

CSO
US AI experts targeted in cyberespionage campaign using SugarGh0st RAT
Threat actors use phishing techniques to obtain non-public information about generative artificial intelligence.


CSO
Threat actors use phishing techniques to obtain non-public information about generative artificial intelligence.


HACKRead
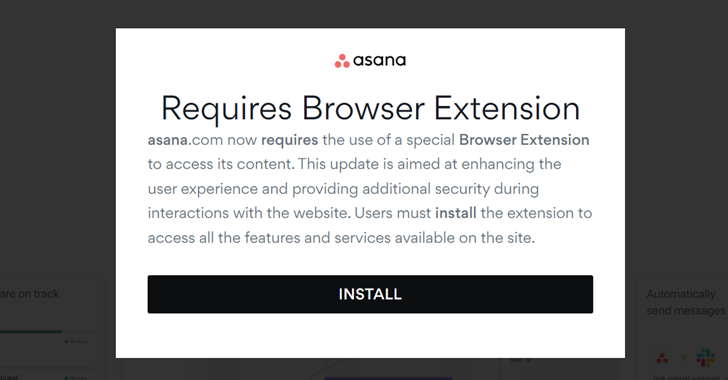
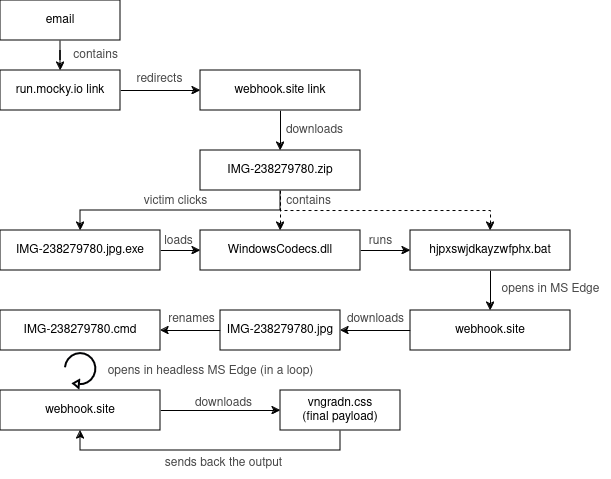
New HP report reveals cybercriminals are increasingly leveraging "cat-phishing" techniques, exploiting open redirects in legitimate websites to deceive users and deliver malware.


DarkReading
Researchers believe the attacker is likely China-affiliated, since a previous version of the malware was used by a China nation-state attack group.


Infosecurity News
Proofpoint said the attackers modified registry key names for persistence


Security Magazine
59% of organizations experienced a software supply chain attack, with 54% of these respondents having experienced one in the past year.


Bleeping Computer
Security researchers discovered two previously unseen backdoors dubbed LunarWeb and LunarMail that were used to compromise a European government's diplomatic institutions abroad.


Infosecurity News
Car manufacturer Nissan revealed that over 53,000 of its North America employees had their social security numbers accessed by a ransomware attacker


The Hacker News
Kimsuky hackers launch new social engineering attack using fake Facebook accounts. Learn how they target activists via Messenger and deliver malware.


Cyber Security News
Best MSP for CISO, CTO & IT Managers - 1. Perimeter 812. Secureworks 3. IBM 4. Trustwave 5. Wipro 6. Verizon 7. Sophos 8. Symantec.


DarkReading
When abused by threat actors with sophisticated social-engineering chops, remote-access tools demand that enterprises remain sharp in both defense strategy and employee-awareness training.


Bleeping Computer
The North Korean hacker group Kimsuki has been using a new Linux malware called Gomir that is a version of the GoBear backdoor delivered via trojanized software installers.


Bleeping Computer
The North Korean hacker group Kimsuki has been using trojanized software packages to deliver a new Linux malware called Gomir in cyberespionage campaigns against targets in South Korea.


