

The Cyber Express
Russian Hackers Used Two New Backdoors to Spy on European Foreign Ministry
Researchers recently uncovered two new backdoors implanted within the infrastructure of a European Ministry of Foreign Affairs (MFA) and its


The Cyber Express
Researchers recently uncovered two new backdoors implanted within the infrastructure of a European Ministry of Foreign Affairs (MFA) and its

The Hacker News
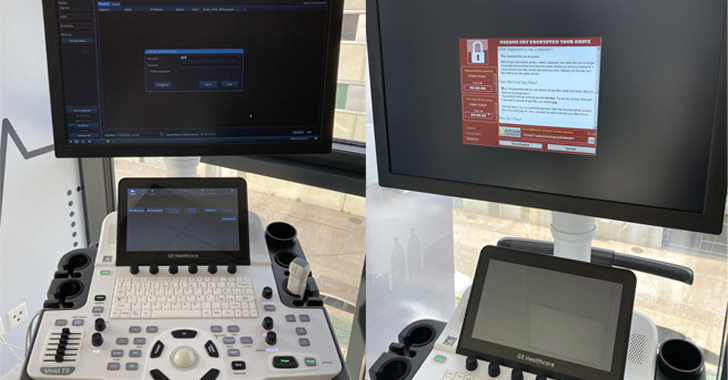
Nearly a dozen security flaws have been discovered in the GE HealthCare Vivid Ultrasound product family.

Cyber Security News
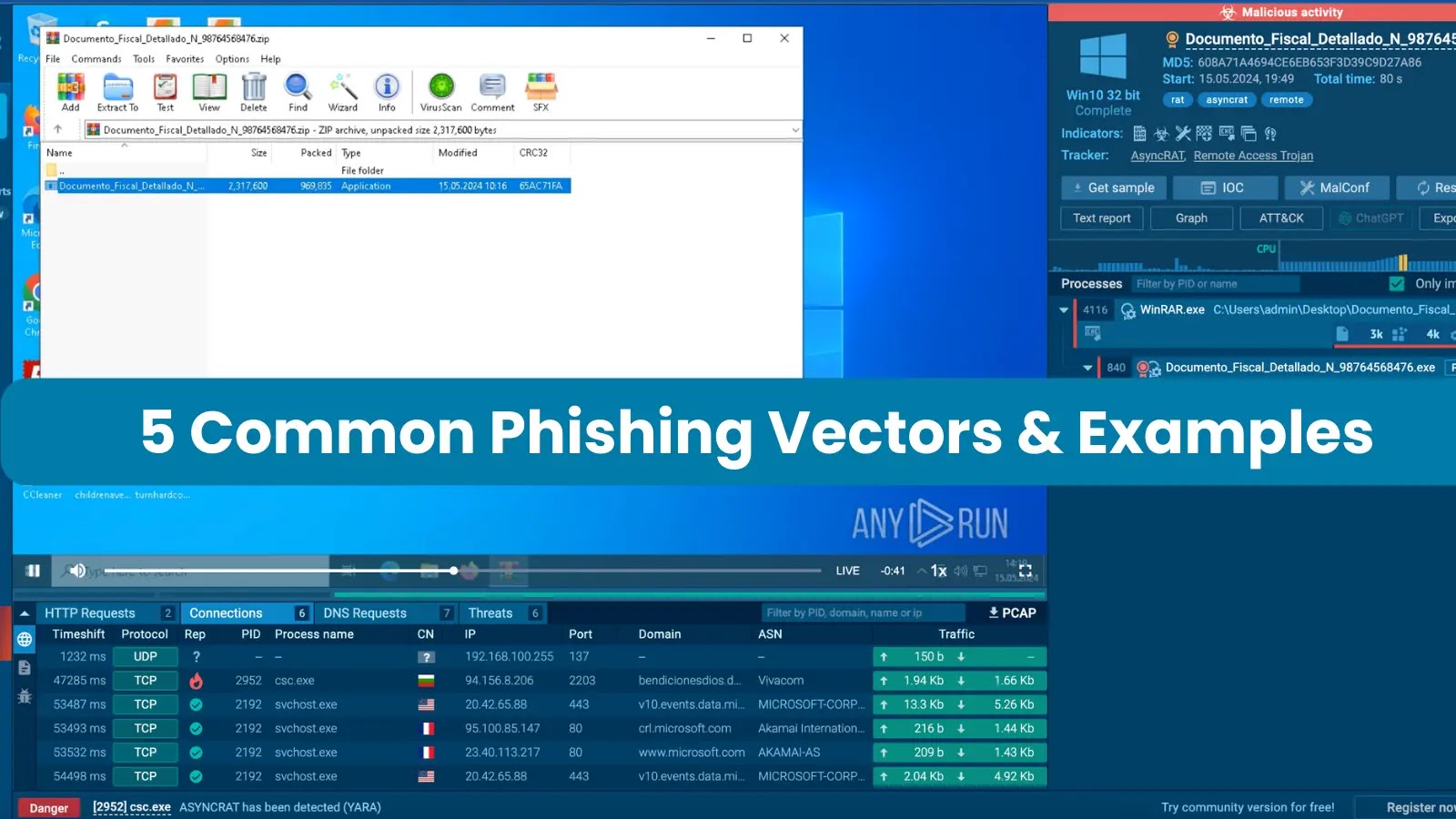
Phishing attacks can be executed through various means, such as SMS and phone calls, but the most prevalent method involves sending victims emails containing malicious attachments.


