

Ars Technica
Archie, the Internet’s first search engine, is rescued and running
A journey through busted tapes, the Internet Old Farts Club, and SPARCstations.


Ars Technica
A journey through busted tapes, the Internet Old Farts Club, and SPARCstations.


SecurityWeek
Russian-speaking threat actors are caught abusing a GitHub profile to distribute information stealers posing as legitimate software.

.webp)
Cyber Security News
WPS Office is a office suite developed by Kingsoft that supports spreadsheets, presentations, documents and others. It has been used


Infosecurity News
Recorded Future details a novel campaign that abuses legitimate internet services to deploy multiple malware variants for credential theft


CyberNews
If your Android device has Xiaomi’s File Manager or WPS Office, update them immediately.


Bleeping Computer
A new campaign tracked as "Dev Popper" is targeting software developers with fake job interviews in an attempt to trick them into installing a Python remote access trojan (RAT).

Security Affairs
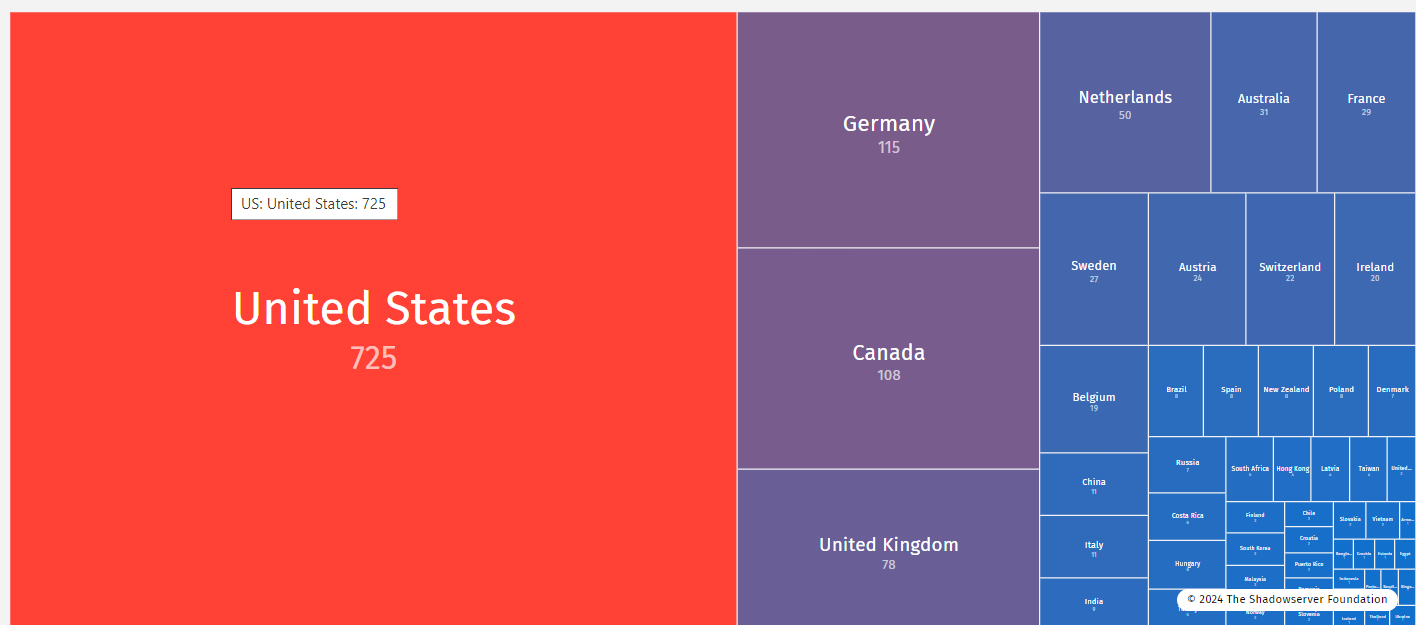
Over 1,400 CrushFTP internet-facing servers are vulnerable to attacks exploiting recently disclosed CVE-2024-4040 vulnerability.


Security Affairs
CISA adds Cisco ASA and FTD and CrushFTP VFS vulnerabilities to its Known Exploited Vulnerabilities catalog.


