

The Hacker News
Microsoft Outlook Flaw Exploited by Russia's APT28 to Hack Czech, German Entities
Czechia and Germany reveal they were targets of a massive cyber espionage campaign by Russia-linked APT28 hacker group.


The Hacker News
Czechia and Germany reveal they were targets of a massive cyber espionage campaign by Russia-linked APT28 hacker group.

Security Affairs
The Ubiquiti EdgeRouter botnet is still used by Russia-linked group APT28 and cybercriminals organizations.


SecurityWeek
A botnet dismantled in January and used by Russia-linked APT28 consisted of more than just Ubiquiti Edge OS routers.


The Hacker News
A new botnet called Goldoon is targeting D-Link routers with a critical vulnerability from 2015 (CVE-2015-2051).

Ars Technica
How and why nation-state hackers and cybercriminals coexist in the same router botnet.


Trend Micro
This blog entry aims to highlight the dangers of internet-facing routers and elaborate on Pawn Storm's exploitation of EdgeRouters, complementing the FBI's advisory from February 27, 2024.


SC Magazine
The IAM service provider said easy access to stolen credentials and residential proxy services were behind the surge.


Security Affairs
Identity and access management services provider Okta warned of a spike in credential stuffing attacks aimed at online services.


The Hacker News
Okta is sounding the alarm on an unprecedented spike in credential stuffing attacks targeting online services.


Bleeping Computer
Cisco warned today that a state-backed hacking group has been exploiting two zero-day vulnerabilities in Adaptive Security Appliance (ASA) and Firepower Threat Defense (FTD) firewalls since November 2023 to breach government networks worldwide.


SecurityWeek
Russia-linked APT28 deploys the GooseEgg post-exploitation tool against numerous US and European organizations.


Bleeping Computer
Microsoft warns that the Russian APT28 threat group exploits a Windows Print Spooler vulnerability to escalate privileges and steal credentials and data using a previously unknown hacking tool called GooseEgg.


Bleeping Computer
Microsoft warns that the Russian APT28 threat group exploits a Windows Print Spooler vulnerability to escalate privileges and steal credentials and data using a previously unknown hacking tool called GooseEgg.


Bleeping Computer
Cisco has released patches for a high-severity Integrated Management Controller (IMC) vulnerability with public exploit code that can let local attackers escalate privileges to root.


SecurityWeek
Cisco has observed an increase in brute-force attacks targeting web application authentication, VPNs, and SSH services.


The Hacker News
Researchers alert of a global rise in brute-force attacks from TOR nodes targeting VPNs, web interfaces, and SSH services


Security Affairs
Cisco Talos warns of large-scale brute-force attacks against VPN services, web application authentication interfaces and SSH services.


Ars Technica
Attacks coming from nearly 4,000 IP addresses take aim at VPNs, SSH and web apps.


CyberNews
A new advisory warns of an uptick in brute force attacks targeting VPNs, SSH services, and other services.


Bleeping Computer
Cisco warns about a large-scale credential brute-forcing campaign targeting VPN and SSH services on Cisco, CheckPoint, Fortinet, SonicWall, and Ubiquiti devices worldwide.


