

SecurityWeek
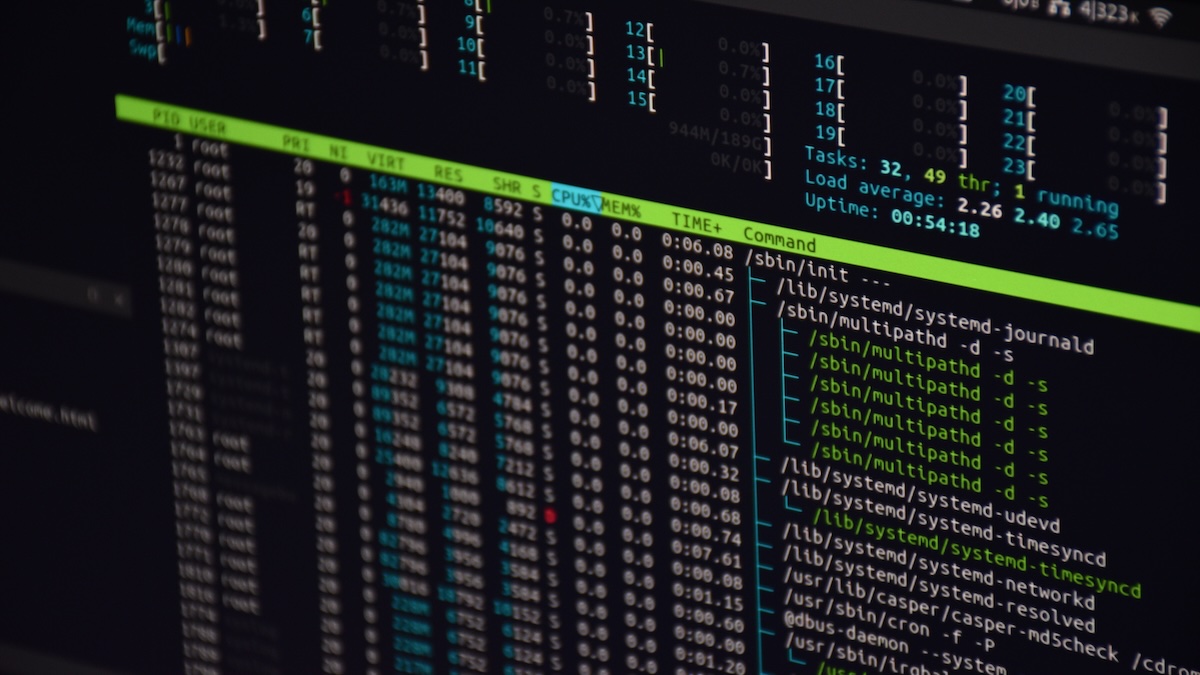
400,000 Linux Servers Hit by Ebury Botnet
The Ebury Linux botnet has ensnared over 400,000 Linux systems in 15 years, with roughly 100,000 still infected.


SecurityWeek
The Ebury Linux botnet has ensnared over 400,000 Linux systems in 15 years, with roughly 100,000 still infected.

Security Affairs
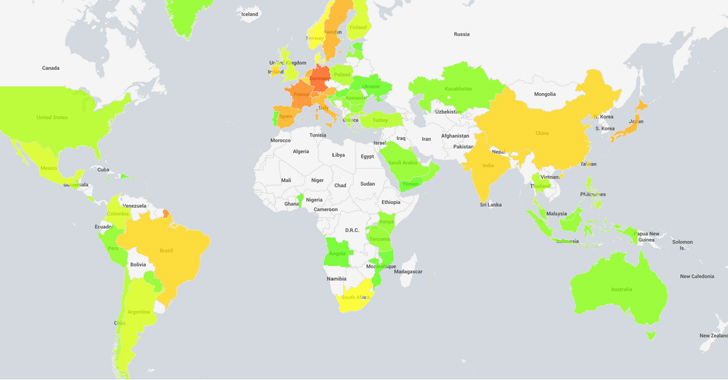
The Ubiquiti EdgeRouter botnet is still used by Russia-linked group APT28 and cybercriminals organizations.


SecurityWeek
A botnet dismantled in January and used by Russia-linked APT28 consisted of more than just Ubiquiti Edge OS routers.