Infosecurity News
CPR said exploit builders in .NET and Python have been employed to deploy this malware


Bleeping Computer
Banco Santander S.A. announced it suffered a data breach impacting customers after an unauthorized actor accessed a database hosted by one of its third-party service providers.


SecurityWeek
Russian-speaking threat actors are caught abusing a GitHub profile to distribute information stealers posing as legitimate software.

.webp)
Cyber Security News
The well-known advanced persistent threat (APT) group Turla, which is based in Russia, is said to be going after the European Ministry.


The Hacker News
Two new backdoors, LunarWeb and LunarMail, have targeted a European ministry of foreign affairs and its diplomatic missions in the Middle East


SecurityWeek
The Ebury Linux botnet has ensnared over 400,000 Linux systems in 15 years, with roughly 100,000 still infected.


Ars Technica
"It’s easier to manage a team that’s happy.”


SecurityWeek
The FCC has issued a public notice on robocall scammer group ‘Royal Tiger’, the first designated threat actor.


SC Magazine
The FCC has smacked the group with a first-of-its-kind threat classification for its persistent, fraudulent activity.


Bleeping Computer
The Federal Communications Commission (FCC) has named its first officially designated robocall threat actor 'Royal Tiger,' a move aiming to help international partners and law enforcement more easily track individuals and entities behind repeat robocall campaigns.


The Cyber Express
An unidentified threat actor known as "pwns3c" has offered access to a database purported to contain sensitive data and documents

.png)
Cyber Security News
Staying informed is the key in this dynamic battle of cybersecurity, and due to this, the weekly news recap provides you with the newest trends, weaknesses, infringements found, and some possible defense mechanisms.


Ars Technica
Report claims new tracking starts May 13 with unclear consequences.


Bleeping Computer
The FBI warned retail companies in the United States that a financially motivated hacking group has been targeting employees in their gift card departments in phishing attacks since at least January 2024.


CyberSecurity Dive
Researchers have not identified any AI-engineered cyberattack campaigns, yet, but they say it’s only a matter of time before an AI system is dominant enough in the market to draw attention.


