

CSO
US AI experts targeted in cyberespionage campaign using SugarGh0st RAT
Threat actors use phishing techniques to obtain non-public information about generative artificial intelligence.


CSO
Threat actors use phishing techniques to obtain non-public information about generative artificial intelligence.


DarkReading
Researchers believe the attacker is likely China-affiliated, since a previous version of the malware was used by a China nation-state attack group.


Infosecurity News
Proofpoint said the attackers modified registry key names for persistence


The Hacker News
A new social engineering campaign is targeting enterprises with spam emails to gain initial access. The threat actor overwhelms users' email and calls


SC Magazine
Emails from “Jenny Green” delivered LockBit Black through attached ZIP files.


Bleeping Computer
Since April, millions of phishing emails have been sent through the Phorpiex botnet to conduct a large-scale LockBit Black ransomware campaign.


The Cyber Express
The ever-evolving digital landscape presents a constant challenge for businesses and individuals alike: staying secure in the face of increasingly


Infosecurity News
Well-funded cybercriminals are adopting more sophisticated techniques, creating a need for defenders to stay informed about the evolving threat landscape


SecurityWeek
Hundreds of companies are showcasing their products and services this week at the 2024 edition of the RSA Conference in San Francisco.

The Hacker News
U.S. government warns of North Korean hackers sending spoofed emails to gather intelligence.


CSO
Mandiant observed several malicious campaigns with threat actors impersonating journalists and harvesting the victim’s cloud environment credentials.


Bleeping Computer
Latrodectus malware is now being distributed in phishing campaigns using Microsoft Azure and Cloudflare lures to appear legitimate while making it harder for email security platforms to detect the emails as malicious.

.webp)
Cyber Security News
The hacker group known as TransparentTribe, also referred to as APT-36, has intensified its cyber espionage activities.


The Hacker News
North Korea's state-linked hackers are enhancing their operations with advanced artificial intelligence tools.


Infosecurity News
Proofpoint confirmed Kimsuky has directly contacted foreign policy experts since 2023 through seemingly benign email conversations


The Hacker News
MuddyWater, linked to Iran's MOIS, strikes again with DarkBeatC2. Our latest blog unpacks the latest tactics in cyber warfare.

Security Affairs
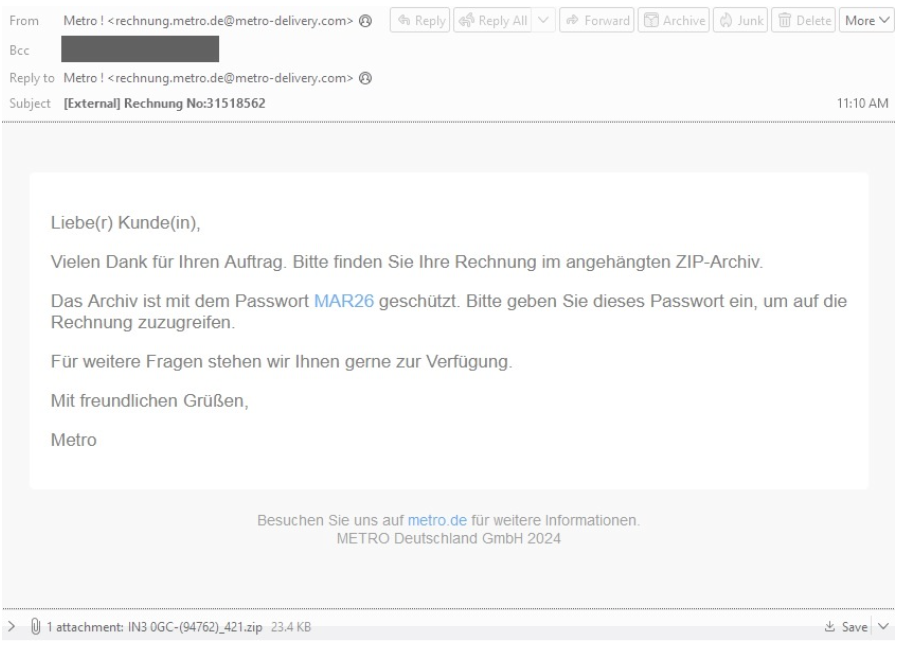
TA547 group is targeting dozens of German organizations with an information stealer called Rhadamanthys, Proofpoint warns.


SC Magazine
A PowerShell script used to deploy the infostealer contains unusually specific comments, researchers say.


CyberNews
Two-thirds of the official Paris Olympic Games partners do not have sufficient measures to protect the public from email fraud, cybersecurity experts have warned.