Ars Technica
How and why nation-state hackers and cybercriminals coexist in the same router botnet.


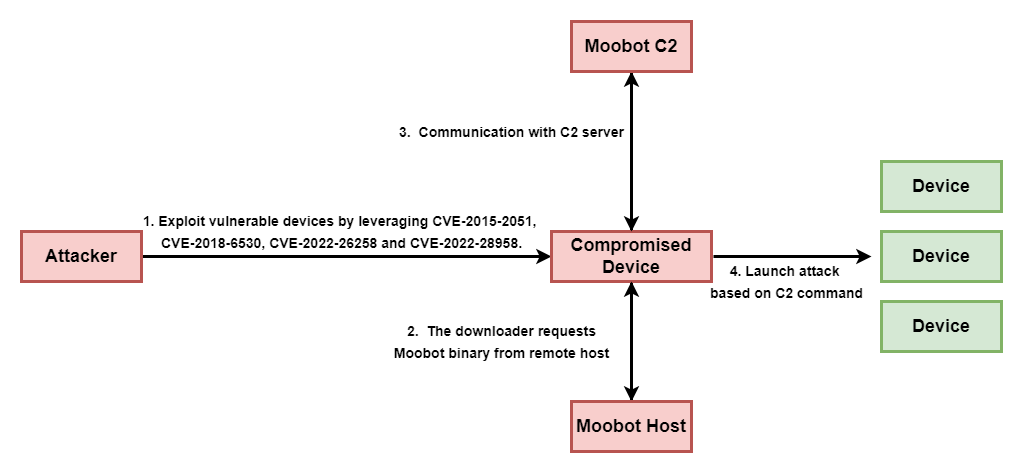
Trend Micro
This blog entry aims to highlight the dangers of internet-facing routers and elaborate on Pawn Storm's exploitation of EdgeRouters, complementing the FBI's advisory from February 27, 2024.


CyberNews
Multi-factor and 2-factor authentication, its safety and how hackers can overcome it


DarkReading
Unlike the SolarWinds and CodeCov incidents, all that it took for an adversary to nearly pull off a massive supply chain attack was some slick social engineering and a string of pressure emails.


Cyber Security News
The MITRE Corporation has disclosed that a sophisticated cyber attack recently compromised one of its internal r&d networks.


Bleeping Computer
The MITRE Corporation says a state-backed hacking group breached its systems in January 2024 by chaining two Ivanti VPN zero-days.

The Record
Analysts at Sophos X-Ops are comparing the low-budget cybercrime tools to “junk guns” — cheap, imported weapons that flooded the U.S. in the 1960s and 1970s.