Infosecurity News
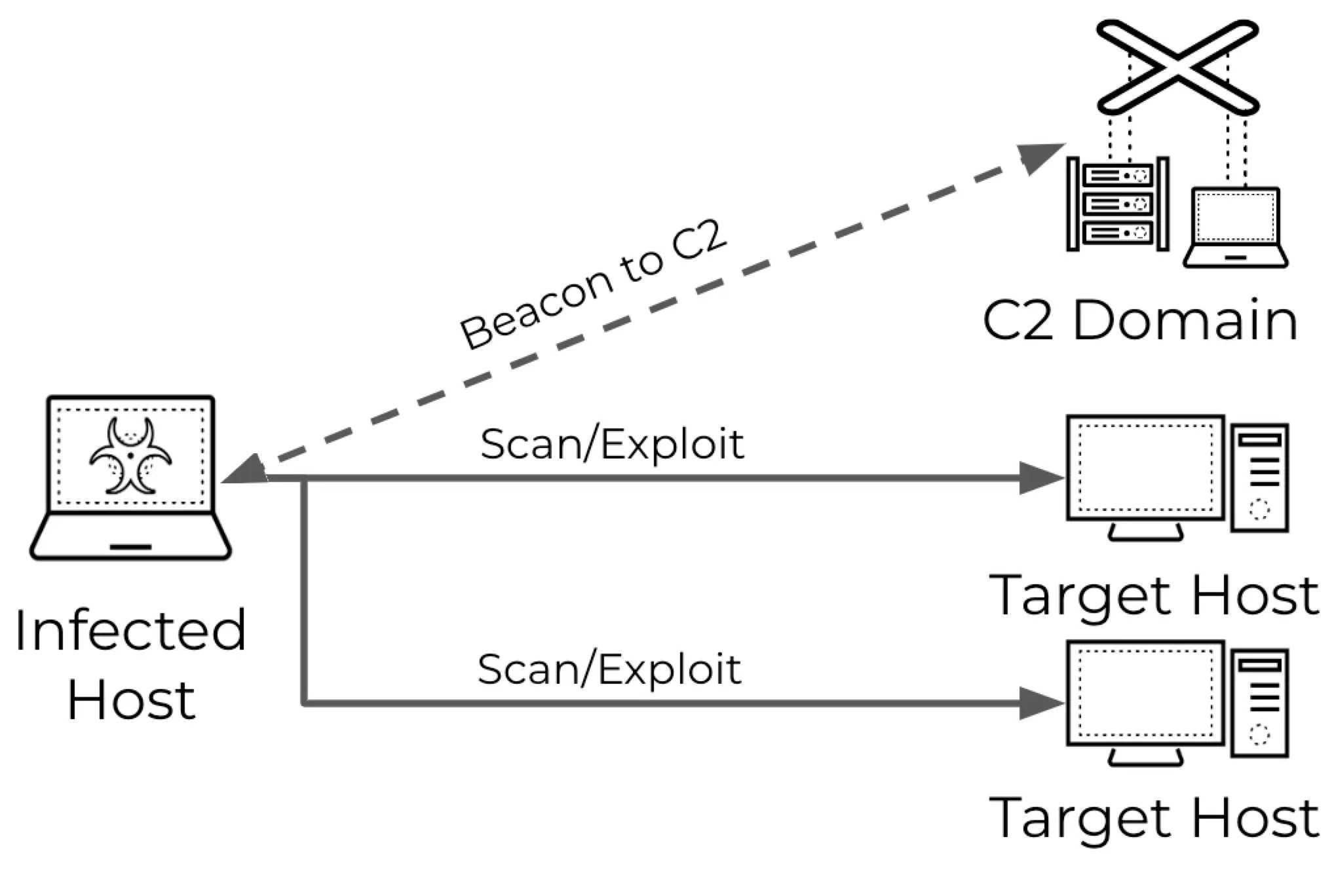
Palo Alto Networks observed growing malware-initiated vulnerability scanning activity

Cyber Security News
Adversaries are increasingly utilizing malware-infected devices to perform scans on target networks, shifting away from traditional direct


SC Magazine
Malware first identified in 2014 re-emerges and gets delivered by the criminal proxy service Faceless, now growing at 7,000 users per week.


SecurityWeek
Malware hunters sound an alarm after discovering a 40,000-strong botnet packed with end-of-life routers and IoT devices powering cybercrime.


The Hacker News
IBM X-Force uncovers extensive phishing campaigns by APT28, targeting Europe, the South Caucasus, Central Asia, and the Americas.


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


Infosecurity News
The routers were hijacked to steal credentials, proxy traffic, and host phishing pages and custom tools


Cyber Security News
Threat actors hijack routers to gain unauthorized access to network traffic. This enables them to monitor, manipulate, or intercept sensitive


SecurityWeek
The US government says Russia’s APT28 group compromised Ubiquiti EdgeRouters to run cyberespionage operations worldwide.


HACKRead
Russian hackers from APT28 are using hacked Ubiquiti EdgeRouters to build extensive botnets, steal credentials and other malicious activities.