The Hacker News
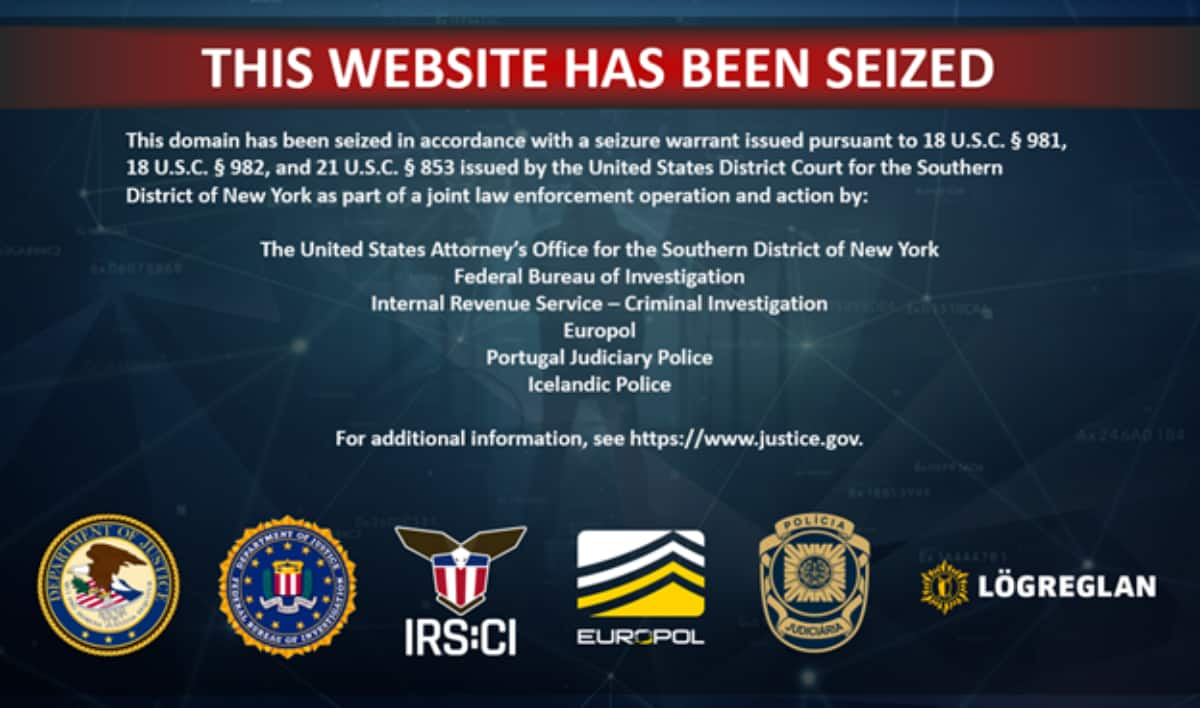
Russian operator of BTC-e crypto exchange pleads guilty to money laundering charges spanning 2011-2017.


Krebs on Security
The United States joined the United Kingdom and Australia today in sanctioning 31-year-old Russian national Dmitry Yuryevich Khoroshev as the alleged leader of the infamous ransomware group LockBit. The U.S. Department of Justice also indicted Khoroshev as the gang's leader…


Ars Technica
"One of the largest counterfeit-trafficking operations ever."


Ars Technica
Microsoft has been criticized for "preventable" failures and poor communication.


Bleeping Computer
The NSA and FBI warned that the APT43 North Korea-linked hacking group exploits weak email Domain-based Message Authentication Reporting and Conformance (DMARC) policies to mask spearphishing attacks.


SecurityWeek
CISA and the FBI warn of threat actors abusing path traversal software vulnerabilities in attacks targeting critical infrastructure.


Bleeping Computer
CISA and the FBI urged software companies today to review their products and eliminate path traversal security vulnerabilities before shipping.

SecurityWeek
Verizon 2024 DBIR shows that vulnerability exploitation increased three times and confirmed data breaches doubled compared to 2023.


CSO
Mandiant observed several malicious campaigns with threat actors impersonating journalists and harvesting the victim’s cloud environment credentials.


The Cyber Express
A threat actor has claimed to have leaked the database of the Department of Social Welfare Ladakh, Government of India.


SecurityWeek
UnitedHealth Group’s CEO Andrew Witty shares details on the damaging cyberattack in testimony before a US Congress committee on May 1.


Bleeping Computer
Latrodectus malware is now being distributed in phishing campaigns using Microsoft Azure and Cloudflare lures to appear legitimate while making it harder for email security platforms to detect the emails as malicious.


Bleeping Computer
Daily newspaper Philadelphia Inquirer revealed that attackers behind a May 2023 security breach have stolen the personal and financial information of 25,549 individuals.


DarkReading
Verizon, AT&T, and T-Mobile USA are being fined $200 million for sharing location data. They plan to appeal the decision, which is the culmination of a four-year investigation into how carriers sold customer data to third parties.


SecurityWeek
Muddling Meerkat conducts operations through DNS by creating large volumes of widely distributed queries that are propagated using open DNS resolvers.