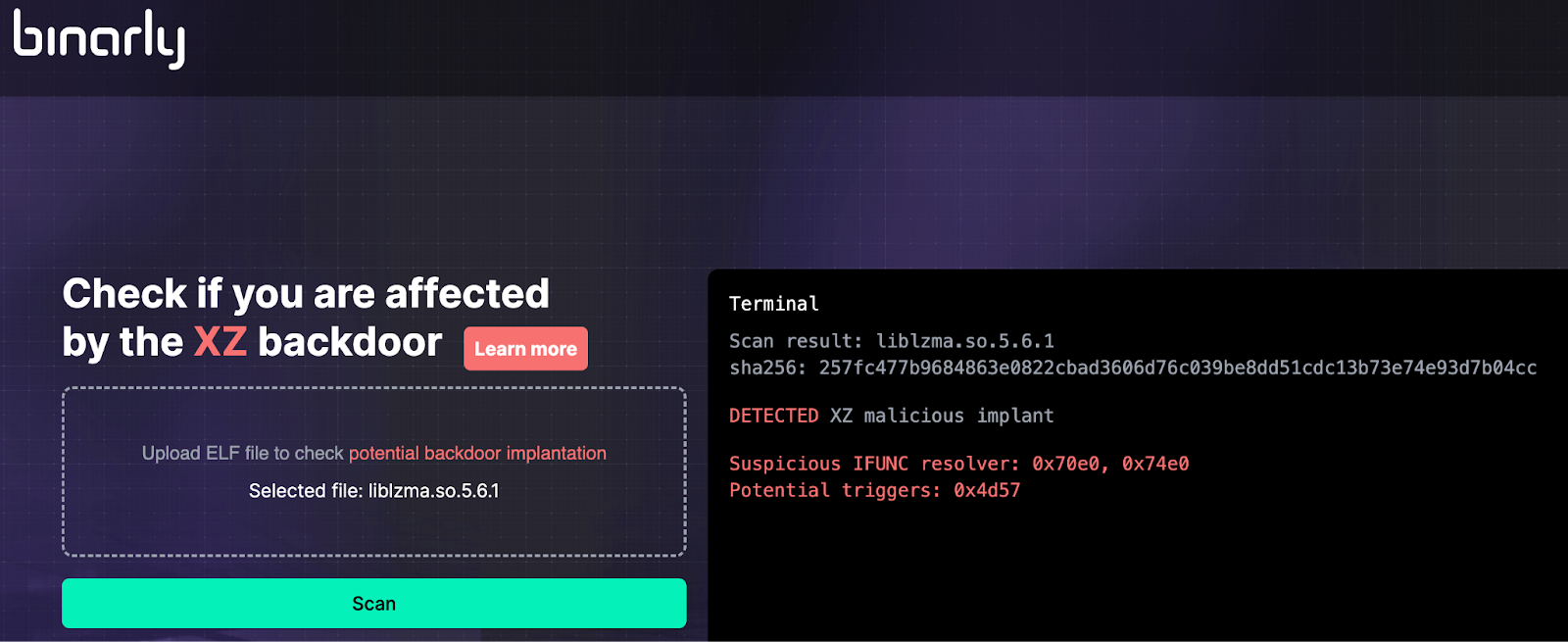
Security Affairs
Researchers from the firmware security firm Binarly released a free online scanner to detect the CVE-2024-3094 Backdoor


The Cyber Express
A critical vulnerability has been discovered within the XZ Utils library (a command line tool for compressing and decompressing XZ


DarkReading
Had a researcher not spotted the malware when he did, the outcome could have been much worse.

SecurityWeek
Major Linux distributions have been impacted by a supply chain attack involving backdoored versions of the XZ Utils data compression library.


Ars Technica
Malicious updates made to a ubiquitous tool were a few weeks away from going mainstream.


The Hacker News
Secret backdoor found in XZ Utils compression library used by major Linux distros, like Fedora, Kali Linux, and openSUSE.

Ars Technica
Malicious code planted in xz Utils has been circulating for more than a month.


DarkReading
Machine-learning platforms like Hugging Face are suspectible to the same kind of attacks that threat actors have executed successfully for years via npm, PyPI, and other open source repos.


HACKRead
A Chinese hacking group, Evasive Panda (aka BRONZE HIGHLAND and Daggerfly), has launched a cyberespionage campaign targeting Tibetans.


The Cyber Express
WordPress, a widely used content management system that powers millions of websites around the world, has become a source of


Ars Technica
Malicious submissions have been a fact of life for code repositories. AI is no different.


HACKRead
Discover the latest cybersecurity revelation: KONNI malware, linked to North Korea, targets the Russian Ministry of Foreign Affairs.


Cyber Security News
Konni RAT is a sophisticated malware tool cyber threat actors use to gain unauthorized access to systems, execute commands remotely.


The Hacker News
Russian government software compromised in suspected North Korean cyberattack. Konni RAT backdoor discovered in Ministry of Foreign Affairs tool.


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.