Security Affairs
Russian cyberspies are compromising Ubiquiti EdgeRouters to evade detection, warns a joint advisory published by authorities.


The Hacker News
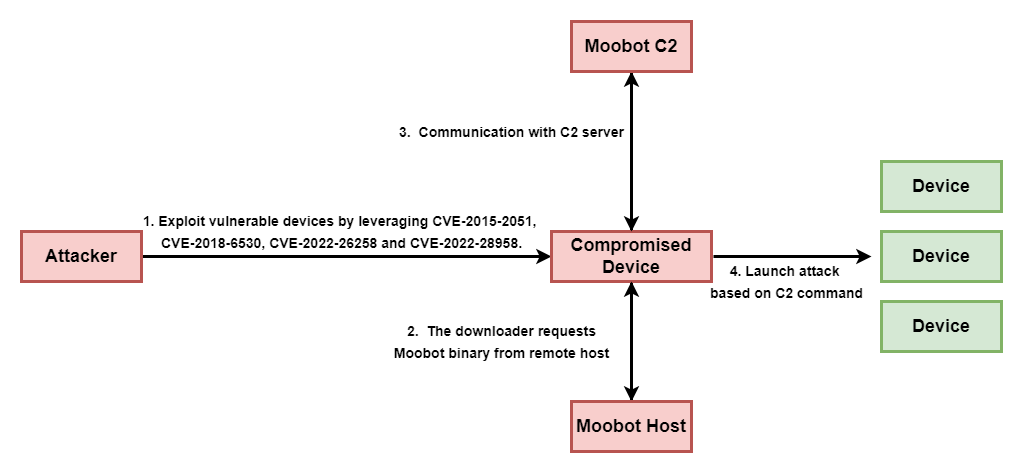
Nations unite to warn against the MooBot botnet threat targeting Ubiquiti EdgeRouters.


SC Magazine
The routers’ utility makes them “popular for both consumers and malicious cyber actors,” security agencies warn.


Ars Technica
Six years on, routers remain a favorite post for concealing malicious activities.

Bleeping Computer
Russian APT28 military hackers are using compromised Ubiquiti EdgeRouters to evade detection, the FBI says in a joint advisory issued with the NSA, the U.S. Cyber Command, and international partners.


Cyber Security News
Best Automatic WiFi Security Providers : 1. Perimeter 81 2. Cisco Systems 3. Fortinet 4. Palo Alto Networks 5. Aruba Networks 6. Sophos.


SecurityWeek
US government and allies expose TTPs used by notorious Russian hacking teams and warn of the targeting of dormant cloud accounts.


Ars Technica
Feds once again fix up compromised retail routers under court order.


CyberNews
The Department of Justice (DoJ) says it has taken down a global botnet controlled by Russia’s military intelligence agency, the GRU.


CyberSecurity Dive
Russia’s GRU-backed group exploited hundreds of vulnerable routers to conduct spear phishing and credential harvesting attacks against U.S. targets.


The Hacker News
U.S. government disrupted a botnet comprised of SOHO routers used by the Russia-linked APT28 group for malicious activities.


SC Magazine
For the second time this year, U.S. authorities neutralize a botnet of SOHO routers run by nation-state threat actors.

DarkReading
The feds have disrupted a Russian intelligence SOHO router botnet notable for being built with Moobot malware rather than custom code.


Security Affairs
The US authorities dismantled the Moobot botnet, which was controlled by the Russia-linked cyberespionage group APT28


PCMag
The Kremlin's notorious 'Fancy Bear' hacking group gained access to the routers by working with another Russian cybercriminal gang, the FBI says.


SecurityWeek
The US government says it has neutralized a network of hundreds of Ubiquiti Edge OS routers under the control of the notorious APT28 group.


Bleeping Computer
The FBI took down a botnet of small office/home office (SOHO) routers used by Russia's Main Intelligence Directorate of the General Staff (GRU) in spearphishing and credential theft attacks targeting the United States and its allies.


The Record
The court-authorized operation in January neutralized a botnet of routers “used to conceal and otherwise enable a variety of crimes," the Department of Justice said.