HACKRead
The Internet of Things (IoT) promises a world of interconnected devices, but with this connectivity comes a dark side such as security vulnerabilities.


SecurityWeek
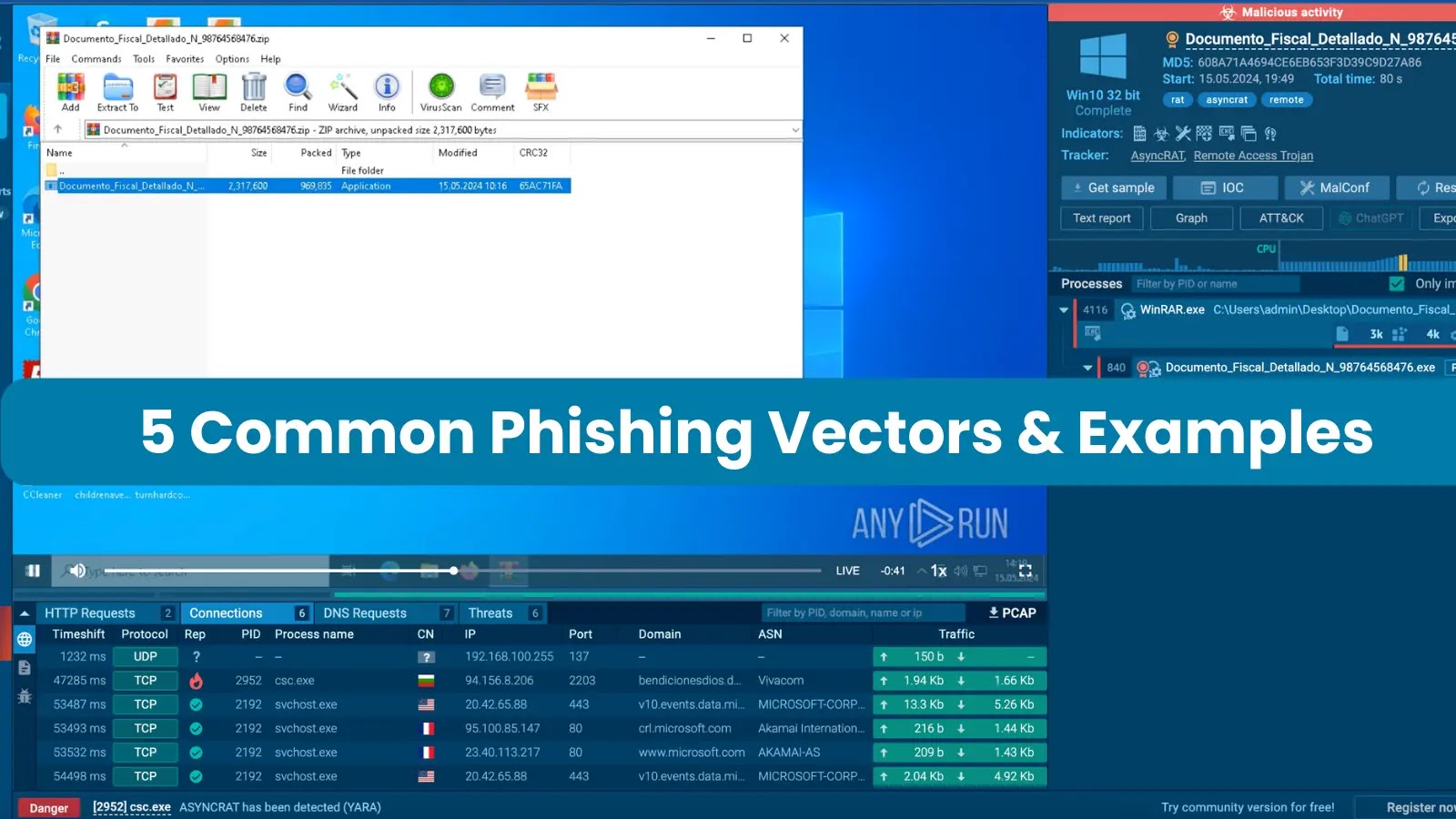
Google is boosting fraud and malware protections in Android 15 with live threat detection and expanded restricted settings.


