

The Hacker News
New Wi-Fi Vulnerability Enables Network Eavesdropping via Downgrade Attacks
New Wi-Fi vulnerability discovered! CVE-2023-52424, dubbed "SSID Confusion attack," affects all operating systems and Wi-Fi clients.


The Hacker News
New Wi-Fi vulnerability discovered! CVE-2023-52424, dubbed "SSID Confusion attack," affects all operating systems and Wi-Fi clients.


Bleeping Computer
Security researchers discovered two previously unseen backdoors dubbed LunarWeb and LunarMail that were used to compromise a European government's diplomatic institutions abroad.


The Cyber Express
In response to heightened cyber threats targeting political candidates, election officials and civil society groups, the National Cyber Security Centre


The Record
The Share and Defend system will provide a list of malicious domains to a range of U.K. communications providers so the domains can be added to blocklists.

.webp)
Cyber Security News
The well-known advanced persistent threat (APT) group Turla, which is based in Russia, is said to be going after the European Ministry.


Cyber Security News
Best Network Security Providers for the Healthcare Industry - 1. Perimeter 81, 2. Palo Alto Networks, 3. Fortinet, 4. Cisco, 5. Trend Micro


The Record
The U.K. government has warned that the accounts of political candidates and election officials are “almost certainly attractive targets for cyber actors looking to carry out espionage operations.”


DarkReading
While the protocol has made passwordless authentication a reality, token-binding is key to prevent against token theft and reuse, security vendor says.


Infosecurity News
Recorded Future details a novel campaign that abuses legitimate internet services to deploy multiple malware variants for credential theft

HACKRead
DNS tunneling is being used to bypass security filters by hiding malicious traffic in DNS packets, allowing hackers to steal stolen data.


DarkReading
Several campaigns are leveraging the evasive tactic to provide useful insights into victims' online activities, and find new ways to compromise organizations.


SecurityWeek
Threat actors are using DNS tunneling to track victims’ interaction with spam and to scan network infrastructures.


Infosecurity News
Palo Alto Networks warns threat actors are using DNS tunneling techniques to probe for network vulnerabilities


Latest Hacking News
Torrance, California, May 13th, 2024, CyberNewsWireCriminal IP, a renowned Cyber Threat Intelligence (CTI) search engine developed by AI SPERA, has recently signed a technology partnership to exchange threat intelligence data based on domains and potentially


Bleeping Computer
Threat actors are using Domain Name System (DNS) tunneling to track when their targets open phishing emails and click on malicious links, and to scan networks for potential vulnerabilities.

%20(1).webp)
Cyber Security News
"Our partnership with Quad9 is a recognition of the accuracy of Criminal IP's data," stated Byungtak Kang, CEO of AI SPERA.


Bleeping Computer
The Criminal IP Threat Intelligence (CTI) search engine to integrate with Quad9's threat-blocking service. Learn more from Criminal IP about how this integration can help you.


HACKRead
Torrance, California, May 13th, 2024, CyberNewsWire


Cyber Security News
The Go team has released patches for two significant vulnerabilities that could allow attackers to execute arbitrary code and cause service disruptions through infinite loops.


Security Affairs
Threat actors are exploiting a high-severity vulnerability in the LiteSpeed Cache plugin for WordPress to take over web sites


Latest Hacking News
Heads up, Android users! If you’re using a VPN, it’s time to meddle with your device settings to deal with the DNS leak vulnerability that sneakily affects Android devices. This vulnerability keeps leaking the DNS


The Cyber Express
By Eyal Arazi, senior security solutions lead for Radware The cybersecurity landscape evolved rapidly in 2023. In particular, there was


SC Magazine
RSA Conference will tackle everything AI, but will also go deep on government policy, innovative new security solutions and explore "The Art of Possible."


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.

.png)
Cyber Security News
The weekly news summary keeps you up to date with what’s happening in cybersecurity, including developments, vulnerabilities, breaches, threats, and defensive strategies. Knowing about new cyber risks and attack vectors helps you put up safeguards and preventive measures as soon as possible to protect your systems. Remaining constantly aware gives you a holistic view of […]


Cyber Security News
Android's operating system has identified a critical vulnerability that allows DNS traffic to leak during VPN server switches, potentially exposing users' internet activity to cybercriminals.


Ars Technica
ZTDNS brings the best of both worlds to DNS: encryption and fine-grained control.


DarkReading
Our collection of the most relevant reporting and industry perspectives for those guiding cybersecurity strategies and focused on SecOps. Also included: a Tech Tip on setting up DMARC, a DNS mystery from Muddling Meerkat, and a cybersecurity checklist for M&A transitions.