Cyber Security News
Attackers continue to use compromised routers as malicious infrastructure to target government organizations in Europe and the Caucasus region.


CyberNews
Ukraine’s National Cyber Security Center discovered a new phishing campaign aimed at Ukraine's military members led by the Russian-backed cybercriminal group APT28.


SecurityWeek
PoC exploit code targeting a critical Jenkins vulnerability patched last week is already publicly available.


HACKRead
Pwn2Own Automotive 2024, a 3-day contest, saw competitors earn $1,323,750 for hacking Tesla and discovering 49 zero-day bugs in EV systems.


Cyber Security News
On the final day of Pwn2Own Automotive 2024 - Day 3, researchers were granted $1,323,750 in rewards for identifying 49 distinct zero-days.


Bleeping Computer
The first edition of Pwn2Own Automotive has ended with competitors earning $1,323,750 for hacking Tesla twice and demoing 49 zero-day bugs in multiple electric car systems between January 24 and January 26.


DarkReading
Hacking teams pick apart electrical vehicles (EVs), exposing them for what they are: safety-critical computers without commensurate security.


Bleeping Computer
Security researchers hacked the Tesla infotainment system and demoed a total of 24 zero-days on the second day of the Pwn2Own Automotive 2024 hacking competition.


HACKRead
Bug Bounty Bonanza: Hackers Rake in Millions as Connected Cars Show Security Cracks at Pwn2Own Automotive 2024.


Infosecurity News
The Zero Day Initiative’s first Pwn2Own Automotive competition has handed out over $1m for 24 zero-days


SecurityWeek
On the first day of Pwn2Own Automotive participants earned over $700,000 for hacking Tesla, EV chargers and infotainment systems.


Cyber Security News
Pwn2Own 2024 Automotive is a unique event aimed at identifying and fixing flaws in connected automotive technologies.

Bleeping Computer
Security researchers hacked a Tesla Modem and collected awards of $722,500 on the first day of Pwn2Own Automotive 2024 for three bug collisions and 24 unique zero-day exploits.


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


Infosecurity News
VulnCheck claims the potential impact of Log4Shell was exaggerated


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


Ars Technica
"I was presented with 88 consoles from another account," one user reports.


Cyber Security News
Using a zero-day exploit in Microsoft Outlook (CVE-2023-23397), Fighting Ursa Aka APT28 targets at least 30 companies across 14 countries.


SecurityWeek
Thomas McCormick, aka fubar, an administrator of the Darkode hacking forum, has been sentenced to 18 months in prison.


The Record
A hacking group associated with Russia’s military intelligence agency has been spying on French universities, businesses, think tanks, and government agencies, according to a new report from France’s top cybersecurity agency.


Bleeping Computer
The Russian APT28 hacking group (aka 'Strontium' or 'Fancy Bear') has been targeting government entities, businesses, universities, research institutes, and think tanks in France since the second half of 2021.


Ars Technica
Turns out that only lightning could kill the otherwise-unkillable US-8-150W.


SecurityWeek
Former Navy IT manager Marquis Hooper was sentenced to prison for stealing PII and selling it on the dark web.

SecurityWeek
ZDI is offering more than $1 million at the Pwn2Own Automotive hacking contest, hosted in January at the Automotive World conference in Tokyo.


Cyber Security News
BGP is the backbone protocol and the internet's "glue," which directs the routing decisions between ISP networks to hold the internet under a set.


SecurityWeek
Serious flaw affecting BGP implementations can be exploited to cause prolonged internet outages, but several vendors have not patched it.


SecurityWeek
Olalekan Jacob Ponle, a Nigerian national living in the UAE, was sentenced to 8 years in a US prison for his role in an $8 million BEC scheme


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press. Russia-linked APT Gamaredon starts stealing data from victims between 30 and 50 minutes after the initial […]


SecurityWeek
Multiple hardcoded accounts on the Technicolor TG670 DSL gateway router can be used to completely take over the impacted devices.