Cyber Security News
Remote assist tools are often targeted by hackers as they create a direct channel that can be used to get into desired systems while using

%20(1).webp)
Cyber Security News
Earth Hundun, a notable Asia-Pacific malware organization, uses Waterbear and Deuterbear, first encountered Deuterbear.


Cyber Security News
In a major move to bolster its cloud security offerings, Palo Alto Networks announced today that it has agreed to purchase the QRadar .


The Cyber Express
In response to heightened cyber threats targeting political candidates, election officials and civil society groups, the National Cyber Security Centre


The Hacker News
Beware of Storm-1811! This financially motivated group is abusing Microsoft's Quick Assist tool in social engineering attacks.


SC Magazine
Threat actors use the remote management tool and social engineering to access victims’ systems and install malware.


Trend Micro
This report describes how Waterbear and Deuterbear — two of the tools in Earth Hundun's arsenal — operate, based on a campaign from 2024.


The Record
The Share and Defend system will provide a list of malicious domains to a range of U.K. communications providers so the domains can be added to blocklists.


Ars Technica
An earlier iteration of the site was taken down last year; now its reincarnation is gone.


Bleeping Computer
Google is introducing multiple anti-theft and data protection features later this year, some available only for Android 15+ devices, while others will roll out to billions of devices running Android 10 and later.

Bleeping Computer
Today, Google announced new security features coming to Android 15 and Google Play that will help block scams, fraud, and malware apps on users' devices.

Bleeping Computer
Today, Google announced new security features coming to Android 15 and Google Play Protect that will help block scams, fraud, and malware apps on users' devices.

Cyber Security News
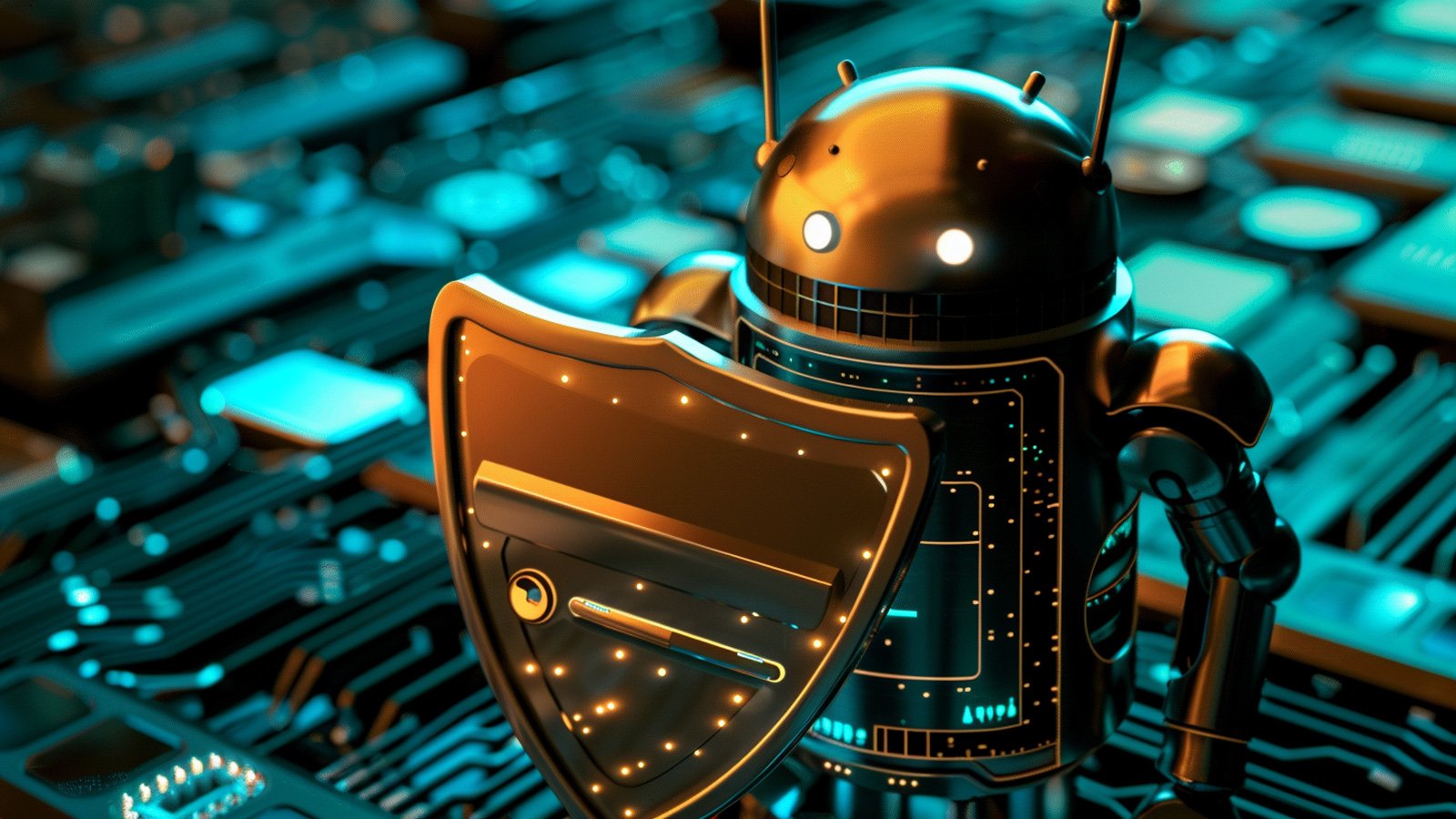
Phishing attacks can be executed through various means, such as SMS and phone calls, but the most prevalent method involves sending victims emails containing malicious attachments.