SecurityWeek
Microsoft Copilot provides an easy and logical first step into GenAI for many organizations, but beware of the privacy pitfalls.


SC Magazine
The guidelines are part of Homeland Security’s ongoing efforts to reduce the risks, and maximize the benefits of artificial intelligence.


SecurityWeek
An analysis conducted by Honeywell shows that much of the USB-borne malware targeting industrial organizations can still cause OT disruption.


CyberNews
The FTC is claiming top Amazon executives, including founder Jeff Bezos, have been using disappearing messaging apps such as Signal to conceal potential evidence.


Cyber Security News
Welcome to this week's edition of the Cyber Security News Weekly Round-Up. This issue covers the latest vulnerabilities, cyber attacks, and emerging threats that have been making headlines. Stay informed and stay secure!

HACKRead
The official website of Samourai Wallet has been seized, while its official app on the Apple Store and Google Play has been removed.

Cyber Security News
Hackers abuse the Autodesk hosting platform to host malicious PDF files, which leads to phishing attacks on victims.


Cyber Security News
A critical vulnerability was addressed by Progress last week which was associated with unauthenticated Command injection on the Progress


SecurityWeek
A new phishing campaign abuses compromised email accounts and targets corporate users with PDF files hosted on Autodesk Drive.


DarkReading
A state-sponsored hacking team employed a clever masquerade and elaborate back-end infrastructure as part of a five-year info-stealing campaign that compromised the US State and Treasury Departments, and hundreds of thousands of accounts overall.


SecurityWeek
UnitedHealth confirms that personal and health information was stolen in a ransomware attack that could cost the company up to $1.6 billion.


SecurityWeek
New US guidance details foreign malign influence operations to help election infrastructure stakeholders increase resilience.


SecurityWeek
Malicious hackers are targeting SAP applications at an alarming pace, according to warnings from Onapsis and Flashpoint.


SecurityWeek
Five Eyes cybersecurity agencies have released joint guidance on securely deploying and operating AI systems.


The Hacker News
Ever worried about malware in PDFs? ANY.RUN's sandbox can expose hidden threats just by analyzing the file's structure.


Ars Technica
Broadcom reportedly accused of changing VMware licensing and support conditions.


CyberNews
Canada will press ahead with the introduction of a digital services tax on large tech companies, Because these firms are American, Washington thinks the plan is unfair.


SecurityWeek
Charles O. Parks III was arrested and charged with defrauding two cloud-services providers of $3.5 million.


The Hacker News
The FTC fined mental telehealth service Cerebral over $7 million for deceptive data sharing practices and failing to honor its cancellation policies.

Krebs on Security
For nearly a dozen years, residents of South Carolina have been kept in the dark by state and federal investigators over who was responsible for hacking into the state's revenue department in 2012 and stealing tax and bank account information…

Cyber Security News
we’ll dissect a timely example of credential theft—StrelaStealer—to identify the malware’s characteristics and capabilities.


CSO
Malware Next-Gen will allow organizations to submit suspicious files and URLs for analysis.


HACKRead
In this article, we will explore 12 paid and free OSINT tools that can be very useful when utilized properly and for appropriate purposes.


Bleeping Computer
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has released a new version of "Malware Next-Gen," now allowing the public to submit malware samples for analysis by CISA.


Bleeping Computer
LastPass revealed this week that threat actors targeted one of its employees in a voice phishing attack, using deepfake audio to impersonate Karim Toubba, the company's Chief Executive Officer.


SecurityWeek
CISA issues a red-alert for what appears to be a massive supply chain breach at Sisense, a company that sells big-data analytics services.

