

CSO
US AI experts targeted in cyberespionage campaign using SugarGh0st RAT
Threat actors use phishing techniques to obtain non-public information about generative artificial intelligence.


CSO
Threat actors use phishing techniques to obtain non-public information about generative artificial intelligence.


DarkReading
Researchers believe the attacker is likely China-affiliated, since a previous version of the malware was used by a China nation-state attack group.


Infosecurity News
Proofpoint said the attackers modified registry key names for persistence


Bleeping Computer
Security researchers discovered two previously unseen backdoors dubbed LunarWeb and LunarMail that were used to compromise a European government's diplomatic institutions abroad.


The Hacker News
Kimsuky hackers launch new social engineering attack using fake Facebook accounts. Learn how they target activists via Messenger and deliver malware.


Bleeping Computer
The North Korean hacker group Kimsuki has been using a new Linux malware called Gomir that is a version of the GoBear backdoor delivered via trojanized software installers.


Bleeping Computer
The North Korean hacker group Kimsuki has been using trojanized software packages to deliver a new Linux malware called Gomir in cyberespionage campaigns against targets in South Korea.


Cyber Security News
Remote assist tools are often targeted by hackers as they create a direct channel that can be used to get into desired systems while using

.webp)
Cyber Security News
The well-known advanced persistent threat (APT) group Turla, which is based in Russia, is said to be going after the European Ministry.

.webp)
Cyber Security News
Cybercriminals have been exploiting GitHub, a platform widely trusted by developers, to host malicious infrastructure.


HACKRead
A new Android malware poses as popular applications like WhatsApp, Instagram, and Snapchat to steal user data, including login credentials.


Infosecurity News
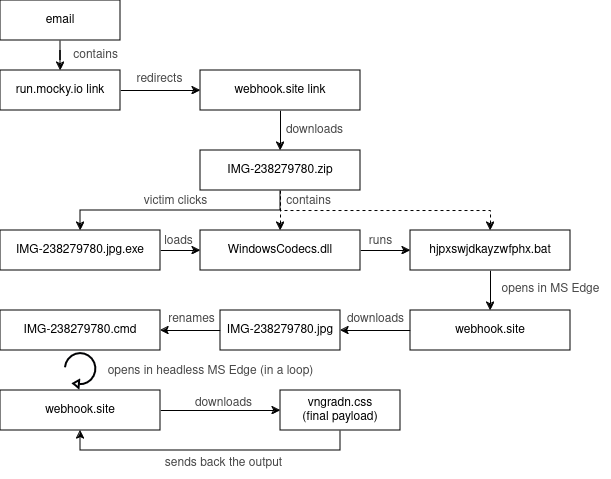
Recorded Future details a novel campaign that abuses legitimate internet services to deploy multiple malware variants for credential theft

HACKRead
DNS tunneling is being used to bypass security filters by hiding malicious traffic in DNS packets, allowing hackers to steal stolen data.


DarkReading
Several campaigns are leveraging the evasive tactic to provide useful insights into victims' online activities, and find new ways to compromise organizations.


The Hacker News
A new social engineering campaign is targeting enterprises with spam emails to gain initial access. The threat actor overwhelms users' email and calls


Cyber Security News
Recent email campaigns distribute DanaBot malware through two document types: those using equation editor exploits and those containing

Security Affairs
Experts reported that since April, the Phorpiex botnet sent millions of phishing emails to spread LockBit Black ransomware


Bleeping Computer
A new package mimicked the popular 'requests' library on the Python Package Index (PyPI) to target macOS devices with the Sliver C2 adversary framework, used for gaining initial access to corporate networks.


DarkReading
Ransomware groups have always created problems for their victims that only they could solve. Black Basta is taking that core idea in a creative, new direction.


Bleeping Computer
Threat actors are using Domain Name System (DNS) tunneling to track when their targets open phishing emails and click on malicious links, and to scan networks for potential vulnerabilities.


Cyber Security News
An attacker published a malicious package on PyPI named "requests-darwin-lite," masquerading as a variant of the popular "requests" library,


The Hacker News
Researchers found a malicious Python package called requests-darwin-lite hiding a sneaky malware.


SC Magazine
The “requests-darwin-lite” package was downloaded more than 400 times before its removal.

Security Affairs
CERT Polska warns of a large-scale malware campaign against Polish government institutions conducted by Russia-linked APT28.


The Hacker News
Fake Android apps mimicking popular platforms like Google & WhatsApp are stealing user data.


