

Infosecurity News
Windows Quick Assist Exploited in Ransomware Attacks
Microsoft warned Storm-1811 started vishing attacks in April to gain access to target devices


Infosecurity News
Microsoft warned Storm-1811 started vishing attacks in April to gain access to target devices


DarkReading
In a first-ever move, the commission's enforcement bureau has high hopes that official classification will allow law enforcement partners to better combat these kinds of threats.


DarkReading
When abused by threat actors with sophisticated social-engineering chops, remote-access tools demand that enterprises remain sharp in both defense strategy and employee-awareness training.


HACKRead
The Internet of Things (IoT) promises a world of interconnected devices, but with this connectivity comes a dark side such as security vulnerabilities.


Trend Micro
This report describes how Waterbear and Deuterbear — two of the tools in Earth Hundun's arsenal — operate, based on a campaign from 2024.

Bleeping Computer
Today, Google announced new security features coming to Android 15 and Google Play Protect that will help block scams, fraud, and malware apps on users' devices.

Bleeping Computer
Today, Google announced new security features coming to Android 15 and Google Play that will help block scams, fraud, and malware apps on users' devices.


The Cyber Express
Santander, one of the largest banks in the eurozone, confirmed that an unauthorized party had gained access to a database


DarkReading
A vulnerability in the HNAP login request protocol that affects a family of devices gives unauthenticated users root access for command execution.


The Cyber Express
The ever-evolving landscape of cybersecurity is shaped by a dedicated group of individuals. These pioneers, through their research, entrepreneurship, and


Infosecurity News
Google DeepMind’s SynthID can now be used to watermark AI-generated images, audio, text and video


The Cyber Express
Santander, one of the largest banks in the eurozone, confirmed that an unauthorized party had gained access to a database


The Cyber Express
Cyble Research and Intelligence Labs (CRIL) researchers have uncovered a new SideCopy campaign. The threat actor group has previously been


DarkReading
CVE-2024-30051 is the most concerning out of this month's Patch Tuesday offerings, and is already under active exploit by several QakBot actors.


HACKRead
A new Android malware poses as popular applications like WhatsApp, Instagram, and Snapchat to steal user data, including login credentials.


DarkReading
Several campaigns are leveraging the evasive tactic to provide useful insights into victims' online activities, and find new ways to compromise organizations.


The Cyber Express
The field of Artificial Intelligence is rapidly evolving, and OpenAI's ChatGPT is a leader in this revolution. This groundbreaking large


Infosecurity News
Palo Alto Networks warns threat actors are using DNS tunneling techniques to probe for network vulnerabilities


The Record
In a blog post, the FTC gave special attention to the sale of geolocation data and what the agency called the “surreptitious disclosure of sensitive information" by automakers.


Bleeping Computer
A cybercriminal using the name "salfetka" claims to be selling the source code of INC Ransom, a ransomware-as-a-service (RaaS) operation launched in August 2023.


The Cyber Express
Cybersecurity researchers at Cyble's Research and Intelligence Labs (CRIL) have uncovered a new ransomware variant called Trinity, which employs a


SC Magazine
The “requests-darwin-lite” package was downloaded more than 400 times before its removal.


SC Magazine
Security pros say critical flaws in cellular these modems could cut across the industrial, healthcare, automotive, financial, and telecom sectors.


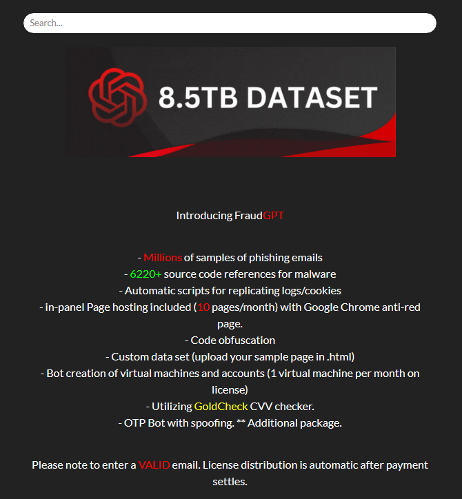
Krebs on Security
Last week, the United States joined the U.K. and Australia in sanctioning and charging a Russian man named Dmitry Yuryevich Khoroshev as the leader of the infamous LockBit ransomware group. LockBit's leader "LockBitSupp" claims the feds named the wrong guy,…


HACKRead
Researchers have discovered a novel cyberattack scheme, dubbed, LLMjacking, in which, threat actors gain access to the cloud environment.