Security Affairs
A Proof-of-Concept (PoC) exploit for the CVE-2023-31998 vulnerability in the Ubiquiti EdgeRouter has been publicly released. The CVE-2023-31998 flaw (CVSS v3 5.9) is a heap overflow issue impacting Ubiquiti EdgeRouters and Aircubes, an attacker can exploit it to potentially execute arbitrary code and interrupt UPnP service to a vulnerable device. The flaw resides in the […]


SecurityWeek
PoC exploit has been published for a recently patched Ubiquiti EdgeRouter vulnerability leading to arbitrary code execution.


SecurityWeek
Former contractor employee charged with hacking for accessing the systems of a water treatment facility in California


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press. We are in the final! Please vote for Security Affairs (https://securityaffairs.com/) as the best European Cybersecurity […]


Infosecurity News
The defendant was also ordered to pay $1.6m in restitution and forfeit property used for the crimes


Security Affairs
A former Ubiquiti employee has been sentenced to six years in jail for the theft of confidential data and extorting company for ransom. NICKOLAS SHARP, a former Ubiquiti employee was sentenced today to six years in prison. In December 2020, SHARP stole gigabytes of data from the company, then he posed as an anonymous hacker that was […]


The Hacker News
A former Ubiquiti employee has been sentenced to six years behind bars after attempting to extort $2 million in cryptocurrency.


DataBreaches
Graham Cluley writes: A former software engineer at Ubiquit Networks has been sent to prison for six years after stealing gigabytes of data from the firm,...


Bleeping Computer
Nickolas Sharp, a former senior developer of Ubiquiti, was sentenced to six years in prison for stealing company data, attempting to extort his employer, and aiding the publication of misleading news articles that severely impacted the firm's market capitalization.


DataBreaches
There’s an update to a previously reported case involving a former employee of Ubiquiti Networks, although as is their policy, the DOJ does not name...

Bleeping Computer
Nickolas Sharp, a former Ubiquiti employee who managed the networking device maker's cloud team, pled guilty today to stealing gigabytes worth of files from Ubiquiti's network and trying to extort his employer while posing as an anonymous hacker and a whistleblower.


Naked Security
That’s a mean average of $15,710 per bug… and 63 fewer bugs out there for crooks and rogues to find.

Infosecurity News
Competition awards winning participants nearly $1m

Bleeping Computer
Pwn2Own Toronto 2022 has ended with competitors earning $989,750 for 63 zero-day exploits (and multiple bug collisions) targeting consumer products between December 6th and December 9th.


Bleeping Computer
On the third day of Pwn2Own, contestants hacked the Samsung Galaxy S22 a fourth time since the start of the competition, and this time they did it in just 55 seconds.


Bleeping Computer
On the third day of Pwn2Own, contestants hacked the Samsung Galaxy S22 a fourth time since the start of the competition, and this time they did it in just 55 seconds.


Security Affairs
On the third day of the Zero Day Initiative’s Pwn2Own Toronto 2022 hacking competition, participants earned more than $250,000. On the third day of the Zero Day Initiative’s Pwn2Own Toronto 2022 hacking competition, participants earned more than $250,000 for demonstrating zero-day attacks against NAS devices, printers, smart speakers, routers, and smartphones. In the two days, participants earned […]

SecurityWeek
Exploits simulating a real world SOHO attack earned participants well over $100,000 on the third day of Pwn2Own Toronto 2022.


ThreatPost
The Russian-speaking APT behind the NotPetya attacks and the Ukrainian power grid takedown could be setting up for additional sinister attacks, researchers said.


Trend Micro
This report discusses the technical capabilities of this Cyclops Blink malware variant that targets ASUS routers and includes a list of more than 150 current and historical command-and-control (C&C) servers of the Cyclops Blink botnet.


The Record
After all the hype in December last year, threat actors appear to have lost interest in exploiting the Log4Shell vulnerability, as both Sophos and the SANS Internet Storm Center are reporting dwindling numbers this year.

The Hacker News
U.S. and U.K. cybersecurity agencies have issued an urgent warning about a new Russian botnet malware, dubbed Cyclops Blink.


ZDNet
Solid antivirus protection isn't enough anymore. Here's a brief guide to shoring up your SOHO and SMB cybersecurity defenses.
Loading more articles....