The Hacker News
TA547 hacker group adopts new tactics, possibly harnessing the power of generative AI, to deploy the Rhadamanthys info stealer in attacks on German or


CyberNews
Cybercriminals impersonating legitimate German companies are attacking organizations in the country.


DarkReading
It's finally happening: Rather than just for productivity and research, threat actors are using LLMs to write malware. But companies need not worry just yet.


Infosecurity News
Proofpoint said this is the first time the threat actor has been seen using LLM-generated PowerShell scripts


Bleeping Computer
A threat actor is using a PowerShell script that was likely created with the help of an artificial intelligence system such as OpenAI's ChatGPT, Google's Gemini, or Microsoft's CoPilot.


Infosecurity News
The malware, discovered by Proofpoint and Team Cymru, was mainly utilized by initial access brokers


The Hacker News
'Latrodectus' strikes via phishing emails. This powerful downloader can execute commands, evade detection, and pave the way for further attacks.

DarkReading
Initial access brokers are using the new downloader malware, which emerged just after QBot's 2023 disruption.


Bleeping Computer
A relatively new malware called Latrodectus is believed to be an evolution of the IcedID loader, seen in malicious email campaigns since November 2023.


HACKRead
Latrodectus is a downloader malware used by cybercriminals to gain initial access to victim systems and deploy further malicious payloads.

.webp)
Cyber Security News
Cybercriminals are increasingly exploiting YouTube, a platform beloved by millions, to orchestrate sophisticated malware attacks.


SC Magazine
Proofpoint researchers say new malware aligns with trend by cybercriminals to find more creative ways to bypass defenders.


Infosecurity News
Proofpoint has spotted a new infostealer campaign using malicious links in YouTube video descriptions


The Hacker News
Banking trojan Mispadu expands from Latin America, now targets users in Italy, Poland & Sweden. Finance, automotive, legal & commercial entities at ri


CyberNews
Information stealer malware is being delivered via YouTube in the guise of pirated software and video game cracks, cybersecurity firm Proofpoint warns.

The Record
Researches at Proofpoint have been tracking a campaign in which hackers put links in YouTube video descriptions that appear to take victims to other sites that deliver information-stealing malware such as Vidar, StealC and Lumma Stealer.


The DFIR Report
Key Takeaways We provide a range of services, one of which is our Threat Feed, specializing in monitoring Command and Control frameworks like Cobalt Strike, Metasploit, Sliver, Viper, Mythic, Havoc, … Read More


DarkReading
A majority of enterprises that employ cloud-based email spam filtering services are potentially at risk, thanks to a rampant tendency to misconfigure them.


DarkReading
Those with special committees that include a cyber expert rather than relying on the full board more likely to improve security and financial performance.

Krebs on Security
Thread hijacking attacks. They happen when someone you know has their email account compromised, and you are suddenly dropped into an existing conversation between the sender and someone else. These missives draw on the recipient's natural curiosity about being copied…


Cyber Security News
TA450, also recognized by aliases such as MuddyWater, Mango Sandstorm, and Static Kitten, has been reported to employ a new strategy in its phishing campaigns.

Security Affairs
In recent campaigns, Iran-linked APT group MuddyWater used a legitimate Remote Monitoring and Management (RMM) solution called Atera.


The Hacker News
Iran-linked hackers, MuddyWater, launch new phishing attacks against Israeli organizations.


Ars Technica
Discovery means that NerbianRAT is cross-platform used by for-profit threat group.


HACKRead
Magnet Goblin targets businesses using outdated software. Patch immediately and implement strong security measures to protect against attacks.


Cyber Security News
Linux servers are often targeted by threat actors due to their widespread use in critical infrastructure, web hosting, and cloud environments


The Hacker News
Magnet Goblin, a threat group known for fast exploitation of 1-day vulnerabilities, targets edge devices & public servers to deploy malware.

%20(1).webp)
Cyber Security News
Financially motivated threat who impersonates both US government institutions & private businesses across a wide range of industries.


Infosecurity News
Proofpoint said TA4903 adopted new tactics, including lure themes referencing confidential docs and ACH payments

Bleeping Computer
The hacking group known as TA577 has recently shifted tactics by using phishing emails to steal NT LAN Manager (NTLM) authentication hashes to perform account hijacks.


DarkReading
Yet challenges remain as many nation's policies for the email authentication protocol remain lax and could run afoul of Google's and Yahoo's restrictions.