CyberNews
One cubic millimeter of the human brain has been shown to have 50,000 cells and 150 million neural connections.


The Cyber Express
In an unexpected turn of events, LockBitSupp, the administrator of the notorious LockBit ransomware group, responded publicly to the Federal


SC Magazine
Dell began notifying customers this week after database records surfaced on a cybercrime forum.


SC Magazine
While Google confirmed that the bug exists in the wild, security researchers say there has yet to have been an instance of active exploitation.


DarkReading
Researchers recently spotted the Spanish-speaking threat actor —with nearly 400 previous victims under its belt — in a new campaign in Latin America and Central Africa.


Infosecurity News
Sysdig said the attackers gained access to these credentials from a vulnerable version of Laravel


DarkReading
China-based cybercriminal group "BogusBazaar" created tens of thousands of fraudulent online stores based on expired domains to steal payment credentials.

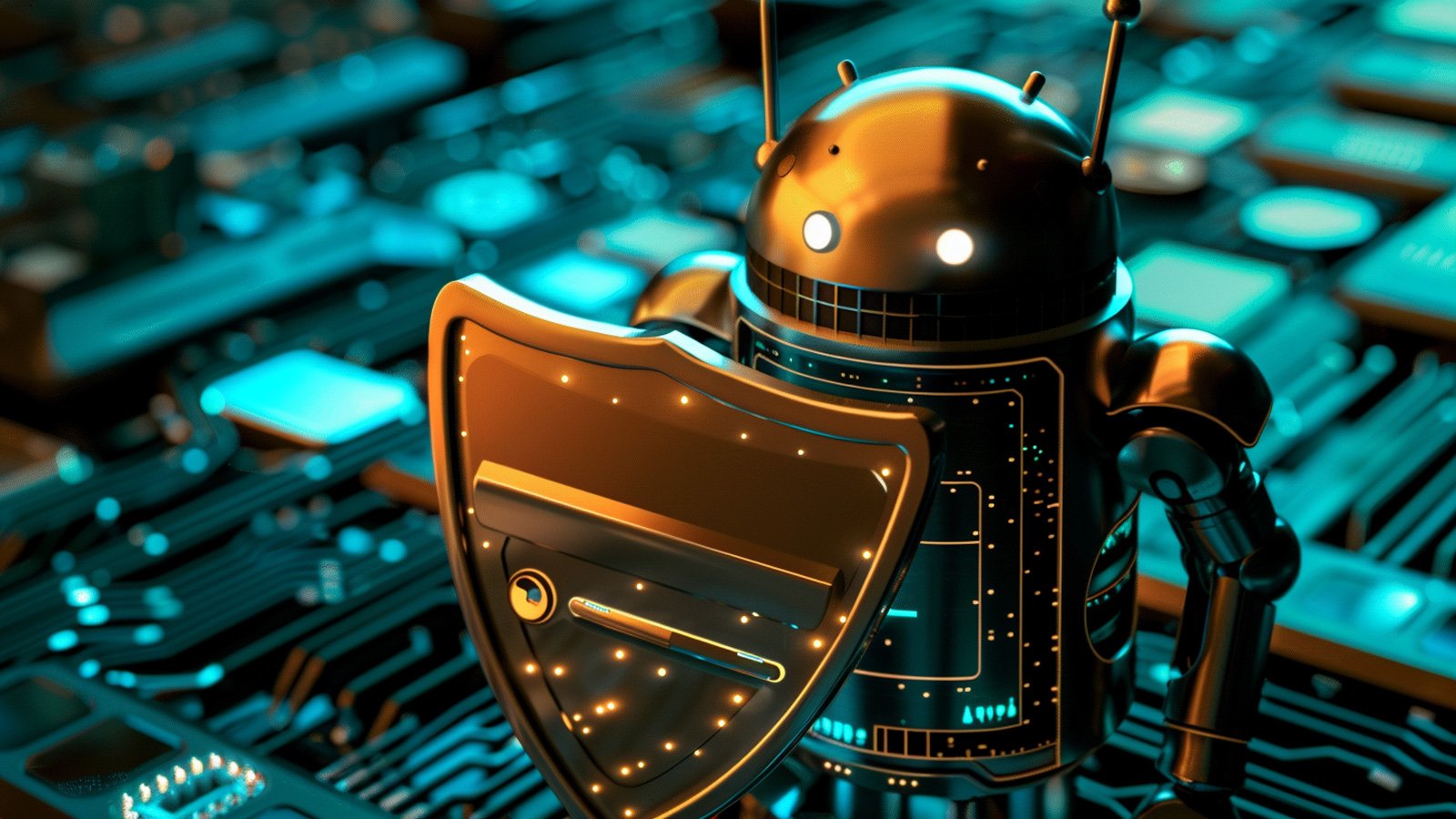
SecurityWeek
Despite the current lack of large-scale criminal exploitation of gen-AI, researchers highlight indications that this may change.