Cyber Security News
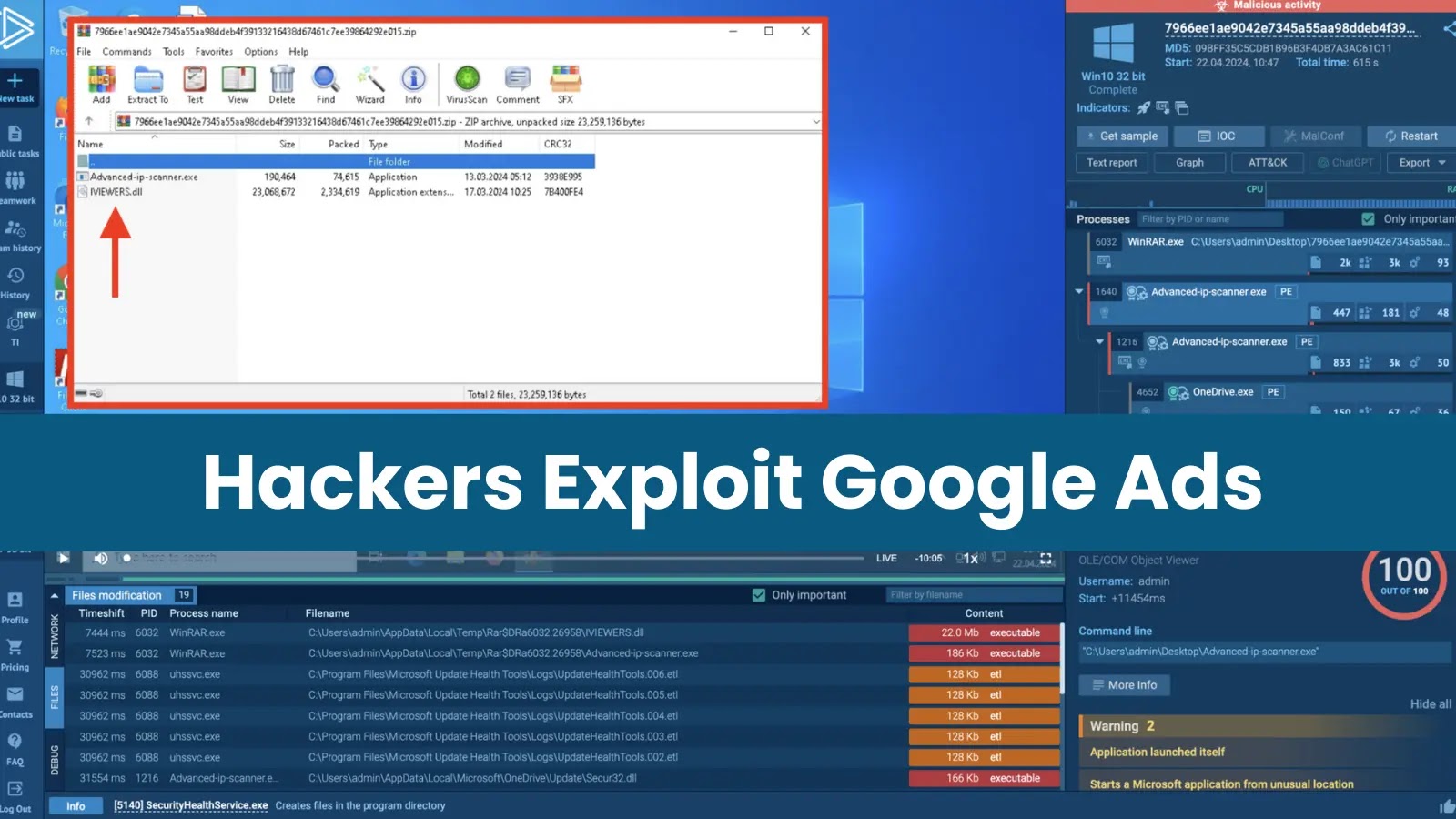
Hackers take advantage of sponsored Google Ads as they provide an excellent chance to quickly reach a large audience.


Bleeping Computer
Poland says a state-backed threat group linked to Russia's military intelligence service (GRU) has been targeting Polish government institutions throughout the week.


DarkReading
MITRE's hackers made use of at least five different Web shells and backdoors as part of their attack chain.


Security Affairs
MITRE published more details on the recent security breach, including a timeline of the attack and attribution evidence.

%20(1).webp)
Cyber Security News
Kapeka, also known as KnuckleTouch, is a sophisticated backdoor malware that has been making waves in the cybersecurity world.


DarkReading
As Verizon Business redefines "supply chain breach," it could either help organizations address third-party risk holistically or just conflate and confuse.


The Hacker News
New findings suggest the ArcaneDoor cyber espionage campaign targeting network devices from Cisco (CVE-2024-20353, CVE-2024-20359).


Bleeping Computer
The Iranian state-backed threat actor tracked as APT42 is employing social engineering attacks, including posing as journalists, to breach corporate networks and cloud environments of Western and Middle Eastern targets.

Security Affairs
The Ubiquiti EdgeRouter botnet is still used by Russia-linked group APT28 and cybercriminals organizations.


SC Magazine
Microsoft Graph API has become popular with hackers because running criminal ops on widely used cloud services raises less suspicion.


The Hacker News
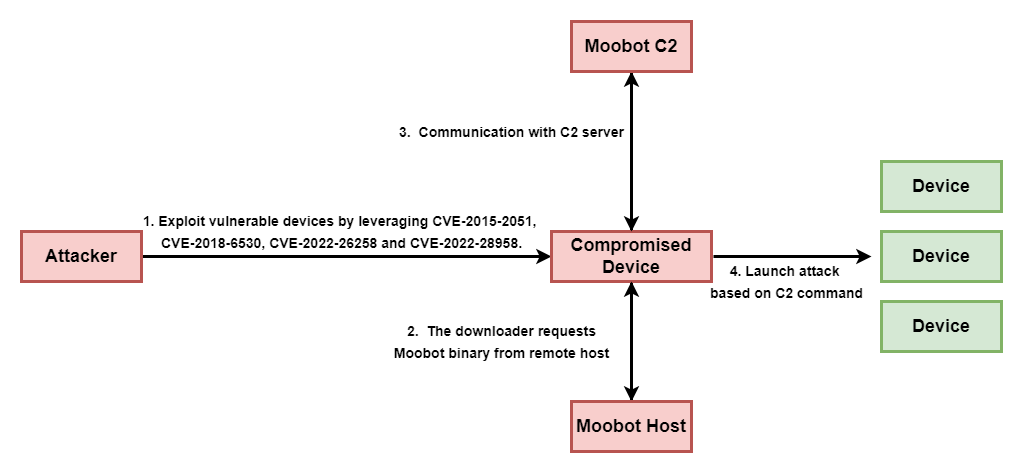
A new botnet called Goldoon is targeting D-Link routers with a critical vulnerability from 2015 (CVE-2015-2051).


DarkReading
Weaponizing Microsoft's own services for command-and-control is simple and costless, and helps attackers better avoid detection.


The Hacker News
Attention SOHO router users! A new malware called Cuttlefish is on the prowl, stealthily monitoring your traffic and stealing authentication data.


DarkReading
A recent campaign targeting Middle Eastern government organizations plays standard detection tools like a fiddle. Cyber defenders must keep pace.