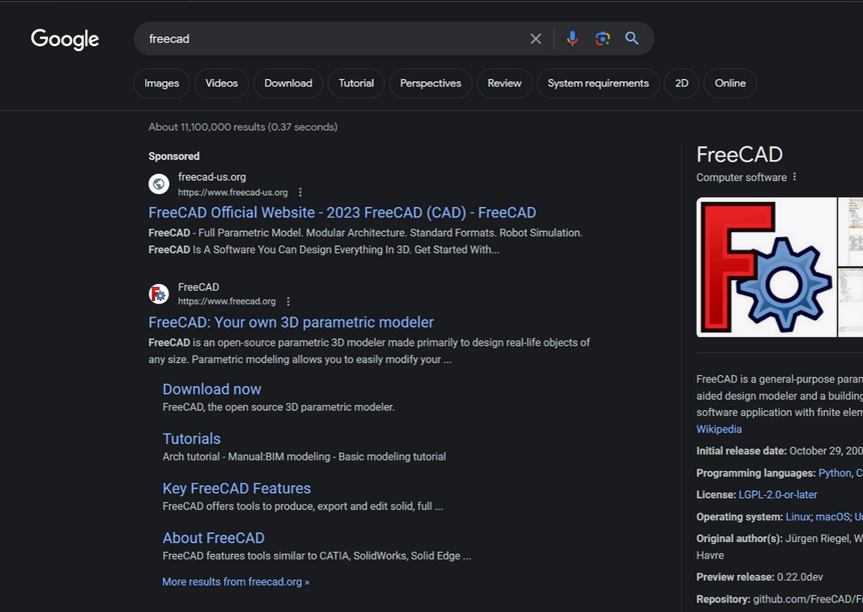
Krebs on Security
Google continues to struggle with cybercriminals running malicious ads on its search platform to trick people into downloading booby-trapped copies of popular free software applications. The malicious ads, which appear above organic search results and often precede links to legitimate…


Cyber Security News
According to the reports shared with Cyber Security News, there were more than 26000 unique internet-facing Ivanti VPN Connect Secure hosts.


Bleeping Computer
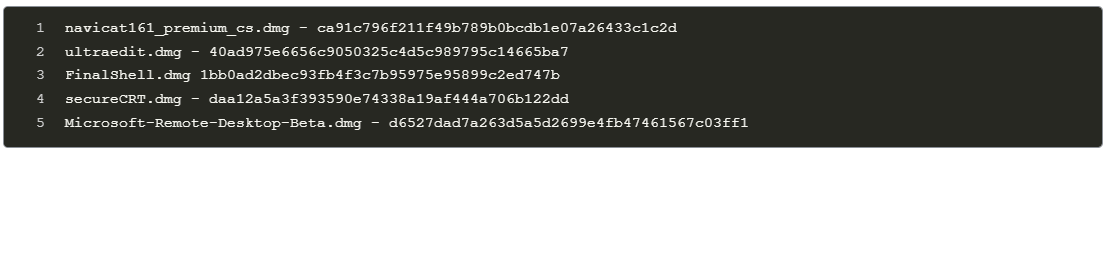
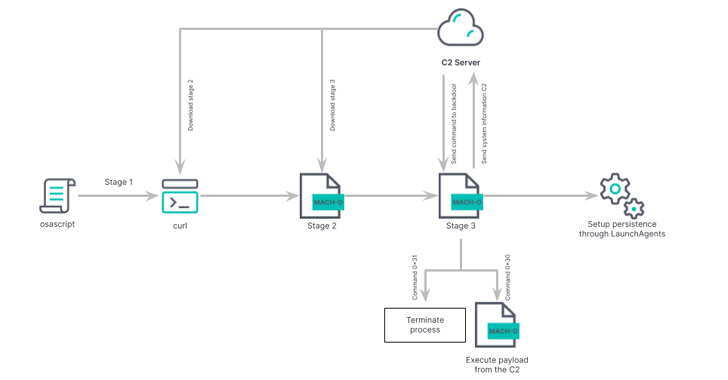
Hackers are using a stealthy method to deliver to macOS users information-stealing malware through DNS records that hide malicious scripts.


Bleeping Computer
Ivanti warned admins to stop pushing new device configurations to appliances after applying mitigations because this will leave them vulnerable to ongoing attacks exploiting two zero-day vulnerabilities.

Security Affairs
Researchers warned that pirated applications have been employed to deliver a backdoor to Apple macOS users.


Bleeping Computer
CISA issued this year's first emergency directive ordering Federal Civilian Executive Branch (FCEB) agencies to immediately mitigate two Ivanti Connect Secure and Ivanti Policy Secure zero-day flaws in response to widespread and active exploitation by multiple threat actors.


The Hacker News
Thinking of downloading a pirated copy of that software? Think again. A new backdoor malware has been discovered in pirated macOS apps.


Bleeping Computer
CISA warns that a critical authentication bypass vulnerability in Ivanti's Endpoint Manager Mobile (EPMM) and MobileIron Core device management software (patched in August 2023) is now under active exploitation.