Bleeping Computer
A Mullvad VPN user has discovered that Android devices leak DNS queries when switching VPN servers even though the "Always-on VPN" feature was enabled with the "Block connections without VPN" option.


Bleeping Computer
A Mullvad VPN user has discovered that Android devices leak DNS queries when switching VPN servers even though the "Always-on VPN" feature was enabled with the "Block connections without VPN" option.


Infosecurity News
The US warns that the North Korea-linked Kimsuky group is exploiting poorly configured DMARC protocols to spoof legitimate domains in espionage phishing campaigns

The Hacker News
U.S. government warns of North Korean hackers sending spoofed emails to gather intelligence.


SC Magazine
The state-sponsored group is exploiting weak DMARC policies to impersonate legitimate domains.


The Record
The FBI, NSA are warning that the group labeled Kimsuky is exploiting improperly configured instances of DMARC, an email security tool, to send messages intended to trick recipients into thinking they came from legitimate sources.


DarkReading
Organizations can go a long way toward preventing spoofing attacks by changing one basic parameter in their DNS settings.


SecurityWeek
With so many vendors, approaches and solutions, how do you know what cybersecurity solutions you should be investing in?

SecurityWeek
Verizon 2024 DBIR shows that vulnerability exploitation increased three times and confirmed data breaches doubled compared to 2023.


DarkReading
DMARC adoption is more important than ever following Google's and Yahoo's latest mandates for large email senders. This Tech Tip outlines what needs to be done to enable DMARC on your domain.


The Hacker News
A new botnet called Goldoon is targeting D-Link routers with a critical vulnerability from 2015 (CVE-2015-2051).


The Hacker News
Attention SOHO router users! A new malware called Cuttlefish is on the prowl, stealthily monitoring your traffic and stealing authentication data.

The Record
Anne Neuberger, deputy national security adviser for cyber, talks with the Click Here podcast team about the big picture for mitigating cybersecurity risk in the U.S., the growing cyberthreat from China, the government's relationship with Microsoft and the White House’s latest cyber initiatives.

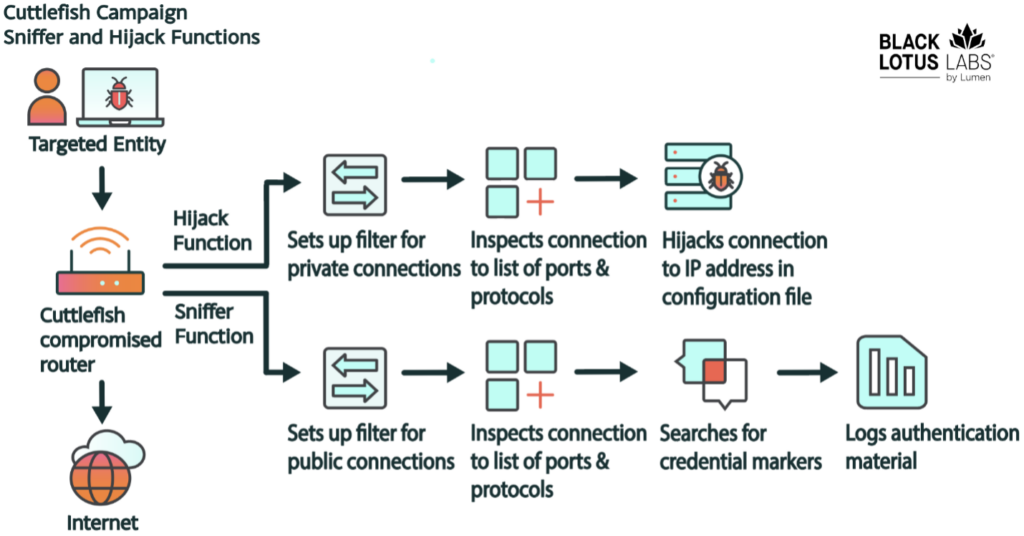
Security Affairs
Cuttlefish malware targets enterprise-grade and small office/home office (SOHO) routers to harvest public cloud authentication data.


