

The Hacker News
APT42 Hackers Pose as Journalists to Harvest Credentials and Access Cloud Data
APT42, an Iranian state-backed hacking group, is leveling up its social engineering tactics. They're posing as journalists and event organizers to bui


The Hacker News
APT42, an Iranian state-backed hacking group, is leveling up its social engineering tactics. They're posing as journalists and event organizers to bui


Bleeping Computer
The Iranian state-backed threat actor tracked as APT42 is employing social engineering attacks, including posing as journalists, to breach corporate networks and cloud environments of Western and Middle Eastern targets.


SecurityWeek
Palo Alto Networks has shared remediation instructions for organizations whose firewalls have been hacked via CVE-2024-3400.


DarkReading
A state-sponsored hacking team employed a clever masquerade and elaborate back-end infrastructure as part of a five-year info-stealing campaign that compromised the US State and Treasury Departments, and hundreds of thousands of accounts overall.


DarkReading
Growing attacks targeting the flaw prompted CISA to include it in the known exploited vulnerabilities catalog earlier this month.


SecurityWeek
Palo Alto Networks firewall vulnerability CVE-2024-3400, exploited as a zero-day, impacts a Siemens industrial product.


CyberSecurity Dive
The security vendor downplayed the impact of exploit activity, describing most attempts as unsuccessful, but outside researchers say 6,000 devices are vulnerable.


The Hacker News
MITRE, a top cybersecurity firm, breached by a nation-state. Zero-days and session hijacking were the weapons.


Latest Hacking News
A critical zero-day vulnerability in Palo Alto networks Pan-OS firewall has received an emergency fix following active exploitation. The vulnerability lets an attacker execute arbitrary codes on vulnerable devices under specific conditions. Given the active


SecurityWeek
MITRE R&D network hacked in early January by a state-sponsored threat group that exploited an Ivanti zero-day vulnerability.


SC Magazine
Proof-of-concept exploits for CVE-2024-3400 are now publicly available.


Cyber Security News
The MITRE Corporation has disclosed that a sophisticated cyber attack recently compromised one of its internal r&d networks.


The Cyber Express
The MITRE Corporation revealed on April 19 that it was one of over 1700 organizations compromised by a state-backed hacking

The Hacker News
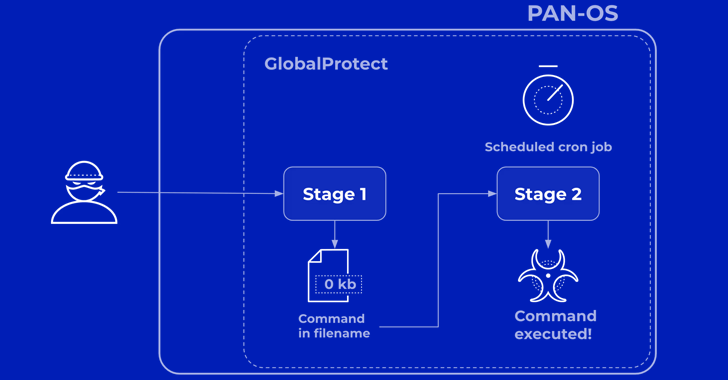
A critical vulnerability (CVE-2024-3400) in Palo Alto Networks PAN-OS is being actively exploited by threat actors.


Bleeping Computer
The MITRE Corporation says a state-backed hacking group breached its systems in January 2024 by chaining two Ivanti VPN zero-days.


Bleeping Computer
Approximately 22,500 exposed Palo Alto GlobalProtect firewall devices are likely vulnerable to the CVE-2024-3400 flaw, a critical command injection vulnerability that has been actively exploited in attacks since at least March 26, 2024.


CyberSecurity Dive
Attempted exploits and attacks linked to the zero-day vulnerability, which has a CVSS of 10, grew after proof of concepts were released.


SecurityWeek
Palo Alto Networks firewall vulnerability CVE-2024-3400 increasingly exploited after PoC code has been released.


Security Affairs
Researchers released an exploit code for the actively exploited vulnerability CVE-2024-3400 in Palo Alto Networks' PAN-OS.


CyberSecurity Dive
The security vendor said a “limited number of attacks” were linked to the exploited vulnerability. Volexity observed exploits dating back to March 26.


DarkReading
A likely sophisticated threat actor is leveraging the bug to deploy a Python backdoor for stealing data and executing other malicious actions.


HACKRead
Palo Alto Networks has released patches for a 0-day vulnerability (CVE-2024-3400) that threatened to leave firewalls exposed to cyberattacks.


Infosecurity News
Designated CVE-2024-3400 and with a CVSS score of 10.0, the flaw enables unauthorized actors to execute arbitrary code on affected firewalls


Security Affairs
U.S. CISA adds Palo Alto Networks PAN-OS Command Injection flaw to its Known Exploited Vulnerabilities catalog.

