
Ars Technica
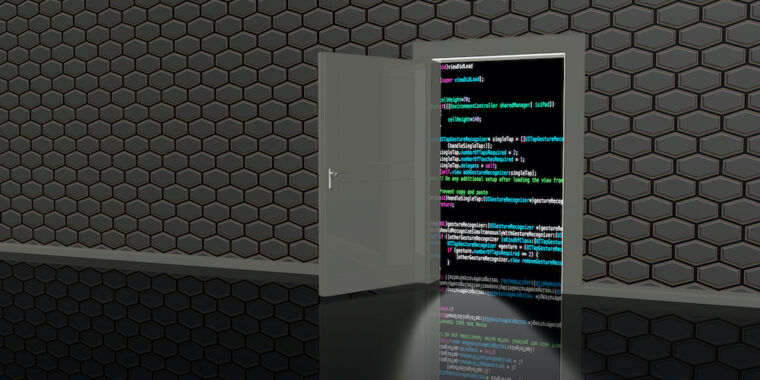
SSH backdoor has infected 400,000 Linux servers over 15 years and keeps on spreading
Ebury backdoors SSH servers in hosting providers, giving the malware extraordinary reach.

Ars Technica
Ebury backdoors SSH servers in hosting providers, giving the malware extraordinary reach.


DarkReading
A vulnerability in the HNAP login request protocol that affects a family of devices gives unauthenticated users root access for command execution.


SecurityWeek
The Ebury Linux botnet has ensnared over 400,000 Linux systems in 15 years, with roughly 100,000 still infected.

The Hacker News
Ebury malware botnet has compromised an estimated 400,000 servers since 2009. Learn how to protect your systems from this advanced threat.


CSO
CISA advisory includes indicators of compromise and TTPs that can be used for threat hunting.


Infosecurity News
The 15-year-old Ebury botnet is more active than ever, as ESET found 400,000 Linux servers compromised for cryptocurrency theft and financial gain

Bleeping Computer
A malware botnet known as 'Ebury' has infected almost 400,000 Linux servers since 2009, with roughly 100,000 still compromised as of late 2023.

.webp)
Cyber Security News
The botnet, operated by the threat group behind the Ebury malware, has been active since at least 2009 but has evolved over the past decade.

The Hacker News
12 security flaws addressed, including two critical issues leading to remote code execution. Update to version 1.2.27 now to stay protected


The Hacker News
A new social engineering campaign is targeting enterprises with spam emails to gain initial access. The threat actor overwhelms users' email and calls

Security Affairs
Experts reported that since April, the Phorpiex botnet sent millions of phishing emails to spread LockBit Black ransomware


SC Magazine
Emails from “Jenny Green” delivered LockBit Black through attached ZIP files.


Bleeping Computer
Since April, millions of phishing emails have been sent through the Phorpiex botnet to conduct a large-scale LockBit Black ransomware campaign.


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.

Security Affairs
Threat actors exploit recently disclosed Ivanti Connect Secure (ICS) vulnerabilities to deploy the Mirai botnet.


The Hacker News
Ivanti Connect Secure (ICS) devices are under attack! Two critical vulnerabilities are being exploited to deploy the notorious Mirai botnet.


SecurityWeek
As cyber threats grow more sophisticated, America can't afford complacency. The time for decisive action and enhanced cyber resilience is now.


SecurityWeek
Germany recalled its ambassador to Russia for consultations in Berlin following an alleged hacker attack on Chancellor Olaf Scholz’s party.


CSO
The attacks by Russia-backed Fancy Bear used an Outlook exploit to compromise several German officials’ accounts.


SecurityWeek
Germany was joined by NATO and fellow European countries in warning that Russia’s cyberespionage would have consequences.


The Hacker News
Czechia and Germany reveal they were targets of a massive cyber espionage campaign by Russia-linked APT28 hacker group.


HACKRead
A new botnet called Goldoon targets D-Link routers and NAS devices putting them at risk of DDoS attacks and more. Learn how weak credentials leave you vulnerable and how to secure your network. pen_spark

Security Affairs
The Ubiquiti EdgeRouter botnet is still used by Russia-linked group APT28 and cybercriminals organizations.


SecurityWeek
4,000 take part in Locked Shields 2024 exercise, Qantas and JP Morgan hit by data exposure bugs, NVIDIA patches critical flaw.