DarkReading
Modified malware from the Khepri open source project that shares similarities with the ZuRu data stealer harvests data and drops additional payloads.


CyberNews
MacOS knock-offs are being put up on Chinese pirating sites to lure victims and compromise their devices, cybersecurity firm Jamf Threat Labs warns.


Bleeping Computer
Microsoft says that a group of Iranian-backed state hackers are targeting high-profile employees of research organizations and universities across Europe and the United States in spearphishing attacks pushing new backdoor malware.

Bleeping Computer
A previously unknown cybercrime syndicate named 'Bigpanzi' has been making significant money by infecting Android TV and eCos set-top boxes worldwide since at least 2015.


DarkReading
Anyone who hasn't mitigated two zero-day security bugs in Ivanti VPNs may already be compromised by a Chinese nation-state actor.


HACKRead
The vulnerabilities in Ivanti VPN devices enable remote, unauthenticated hackers to compromise targeted devices, execute arbitrary commands, infiltrate internal networks, and steal sensitive data.

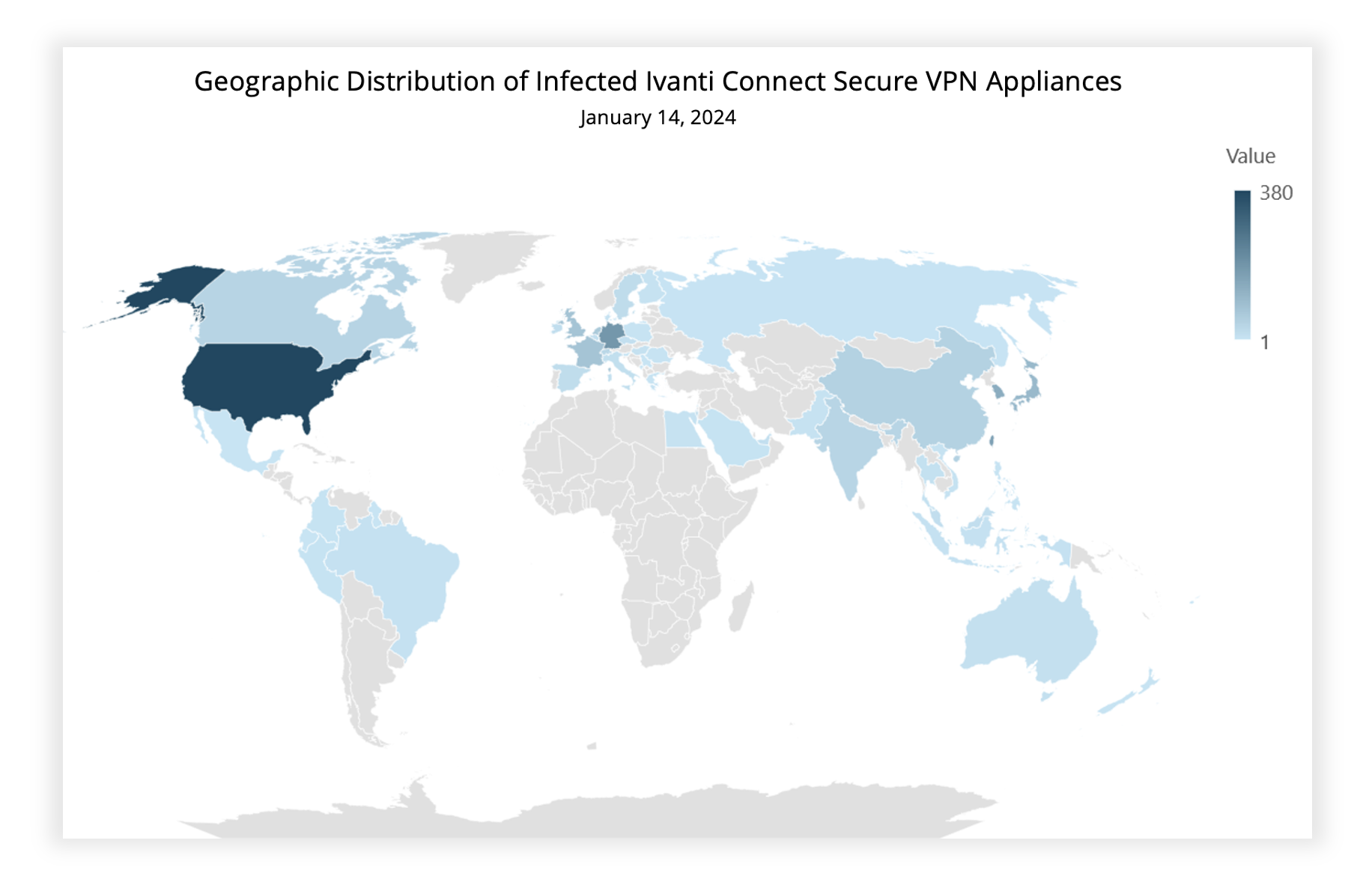
Security Affairs
Experts warn that recently disclosed Ivanti Connect Secure VPN and Policy Secure vulnerabilities are massively exploited in the wild.