Bleeping Computer
Palo Alto Networks has started releasing hotfixes for a zero-day vulnerability that has been actively exploited since March 26th to backdoor PAN-OS firewalls.


Security Affairs
Threat actors have been exploiting the recently disclosed zero-day in Palo Alto Networks PAN-OS since March 26, 2024.


SecurityWeek
Palo Alto Networks has started releasing hotfixes for the firewall zero-day CVE-2024-3400, which some have linked to North Korea’s Lazarus.


The Hacker News
Palo Alto Networks has issued critical hotfixes for a severe security vulnerability in PAN-OS, which is being actively exploited.


The Record
The company released hotfixes for the vulnerability affecting GlobalProtect VPN, which carries the highest severity score possible of 10.


Bleeping Computer
Suspected state-sponsored hackers have been exploiting a zero-day vulnerability in Palo Alto Networks firewalls tracked as CVE-2024-3400 since March 26, using the compromised devices to breach internal networks, steal data and credentials.

The Hacker News
Hackers have been exploiting a severe flaw (CVE-2024-3400) in Palo Alto Networks' software that began nearly three weeks before discovery.


Ars Technica
No patch yet for unauthenticated code-execution bug in Palo Alto Networks firewall.


SecurityWeek
A state-sponsored threat actor has been exploiting a zero-day in Palo Alto Networks firewalls for the past two weeks.

Bleeping Computer
Today, Palo Alto Networks warns that an unpatched critical command injection vulnerability in its PAN-OS firewall is being actively exploited in attacks.


Infosecurity News
A fix for CVE-2024-3400 is scheduled on April 4, Palo Alto Networks announced


SecurityWeek
Palo Alto Networks warns of limited exploitation of a critical command injection vulnerability leading to code execution on firewalls.


The Hacker News
Critical security flaw found in Palo Alto Networks firewalls. Hackers are already taking advantage.


SC Magazine
The max severity (CVSS 10) bug enables command injection through the GlobalProtect feature.


The Record
The company released an advisory about a vulnerability in the popular GlobalProtect VPN product that was unknown to security researchers until this week.


SecurityWeek
Ivanti chief executive Jeff Abbott vows a complete overhaul of core engineering, security and vulnerability management practices.


SC Magazine
With its appliances repeatedly targeted by cyberespionage gangs, Ivanti's CEO has pledged a “new era” where security is paramount.


CyberSecurity Dive
Threat actors gained access to and potentially compromised two CISA systems weeks after the agency applied Ivanti’s initial mitigation measures.


The Record
Hackers breached the systems of the Cybersecurity and Infrastructure Security Agency (CISA) in February through vulnerabilities in Ivanti products, officials said.


Infosecurity News
Government agencies from the Five Eyes coalition said that Ivanti’s own tools are not sufficient to detect compromise


CyberScoop
The software company pushed back on the joint advisory, which comes following multiple directives from CISA this year prodding agencies to patch against Ivanti exploits.


SecurityWeek
Chinese threat actors target Ivanti VPN appliances with new malware designed to persist system upgrades.


DarkReading
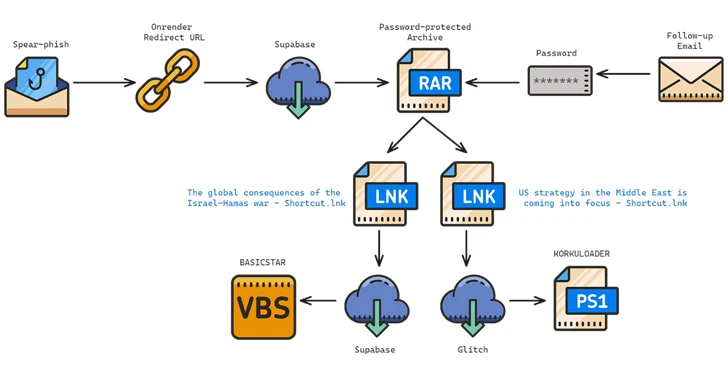
The latest ploy by the APT also known as Charming Cypress targets policy experts in the Middle East, Europe, and the US.

Cyber Security News
Ivanti Connect Secure vulnerabilities were disclosed in January 2024 as a potential gateway for threat actors to penetrate into corporate networks.

The Hacker News
The Iranian cyberespionage group Charming Kitten is using fake webinars and a new 'BASICSTAR' backdoor to target experts in Middle Eastern policy.

DarkReading
'Voltzite,' the APT's subset that focuses on OT networks and critical infrastructure, has also compromised targets in Africa.

Cyber Security News
CharmingCypress frequently uses novel social-engineering techniques in its phishing efforts, like emailing people & long-lasting discussions


CyberScoop
Dragos researchers found that the China-sponsored hacking group has been attacking electric utilities since 2023.


The Record
The issue is yet another chapter in Ivanti’s weeks-long scramble to address vulnerabilities that have been exploited by hackers.


HACKRead
The zero-day vulnerability, CVE-2024-21893 (CVSS score 8.2), disclosed by Ivanti on 31 January 2024, is now being actively exploited in the wild.