DarkReading
The newly discovered malware, which has so far mainly targeted Turkish telcos and has links to HiatusRat, infects routers and performs DNS and HTTP hijacking attacks on connections to private IP addresses


HACKRead
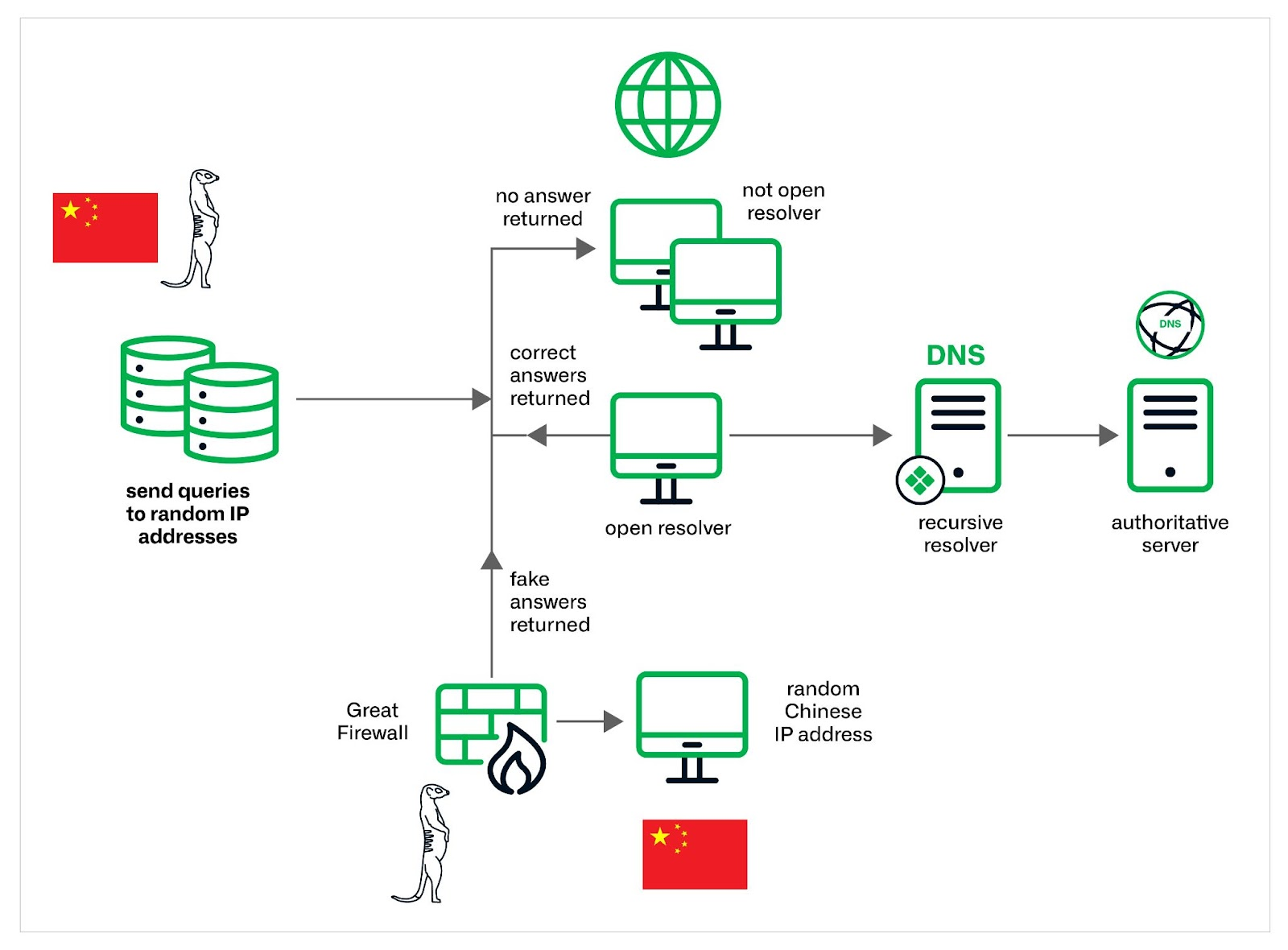
Uncover the "Muddling Meerkat," a China-linked threat actor manipulating the DNS. Infoblox research reveals a sophisticated group with deep DNS expertise and potential ties to the Great Firewall. Learn their tactics and how to stay protected.


SecurityWeek
Malware platform roaming around enterprise SOHO routers capable of covertly harvesting public cloud authentication data from internet traffic.

Bleeping Computer
A new malware named 'Cuttlefish' has been spotted infecting enterprise-grade and small office/home office (SOHO) routers to monitor data that passes through them and steal authentication information.

Security Affairs
The China-linked threat actors Muddling Meerkat are manipulating DNS to probe networks globally since 2019..


Bleeping Computer
A new Android backdoor malware named 'Wpeeper' has been spotted in at least two unofficial app stores mimicking the Uptodown App Store, a popular third-party app store for Android devices with over 220 million downloads.


SecurityWeek
Muddling Meerkat conducts operations through DNS by creating large volumes of widely distributed queries that are propagated using open DNS resolvers.


Cyber Security News
Hackers exploit DNS vulnerabilities to redirect users to malicious websites, launch distributed denial-of-service (DDoS) attacks by

.webp)
Cyber Security News
This sophisticated backdoor Trojan to infiltrate Android systems & execute a malicious commands, posing a threat to unsuspecting users.