Bleeping Computer
Two zero-day vulnerabilities affecting Ivanti's Connect Secure VPN and Policy Secure network access control (NAC) appliances are now under mass exploitation.


Ars Technica
Trained LLMs that seem normal can generate vulnerable code given different triggers.


The Hacker News
Ivanti Connect Secure hit by two zero-day flaws, exploited by suspected China-linked hackers to breach under 10 customers.


Ars Technica
"Triangulation" infected dozens of iPhones belonging to employees of Moscow-based Kaspersky.


CSO
Threat actors are combining RustBucket loader with KandyKorn payload to effect an evasive and persistent RAT attack.


The Hacker News
Lazarus Group's evolving cyber tactics target macOS systems by combining elements from multiple malware campaigns for better effectiveness and to avoi


CyberNews
Security researchers are blaming a now-patched Citrix zero-day vulnerability for a recent spate of ransomware attacks said to be carried out by the LockBit gang.


Bleeping Computer
The North Korean-backed BlueNorOff threat group targets Apple customers with new macOS malware tracked as ObjCShellz that can open remote shells on compromised devices.


SecurityWeek
VMware’s Threat Analysis Unit finds 34 new vulnerable kernel drivers that can be exploited to alter or erase firmware and escalate privileges.


The Hacker News
State-sponsored North Korean hackers are using a sneaky macOS malware called KANDYKORN to target crypto engineers via Discord.


SecurityWeek
Google improves Android devices’ proactive protections against malware with real-time scanning at code level.

SecurityWeek
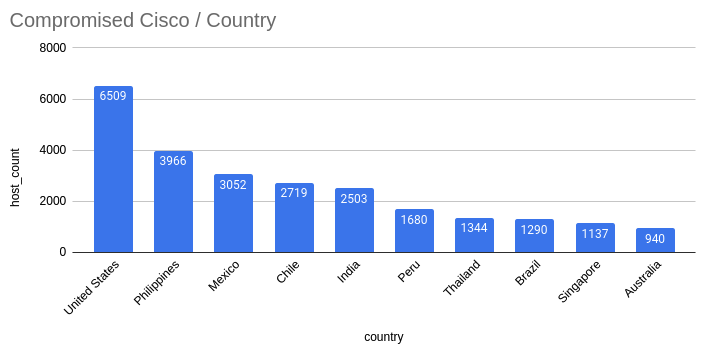
The number of Cisco devices hacked via the CVE-2023-20198 zero-day has reached 40,000, including many in the US.


The Hacker News
Korean hacking group Lazarus Group targets defense industry and nuclear engineers with fake job interviews, using trojanized VNC apps to steal data an


SecurityWeek
A threat actor targets Israelis with spyware masquerading as an Android application for receiving rocket alerts.


Latest Hacking News
Numerous researchers have found a large number of Android TV Boxes, already accessible to the public, backdoored to conduct adware fraud. Researchers warn the users to get rid of those specific models and buy reputed


The Hacker News
PEACHPIT alert! This ad fraud botnet, linked to China's BADBOX operation, targeted 15M+ Android & iOS users. Learn how threat actors exploited devices


Bleeping Computer
A bounty of $12,288 has been announced for the first person to crack the NIST elliptic curves seeds and discover the original phrases that were hashed to generate them.