HACKRead
A critical zero-day vulnerability in CrushFTP, a popular file transfer software, allows attackers to download sensitive system files.


The Record
The federal government urged civilian agencies to patch severe bugs in certain Cisco hardware, as well as a flaw in the CrushFTP software, within a week.


Security Affairs
Threat actors exploited a critical zero-day vulnerability in the CrushFTP enterprise in targeted attacks, Crowdstrike experts warn.


Infosecurity News
A joint advisory from Europol and US and Dutch government agencies estimated that Akira made around $42m in ransomware proceeds from March 2023 to January 2024


The Hacker News
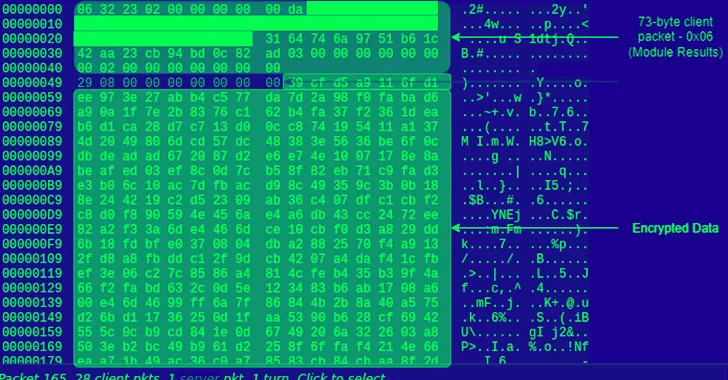
TA558 hackers are using steganography to hide and distribute malware like Agent Tesla, FormBook, Remcos RAT, LokiBot.


Bleeping Computer
A new campaign conducted by the TA558 hacking group is concealing malicious code inside images using steganography to deliver various malware tools onto targeted systems.


DarkReading
Latest campaign underscores wide-ranging functionality and staying power of a decade-old piece of information-stealing malware, Agent Tesla.


The DFIR Report
Key Takeaways We provide a range of services, one of which is our Threat Feed, specializing in monitoring Command and Control frameworks like Cobalt Strike, Metasploit, Sliver, Viper, Mythic, Havoc, … Read More


HACKRead
Sign1 malware's tactics make it a significant threat as it uses time-based randomization to generate dynamic URLs, making it difficult to block.


DarkReading
Unsophisticated threat actor is targeting Russian companies with both readily available malware and authentic software.

.webp)
Cyber Security News
With our weekly cybersecurity news summary, explore and learn about the most recent developments in the cybersecurity field.


The Hacker News
Researchers at G DATA have exposed a scheme dubbed "gitgub" on GitHub, where 17 repositories were delivering the information stealer, RisePro.


Cyber Security News
Threat actors use keyloggers to capture sensitive information, as covert techniques and tactics allow them to steal valuable information.


The Cyber Express
Dark web rumors indicate Banregio, a leading financial institution in Mexico, may have suffered a data breach. Allegedly, unauthorized access


The Cyber Express
The Lindsay Municipal Hospital cyberattack has been claimed by the BianLian ransomware group. This nefarious organization, known for its disruptive


Cyber Security News
Stay updated with the most recent advancements in the cybersecurity industry with our weekly recap of cybersecurity news.


SecurityWeek
Researchers demonstrate that remote Stuxnet-style attacks are possible against many modern PLCs using web-based malware.


Security Affairs
CISA, the FBI, and MS-ISAC issued a joint CSA to warn of attacks involving Phobos ransomware variants observed as recently as February 2024


SecurityWeek
US government agencies warn of Backmydata, Devos, Eight, Elking, and Faust ransomware attacks connected to Phobos.


Security Affairs
Taiwanese vendor Zyxel warns of security vulnerabilities in its firewalls and access points, including a remote code execution flaw.


SecurityWeek
Taiwanese networking vendor Zyxel confirms security flaws in firewall and access points put users at risk of remote code execution attacks.