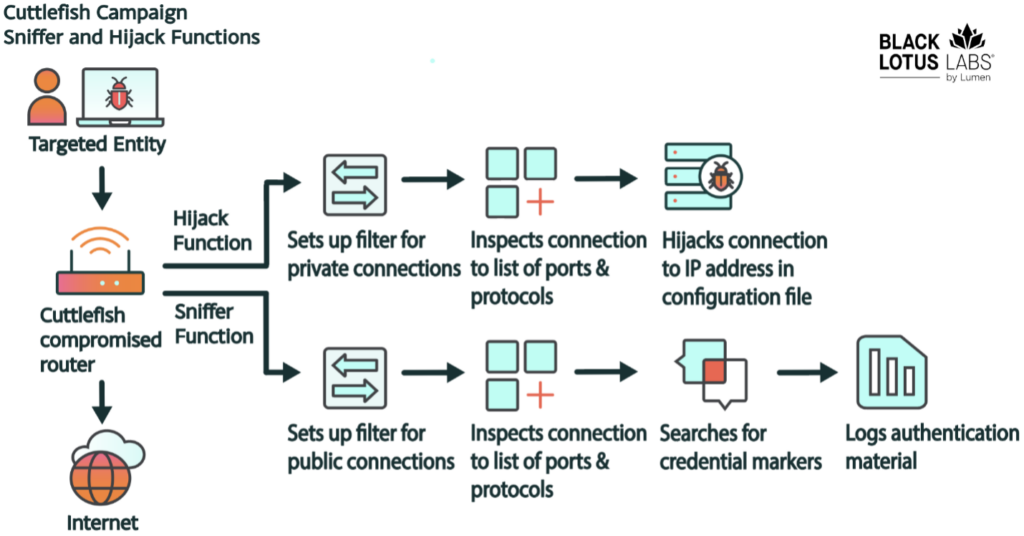
Security Affairs
Cuttlefish malware targets enterprise-grade and small office/home office (SOHO) routers to harvest public cloud authentication data.


DarkReading
The newly discovered malware, which has so far mainly targeted Turkish telcos and has links to HiatusRat, infects routers and performs DNS and HTTP hijacking attacks on connections to private IP addresses

The Hacker News
Researchers have uncovered a new Android malware called Wpeeper that uses compromised WordPress sites to hide its true command-and-control servers.

Bleeping Computer
A new malware named 'Cuttlefish' has been spotted infecting enterprise-grade and small office/home office (SOHO) routers to monitor data that passes through them and steal authentication information.


SecurityWeek
Chinese cybersecurity firm QAX XLab uncovered an Android trojan that hides its command-and-control server behind compromised WordPress sites.


Bleeping Computer
A new Android backdoor malware named 'Wpeeper' has been spotted in at least two unofficial app stores mimicking the Uptodown App Store, a popular third-party app store for Android devices with over 220 million downloads.

Infosecurity News
According to JFrog, approximately 25% of all repositories lack useful functionality and serve as vehicles for spam and malware


The Hacker News
Millions of malicious "imageless" containers have been planted on Docker Hub over the past 5 years in multiple cybercriminal campaigns.

.webp)
Cyber Security News
This sophisticated backdoor Trojan to infiltrate Android systems & execute a malicious commands, posing a threat to unsuspecting users.


Cyber Security News
In a sophisticated cyberattack that unfolded over 29 days, cybersecurity analysts have meticulously traced the steps of threat actors from the initial infection with IcedID malware to the eventual deployment of Dagon Locker ransomware. The detailed account of this cyber intrusion provides a chilling example of how quickly and stealthily cybercriminals can compromise an organization’s […]

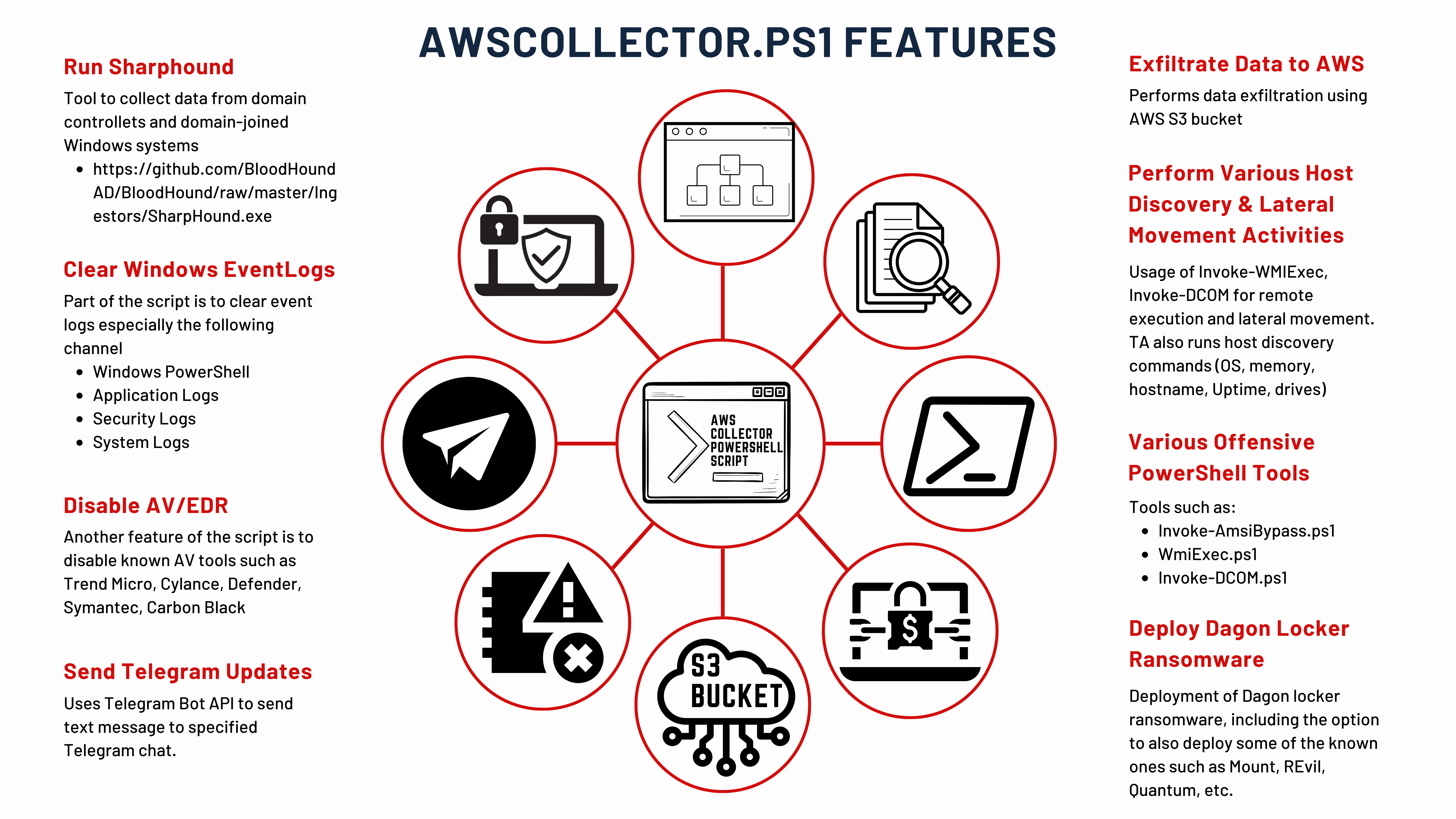
The DFIR Report
Key Takeaways In August 2023, we observed an intrusion that started with a phishing campaign using PrometheusTDS to distribute IcedID. IcedID dropped and executed a Cobalt Strike beacon, which was … Read More