SecurityWeek
A botnet dismantled in January and used by Russia-linked APT28 consisted of more than just Ubiquiti Edge OS routers.


The Hacker News
A Ukrainian hacker part of the notorious REvil gang has been sentenced to over 13 years for orchestrating 2,500+ attacks demanding $700M in crypto ran


The Hacker News
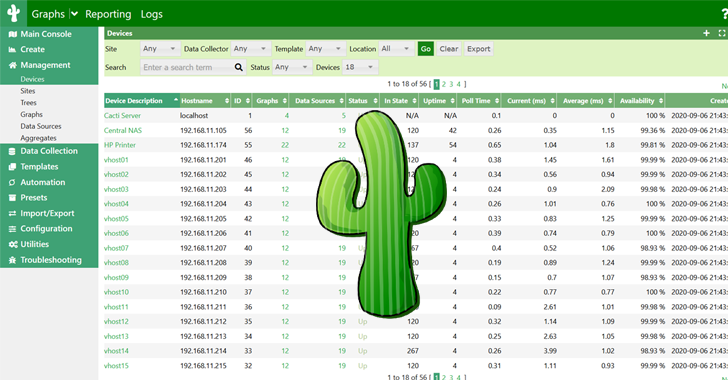
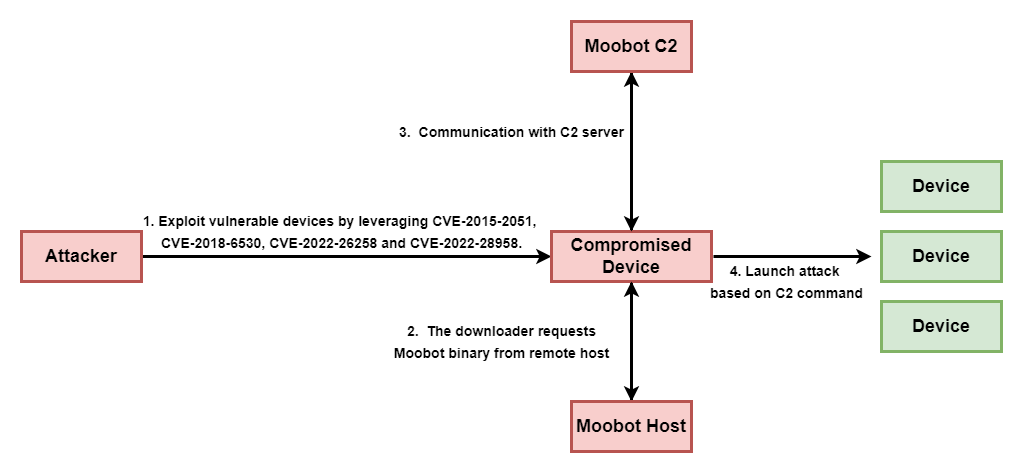
A new botnet called Goldoon is targeting D-Link routers with a critical vulnerability from 2015 (CVE-2015-2051).

Ars Technica
How and why nation-state hackers and cybercriminals coexist in the same router botnet.

The Record
Researchers at Fortinet are calling the botnet Goldoon. D-Link released a patch in 2015 for the bug that it exploits, but some device owners didn't install it.


SecurityWeek
Malware platform roaming around enterprise SOHO routers capable of covertly harvesting public cloud authentication data from internet traffic.

The Hacker News
Researchers have uncovered a new Android malware called Wpeeper that uses compromised WordPress sites to hide its true command-and-control servers.


Trend Micro
This blog entry aims to highlight the dangers of internet-facing routers and elaborate on Pawn Storm's exploitation of EdgeRouters, complementing the FBI's advisory from February 27, 2024.


Bleeping Computer
A new Android backdoor malware named 'Wpeeper' has been spotted in at least two unofficial app stores mimicking the Uptodown App Store, a popular third-party app store for Android devices with over 220 million downloads.


The Hacker News
The U.K. is the first country to ban default passwords on smart devices starting April 29, 2024. Manufacturers must provide unique passwords and secur

Krebs on Security
A 26-year-old Finnish man was sentenced to more than six years in prison today after being convicted of hacking into an online psychotherapy clinic, leaking tens of thousands of patient therapy records, and attempting to extort the clinic and patients.


Ars Technica
The law aims to prevent global-scale botnet attacks.

Ars Technica
Credential-stuffing attack uses proxies to hide bad behavior.