CyberNews
Elon Musk’s Neuralink has admitted part of its brain implant – already in a patient’s head – has malfunctioned, before adding there was no risk to the person’s safety.


CSO
Two high-risk vulnerabilities could be exploited to allow attackers to gain full administrative control on devices via leaked password hashes.

The Record
LockBitSupp, head of the LockBit cybercrime operation, tells the Click Here podcast team that he is not Russian national Dmitry Khoroshev, as claimed by the U.S., U.K. and Australia.


Ars Technica
Report claims new tracking starts May 13 with unclear consequences.

Security Affairs
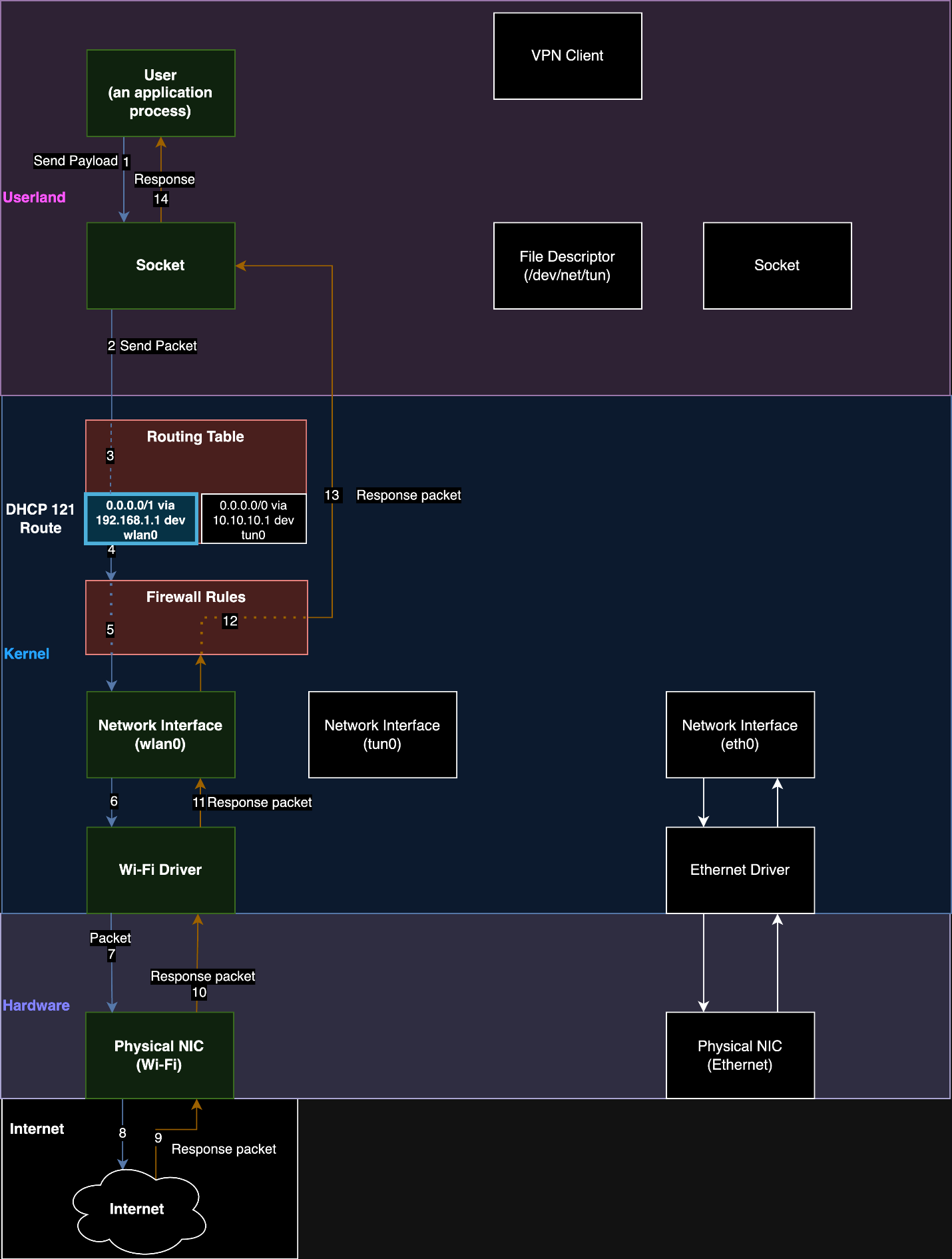
TunnelVision is a new VPN bypass technique that enables threat actors to spy on users’ traffic bypassing the VPN encapsulation.