The Hacker News
Android 15 introduces new features to prevent malicious apps from capturing your sensitive data. Find out more about these crucial updates:

Ars Technica
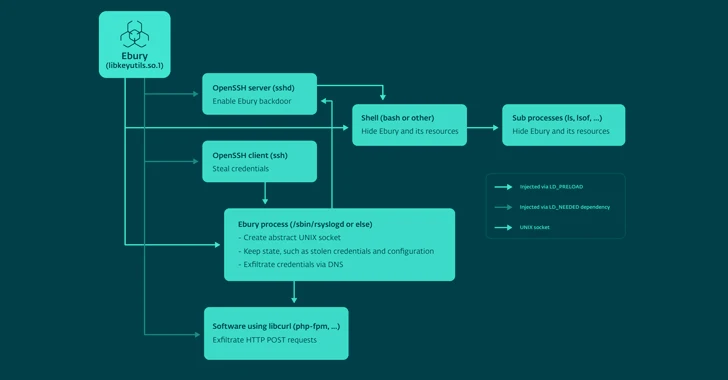
Ebury backdoors SSH servers in hosting providers, giving the malware extraordinary reach.


Infosecurity News
CPR said exploit builders in .NET and Python have been employed to deploy this malware


Infosecurity News
The National Cyber Security Centre launches an opt-in Personal Internet Protection service to safeguard individuals from cyber threats during the upcoming election


SecurityWeek
Russian-speaking threat actors are caught abusing a GitHub profile to distribute information stealers posing as legitimate software.


Bleeping Computer
Organizations need to detect and remove intruders quickly to prevent data loss and minimize the impact of lateral movement attacks. Learn more from Specops Software on blocking lateral movement in networks.

.webp)
Cyber Security News
The well-known advanced persistent threat (APT) group Turla, which is based in Russia, is said to be going after the European Ministry.


Security Magazine
According to a cybersecurity and threat intelligence report, the U.S. was the 4th most targeted country in the world regarding phishing attacks.