SecurityWeek
Tens of thousands of Android devices have been shipped to end-users with backdoored firmware, Human Security warns.


Infosecurity News
The BADBOX scheme deploys the Triada malware on various devices like smartphones and tablets


Ars Technica
The modified firmware used by BlackTech is hard to detect.


Infosecurity News
This extensive operation is directed at Tibetan, Uyghur and Taiwanese individuals and organizations

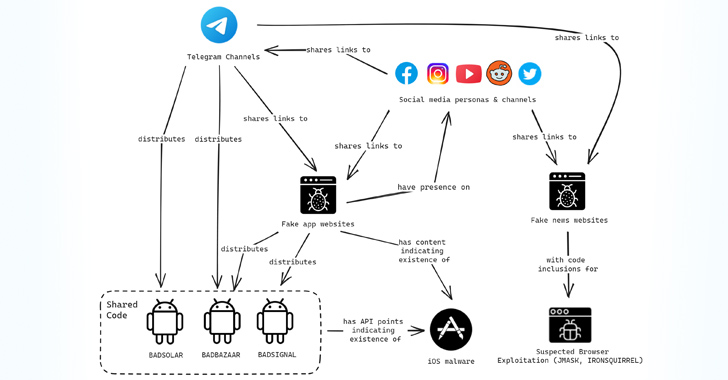
The Hacker News
EvilBamboo tactics exposed: Targets sensitive data from Tibetan, Uyghur, and Taiwanese organizations.


SecurityWeek
Noteworthy stories that might have slipped under the radar: China blames NSA for a cyberattack, AI jailbreaks, and Netography spin-off.

Ars Technica
It's not too late to check if a Linux device you use was targeted.


DarkReading
Citrix issued a patch for the critical remote code execution bug in July for its NetScaler devices.


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press. Over 3,000 Android Malware spotted using unsupported/unknown compression methods to avoid detection WinRAR flaw enables remote […]


SecurityWeek
Exploitation of a Citrix ShareFile vulnerability tracked as CVE-2023-24489 has spiked as CISA added it to its ‘must patch’ catalog.

Infosecurity News
The attack was unveiled by cybersecurity firm Fox-IT in collaboration with the DIVD


Cyber Security News
Recently, discovered that an attacker installed web shells on susceptible Citrix NetScalers using (CVE-2023-3519) to acquire access.


Security Affairs
A threat actor has compromised roughly 2,000 Citrix NetScaler servers exploiting a remote code execution tracked as CVE-2023-3519. In July Citrix warned customers of a critical vulnerability, tracked as CVE-2023-3519 (CVSS score: 9.8), in NetScaler Application Delivery Controller (ADC) and Gateway that is being actively exploited in the wild The vulnerability CVE-2023-3519 (CVSS score: 9.8) is a code injection that […]

The Hacker News
1,900+ Citrix NetScaler instances breached in a massive attack exploiting critical vulnerability. Hackers used automated methods to install web shells


The Record
Alarms have been raised about several vulnerabilities affecting products from Citrix that are being exploited widely by a variety of threat actors.

The Record
After analyzing millions of computers infected with info-stealing malware, researchers at Hudson Rock said they identified 120,000 that contained credentials used for logging into cybercrime forums.


Bleeping Computer
A threat actor has compromised close to 2,000 thousand Citrix NetScaler servers in a massive campaign exploiting the critical-severity remote code execution tracked as CVE-2023-3519.


SecurityWeek
A threat actor has exploited a recent Citrix vulnerability (CVE-2023-3519) to infect roughly 2,000 NetScaler instances with a backdoor.


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press. Reptile Rootkit employed in attacks against Linux systems in South Korea New PaperCut flaw in […]


Cyber Security News
The Threat and Vulnerability Roundup for this week is out! With great pride, Cyber Writes presents a weekly overview of the most recent cybersecurity news.


Bleeping Computer
Hundreds of Citrix Netscaler ADC and Gateway servers have already been breached and backdoored in a series of attacks targeting a critical remote code execution (RCE) vulnerability tracked as CVE-2023-3519.


Bleeping Computer
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has given federal agencies three weeks to secure Adobe ColdFusion servers on their networks against two critical security flaws exploited in attacks, one of them as a zero-day.