Infosecurity News
Europol and Eurojust targeted the orchestrators of a cryptocurrency scam launched in December 2017


HACKRead
WordPress websites are under attack with a surge of malicious JavaScript being injected using vulnerable versions of the LiteSpeed Cache plugin.


HACKRead
This article explores Microsoft Azure Entra ID flaw, explains the vulnerability in context, and offers actionable steps to secure your organization.

The Hacker News
The cloud promises agility, but opens a Pandora's box of cyber risks if not secured properly. Understand your responsibility under the shared responsi


CSO
Security researchers allege that several apps are collecting data from iOS devices, violating Apple’s policy on device fingerprinting.


SC Magazine
Security pros warn that this flaw could affect just about every IP-routing based VPN.


DarkReading
MITRE's hackers made use of at least five different Web shells and backdoors as part of their attack chain.


DarkReading
Much of the funding will be used for product development and talent acquisition to cover more ground as the cybersecurity industry continues to evolve.


CyberNews
OpenAI has said that it’s building a tool to detect content created by its text-to-image generator DALL-E 3, with early testing showing 98% accuracy.


CyberNews
The leadership identity of the LockBit ransomware group is unveiled by the US Department of Justice (DoJ), UK’s National Crime Agency (NCA), and Europol.

%20(1).webp)
Cyber Security News
A critical XSS vulnerability has discovered in the popular Yoast SEO WordPress plugin, potentially putting over 5m websites at risk.


CSO
Much similar to Citrix-Bleed, the information disclosure bug was identified within NetScaler devices configured as gateway or virtual servers.


DarkReading
The flaw was nearly identical to last year's CitrixBleed flaw, but not as severe.


Krebs on Security
The United States joined the United Kingdom and Australia today in sanctioning 31-year-old Russian national Dmitry Yuryevich Khoroshev as the alleged leader of the infamous ransomware group LockBit. The U.S. Department of Justice also indicted Khoroshev as the gang's leader…


HACKRead
Cybersecurity researchers from Mac security provider, Kandji, have discovered a new malware dubbed "Cuckoo" targeting macOS users.


CyberNews
Deutsche Telekom was one of dozens of other companies from around the globe posted on the infamous LockBit ransomware leak list of victims.


Bleeping Computer
The NCA, FBI, and Europol have revived a seized LockBit ransomware data leak site to hint at new information being revealed by law enforcement this Tuesday.


The Cyber Express
Anonymous Arabia, a ransomware group notorious for its clandestine operations, has allegedly targeted two significant entities in the UAE: Dubai.ae,


Security Affairs
Resecurity found a massive leak involving the exposure of personally identifiable information (PII) of over 5M citizens of El Salvador.


Ars Technica
Andrej Karpathy muses about sending a LLM binary that could "wake up" and answer questions.


CyberSecurity Dive
The company will enhance management roles under the CISO and partially tie compensation to security performance.


CyberNews
Fancy Bear attacks prompted Germany to react diplomatically.


The Cyber Express
A threat actor group Stormous Ransomware, affiliated with the Five Families alliance, has claimed responsibility for alleged cyberattacks targeting several


SC Magazine
Microsoft Graph API has become popular with hackers because running criminal ops on widely used cloud services raises less suspicion.


DarkReading
Microsoft has uncovered a common vulnerability pattern in several apps allowing code execution; at least four of the apps have more than 500 million installations each; and one, Xiaomi's File Manager, has at least 1 billion installations.


DarkReading
Threat actor dropped in to Dropbox Sign production environment and accessed emails, passwords, and other PII, along with APIs, OAuth, and MFA info.


Infosecurity News
Microsoft illustrated the severity of the issue via a case study involving Xiaomi’s File Manager


Infosecurity News
Attackers accessed emails, usernames, phone numbers, hashed passwords and authentication information


CSO
Mandiant observed several malicious campaigns with threat actors impersonating journalists and harvesting the victim’s cloud environment credentials.


CSO
The names and email addresses of those customers were also exposed who had never created an account with Dropbox Sign but had “received or signed a document through Dropbox Sign.”


SC Magazine
Security pros see the Dropbox Sign breach as not just a blow to Dropbox, but a really bad day for electronic signatures.