Security Affairs
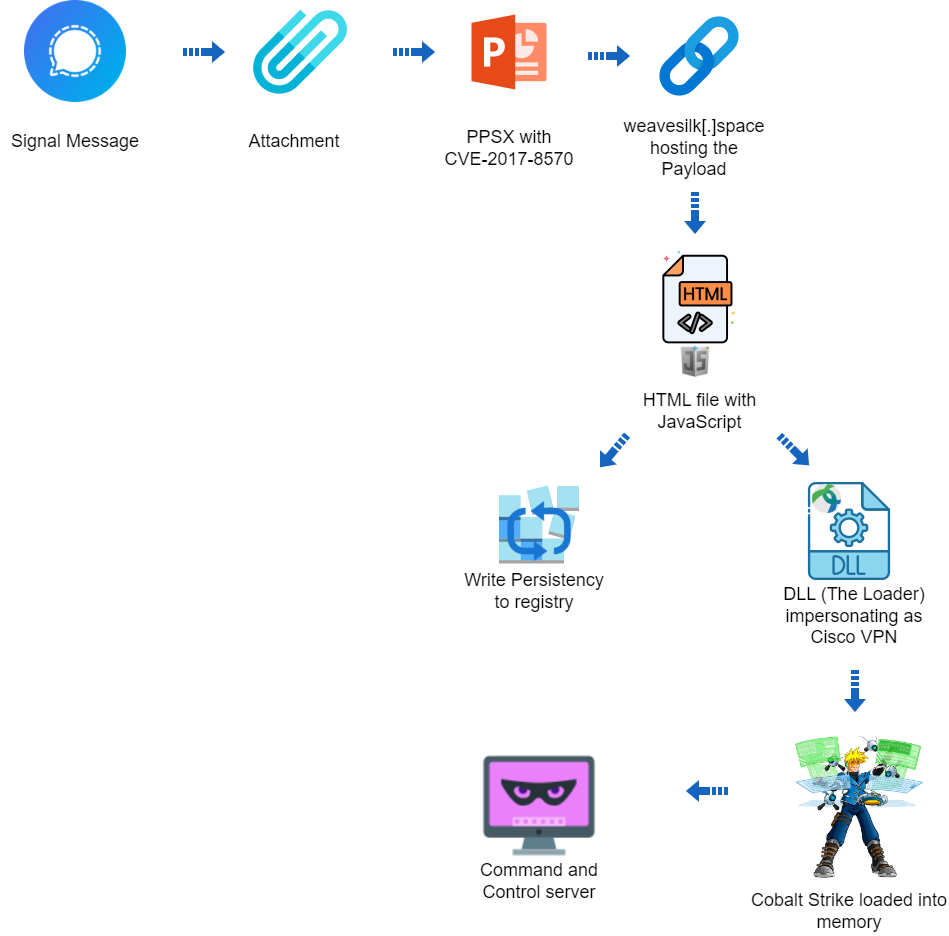
A hacking campaign targeted Ukraine exploiting a seven-year-old vulnerability in Microsoft Office to deliver Cobalt Strike.


The Hacker News
Cybersecurity researchers have uncovered a targeted cyber attack against Ukraine that leveraged a 7-year-old Microsoft Office flaw to deploy Cobalt St

Security Affairs
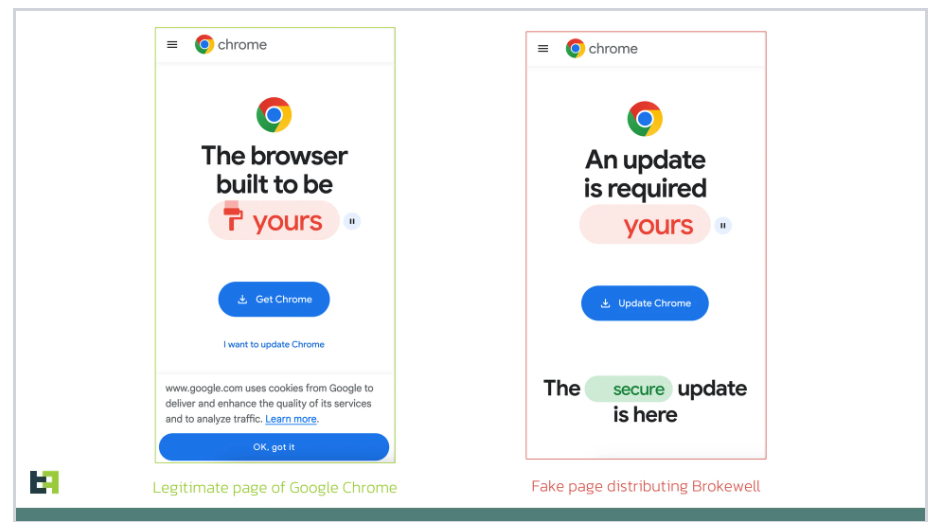
ThreatFabric researchers identified a new Android malware called Brokewell, which implements a wide range of device takeover capabilities.