Bleeping Computer
This edition of the Week in Ransomware covers the last two weeks of news, as we could not cover it last week, and includes quite a bit of new information, including the return of the Avaddon ransomware gang.


Bleeping Computer
A financially motivated cybercrime gang has been observed deploying BlackCat ransomware payloads on networks backdoored using a revamped Sardonic malware version.

The Hacker News
A sophisticated threat actor is targeting Pakistan government entities through a trojanized version of the E-Office application.


Infosecurity News
Trend Micro found a backdoor previously exploited by various Chinese threat actors in a popular application used by Pakistan’s government agencies


Trend Micro
We recently found that an MSI installer built by the National Information Technology Board (NITB), a Pakistani government entity, delivered a Shadowpad sample, suggesting a possible supply-chain attack.

The Hacker News
North Korea's BlueNoroff, part of Lazarus Group, has upgraded their macOS malware, Rustbucket, to avoid detection and persist longer.


Ars Technica
It's not yet clear how the full-featured JokerSpy backdoor gets installed.


Security Affairs
An unnamed Japanese cryptocurrency exchange was the victim of a cyber attack aimed at deploying an Apple macOS backdoor named JokerSpy. Elastic Security Labs researchers provided details about a recently discovered intrusion at an unnamed cryptocurrency exchange, aimed at deploying an Apple macOS backdoor named JokerSpy. The researchers tracked the intrusion as REF9134, the threat […]


Security Affairs
China-linked APT group VANGUARD PANDA, aka Volt Typhoon, was spotted observing a novel tradecraft to gain initial access to target networks. CrowdStrike researchers observed the China-linked APT group VANGUARD PANDA, aka Volt Typhoon, using a novel tradecraft to gain initial access to target networks. The Volt Typhoon group has been active since at least mid-2021 […]


The Hacker News
A Japanese cryptocurrency exchange fell victim to a recent cyberattack, deploying the stealthy JokerSpy backdoor on Apple macOS.


The Hacker News
New cyber espionage threat! Chinese group Volt Typhoon, aka Bronze Silhouette, employs advanced techniques to infiltrate and maintain access.

Bleeping Computer
A suspected pro-China hacker group tracked by Mandiant as UNC4841 has been linked to data-theft attacks on Barracuda ESG (Email Security Gateway) appliances using a now-patched zero-day vulnerability.


The Hacker News
Chinese state-sponsored group UNC3886 exploits a zero-day VMware authentication bypass flaw (CVE-2023-20867) to backdoor Windows, Linux, and PhotonOS.


Security Affairs
A China-linked APT group tracked as UNC3886 has been spotted exploiting a VMware ESXi zero-day vulnerability. Mandiant researchers observed a China-linked cyberespionage group, tracked as UNC3886, exploiting a VMware ESXi zero-day vulnerability tracked as CVE-2023-20867. “VMware Tools contains an Authentication Bypass vulnerability in the vgauth module.” reads the advisory published by VMware. “A fully compromised […]


Bleeping Computer
VMware patched today a VMware ESXi zero-day vulnerability exploited by a Chinese-sponsored hacking group to backdoor Windows and Linux virtual machines and steal data.

Bleeping Computer
Email and network security company Barracuda warns customers they must replace Email Security Gateway (ESG) appliances hacked in attacks targeting a now-patched zero-day vulnerability.


Bleeping Computer
Network and email security firm Barracuda today revealed that a recently patched zero-day vulnerability had been exploited for at least seven months to backdoor customers' Email Security Gateway (ESG) appliances with custom malware and steal data.


The Hacker News
An Iranian threat actor targeted a government entity in the UAE, leveraging PowerExchange backdoor to breach their Microsoft Exchange Servers.


Bleeping Computer
A new PowerShell-based malware dubbed PowerExchange was used in attacks linked to APT34 Iranian state hackers to backdoor on-premise Microsoft Exchange servers.


DarkReading
As threat actors around the world grow and evolve, APTs from the DPRK stand out for their spread and variety of targets.


The Hacker News
Pakistan-based APT36 hackers are reportedly using a new Linux backdoor called Poseidon to target Indian government agencies.
Loading more articles....