Bleeping Computer
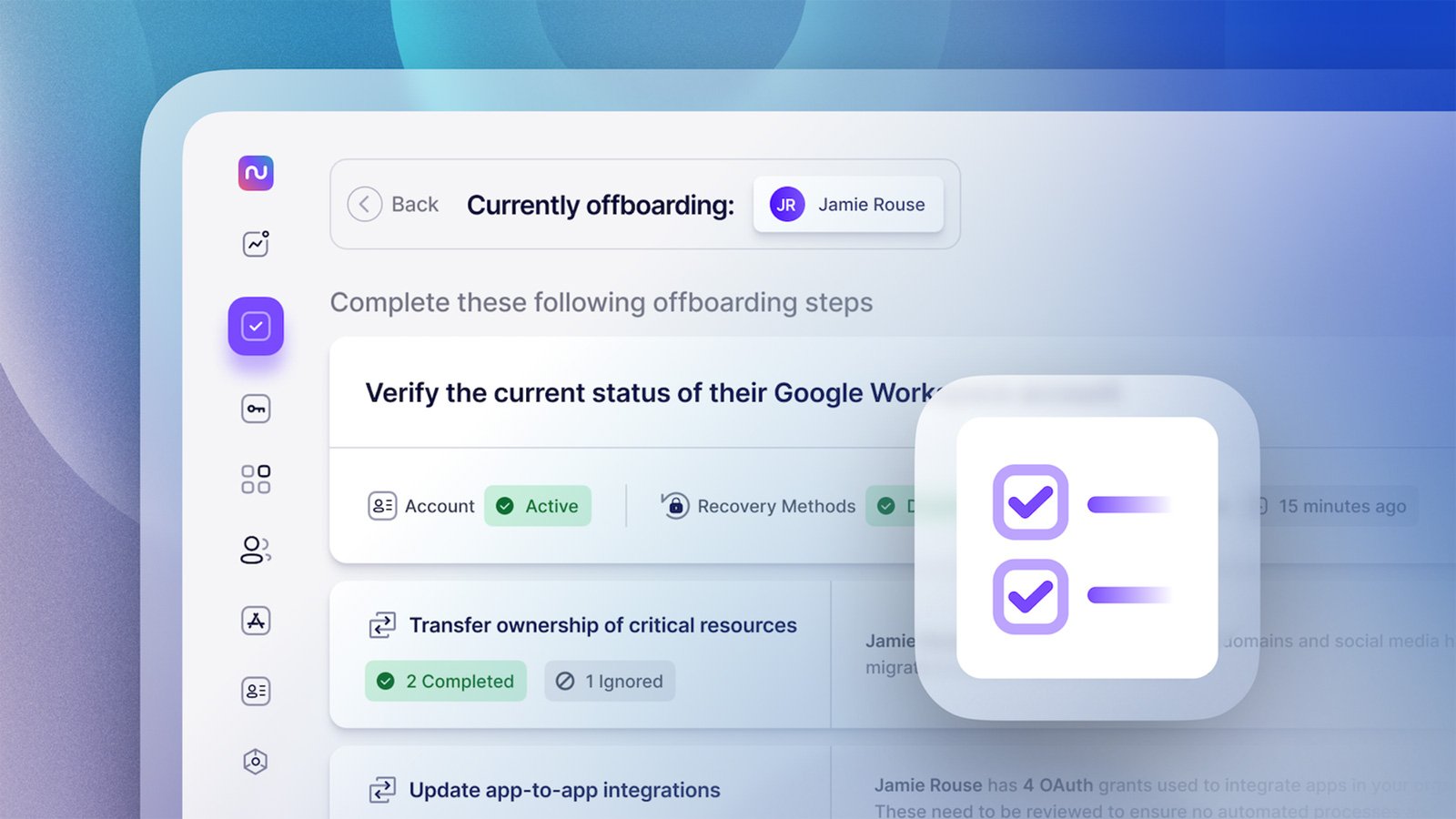
Employee offboarding isn't anybody's favorite task—but it's a critical IT process that needs to be executed diligently and efficiently. Learn more from Nudge Security on automating offboarding of users in a secure manner.


SecurityWeek
The financial sector has suffered over 20,000 cyberattacks in two decades, causing more than $12 billion in losses.


SecurityWeek
The Malware Next-Gen system is now available for any organization to submit malware samples and other suspicious artifacts for analysis.


SecurityWeek
The personal information of 500,000 people was compromised in a data breach at Group Health Cooperative of South Central Wisconsin.


DarkReading
A cheat sheet for all of the most common techniques hackers use, and general principles for stopping them.


Infosecurity News
DTEX claims industrial espionage and IP theft are at an all-time high thanks to malicious insiders


DarkReading
With a complex attack chain and a Telegram C2, CoralRaider targets victims in Asian countries — and appears to have accidentally infected itself.