HACKRead
A recent attack exploited vulnerabilities in systems running outdates Microsoft Office to deliver Cobalt Strike malware. Learn how to protect yourself!


Bleeping Computer
A new campaign tracked as "Dev Popper" is targeting software developers with fake job interviews in an attempt to trick them into installing a Python remote access trojan (RAT).


DarkReading
The targeted operation utilized CVE-2017-8570 as the initial vector and employed a notable custom loader for Cobalt Strike, yet attribution to any known threat actor remains elusive.

Bleeping Computer
Researchers have sinkholed a command and control server for a variant of the PlugX malware and observed in six months more than 2.5 million connections from unique IP addresses.

Cyber Security News
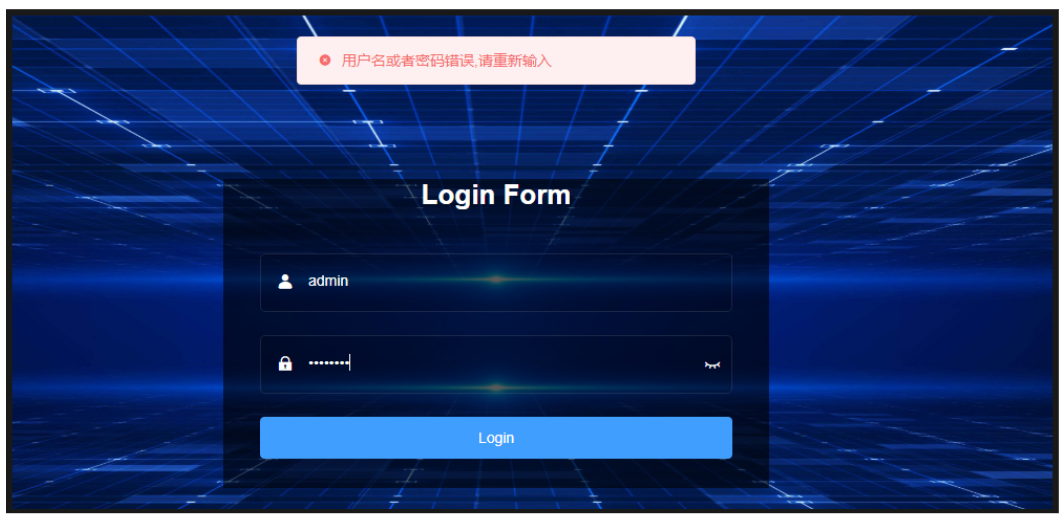
Malicious actors are distributing a new backdoor, MadMxShell, through a Google Ads campaign that impersonates an IP scanner.


The Hacker News
North Korean hackers used fake job offers to deliver a new Trojan called Kaolin RAT. It can change file timestamps and load malware.

.webp)
Cyber Security News
The PlugX USB worm, a piece of malware, has been reported to have infected over 2.5 million devices, posing a threat to global cybersecurity.


Cyber Security News
Black hat SEO methods are used by hackers to manipulate search engine rankings and make malicious or fraudulent websites more visible.

Security Affairs
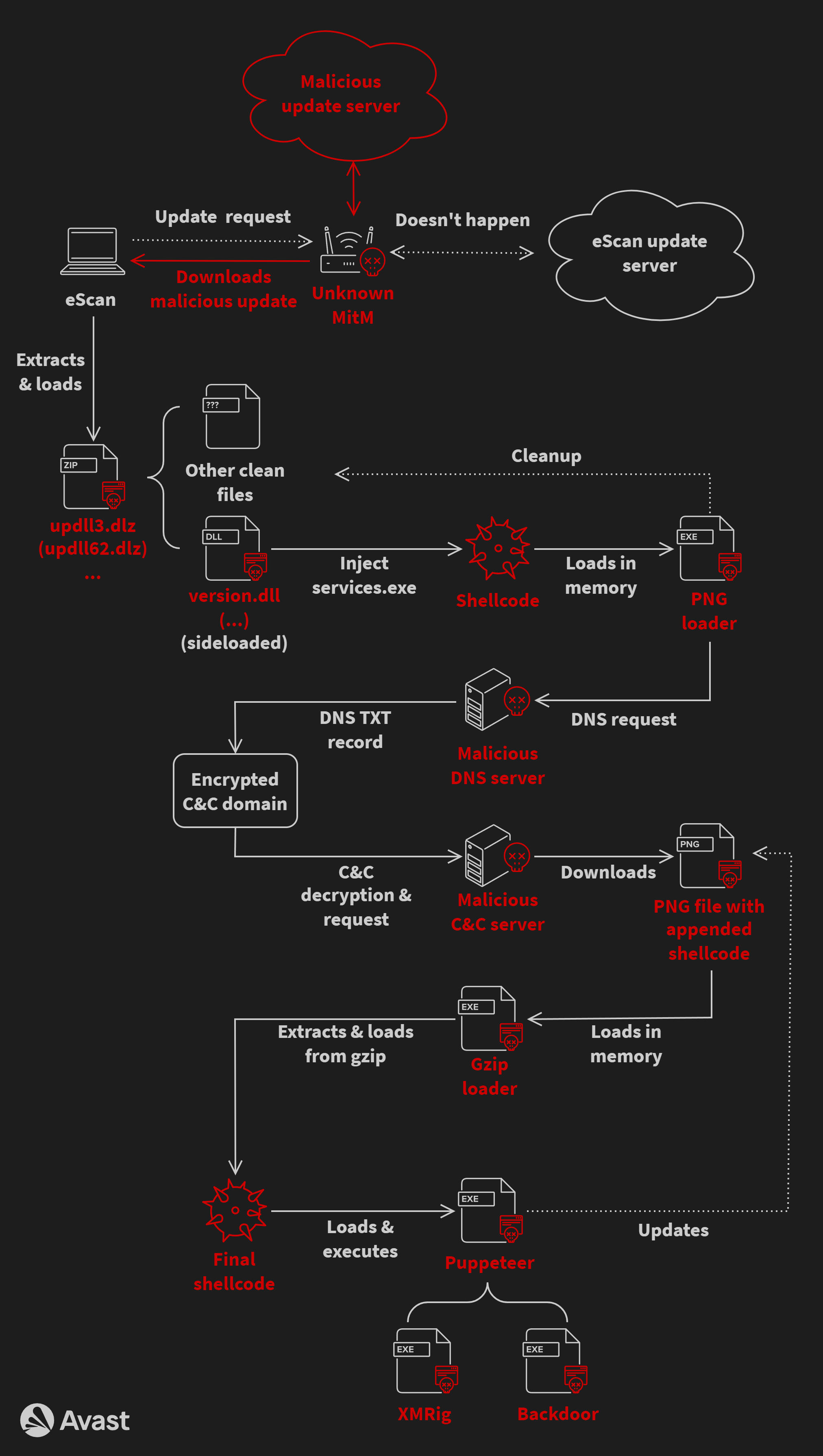
A malware campaign has been exploiting the updating mechanism of the eScan antivirus to distribute backdoors and cryptocurrency miners.


