actively exploited zero-day flaw with the latest build, which applies to all Chrome users with various devices. The

.webp)
Cyber Security News
According to the FCC, the Royal Tiger Group and the people who work with it are a C-Communications Information Services Threat (C-CIST).


The Cyber Express
In the latest twist of the cyber warfare between Anonymous Egypt group and R00TK1T hackers, the latter has turned up
Loading more articles....