CyberNews
Timothy Burke faces charges for hacking and violations of the Wiretap Act


The Cyber Express
A group identifying themselves as RansomedVC has emerged on the dark web, claiming to possess access to an Australian women's


The Cyber Express
The BianLian ransomware group has claimed three new victims, adding them to their dark web portal. The targeted organizations include


Ars Technica
Dave Mills created NTP, the protocol that holds the temporal Internet together, in 1985.


DarkReading
Just like you and me, cyberattackers returned from winter break and immediately started sending thousands of emails.


SecurityWeek
SecurityWeek Hacker Conversations interview with HD Moore, best known as the founder and original developer of Metasploit.


The Cyber Express
Republic Shipping Consolidators, a prominent logistics company, finds itself entangled in the web of a cyberattack orchestrated by the notorious

Bleeping Computer
A Phemedrone information-stealing malware campaign exploits a Microsoft Defender SmartScreen vulnerability (CVE-2023-36025) to bypass Windows security prompts when opening URL files.


The Hacker News
2023 witnessed a shocking 55.5% increase in ransomware victims! Over 4,368 cases reported globally. Stay ahead in the cybersecurity game.

Trend Micro
This blog delves into the Phemedrone Stealer campaign's exploitation of CVE-2023-36025, the Windows Defender SmartScreen Bypass vulnerability, for its defense evasion and investigates the malware's payload.


Bleeping Computer
A pro-Ukraine hacktivist group named 'Blackjack' has claimed a cyberattack against Russian provider of internet services M9com as a direct response to the attack against Kyivstar mobile operator.


Cyber Security News
Top 10 Notorious Ransomware Gangs of 2023. LockBit. Alphv/Black. Cat. Clop. Royal. Black Byte. Black Basta. Ragnar Locker. Vice Society.


The Cyber Express
The notorious BianLian ransomware group has targeted MOOver, claiming to have gained access to a staggering 1.1 terabytes of the


DarkReading
Malicious attachments that exploit an RCE flaw from 2017 are propagating Agent Tesla, via socially engineered emails and an evasive infection method.


The Cyber Express
The notorious BianLian ransomware group has expanded its list of victims, adding the name of Air Sino-Euro Associates (ASA Holidays).


Cyber Security News
The Cyber-Extortion Trinity—the BianLian, White Rabbit, and Mario ransomware gangs—was observed by researchers working together to launch a joint extortion campaign against publicly traded financial services companies.


The Hacker News
Rhadamanthys, a versatile info-stealer, introduces a plugin system, making it more customizable. Cybercriminals can now tailor it to their needs.


Bleeping Computer
While we may joke that the internet is forever, it can often be anything but. This lifetime subscription to Offcloud helps you keep what matters for $39.99, $169 off the $209 MSRP.


Bleeping Computer
The developers of the Rhadamanthys information-stealing malware have recently released two major versions to add improvements and enhancements across the board, including new stealing capabilities and enhanced evasion.


SecurityWeek
The Shadowserver Foundation warns of an increase in the number of devices hacked via recent Cisco IOS XE vulnerabilities.


CyberNews
Hacktivism and its lesser-known impacts on mental health

Security Affairs
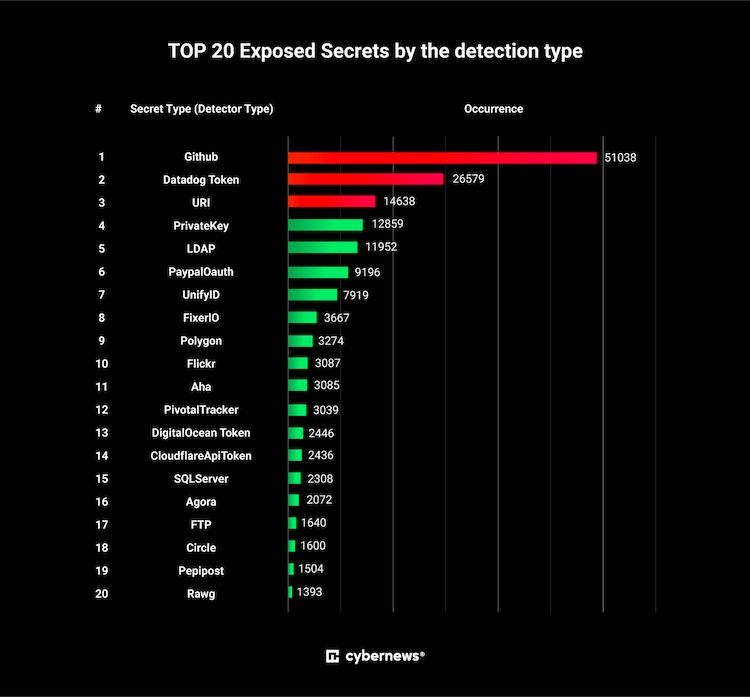
Thousands of secrets have been left exposed on Docker Hub, a platform where web developers collaborate on their code for web applications.