Infosecurity News
Proofpoint warned the method could be used for data gathering and further malicious activities


Infosecurity News
Proofpoint found that 69% of organizations experienced a successful ransomware incident in the past year, with 60% hit on four or more occasions

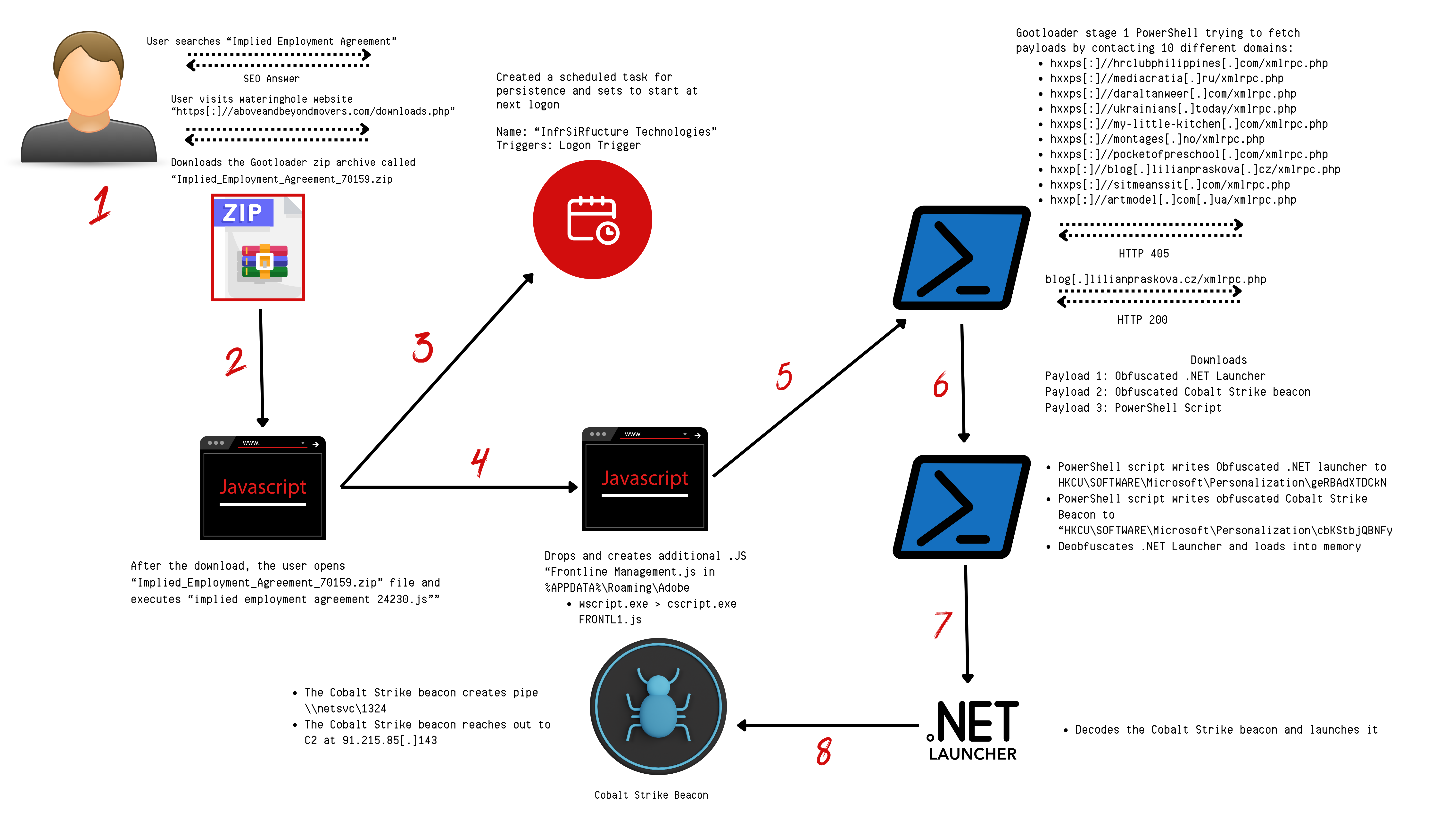
The DFIR Report
Key Takeaways More information about Gootloader can be found in the following reports: The DFIR Report, GootloaderSites, Mandiant, Red Canary, & Kroll. An audio version of this report can be … Read More


CyberSecurity Dive
Threat actors are targeting organizations’ inconsistent cloud security systems to intrude networks and maintain persistence.


DarkReading
Cyberattacks targeting thousands of US organizations wields a new attack vector to deliver the versatile initial-access loader — and is a harbinger of a surge in threat activity.