The Hacker News
A sophisticated attack campaign dubbed "FROZEN#SHADOW" is underway, using phishing emails to infect systems with the stealthy malware SSLoad.


The Hacker News
A sophisticated malware called GuptiMiner has been leveraging a flaw in eScan antivirus updates to spread backdoors and crypto miners across corporate


SC Magazine
A new CryptBot variant targets password managers and authentication apps in the new campaign.


Bleeping Computer
A threat actor has been using a content delivery network cache to store information-stealing malware in an ongoing campaign targeting systems U.S., the U.K., Germany, and Japan.


DarkReading
The irony is lost on few, as a Chinese threat actor used eight MITRE techniques to breach MITRE itself — including exploiting the Ivanti bugs that attackers have been swarming on for months.


The Hacker News
Kaspersky has uncovered a concerning threat actor, ToddyCat, targeting government and military entities.

Cyber Security News
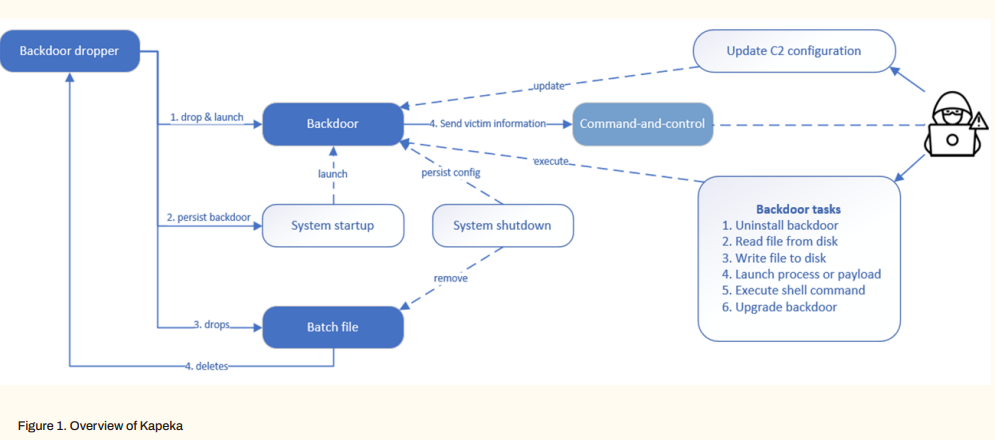
A new backdoor named "Kapeka" has been identified to be attacking victims in Eastern Europe since mid-2022.


HACKRead
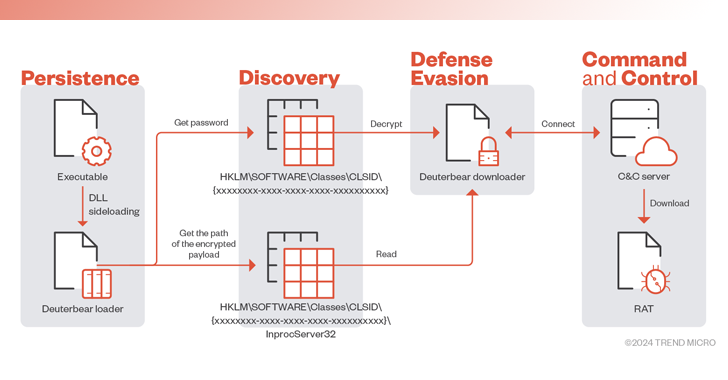
Cybersecurity researchers at Zscaler ThreatLabz believe that the primary target of the MadMxShell backdoor seems to be IT professionals.