Bleeping Computer
A new cluster of activity tracked as "Muddling Meerkat" is believed to be linked to a Chinese state-sponsored threat actor's manipulation of DNS to probe networks globally since October 2019, with a spike in activity observed in September 2023.


Infosecurity News
The top malicious domains attracted over 100,000 hits each, according to Akamai Security


DarkReading
Likely China-linked adversary has blanketed the Internet with DNS mail requests over the past five years via open resolvers, furthering Great Firewall of China ambitions. But the exact nature of its activity is unclear.


The Hacker News
The "Muddling Meerkat" threat actor is abusing DNS open resolvers to evade detection and conduct reconnaissance across the globe.

The DFIR Report
Key Takeaways In August 2023, we observed an intrusion that started with a phishing campaign using PrometheusTDS to distribute IcedID. IcedID dropped and executed a Cobalt Strike beacon, which was … Read More

The Record
Britain now has IoT hardware standards that ban weak or easily guessable default passwords such as “admin” or “12345." Manufacturers are also required to publish contact details so users can report bugs.


Bleeping Computer
Security researchers analyzing phishing campaigns that target United States Postal Service (USPS) saw that the traffic to the fake domains is typically similar to what the legitimate site records and it is even higher during holidays.


Cyber Security News
Welcome to this week's edition of the Cyber Security News Weekly Round-Up. This issue covers the latest vulnerabilities, cyber attacks, and emerging threats that have been making headlines. Stay informed and stay secure!

Cyber Security News
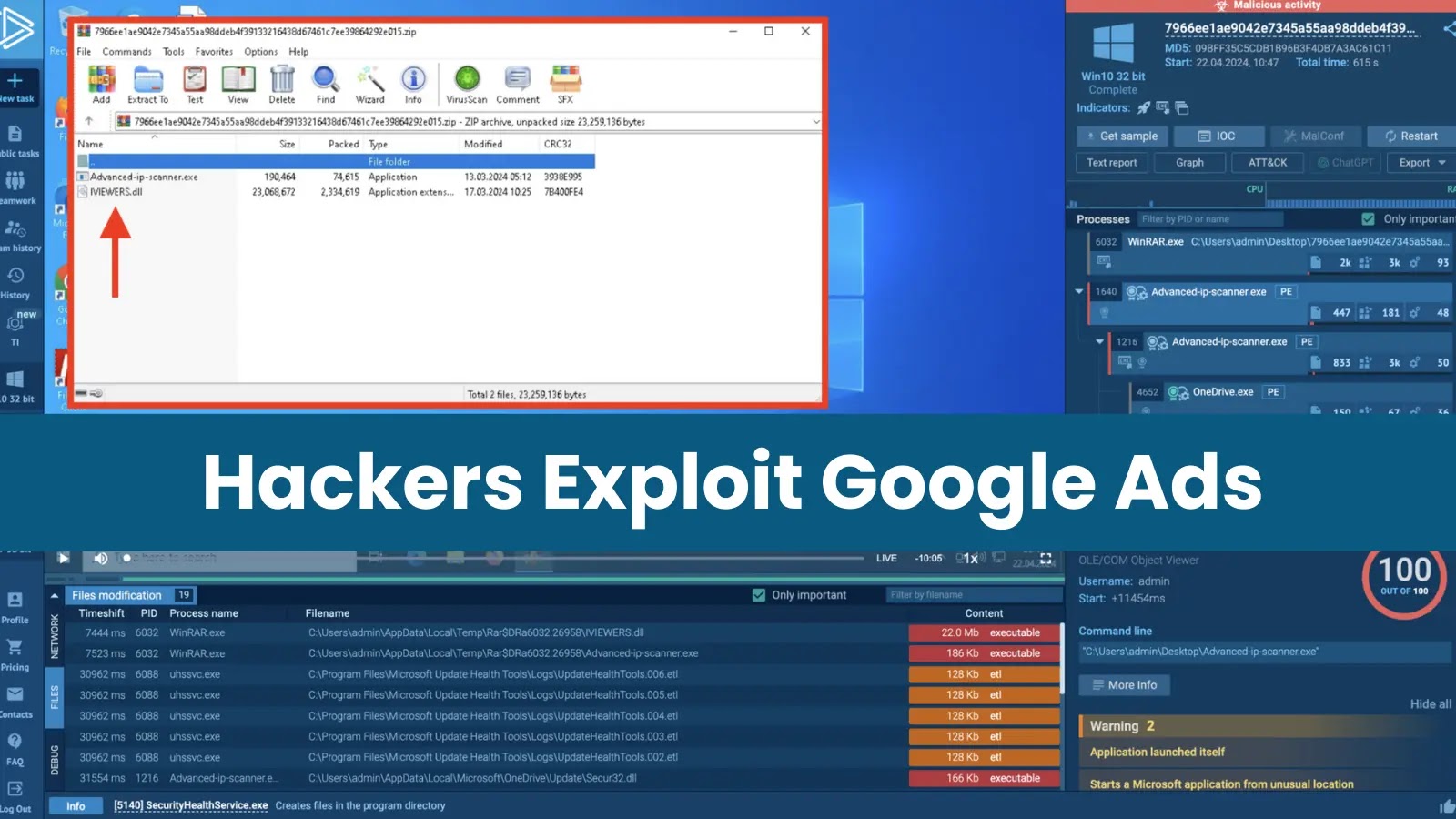
Malicious actors are distributing a new backdoor, MadMxShell, through a Google Ads campaign that impersonates an IP scanner.