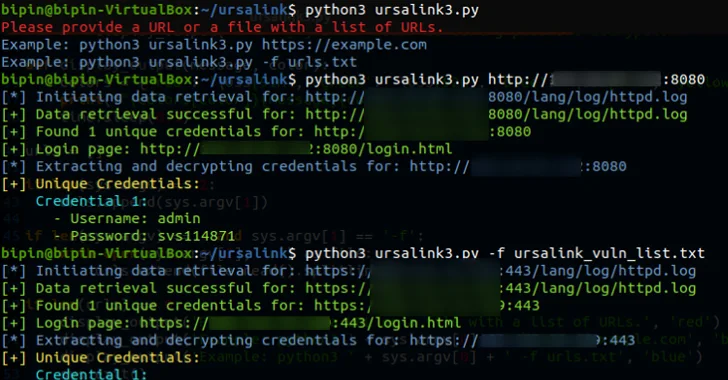
Ars Technica
Easy-to-exploit flaw can give hackers passwords and cryptographic keys to vulnerable servers.


CyberNews
The Docker Hub store has at least 5,493 container images that contain secrets and could be considered as exposing sensitive information.


SecurityWeek
Car parts giant AutoZone says nearly 185,000 individuals were impacted by a data breach caused by the MOVEit hack.


The Hacker News
Indian Hack-for-Hire Group targeted U.S., China, Pakistan, and more for over a decade.


DarkReading
The obscure Kazuar backdoor used by Russian attack group Turla has resurfaced, and it's more dangerous than ever.

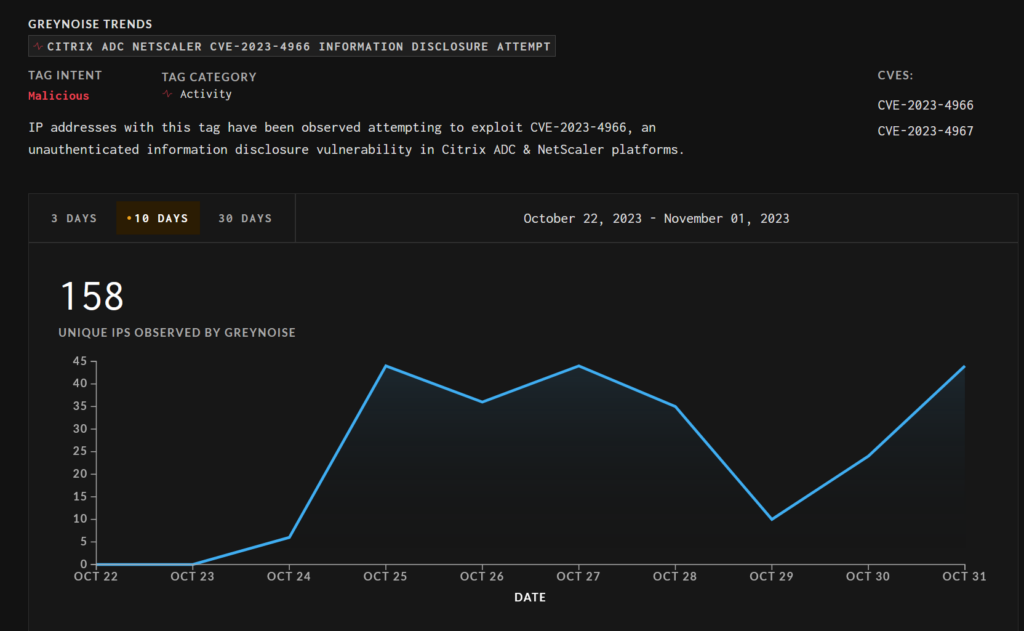
SecurityWeek
Multiple threat actors are exploiting CVE-2023-4966, aka Citrix Bleed, a critical vulnerability in NetScaler ADC and Gateway.