The Cyber Express
Okta reported an "unprecedented scale" of credential stuffing attacks targeting its identity and access management solutions, resulting in the breach


Infosecurity News
Okta has issues customers with new advice on how to block mounting credential stuffing attacks


CyberNews
The mobile devices and browsers of everyday users are behind the recent spike in credential-stuffing attacks.

The DFIR Report
Key Takeaways In August 2023, we observed an intrusion that started with a phishing campaign using PrometheusTDS to distribute IcedID. IcedID dropped and executed a Cobalt Strike beacon, which was … Read More

The Record
Britain now has IoT hardware standards that ban weak or easily guessable default passwords such as “admin” or “12345." Manufacturers are also required to publish contact details so users can report bugs.


Security Affairs
Identity and access management services provider Okta warned of a spike in credential stuffing attacks aimed at online services.


The Hacker News
Okta is sounding the alarm on an unprecedented spike in credential stuffing attacks targeting online services.

SecurityWeek
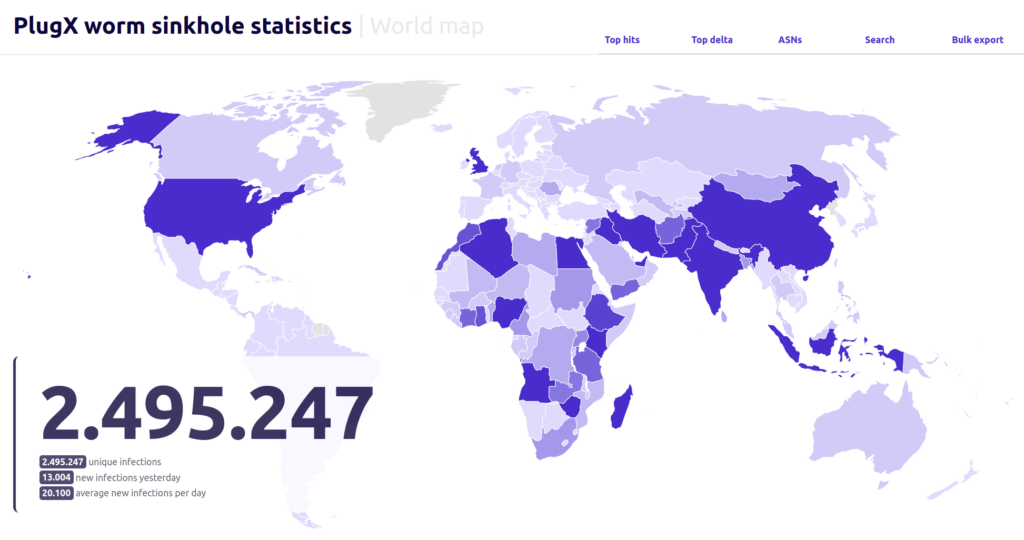
More than 90,000 unique IPs are still infected with a PlugX worm variant that spreads via infected flash drives.


SecurityWeek
Noteworthy stories that might have slipped under the radar: Volkswagen hacked by Chinese threat group, DDoS service shut down, Rubrik IPO.

The Record
Before the Russian elections, Meduza was the target of "the most intense cyber campaign" in its history. Since then, the onslaught hasn't let up.

Bleeping Computer
Researchers have sinkholed a command and control server for a variant of the PlugX malware and observed in six months more than 2.5 million connections from unique IP addresses.


SecurityWeek
Russia-linked APT28 deploys the GooseEgg post-exploitation tool against numerous US and European organizations.


SC Magazine
Microsoft says the launcher application is unique to Russia’s APT28 threat group and can lead to remote code execution.


HACKRead
A surge in attacks from the Androxgh0st malware family uncovers over 600 servers compromised primarily in the U.S., India and Taiwan.


Bleeping Computer
While ransomware attacks decreased after the LockBit and BlackCat disruptions, they have once again started to ramp up with other operations filling the void.


SecurityWeek
OpenSSF and OpenJS incidents similar to XZ backdoor, Moldovan botnet operator charged, US automotive company targeted by FIN7.


Security Affairs
China-linked threat actors are preparing cyber attacks against U.S. critical infrastructure warned FBI Director Christopher Wray.


Bleeping Computer
The U.S. Justice Department charged Moldovan national Alexander Lefterov, the owner and operator of a large-scale botnet that infected thousands of computers across the United States.


DarkReading
Moobot, Miori, AGoent, and a Gafgyt variant have joined the infamous Mirai botnet in attacking unpatched versions of vulnerable Wi-Fi routers.