Bleeping Computer
Reddit is investigating a major outage blocking users worldwide from accessing the social network's websites and mobile apps.


SecurityWeek
A North Korea-linked threat actor hijacked the update mechanism of eScan antivirus to deploy backdoors and cryptocurrency miners.

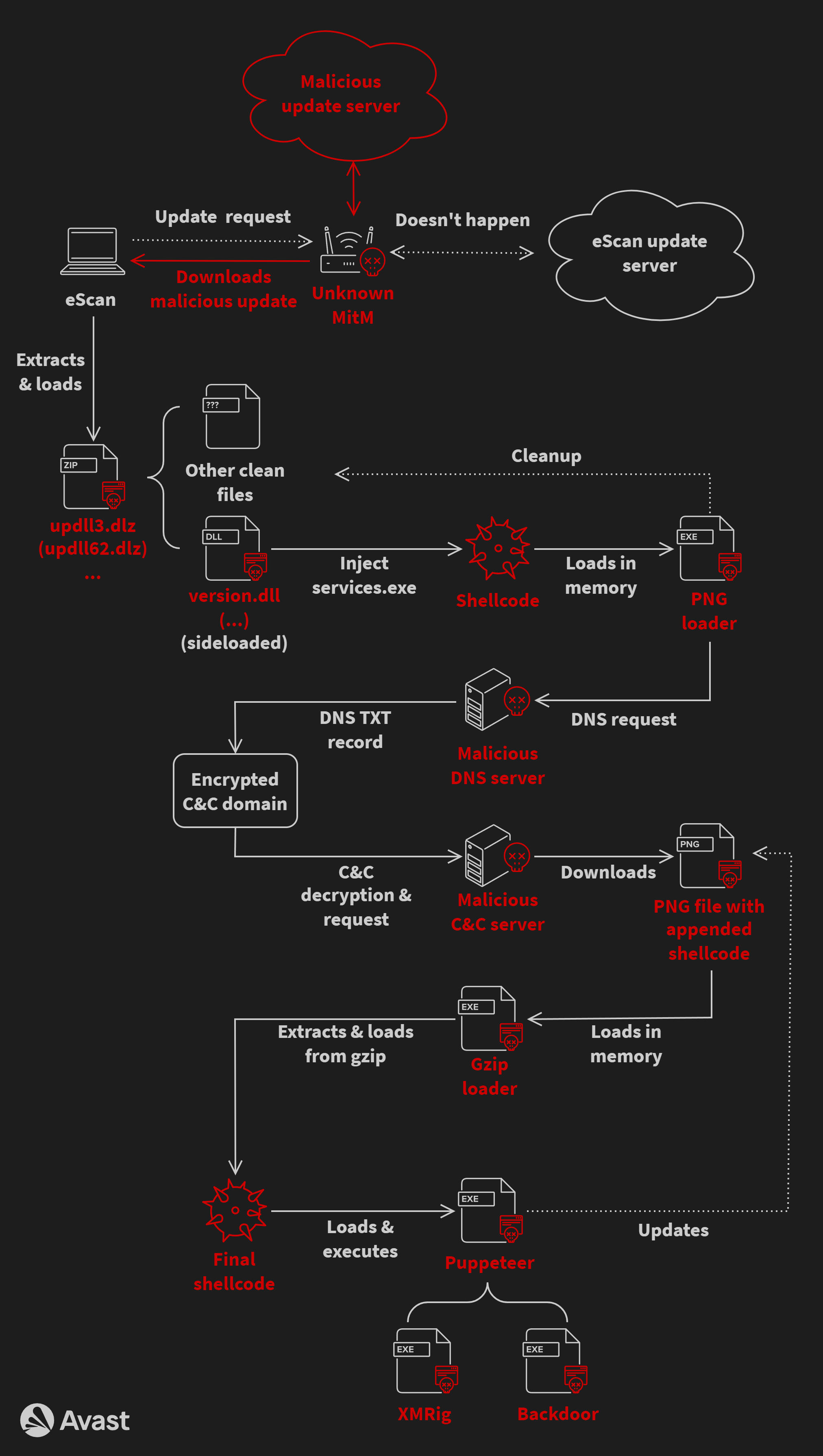
Security Affairs
A malware campaign has been exploiting the updating mechanism of the eScan antivirus to distribute backdoors and cryptocurrency miners.