Security Affairs
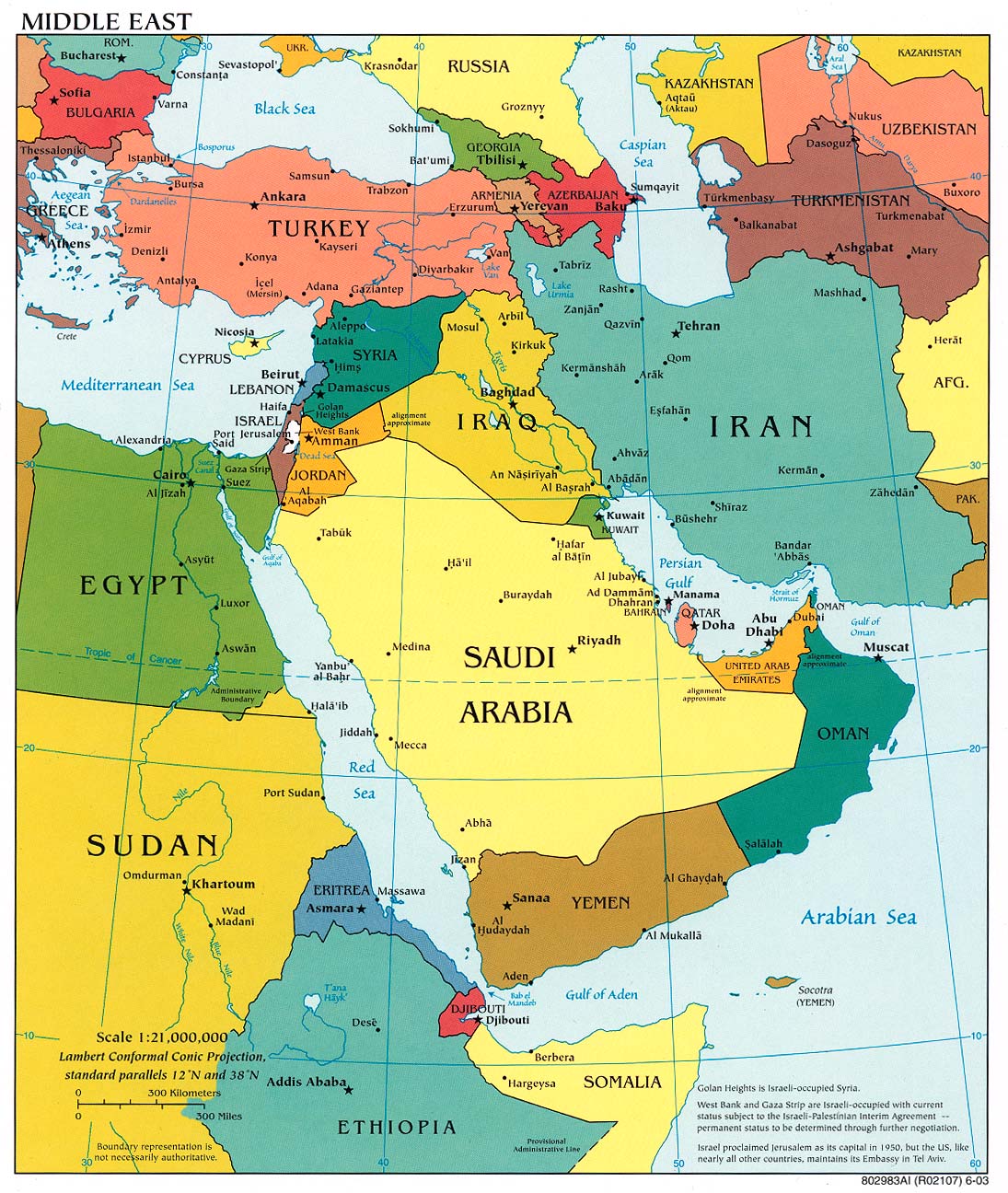
Threat actors target government entities in the Middle East with a new backdoor dubbed CR4T as part of an operation tracked as DuneQuixote.


HACKRead
A surge in attacks from the Androxgh0st malware family uncovers over 600 servers compromised primarily in the U.S., India and Taiwan.


The Hacker News
A new variant of the RedLine Stealer malware has been discovered, utilizing Lua bytecode for stealth and effectiveness.

The Hacker News
China-linked hacking group Earth Hundun is targeting Asia-Pacific tech, research, and government sectors with advanced malware, including "Waterbear"

The Hacker News
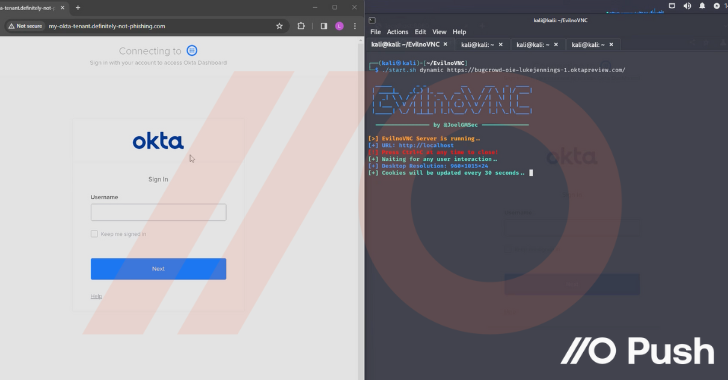
How attackers are hacking organizations without touching the endpoint by targeting cloud identities.


Security Affairs
China-linked threat actors are preparing cyber attacks against U.S. critical infrastructure warned FBI Director Christopher Wray.


The Hacker News
A new threat, 'DuneQuixote', targets Middle East governments with sophisticated evasion tactics.


Bleeping Computer
A new info-stealing malware linked to Redline poses as a game cheat called 'Cheat Lab,' promising downloaders a free copy if they convince their friends to install it too.


Infosecurity News
Zscaler also confirmed MadMxShell uses DLL sideloading and DNS tunneling for C2 communication


Cyber Security News
Redline Stealer is a powerful information-stealing malware and hackers often exploit this stealthy stealer to gain unauthorized access to a


The Hacker News
Ever worried about malware in PDFs? ANY.RUN's sandbox can expose hidden threats just by analyzing the file's structure.

Security Affairs
Russia-linked APT Sandworm employed a previously undocumented backdoor called Kapeka in attacks against Eastern Europe since 2022.

.webp)
Cyber Security News
Security researchers uncovered a sophisticated malvertising campaign targeting IT professionals, particularly those in security.


The Hacker News
Vulnerabilities in OpenMetadata are being exploited. These critical security flaws enable hackers to get into Kubernetes environments.