SecurityWeek
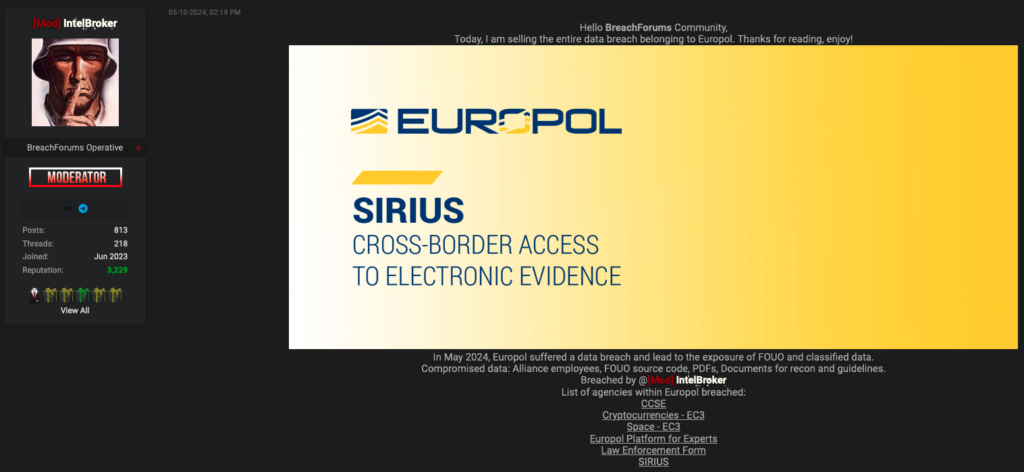
The Ebury Linux botnet has ensnared over 400,000 Linux systems in 15 years, with roughly 100,000 still infected.

.webp)
Cyber Security News
Cybercriminals have been exploiting GitHub, a platform widely trusted by developers, to host malicious infrastructure.

The Hacker News
Ebury malware botnet has compromised an estimated 400,000 servers since 2009. Learn how to protect your systems from this advanced threat.


The Cyber Express
Microsoft patched a zero-day vulnerability exploited by attackers to distribute QakBot and other malware payloads on susceptible Windows systems. Identified


Infosecurity News
Microsoft has released patches for three zero-day vulnerabilities including two actively exploited in the wild


Cyber Security News
Best Network Security Providers for the Healthcare Industry - 1. Perimeter 81, 2. Palo Alto Networks, 3. Fortinet, 4. Cisco, 5. Trend Micro


The Cyber Express
Cyble Research and Intelligence Labs (CRIL) researchers have uncovered a new SideCopy campaign. The threat actor group has previously been

%20(1).webp)
Cyber Security News
Cybersecurity experts have identified a new malware, dubbed WaveStealer, being actively distributed through popular messaging platforms.


The Hacker News
Microsoft has patched 61 new security flaws, including two zero-days actively exploited in the wild.


CSO
CISA advisory includes indicators of compromise and TTPs that can be used for threat hunting.


The Record
Researchers with cybersecurity company ESET have labeled two new pieces of suspected Russian malware as LunarWeb and LunarMail.


SC Magazine
In this month’s release, Redmond patched 60 CVEs including two other zero-days and a SharePoint Server remote code execution vulnerability rated critical.


Bleeping Computer
Today, Microsoft fixed a known issue breaking VPN connections across client and server platforms after installing the April 2024 Windows security updates.


Cyber Security News
Microsoft fixed 60 vulnerabilities in its Patch Tuesday release in May 2024, including 2 zero-day vulnerabilities actively exploited in the wild


Bleeping Computer
Microsoft has fixed a known issue causing NTLM authentication failures and domain controller reboots after installing last month's Windows Server security updates.

SecurityWeek
Microsoft patched 60 security bugs in multiple products and waned of an actively exploited Windows zero-day (CVE-2024-30051)

Bleeping Computer
Microsoft has fixed a zero-day vulnerability exploited in attacks to deliver QakBot and other malware payloads on vulnerable Windows systems.