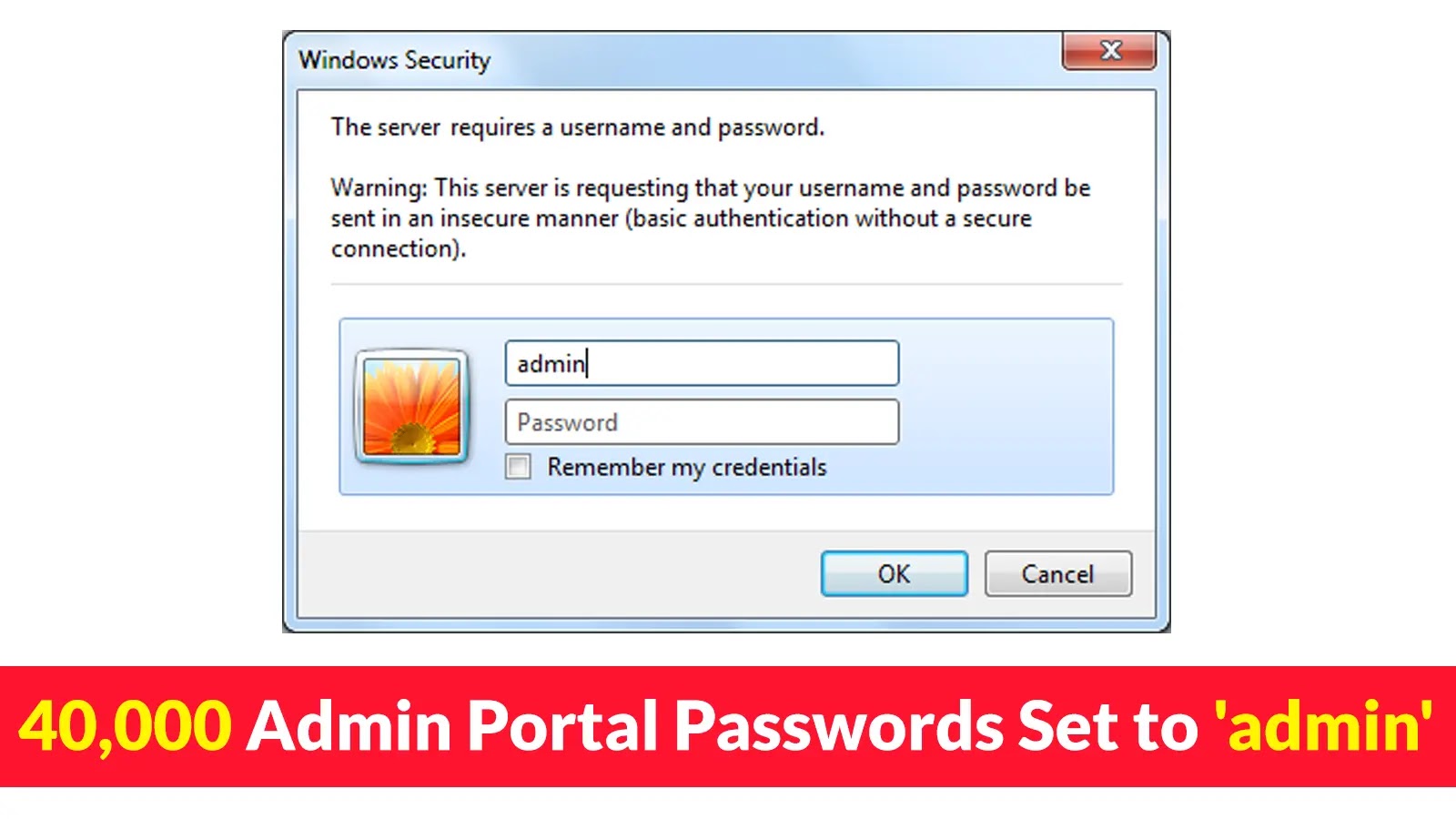
Cyber Security News
IT admins can be considered culpable for weak password use if they fail to enforce strong password policies or neglect proper security measures.