Infosecurity News
Fortinet said the malware functions identified include screen monitoring, screen capturing, cryptomining and more


SecurityWeek
The US Department of Health warns of financially motivated social engineering attacks targeting healthcare organizations.


CyberNews
Chinese actors have been doubling down on familiar targets over the past year and are now using AI-generated content to achieve their goals, a report from Microsoft says.


DarkReading
An ongoing cyberattack with ties to China uses new version of sophisticated JSOutProx Trojan, now targeting banks in the Middle East.


Cyber Security News
GitLab is a prominent web-based Git repository manager that is exploited by hackers to gain unauthorized access to confidential source code,


SC Magazine
Hackers are using a sophisticated social engineering ruse targeting IT help desk staff to gain initial access to healthcare organizations.


Bleeping Computer
Windows 11 24H2 is set to arrive on existing devices this fall with several new features, mostly Copilot-related improvements.

Bleeping Computer
Microsoft is now using a Windows driver to prevent users from changing the Windows 10 and Windows 11 default browser manually or through software.


Cyber Security News
Welcome to the Cyber Security News Weekly Round-Up. Each week, we will explore the latest cyber threats, vulnerabilities, and notable stories that have shaped the cybersecurity landscape.


Bleeping Computer
The U.S. Department of Health and Human Services (HHS) warns that hackers are now using social engineering tactics to target IT help desks across the Healthcare and Public Health (HPH) sector.


Cyber Security News
PDF files weaponized by hackers are commonly used as an attack vector since PDFs are highly trusted and shared documents.


HACKRead
Cybersecurity firm Fortinet alerts users of a phishing scam campaign distributing the Byakugan malware which targets Windows users.


SecurityWeek
Japanese lens maker Hoya says production processes and ordering systems were disrupted by a cyberattack that may involve ransomware.

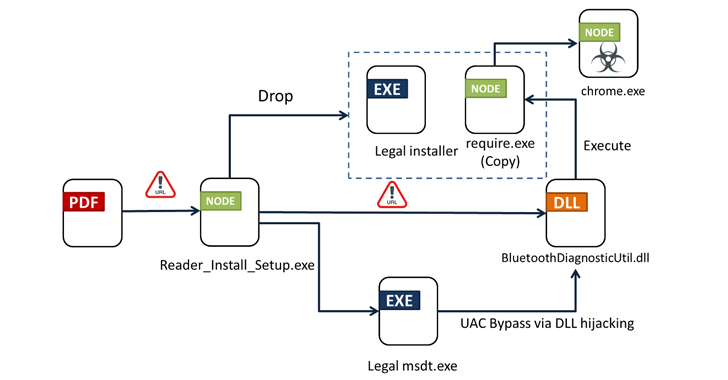
The Hacker News
Watch out for FAKE Adobe Acrobat Reader installers. They carry a nasty malware called Byakugan that steals your data.


Cyber Security News
Hackers use weaponized PDF files as they have the ability to incorporate malicious codes or scripts within a well-known and trusted form of


The Hacker News
Financial organizations in APAC & MENA are under attack. A sophisticated threat dubbed JSOutProx combines JavaScript & .NET to infiltrate systems.


Computerworld
Why are so many companies sending out emails to customers that look like phasing attempts? Don't they pay attention to their own security efforts?


Bleeping Computer
Visa is warning about a spike in detections for a new version of the JsOutProx malware targeting financial institutions and their customers.


Bleeping Computer
Hoya Corporation, one of the largest global manufacturers of optical products, says a "system failure" caused servers at some of its production plants and business divisions to go offline on Saturday.


Infosecurity News
First found in 2019, JSOutProx combines JavaScript and .NET functionalities to infiltrate systems


The Hacker News
Oil & gas companies beware! Hackers are using the updated Rhadamanthys info-stealer in phishing attacks.