The Hacker News
A sophisticated malware called GuptiMiner has been leveraging a flaw in eScan antivirus updates to spread backdoors and crypto miners across corporate


Ars Technica
eScan AV updates were delivered over HTTP for five years.


Bleeping Computer
North Korean hackers have been exploiting the updating mechanism of the eScan antivirus to plant backdoors on big corporate networks and deliver cryptocurrency miners through GuptiMiner malware.

Cyber Security News
A sophisticated malware campaign has been compromising the update mechanism of eScan antivirus software to distribute malicious backdoors and cryptocurrency mining software.


The Hacker News
Hackers linked to Russia have been exploiting a Windows bug for YEARS to deploy GooseEgg malware for escalating attack access.


HACKRead
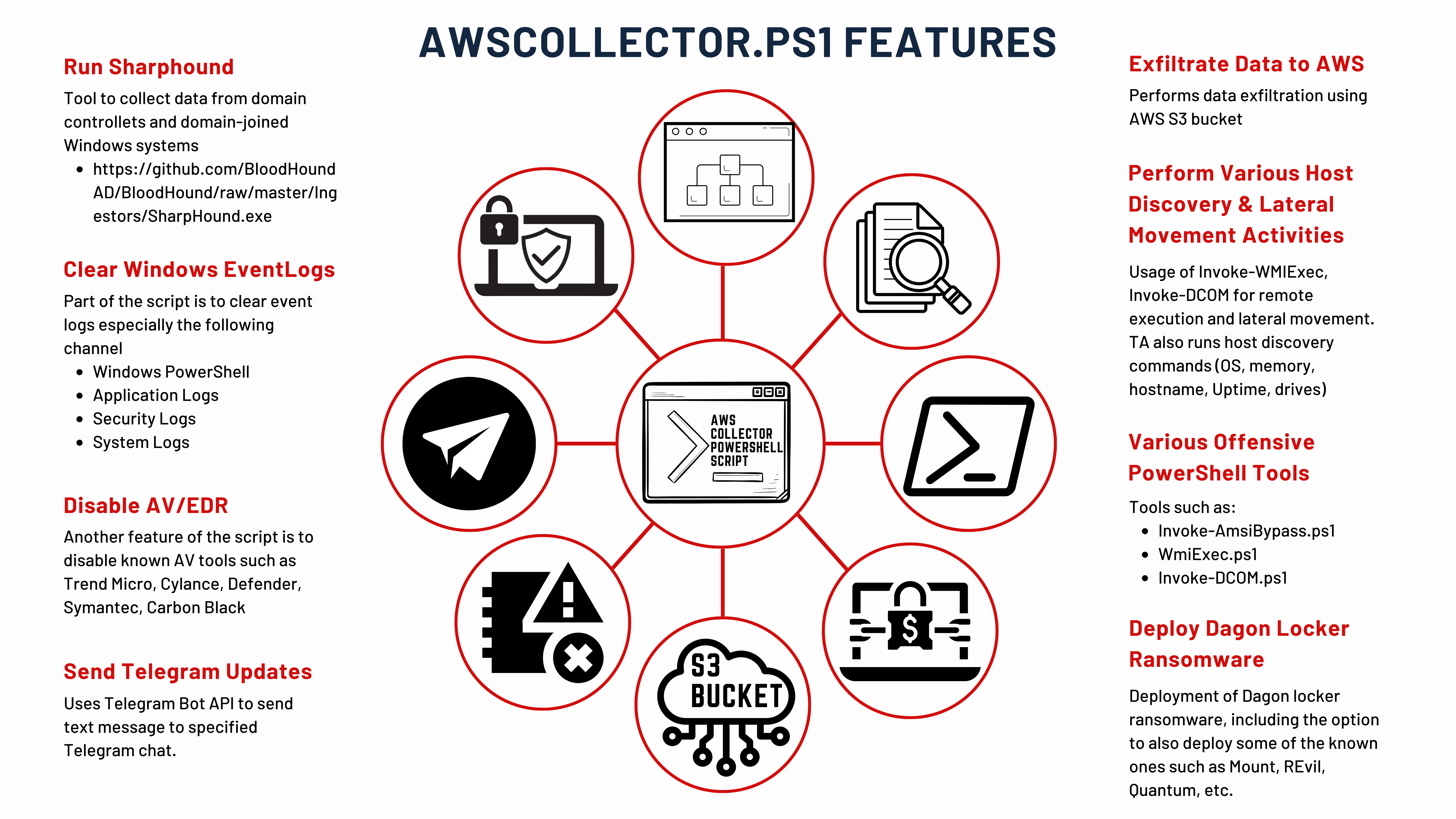
Cybersecurity researchers at Zscaler ThreatLabz believe that the primary target of the MadMxShell backdoor seems to be IT professionals.