Cyber Security News
Multiple vulnerabilities have been discovered in Titan MFT and Titan SFTP servers owned by South River Technologies.

The Hacker News
Milesight's industrial routers risk unauthorized web interface access, while Titan MFT and Titan SFTP servers face remote


Infosecurity News
The threat actors attempted to escalate privileges using the open-source GodPotato tool


SecurityWeek
Flaw poses a direct threat to the SOCKS5 proxy handshake process in cURL and can be exploited remotely in some non-standard configurations.


Cyber Security News
Snake Keylogger, a .NET infostealer malware, also known as 404 Keylogger, steals credentials, keystrokes, and screenshots, collects system info


SecurityWeek
A high-severity vulnerability in the data transfer project cURL will be addressed with libcurl and curl updates this week.

The Hacker News
Curl library, backbone of data transfers, to address TWO security vulnerabilities on October 11, 2023.

The Record
The maintainers of a popular open source tool that serves as a foundational support for many network protocols like SSL, TLS, HTTP, FTP, SMTP are warning of two vulnerabilities that will be announced this coming week.

SecurityWeek
Critical security flaw allows unauthenticated, remote attacker to log in to device using root account, which has default, static credentials that cannot be changed or deleted.


Infosecurity News
Fortinet said these packages can be categorized into nine sets based on their code and functions


The Hacker News
Over 30 malicious npm packages discovered in the wild. They're after your sensitive data - SSH keys, Kubernetes configs, and more.


SecurityWeek
Fortinet warns of multiple malicious NPM packages that include install scripts designed to steal sensitive information.


SecurityWeek
Companies have addressed the impact of the exploited Libwebp vulnerability CVE-2023-4863 on their products.

The Record
One flaw is in open source code known as "libvpx," which is involved with handling media such as images. The other issue is with software known as WS_FTP.


SecurityWeek
Rapid7 says attackers are targeting a critical pre-authentication flaw in Progress Software’s WS_FTP server just days after disclosure.


CSO
A report by Proofpoint identifies the new Trojan as undocumented and possessing information-stealing capabilities.


Bleeping Computer
Fake Bitwarden sites are pushing installers purportedly for the open-source password manager that carry a new password-stealing malware that security researchers call ZenRAT.

The Hacker News
⚠️ Beware of ZenRAT! This new modular malware strain targets Windows users through trojanized Bitwarden installers.


Infosecurity News
Discovered by Proofpoint, ZenRAT is a modular remote access trojan targeting Windows users


Cyber Security News
Magento Security Checklist : 1. Update to the Latest Version 2. Ensure a Strong Password 3. Limit Magento Admin Login Attempts 4. Switch 2FA.


Cyber Security News
Best Data Loss Prevention Software: 1. DoControl 2. Check Point 3. Forcepoint 4. Code42 5. Digital Guardian 6. Trellix 7. Proofpoint.


Bleeping Computer
The malware loader 'Bumblebee' has broken its two-month vacation with a new campaign that employs new distribution techniques that abuse 4shared WebDAV services.

%20Penetration%20Testing%20(1).webp)
Cyber Security News
Penetration testing of point-of-sale (POS) devices is essential to ensure the security of payment systems and protect sensitive customer data


Infosecurity News
Symantec says it was used in a failed LockBit attack


DarkReading
Nothing good happens after 2 a.m., they say, especially when hackers have two kinds of ransomware at their disposal.


Bleeping Computer
A new ransomware strain called 3AM has been uncovered after a threat actor used it in an attack that failed to deploy LockBit ransomware on a target network.


The Hacker News
A new ransomware, 3AM, has emerged! It's written in Rust and aims to encrypt files while deleting Volume Shadow copies.


Ars Technica
With no patch available yet, users must enable workarounds. The best: enforce MFA.


The Hacker News
Are your Microsoft IIS servers safe from cyberattacks? Lazarus strikes again! Discover how to defend your servers from malware.