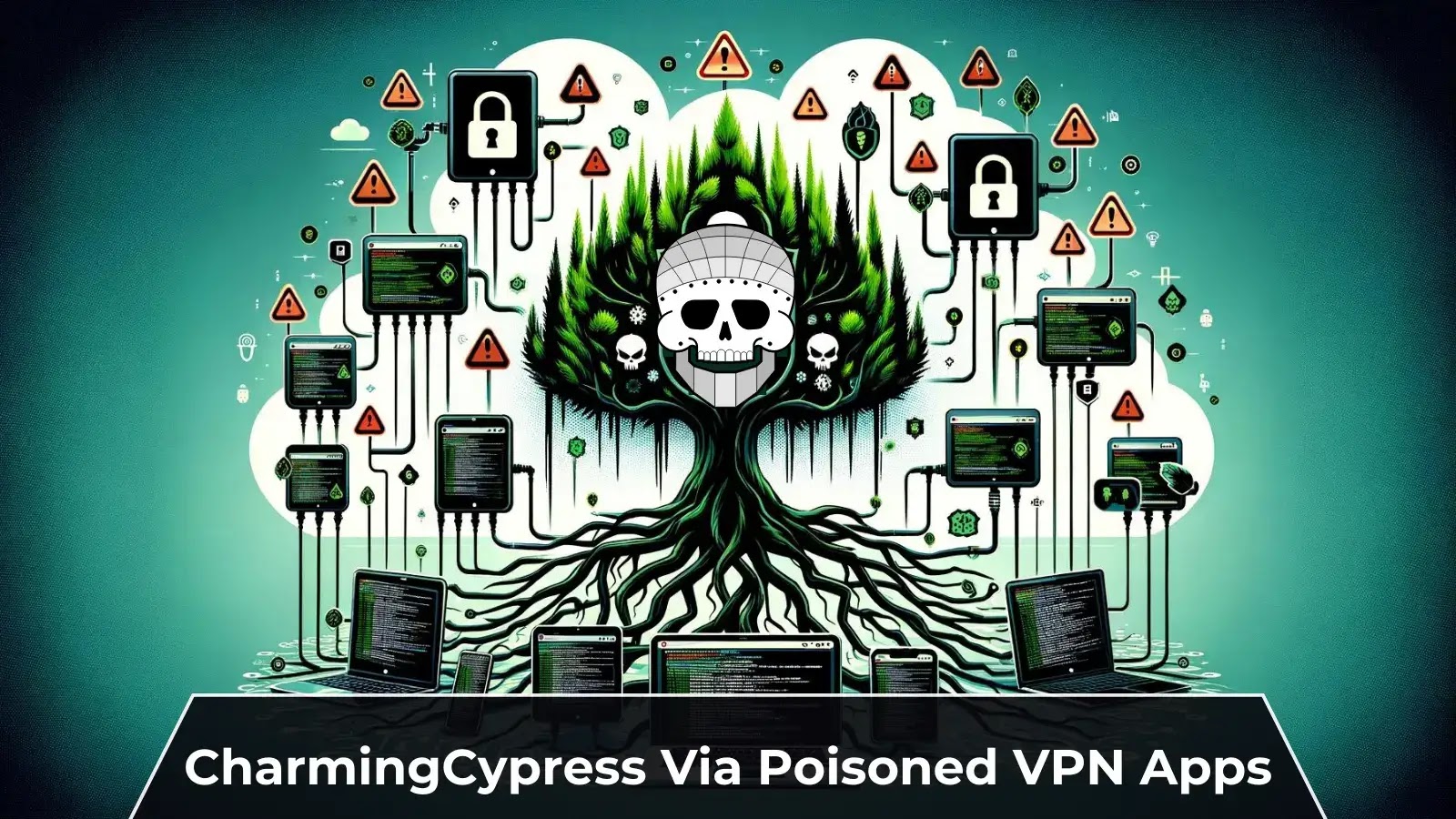
Cyber Security News
CharmingCypress frequently uses novel social-engineering techniques in its phishing efforts, like emailing people & long-lasting discussions


The Hacker News
Bumblebee, QakBot, Zloader, & PikaBot are back, sneakier than ever. Don't trust those shady emails or downloads.


PCMag
Threat actors are directing their attacks against senior-level executives and employees across multiple organizations, says cybersecurity firm Proofpoint.


Bleeping Computer
The Bumblebee malware has returned after a four-month vacation, targeting thousands of organizations in the United States in phishing campaigns.


The Hacker News
PikaBot malware undergoes a dramatic transformation, simplifying its code and communication methods


Infosecurity News
Proofpoint researchers observed a new Bumblebee social engineering campaign in February following a four-month absence


CyberNews
An unidentified cybercriminal gang codenamed Bumblebee has returned to the malware scene with a campaign that targeted thousands of potential victims.


CyberSecurity Dive
More than 200 organizations have been targeted via employee compromise, Proofpoint said.