DarkReading
The newly discovered malware, which has so far mainly targeted Turkish telcos and has links to HiatusRat, infects routers and performs DNS and HTTP hijacking attacks on connections to private IP addresses


SecurityWeek
Venafi’s 90-Day TLS Readiness solution enhances its existing technology to provide full, demonstrable, and visible compliance with the coming 90-day mandate.


Latest Hacking News
A security researcher discovered a security vulnerability in the Judge0 system, which received a patch that could further be bypassed, leading to further vulnerabilities. While the developer eventually patched the issue after repeated exploits, the


Trend Micro
This blog entry aims to highlight the dangers of internet-facing routers and elaborate on Pawn Storm's exploitation of EdgeRouters, complementing the FBI's advisory from February 27, 2024.


The Record
The company told federal regulators that it discovered unauthorized access to the production environment of its Dropbox Sign product.


Ars Technica
Amazon says it's working on stopping others from "making your AWS bill explode."


Cyber Security News
an AWS customer faced a staggering $1,300 bill for S3 usage, despite creating a single, empty bucket for testing purposes.


CyberSecurity Dive
Security researchers warn the threat group is ramping up exploitation of previously disclosed flaws in the cloud platform.


Cyber Security News
Tanto Security has disclosed critical vulnerabilities in the widely-used open-source service Judge0, which could allow attackers to perform a sandbox escape and gain root access to the host machine.


HACKRead
Meet Brokewell malware, a new cybersecurity threat to your Android device (smartphone and tablets) and personal information.


HACKRead
Beware! Agent Tesla & Taskun Malware are targeting US Education & Gov. This cyberattack steals data & exploits vulnerabilities.


DarkReading
The targeted operation utilized CVE-2017-8570 as the initial vector and employed a notable custom loader for Cobalt Strike, yet attribution to any known threat actor remains elusive.


DarkReading
Attacks by a previously unknown state-sponsored actor leveraged two bugs in firewall devices to install custom backdoors on several government networks globally.


Infosecurity News
Cyber threat intelligence provider Cyble found that DragonForce was using a ransomware binary based on LockBit Black’s builder


CyberSecurity Dive
The campaign, dubbed ArcaneDoor, dates back to late 2023 and is targeting perimeter network devices from Cisco — and potentially other companies.


CSO
Hackers exploited previously undetected vulnerabilities in Cisco’s Adaptive Security Appliances — a product that combines multiple cybersecurity functions.


The Record
The cyber agency made nearly 1,800 notifications in 2023 to organizations with internet-exposed devices vulnerable to ransomware attacks.


SC Magazine
Security pros say given the complexity of SAN management tools, it’s understandable the patches took so long.


DarkReading
An exploit for the vulnerability allows attackers to escape a virtual file system sandbox to download system files and potentially achieve RCE.


SecurityWeek
CISA warns organizations of a two-year-old Windows Print Spooler vulnerability being exploited in the wild.


CyberNews
Microsoft identifies the 'GooseEgg' tool created by Russian threat group APT 28, Forrest Blizzard to exploit known vulnerabilities in Windows printer spooler service.

Trend Micro
In this blog entry, we discuss Trend Micro's contributions to an Interpol-coordinated operation to help Brazilian and Spanish law enforcement agencies analyze malware samples of the Grandoreiro banking trojan.


SC Magazine
Security pros say there’s a high potential that attackers could launch arbitrary code execution.


SC Magazine
A new CryptBot variant targets password managers and authentication apps in the new campaign.


The Record
The federal government urged civilian agencies to patch severe bugs in certain Cisco hardware, as well as a flaw in the CrushFTP software, within a week.


Infosecurity News
The move is reportedly part of a broader effort to counter the misuse of surveillance technology


DarkReading
The infamous Russian threat actor has created a custom tool called GooseEgg to exploit CVE-2022-38028 in cyberespionage attacks against targets in Ukraine, Western Europe, and North America.


SecurityWeek
Microsoft PlayReady vulnerabilities that could allow rogue subscribers to illegally download movies from popular streaming services.


Security Affairs
A cyber attack has been disrupting operations at Synlab Italy, a leading provider of medical diagnosis services, since April 18.


SecurityWeek
Shadowserver has identified roughly 6,000 internet-accessible Palo Alto Networks firewalls potentially vulnerable to CVE-2024-3400.


HACKRead
Cybersecurity researchers at Zscaler ThreatLabz believe that the primary target of the MadMxShell backdoor seems to be IT professionals.
Loading more articles....