Bleeping Computer
Today is Microsoft's May 2024 Patch Tuesday, which includes security updates for 61 flaws and three actively exploited or publicly disclosed zero days.


Infosecurity News
The 15-year-old Ebury botnet is more active than ever, as ESET found 400,000 Linux servers compromised for cryptocurrency theft and financial gain


DarkReading
Exploit code is circulating for CVE-2024-4761, disclosed less than a week after a similar security vulnerability was disclosed as being used in the wild.

Bleeping Computer
A malware botnet known as 'Ebury' has infected almost 400,000 Linux servers since 2009, with roughly 100,000 still compromised as of late 2023.


HACKRead
A new Android malware poses as popular applications like WhatsApp, Instagram, and Snapchat to steal user data, including login credentials.


Infosecurity News
Recorded Future details a novel campaign that abuses legitimate internet services to deploy multiple malware variants for credential theft

HACKRead
DNS tunneling is being used to bypass security filters by hiding malicious traffic in DNS packets, allowing hackers to steal stolen data.


DarkReading
Several campaigns are leveraging the evasive tactic to provide useful insights into victims' online activities, and find new ways to compromise organizations.


SecurityWeek
Ron Reiter was a childhood hacker in Israel and recruited into the IDF’s Unit 8200. Now he is CTO and co-founder of cybersecurity firm Sentra.

.webp)
Cyber Security News
The botnet, operated by the threat group behind the Ebury malware, has been active since at least 2009 but has evolved over the past decade.


HACKRead
The Israel-Hamas conflict has fueled a wave of hacktivism activity, with groups like SiegedSec launching attacks and leaking sensitive information.


SecurityWeek
Threat actors are using DNS tunneling to track victims’ interaction with spam and to scan network infrastructures.

The Hacker News
12 security flaws addressed, including two critical issues leading to remote code execution. Update to version 1.2.27 now to stay protected


The Hacker News
A new social engineering campaign is targeting enterprises with spam emails to gain initial access. The threat actor overwhelms users' email and calls


Infosecurity News
Palo Alto Networks warns threat actors are using DNS tunneling techniques to probe for network vulnerabilities


Cyber Security News
Recent email campaigns distribute DanaBot malware through two document types: those using equation editor exploits and those containing


Latest Hacking News
Torrance, California, May 13th, 2024, CyberNewsWireCriminal IP, a renowned Cyber Threat Intelligence (CTI) search engine developed by AI SPERA, has recently signed a technology partnership to exchange threat intelligence data based on domains and potentially


SecurityWeek
Zscaler has completed its investigation into the recent hacking claims and found that only an isolated test environment was compromised.

Security Affairs
Experts reported that since April, the Phorpiex botnet sent millions of phishing emails to spread LockBit Black ransomware


CSO
The odds of attacks are growing as attackers can now easily access code modification and reverse engineering tools.


SC Magazine
Emails from “Jenny Green” delivered LockBit Black through attached ZIP files.


Krebs on Security
Microsoft today released updates to fix more than 60 security holes in Windows computers and supported software, including two "zero-day" vulnerabilities in Windows that are already being exploited in active attacks. There are also important security patches available for macOS…


Bleeping Computer
A new package mimicked the popular 'requests' library on the Python Package Index (PyPI) to target macOS devices with the Sliver C2 adversary framework, used for gaining initial access to corporate networks.


Ars Technica
Threat group has targeted 500 organizations. One is currently struggling to cope.


Infosecurity News
Analyzing Mallox samples, Sekoia identified two distinct affiliates using different approaches

%20(1).webp)
Cyber Security News
"Our partnership with Quad9 is a recognition of the accuracy of Criminal IP's data," stated Byungtak Kang, CEO of AI SPERA.