SC Magazine
The ongoing campaign incorporates individualized phishing lures and has targeted hundreds of user accounts across dozens of organizations.


Ars Technica
The wide range of employee roles targeted indicates attacker's multifaceted approach.


Bleeping Computer
A phishing campaign detected in late November 2023 has compromised hundreds of user accounts in dozens of Microsoft Azure environments, including those of senior executives.

SecurityWeek
An active cloud account takeover campaign has impacted dozens of Azure environments and compromised hundreds of user accounts.


Infosecurity News
Proofpoint has observed an ongoing campaign targeting the Microsoft Azure applications of hundreds of individuals with operational and executive roles


DarkReading
Attackers are breaching cloud environments and playing games with corporate Microsoft 365 apps, and further victims are likely to come.


Security Affairs
26 key cyber security stats for 2024 that every user should know, from rising cyber crime rates to the impact of AI technology.


SC Magazine
Cybersecurity workers and infosec firms are well positioned to weather the layoff storm, experts say.

Cyber Security News
Best Security Service Edge (SSE) Solutions: 1. Perimeter 81 2. wingate 3. Cisco Umbrella 4. Forcepoint 5. Skyhigh Security 6. Netskope.


SecurityWeek
Prominent security vendors Okta and Proofpoint announced layoffs affecting almost 1,000 employees in the United States and Israel.


The Hacker News
Brazilian law enforcement has taken down a major cybercrime ring behind the notorious Grandoreiro banking trojan


The Hacker News
TA866 is back with thousands of invoice-themed, booby-trapped emails targeting users with WasabiSeed and Screenshotter malware.


DarkReading
Just like you and me, cyberattackers returned from winter break and immediately started sending thousands of emails.


Infosecurity News
Proofpoint said it thwarted a large-scale campaign on January 11 primarily targeting North America


CyberNews
After a nine-month sabbatical, a cyber espionage group has returned to the scene, targeting organizations across North America with infected PDF documents.


DarkReading
The post-exploitation backdoor is the latest in a string of custom tools aimed at spying on Apple users.


Cyber Security News
Weaponized Fake Browser Updates and Emails Spread DarkGate Malware also known as BattleRoyal, permits the execution of further malware.


The Hacker News
A new phishing campaign is using Microsoft Word docs as bait to deliver Nim-based malware.


DarkReading
The shadowy threat actor uses some nifty tricks to drop popular malware with targets that meet its specifications.


Infosecurity News
Proofpoint said the cluster’s use of multiple attack chains highlights a new trend among cybercriminals


The Cyber Express
In an era marked by relentless technological evolution and the omnipresence of cyber threats, the role of cybersecurity professionals has


The Hacker News
Attackers could achieve remote code execution on Outlook without any user interaction. Learn how these zero-click exploits were discovered and patched


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


The Hacker News
BazaCall phishing attacks are evolving. Threat actors now use Google Forms to appear more credible.


Cyber Security News
Recruiters Beware! Threat actors have been targeting recruiters disguised as job applicants to deliver their malware.


SC Magazine
Cybercriminals posing as job candidates are luring recruiters to install the “more_eggs” backdoor.


HACKRead
Job seekers and recruiters should be vigilant for malicious emails and messages on LinkedIn, where TA4557 threat actors feign interest in a job, but their actual intent is to deliver a backdoor.


The Hacker News
APT28, the Russian nation-state threat actor, is using lures related to the Israel-Hamas war to distribute the HeadLace backdoor.


Infosecurity News
Recruiters are warned to educate staff about surge in phishing attacks from threat group TA4557


CyberNews
Change of tactics involves building rapport with intended victims via convincing emails, says cybersecurity firm Proofpoint.


CSO
The new technique has the threat actor email malicious URLs directly to recruiters in response to job postings.


The Record
Entities in NATO member countries were among the targets spotted by researchers at Palo Alto Networks, in the third report in a week about Russian state-backed hackers exploiting a long-patched Microsoft bug.


The Cyber Wire
A Russian privacy law seems to have as its principal purpose controlling anything that might resemble independent journalism in advance of the upcoming presidential election theater.


CyberNews
Microsoft Outlook targeted more than 10,000 times this summer by a single threat actor believed to be aligned with Russia.


The Hacker News
New Malware Alert: WailingCrab, a sophisticated loader, is spreading via shipping-themed email messages.


DarkReading
Threat actors were actively exploiting CVE-2023-36025 in Windows SmartScreen as a zero-day vulnerability before Microsoft patched it in November.


DarkReading
Threat actors were actively exploiting CVE-2023-36025 before Microsoft patched it in November.
Loading more articles....