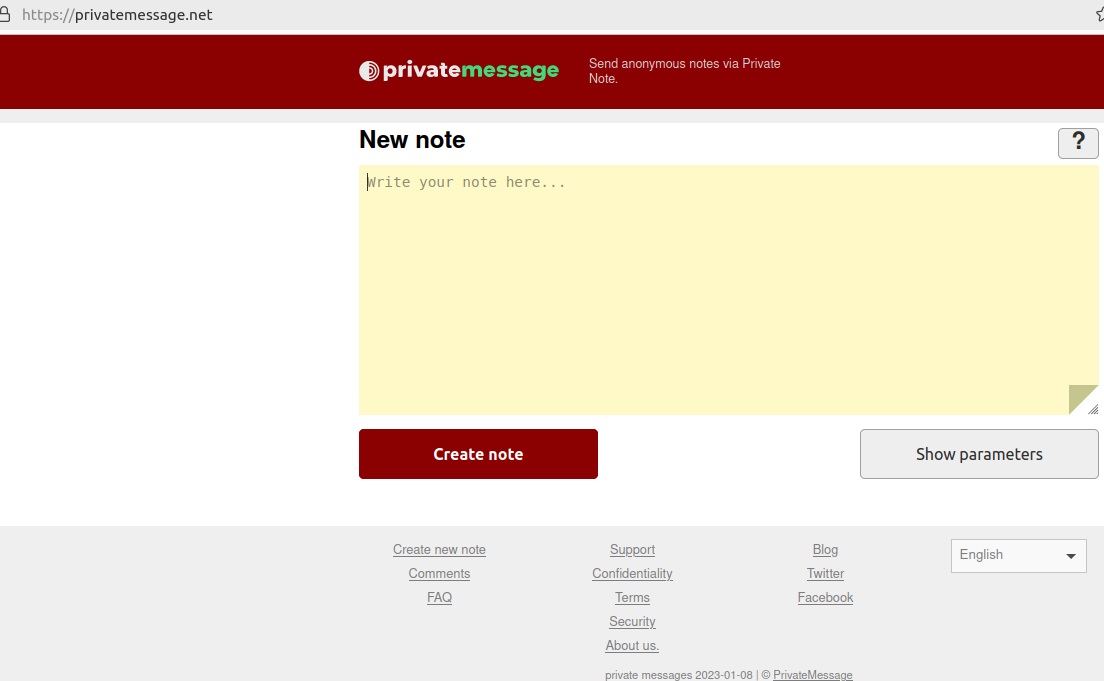
Krebs on Security
A cybercrook who has been setting up websites that mimic the self-destructing message service Privnote.com accidentally exposed the breadth of their operations recently when they threatened to sue a software company. The disclosure revealed a profitable network of phishing sites…

Bleeping Computer
Jackson County, Missouri, is in a state of emergency after a ransomware attack took down some county services on Tuesday.


DarkReading
Effective Rhadamanthys phishing campaign spoofs nonexistent "Federal Bureau of Transportation" to compromise recipients, analysts discover.


HACKRead
The Sophos report is based on a survey of nearly 3,000 IT professionals whose organizations fell victim to ransomware attacks in the past year.


HACKRead
The Sophos report is based on a survey of nearly 3,000 IT professionals whose organizations fell victim to ransomware attacks in the past year.


The Hacker News
Banking trojan Mispadu expands from Latin America, now targets users in Italy, Poland & Sweden. Finance, automotive, legal & commercial entities at ri


Ars Technica
Industry groups aren't giving up hope for government intervention.

%20--%20Supply%20Chain%20Backdoor%20(1).webp)
Cyber Security News
Fedora Linux 40 beta users have been urged to take immediate action after an Upstream supply chain attack that has compromised SSH protocol.


Cyber Security News
The European Union Agency for Cybersecurity (ENISA) has published a list of the top ten emerging threats anticipated to impact the digital.


Cyber Security News
Over the past year, macOS users, particularly those in the cryptocurrency sector, have been increasingly targeted by infostealers.


Cyber Security News
AT&T has confirmed that personal data from approximately 73 million current and former customers has been leaked on the dark web. This confirmation comes after the telecommunications giant initially denied that the leaked data originated from their systems.


Cyber Security News
An automated risk detection system identified a typosquatting campaign targeting popular Python libraries on PyPI.


The DFIR Report
Key Takeaways We provide a range of services, one of which is our Threat Feed, specializing in monitoring Command and Control frameworks like Cobalt Strike, Metasploit, Sliver, Viper, Mythic, Havoc, … Read More
Loading more articles....