Bleeping Computer
At least six distinct botnet malware operations are hunting for TP-Link Archer AX21 (AX1800) routers vulnerable to a command injection security issue reported and addressed last year.

.webp)
Cyber Security News
Exploitation of a critical vulnerability in TP-Link Archer routers, leading to the proliferation of various botnet threats.


The Hacker News
Researchers alert of a global rise in brute-force attacks from TOR nodes targeting VPNs, web interfaces, and SSH services


Bleeping Computer
Cisco warns about a large-scale credential brute-forcing campaign targeting VPN and SSH services on Cisco, CheckPoint, Fortinet, SonicWall, and Ubiquiti devices worldwide.

The Record
The bug affects the the Archer AX21, a popular router model manufactured by TP-Link.


Infosecurity News
An international team of researchers published the first-ever index ranking countries by cybercrime threat level


Cyber Security News
The weekly cybersecurity news wrap-up provides readers with the latest information on emerging risks, vulnerabilities, ways to reduce them, and harmful schemes to help make defensive measures proactive.


SecurityWeek
Researchers uncovered a Romanian cybercriminal group they call "RubyCarp" which they believe has been operational for at least ten years.


Trend Micro
Delve into the crucial practice of file scanning within uploader applications, and learn defensive measures to safeguards against malicious threats like malware.


SecurityWeek
An inside look at how Amazon Web Services (AWS) is leading the charge in the fight against IP spoofing and DDoS attacks.


The Record
The Cybersecurity and Infrastructure Security Agency added two bugs in older D-Link hardware to its Known Exploited Vulnerabilities list. Experts say 92,000 devices could be exposed.


DarkReading
Various anti-detection features, including use of ScrubCrypt antivirus-evasion tool, fuel an attack that aims to take over Microsoft Windows machines.


SecurityWeek
Many LG TVs may be vulnerable to remote hacking due to a series of vulnerabilities found by Bitdefender researchers.


The Record
Rubycarp has been in operation for at least a decade, and its campaigns appear to overlap with other cybercrime groups, according to researchers at Sysdig.


Ars Technica
LG patches four vulnerabilities that allow malicious hackers to commandeer TVs.


Infosecurity News
Palo Alto Networks observed growing malware-initiated vulnerability scanning activity


Bleeping Computer
A Romanian botnet group named 'RUBYCARP' is leveraging known vulnerabilities and performing brute force attacks to breach corporate networks and compromise servers for financial gain.


The Hacker News
RUBYCARP threat group, suspected to be of Romanian origin, has been discovered operating a botnet for crypto mining, DDoS, and phishing attacks


Infosecurity News
Threat actors are targeting a high severity vulnerability in close to 100,000 legacy D-Link devices


CSO
The group was discovered recently through Sysdig honeypots as it attempted to exploit a Laravel vulnerability.


The Hacker News
Hackers are exploiting vulnerabilities (CVE-2024-3272 and CVE-2024-3273) in D-Link NAS devices. Up to 92,000 devices affected.


The Record
Four new vulnerabilities affecting thousands of LG TVs have been found by researchers who said the issues allow hackers to add themselves as users and take other actions.


Bleeping Computer
Attackers are now actively targeting over 92,000 end-of-life D-Link Network Attached Storage (NAS) devices exposed online and unpatched against a critical remote code execution (RCE) zero-day flaw.


Cyber Security News
Law enforcement dismantled the Qakbot botnet's servers in 2023's Operation Duck Hunt, but researchers identified its reemergence with a


SecurityWeek
New HTTP/2 DoS method named Continuation Flood can pose a greater risk than Rapid Reset, which has been used for record-breaking attacks.


Infosecurity News
The findings from Netskope also show a shift in the retail sector’s use of cloud applications


The Hacker News
Traditional defense tactics don't always apply to cyber warfare. With EventSentry, bolster your network's defense with prevention, detection, and ongo


The Hacker News
Android VPN apps hijacking devices, covertly turning them into proxy nodes for threat actors and fueling botnet operations.


DarkReading
Our collection of the most relevant reporting and industry perspectives for those guiding cybersecurity strategies and focused on SecOps. Also included: Australia gets its cyber-groove back, and 2023's zero-day field day.


DarkReading
Outdated SOHO routers and IoT devices being hijacked by TheMoon to operate an anonymous hacker botnet service called Faceless.