SecurityWeek
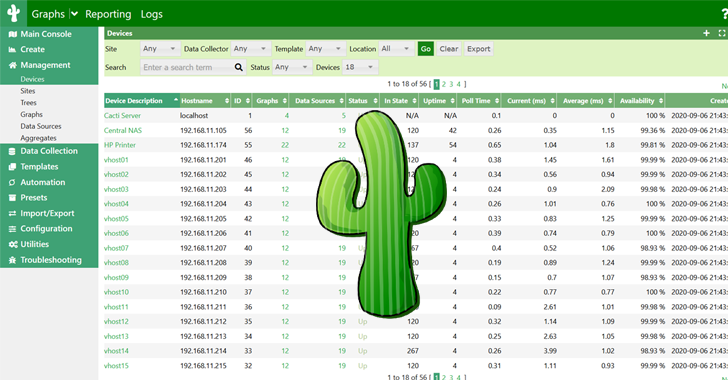
Europol is investigating a data breach, but says no core systems are impacted and no operational data has been compromised.


Bleeping Computer
The Criminal IP Threat Intelligence (CTI) search engine to integrate with Quad9's threat-blocking service. Learn more from Criminal IP about how this integration can help you.


HACKRead
Torrance, California, May 13th, 2024, CyberNewsWire

.webp)
Cyber Security News
Romance scam schemes involve intricate manipulations, including using fake cryptocurrency exchanges to defraud victims.


The Hacker News
Are your browser extensions safe? 33% in most orgs aren't! Learn to protect your data with insights from the 2024 Browser Security Report.


SecurityWeek
The US government warns of Black Basta ransomware attacks targeting critical infrastructure organizations.


The Cyber Express
A dark web hacker, known as "makishimaaaa," has recently advertised a significant data breach on the Nuovo BreachForums. The compromised


Cyber Security News
Black Basta ransomware is used by threat actors because of its powerful abilities and inconspicuous moves.


The Hacker News
Researchers found a malicious Python package called requests-darwin-lite hiding a sneaky malware.


CyberSecurity Dive
Don’t fall for scare headlines about GenAI code—it offers multiple benefits—but also be aware of its limits and risks.


Krebs on Security
Last week, the United States joined the U.K. and Australia in sanctioning and charging a Russian man named Dmitry Yuryevich Khoroshev as the leader of the infamous LockBit ransomware group. LockBit's leader "LockBitSupp" claims the feds named the wrong guy,…


The Record
An infiltrator posted a breaking news story titled "PERVOKLASSNIY RUSSIAN HACKERS ATTACK" on websites owned by Newsquest Media Group.


SC Magazine
The “requests-darwin-lite” package was downloaded more than 400 times before its removal.


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.

.png)
Cyber Security News
Staying informed is the key in this dynamic battle of cybersecurity, and due to this, the weekly news recap provides you with the newest trends, weaknesses, infringements found, and some possible defense mechanisms.


Security Affairs
Black Basta ransomware affiliates have breached over 500 organizations between April 2022 and May 2024, FBI and CISA reported.

The Hacker News
The notorious FIN7 hacking group is at it again! This time, they're using malicious Google ads to trick users into downloading malware disguised as le


Bleeping Computer
After many months of taunting law enforcement and offering a million-dollar reward to anyone who could reveal his identity, the FBI and NCA have done just that, revealing the name of LockBitSupp, the operator of the LockBit ransomware operation.


The Hacker News
North Korean hackers have unleashed a new Golang malware called "Durian" in targeted attacks against South Korean crypto firms.


Infosecurity News
Well-funded cybercriminals are adopting more sophisticated techniques, creating a need for defenders to stay informed about the evolving threat landscape


CyberNews
The UK’s Information Commissioner's Office (ICO) calls organizations to boost “cybersecurity and protect the personal information they hold.”

Security Affairs
CERT Polska warns of a large-scale malware campaign against Polish government institutions conducted by Russia-linked APT28.
Loading more articles....