Cyber Security News
Cisco ASA SSL VPN Appliances is a type of network security device that allows remote users to access a private network over the internet securely.

The Hacker News
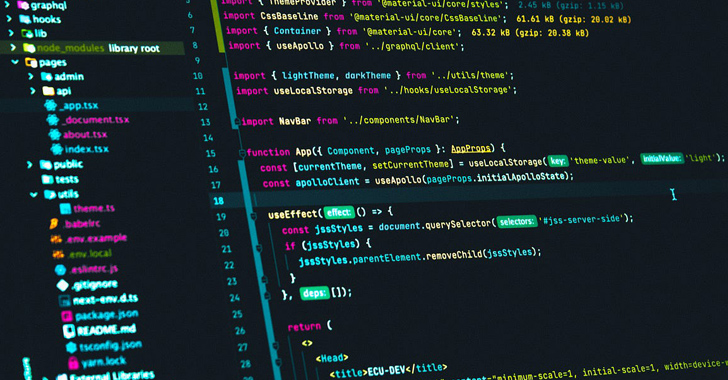
Watch out, coders! Malicious npm packages are exploiting post-install hooks to steal source code & secrets.

The Hacker News
Agile isn't just for devs anymore! Watch how an attacker develops and releases malware iterations targeting cloud credentials.

Latest Hacking News
A new remote access trojan “QwixxRAT” has caught the security researchers’ attention while targeting Windows systems. The threat actors are spreading QwixxRAT malware, also known as “TelegramRAT”, via Telegram and Discord to infect Windows systems. QwixxRAT


Security Affairs
QwixxRAT is a new Windows remote access trojan (RAT) that is offered for sale through Telegram and Discord platforms. The Uptycs Threat Research team discovered the QwixxRAT (aka Telegram RAT) in early August 2023 while it was advertised through Telegram and Discord platforms. The RAT is able to collect sensitive data and exfiltrate them by […]

-1.webp)
Cyber Security News
In this technical article, we delve into the intricacies of Ficker Stealer's operations, highlighting its propagation methods.


Cyber Security News
The protocols SSL (Secure Sockets Layer) and TLS (Transport Layer Security), are used to create connections between networked computers.


Infosecurity News
Phylum said the attack demonstrated a carefully crafted development cycle


Security Affairs
Researchers discovered a new set of malicious packages on the npm package manager that can exfiltrate sensitive developer data. On July 31, 2023, Phylum researchers observed the publication of ten different “test” packages on the npm package manager that were developed to exfiltrate sensitive developer source code and other confidential information. All of these packages […]


Ars Technica
This time we discuss how we manage, update, and deploy the code that makes Ars work.


Bleeping Computer
A new 'Nitrogen' initial access malware campaign uses Google and Bing search ads to promote fake software sites that infect unsuspecting users with Cobalt Strike and ransomware payloads.

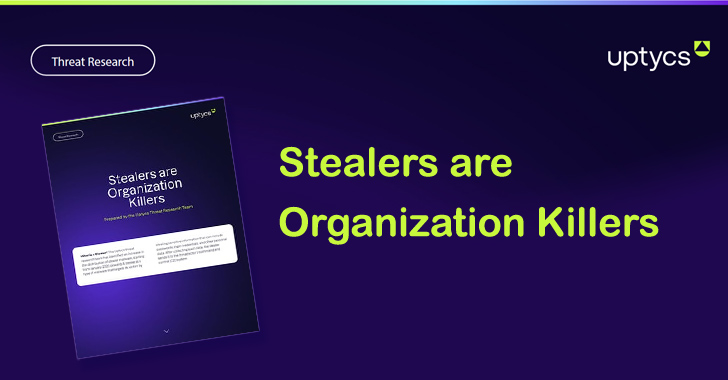
The Hacker News
Info stealing malware on the rise! Windows, Linux, macOS - no system is safe! Get the scoop on these cyber threats in Uptycs' latest whitepaper.


Bleeping Computer
A critical severity 'Super Admin' privilege elevation flaw puts over 900,000 MikroTik RouterOS routers at risk, potentially enabling attackers to take full control over a device and remain undetected.
Loading more articles....