The Hacker News
TheMoon botnet, previously thought to be inactive, is back. Over 40,000 routers & IoT devices hijacked to power Faceless - a criminal proxy service.


SC Magazine
Malware first identified in 2014 re-emerges and gets delivered by the criminal proxy service Faceless, now growing at 7,000 users per week.


Bleeping Computer
Cisco has shared a set of recommendations for customers to mitigate password-spraying attacks that have been targeting Remote Access VPN (RAVPN) services configured on Cisco Secure Firewall devices.


DarkReading
Those with special committees that include a cyber expert rather than relying on the full board more likely to improve security and financial performance.

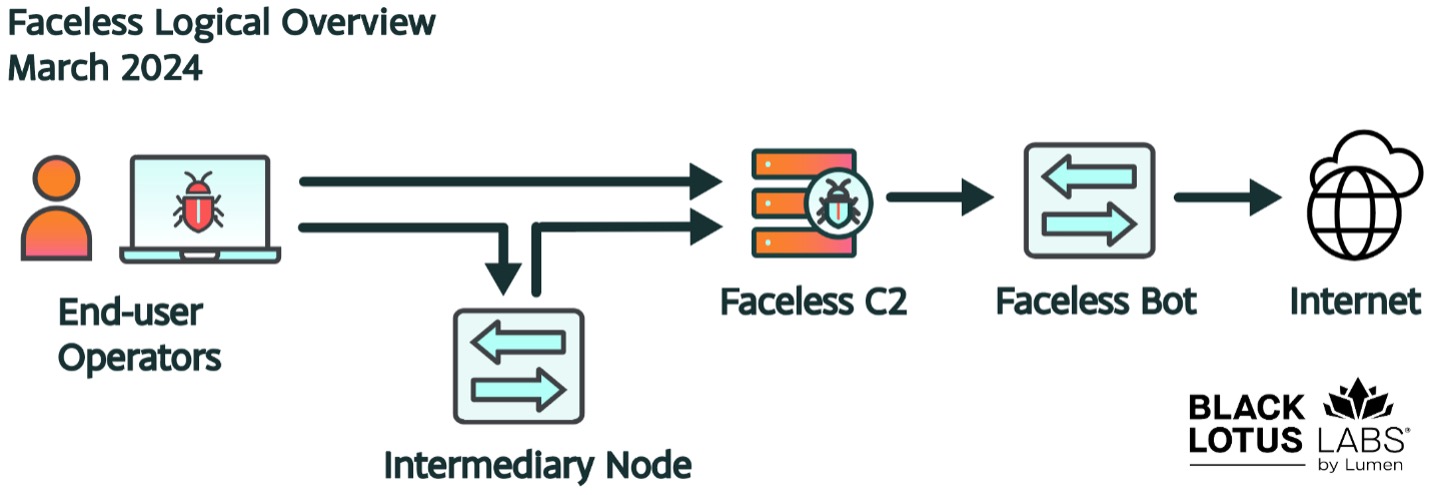
Security Affairs
A new variant of TheMoon malware infected thousands of outdated small office and home office (SOHO) routers and IoT devices worldwide.


Ars Technica
Two new reports show criminals may be using your device to cover their online tracks.


SecurityWeek
Malware hunters sound an alarm after discovering a 40,000-strong botnet packed with end-of-life routers and IoT devices powering cybercrime.


Infosecurity News
The Diligent and Bitsight report found that stronger cybersecurity measures equate to significantly higher financial performance for businesses


Bleeping Computer
A new variant of "TheMoon" malware botnet has been spotted infecting thousands of outdated small office and home office (SOHO) routers and IoT devices in 88 countries.


The Hacker News
Minecraft faces a growing threat from DDoS attacks, impacting over 500 million registered users. Learn how these attacks disrupt gameplay and what you

Cyber Security News
First identified in 2020, Sysrv is a botnet that uses a Golang worm to infect devices and deploy cryptominers, propagates by exploiting


SecurityWeek
Praefortis is a new company pushing ethical and transparent recovery of lost or forgotten crypto wallet passwords.


The Hacker News
Researchers uncover AndroxGh0st, a tool targeting Laravel apps to steal sensitive data from .env files, affecting AWS & Twilio accounts.


SecurityWeek
Idaho man pleads guilty to hacking charges over cyberattacks he conducted in 2017 and 2018, which involved data theft and extortion.
Loading more articles....