The Hacker News
Hackers are using fake domains of popular IP scanners like Advanced IP Scanner & ManageEngine in a Google Ads malvertising scheme to spread malware.


SC Magazine
Security pros say using Windows backdoor in a malvertising campaign could expose companies to other malware attacks.


SC Magazine
A cryptominer campaign leveraged five vulnerabilities in OpenMetadata to infect environments.

SecurityWeek
Kapeka is a new backdoor that may be a new addition to Russia-link Sandworm’s malware arsenal and possibly a successor to GreyEnergy.

Security Affairs
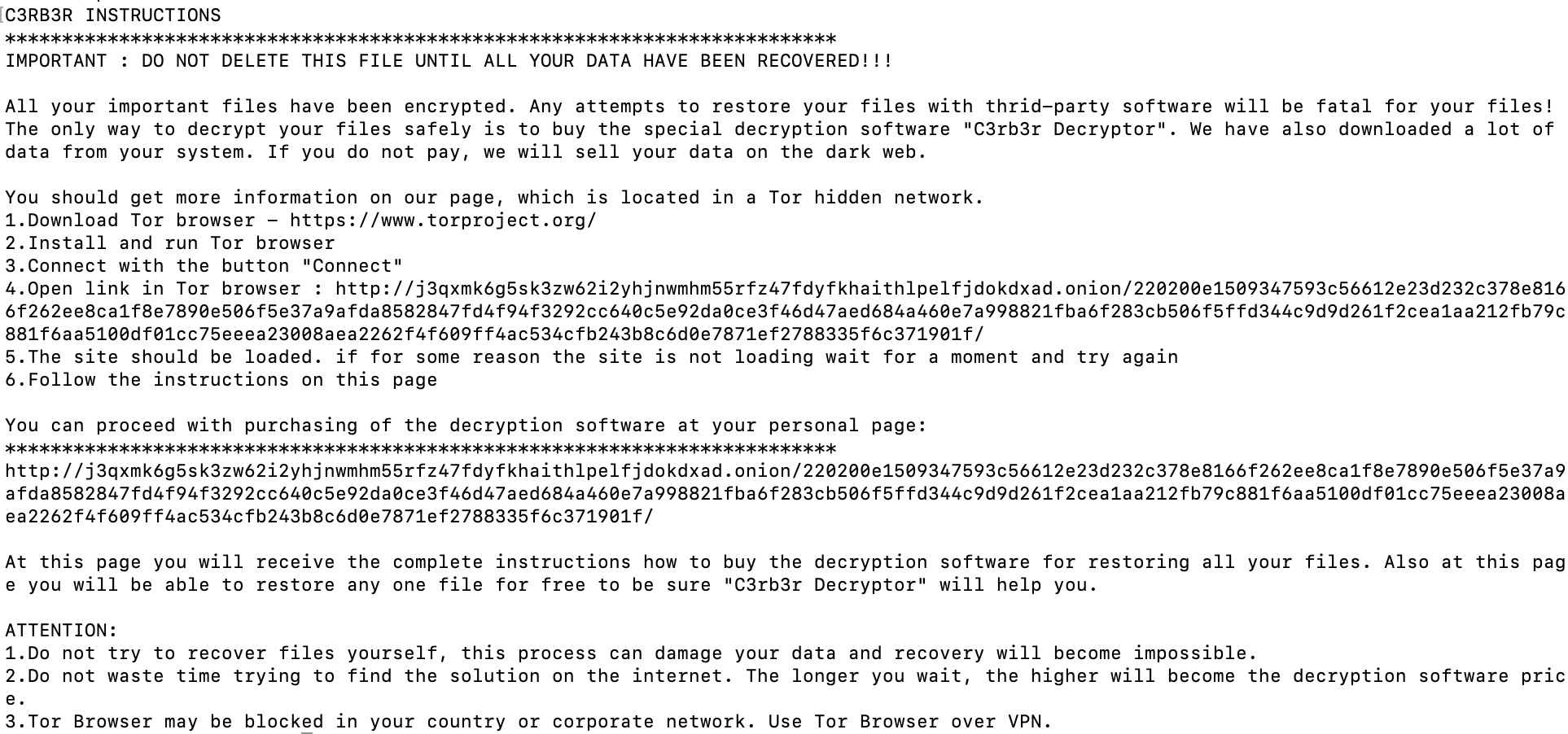
Threat actors are exploiting the CVE-2023-22518 flaw in Atlassian servers to deploy a Linux variant of Cerber (aka C3RB3R) ransomware.


DarkReading
Moobot, Miori, AGoent, and a Gafgyt variant have joined the infamous Mirai botnet in attacking unpatched versions of vulnerable Wi-Fi routers.


The Hacker News
A new stealthy backdoor malware called Kapeka, likely created by Russia's APT group Sandworm, has been targeting Eastern Europe.


The Hacker News
Hackers are exploiting a critical vulnerability in Atlassian servers to gain admin access and deploy a Linux variant of Cerber ransomware.


The Hacker News
If you use Fortinet FortiClient EMS, patch NOW. Hackers are actively using a new exploit


Infosecurity News
WithSecure researchers said it is likely Russian state group Sandworm has added a novel backdoor dubbed ‘Kapeka’ to its arsenal


SC Magazine
Attackers exploited a critical vulnerability to create a new administrator account.

Security Affairs
Researchers warn of a renewed cyber espionage campaign targeting users in South Asia with the Apple iOS spyware LightSpy


Bleeping Computer
A new campaign conducted by the TA558 hacking group is concealing malicious code inside images using steganography to deliver various malware tools onto targeted systems.


DarkReading
A Russian-language campaign impersonates legitimate game operations to spread cross-platform infostealers.

Cyber Security News
we’ll dissect a timely example of credential theft—StrelaStealer—to identify the malware’s characteristics and capabilities.


The Hacker News
A sophisticated cyber-espionage campaign has re-emerged, targeting South Asia with an iOS spyware implant called LightSpy.
Loading more articles....