Infosecurity News
Zscaler also confirmed MadMxShell uses DLL sideloading and DNS tunneling for C2 communication

.webp)
Cyber Security News
Security researchers uncovered a sophisticated malvertising campaign targeting IT professionals, particularly those in security.


The Hacker News
Hackers are using fake domains of popular IP scanners like Advanced IP Scanner & ManageEngine in a Google Ads malvertising scheme to spread malware.


SC Magazine
Security pros say using Windows backdoor in a malvertising campaign could expose companies to other malware attacks.


SecurityWeek
Second identifier, CVE-2024-3272, assigned to unpatched D-Link NAS device vulnerabilities, just as exploitation attempts soar.


The Cyber Express
An active exploitation of critical vulnerabilities in D-Link Network Attached Storage (NAS) devices has raised concerns for D-Link users exposing


Computerworld
Although there have been no reports of zero-day flaws, Microsoft’s April Patch Tuesday release included 149 updates.


Security Affairs
US Cybersecurity and Infrastructure Security Agency (CISA) adds D-Link NAS devices bugs to its Known Exploited Vulnerabilities catalog


The Cyber Express
Microsoft has released the latest Patch Tuesday update, addressing a large number of vulnerabilities across various products and services. The


Security Affairs
Microsoft addressed two zero-day vulnerabilities (CVE-2024-29988 and CVE-2024-26234) actively exploited by threat actors to deliver malware


The Cyber Express
IntelBroker has asserted responsibility for the Accor data breach and purportedly offers the data, containing 642,000 user records, for sale.


The Record
The Cybersecurity and Infrastructure Security Agency added two bugs in older D-Link hardware to its Known Exploited Vulnerabilities list. Experts say 92,000 devices could be exposed.


Security Affairs
Microsoft Patches Tuesday security updates for April 2024 addressed three Critical vulnerabilities, none actively exploited in the wild. Microsoft Patches Tuesday security updates for April 2024 addressed 147 vulnerabilities in multiple products. This is the highest number of fixed issues from Microsoft this year and the largest since at least 2017. The issues impact Microsoft […]


Security Affairs
Microsoft Patches Tuesday security updates for April 2024 addressed three Critical vulnerabilities, none actively exploited in the wild.

.webp)
Cyber Security News
By displaying sponsored search results for utilities like PuTTY and FileZilla, the attackers can lure in their victims.


DarkReading
Microsoft patched a record number of 147 new CVEs this month, though only three are rated "Critical."


SecurityWeek
Microsoft documents a serious vulnerability that allows unauthenticated hackers to take complete control of Azure Kubernetes clusters.


Bleeping Computer
Today is Microsoft's April 2024 Patch Tuesday, which includes security updates for 150 flaws and sixty-seven remote code execution bugs.


DarkReading
The company is asking users to retire several network-attached storage (NAS) models to avoid compromise through a publicly available exploit that results in backdooring.


CyberNews
Cybernews asked cybersecurity professionals how they would allocate a limited budget for the greatest impact on home security.

