

Computerworld
Apple updates its Platform Security Guide
It's essential reading for IT admins, security researchers and anyone with an interest in Apple security, now updated for 2024.


Computerworld
It's essential reading for IT admins, security researchers and anyone with an interest in Apple security, now updated for 2024.


The Hacker News
A new malware called "Cuckoo" is on the loose, targeting both Intel and ARM-based Macs.

.png)
Cyber Security News
The weekly news summary keeps you up to date with what’s happening in cybersecurity, including developments, vulnerabilities, breaches, threats, and defensive strategies. Knowing about new cyber risks and attack vectors helps you put up safeguards and preventive measures as soon as possible to protect your systems. Remaining constantly aware gives you a holistic view of […]

.webp)
Cyber Security News
A new variant of the notorious Adload malware has been discovered to bypass the latest updates to Apple's built-in antivirus, XProtect.


SecurityWeek
Threat Detection Report (2024) is based on analysis of almost 60,000 threats across 216 petabytes of telemetry from over 1,000 endpoints.

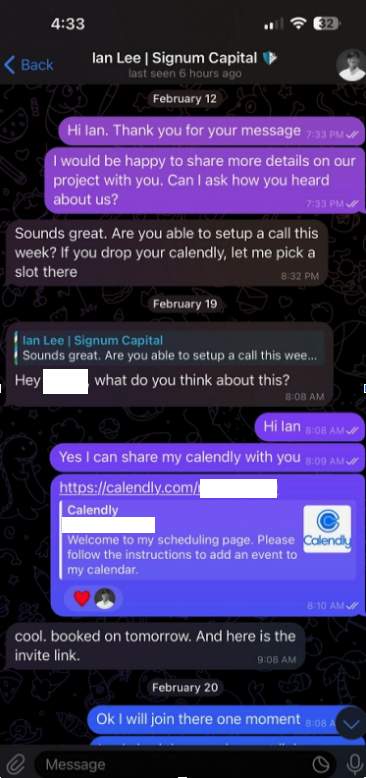
Krebs on Security
Malicious hackers are targeting people in the cryptocurrency space in attacks that start with a link added to the target’s account at Calendly, a popular free calendar application for scheduling appointments and meetings. The attackers impersonate established cryptocurrency investors and…


Computerworld
Apple is updating fundamental Mac protection at a higher release cadence than ever before.


SecurityWeek
WhatsApp privacy issue remains unpatched, spying via tablet ambient light sensors, and the Bigpanzi botnet.


HACKRead
The iShutdown tool has been launched a few weeks after Kaspersky cybersecurity researchers revealed significant insights into Operation Triangulation. This investigation delves into how spyware threats compromise iPhones.


DarkReading
Emerging malware variants can evade various static-signature detection engines, including XProtect, as attackers rapidly evolve to challenge defense systems.


The Hacker News
Discover how a simple 'Shutdown.log' file on your iPhone could be the key to identifying the presence of notorious spyware.


Bleeping Computer
Multiple information stealers for the macOS platform have demonstrated the capability to evade detection even when security companies follow and report about new variants frequently.

Latest Hacking News
Researchers have found the new macOS malware “MetaStealer” running active campaigns against Mac devices. The Go-based infostealer lures victims via social engineering, specifically infecting Intel-based Mac systems. MetaStealer Actively Targeting Macs In Recent Malware Campaigns In a


SecurityWeek
The MetaStealer macOS information stealer has been targeting businesses to exfiltrate keychain and other valuable information.


Bleeping Computer
A new information stealer malware named 'MetaStealer' has appeared in the wild, stealing a wide variety of sensitive information from Intel-based macOS computers.

-1.webp)
Cyber Security News
XLoader has been serving as a particularly persistent and adaptable threat since 2015. It has undergone a transformative evolution that demands the attention of security experts.

DarkReading
Threat actors are distributing new "Realst" infostealer via fake blockchain games, researchers warn.


Security Affairs
An unnamed Japanese cryptocurrency exchange was the victim of a cyber attack aimed at deploying an Apple macOS backdoor named JokerSpy. Elastic Security Labs researchers provided details about a recently discovered intrusion at an unnamed cryptocurrency exchange, aimed at deploying an Apple macOS backdoor named JokerSpy. The researchers tracked the intrusion as REF9134, the threat […]


The Hacker News
A Japanese cryptocurrency exchange fell victim to a recent cyberattack, deploying the stealthy JokerSpy backdoor on Apple macOS.

Cyber Security News
The attackers are using a fraudulent version of the popular video editing software, Final Cut Pro, which has been modified to include malicious code.


Computerworld
Jamf Threat Labs has spotted a family of Mac malware, XMRig, that spreads through pirated versions of Final Cut Pro, Photoshop and Logic Pro X.


Computerworld
“We have a level of malware on the Mac that we don’t find acceptable,” Apple Senior Vice President of Software Engineering Craig Federighi said last year. He meant it....


The Hacker News
Hackers have updated the XCSSET malware to add support for macOS Monterey by updating the source code components to Python 3.


Computerworld
New technologies Apple highlighted at this month's WWDC show the company understands how the enterprise security landscape is changing — and underline a commitment to provide the tools needed to deal with that landscape.


ThreatPost
Huntress Labs R&D Director Jamie Levy busts the old “Macs don’t get viruses” myth and offers tips on how MacOS malware differs and how to protect against it.


Cyber Security News
An espionage threat actor from China known for attacking target organizations across Asia has been linked to a new malware implant for macOS devices.

SecurityWeek
A Chinese threat actor has been observed using a macOS variant of the malware known as Gimmick.


Security Affairs
Gimmick is a newly discovered macOS implant developed by the China-linked APT Storm Cloud and used to target organizations across Asia. In late 2021, Volexity researchers investigated an intrusion in an environment they were monitoring and discovered a MacBook Pro running macOS 11.6 (Big Sur) that was compromised with a previously unknown macOS malware tracked […]

The Hacker News
A new variant of Gimmick malware has been spotted that's designed to target Apple macOS systems.


Bleeping Computer
Researchers have discovered a previously unknown macOS malware variant called GIMMICK, which is believed to be a custom tool used by a Chinese espionage threat actor known as 'Storm Cloud.'


DarkReading
The authors of UpdateAgent have tweaked it yet again — for the fifth time in less than 18 months.


ThreatPost
Ashwin Vamshi Adware strains Shlayer and Bundlore are the most common malware in macOS – although they have slight variations, they have long invaded and bypassed Xprotect, Notarization, Gatekeeper, and File Quarantine, all security features pre-built into macOS. The Uptycs threat research team has tracked these threats, along with 90% of macOS malware in routine


Bleeping Computer
Attackers could use a new macOS vulnerability discovered by Microsoft to bypass System Integrity Protection (SIP) and perform arbitrary operations, elevate privileges to root, and install rootkits on vulnerable devices.

Bleeping Computer
Microsoft says it found new variants of macOS malware known as WizardUpdate (also tracked as UpdateAgent or Vigram), updated to use new evasion and persistence tactics.


Bleeping Computer
A new AdLoad malware variant is slipping through Apple's YARA signature-based XProtect built-in antivirus to infect Macs as part of multiple campaigns tracked by cybersecurity firm SentinelOne.


Bleeping Computer
If your organization is reliant on Apple devices, there's a robust solution to connect, manage, and protect your company's slate of devices, apps and corporate resources: Apple Enterprise Management from Jamf.