Cyber Security News
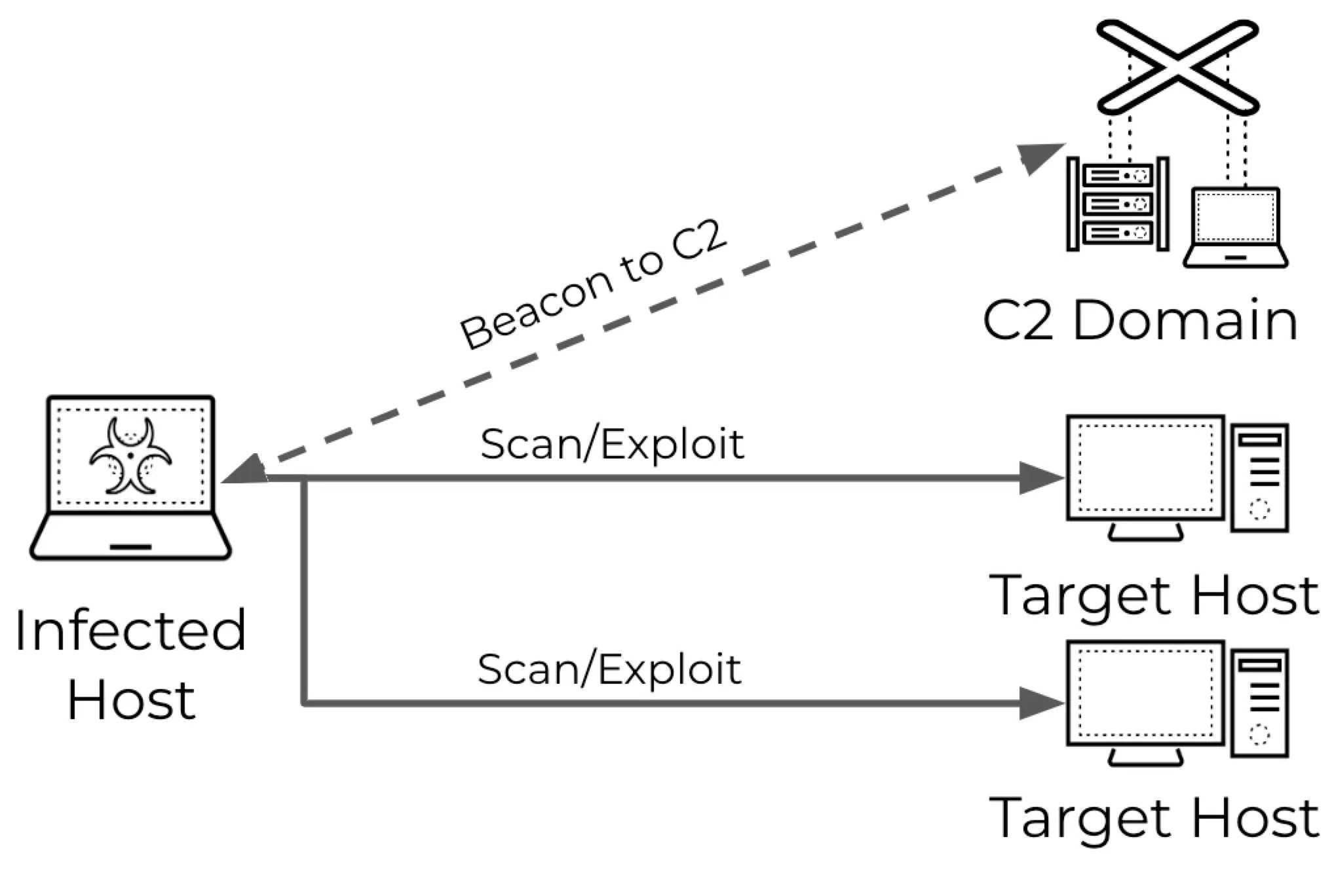
Adversaries are increasingly utilizing malware-infected devices to perform scans on target networks, shifting away from traditional direct


Infosecurity News
Threat actors are targeting a high severity vulnerability in close to 100,000 legacy D-Link devices


SecurityWeek
Unpatched D-Link NAS device vulnerability CVE-2024-3273, potentially affecting many devices, is being exploited in the wild.


The Hacker News
Hackers are exploiting vulnerabilities (CVE-2024-3272 and CVE-2024-3273) in D-Link NAS devices. Up to 92,000 devices affected.


SC Magazine
An attacker could gain remote access to network-attached storage and execute arbitrary commands.

Krebs on Security
If only Patch Tuesdays came around infrequently -- like total solar eclipse rare -- instead of just creeping up on us each month like The Man in the Moon. Although to be fair, it would be tough for Microsoft to…


Bleeping Computer
Attackers are now actively targeting over 92,000 end-of-life D-Link Network Attached Storage (NAS) devices exposed online and unpatched against a critical remote code execution (RCE) zero-day flaw.


Ars Technica
D-Link won't be patching vulnerable NAS devices because they're no longer supported.


CyberSecurity Dive
The networking hardware vendor advised owners of the affected devices to retire and replace them. There is no patch available for the vulnerability.


DarkReading
An ongoing cyberattack with ties to China uses new version of sophisticated JSOutProx Trojan, now targeting banks in the Middle East.


SC Magazine
More than 92,000 outdated internet-exposed D-Link Network Attached Storage devices could be breached in attacks exploiting a newly discovered arbitrary command injection and hardcoded backdoor vulnerability, tracked as CVE-2024-3273, which could result in sensitive data access, system configuration modifications, and denial-of-service conditions, reports Security Affairs.
Loading more articles....