CyberSecurity Dive
After weeks of mitigation efforts, CISA ordered federal civilian agencies to disconnect the devices.


Ars Technica
Things were already bad with two critical zero-days. Then Ivanti disclosed a new one.


CyberScoop
An updated emergency directive includes instructions on how to bring affected devices back online securely.


SecurityWeek
In an unprecedented move, CISA is directing federal agencies to disconnect insecure Ivanti VPN products within 48 hours.


HACKRead
Cybersecurity concerns are rising as hackers try to exploit zero-day vulnerabilities in Ivanti VPN devices to deploy malware and crypto miners.


SecurityWeek
Ivanti documented a new zero-day and belatedly ships patches; Mandiant is reporting "broad exploitation activity" against the vulnerabilities


Bleeping Computer
Today, Ivanti warned of two more vulnerabilities impacting Connect Secure, Policy Secure, and ZTA gateways, one of them a zero-day bug already under active exploitation.


CyberSecurity Dive
The company also disclosed two additional high-severity vulnerabilities in Ivanti Connect Secure and Ivanti Policy Secure.

Security Affairs
Threat actors are exploiting recently disclosed zero-day flaws in Ivanti Connect Secure (ICS) VPN devices to deliver KrustyLoader.


The Hacker News
Chinese nation-state hacker group UTA0178 weaponized Ivanti VPN vulnerabilities to deploy the Rust-based KrustyLoader, cryptocurrency miners.


SC Magazine
Mandiant and CISA say security teams should prioritize the bugs as Ivanti released patches Jan. 31.


The Record
IT company Ivanti said this week that it discovered two new vulnerabilities affecting its products while investigating bugs discovered earlier in the month.


Infosecurity News
After analyzing the Rust payloads exploiting Ivanti ConnectSecure vulnerabilities, Synacktiv found they all enabled a post-exploitation toolkit


SecurityWeek
Ivanti is struggling to hit its own timeline for the delivery of patches for critical -- and already exploited -- flaws in VPN appliances.


Cyber Security News
According to the reports shared with Cyber Security News, there were more than 26000 unique internet-facing Ivanti VPN Connect Secure hosts.


Ars Technica
Orgs that haven't acted yet should, even if it means suspending VPN services.


SecurityWeek
Apple pushes out fresh versions of its iOS and macOS platforms to fix WebKit vulnerabilities being exploited as zero-day in the wild.


Bleeping Computer
Ivanti warned admins to stop pushing new device configurations to appliances after applying mitigations because this will leave them vulnerable to ongoing attacks exploiting two zero-day vulnerabilities.


Infosecurity News
US security agency CISA orders all civilian federal agencies to take immediate steps to mitigate two Ivanti zero-day flaws

The Hacker News
CISA issues emergency directive against two major zero-day actively exploited flaws in Ivanti products.

CyberScoop
The agency says the bug is being actively exploited and poses a risk to federal networks.


SecurityWeek
The US government’s cybersecurity agency CISA ramps up the pressure on organizations to mitigate two exploited Ivanti VPN vulnerabilities.


Bleeping Computer
CISA issued this year's first emergency directive ordering Federal Civilian Executive Branch (FCEB) agencies to immediately mitigate two Ivanti Connect Secure and Ivanti Policy Secure zero-day flaws in response to widespread and active exploitation by multiple threat actors.


SecurityWeek
The number of Ivanti VPN appliances compromised through exploitation of recent flaws increases and another bug is added to exploited list.


CyberSecurity Dive
A suspected state-linked hacker is manipulating an integrity tool used to check systems as customers still await an initial patch.


The Hacker News
A critical flaw (CVE-2023-35082) in Ivanti EPMM is being exploited in the wild, giving attackers access to your data.


The Record
CISA warned that two bugs in Ivanti products are allowing hackers “to move laterally, perform data exfiltration, and establish persistent system access, resulting in full compromise of target information systems.”


SC Magazine
Ivanti reported that it believes malicious code has been added to exploited Connect-Secure and Policy Secure products that allows a threat actor future access, even after mitigation is applied.


CyberSecurity Dive
Researchers warn additional threat actors are actively working to take advantage of two chained together vulnerabilities.


DarkReading
Anyone who hasn't mitigated two zero-day security bugs in Ivanti VPNs may already be compromised by a Chinese nation-state actor.


HACKRead
The vulnerabilities in Ivanti VPN devices enable remote, unauthenticated hackers to compromise targeted devices, execute arbitrary commands, infiltrate internal networks, and steal sensitive data.


Latest Hacking News
Ivanti has warned users of two zero-day vulnerabilities in its Connect Secure and Policy Secure gateways that have already attracted hackers’ attention. The firm confirmed active exploitation of the flaws to target a small number

Security Affairs
Experts warn that recently disclosed Ivanti Connect Secure VPN and Policy Secure vulnerabilities are massively exploited in the wild.


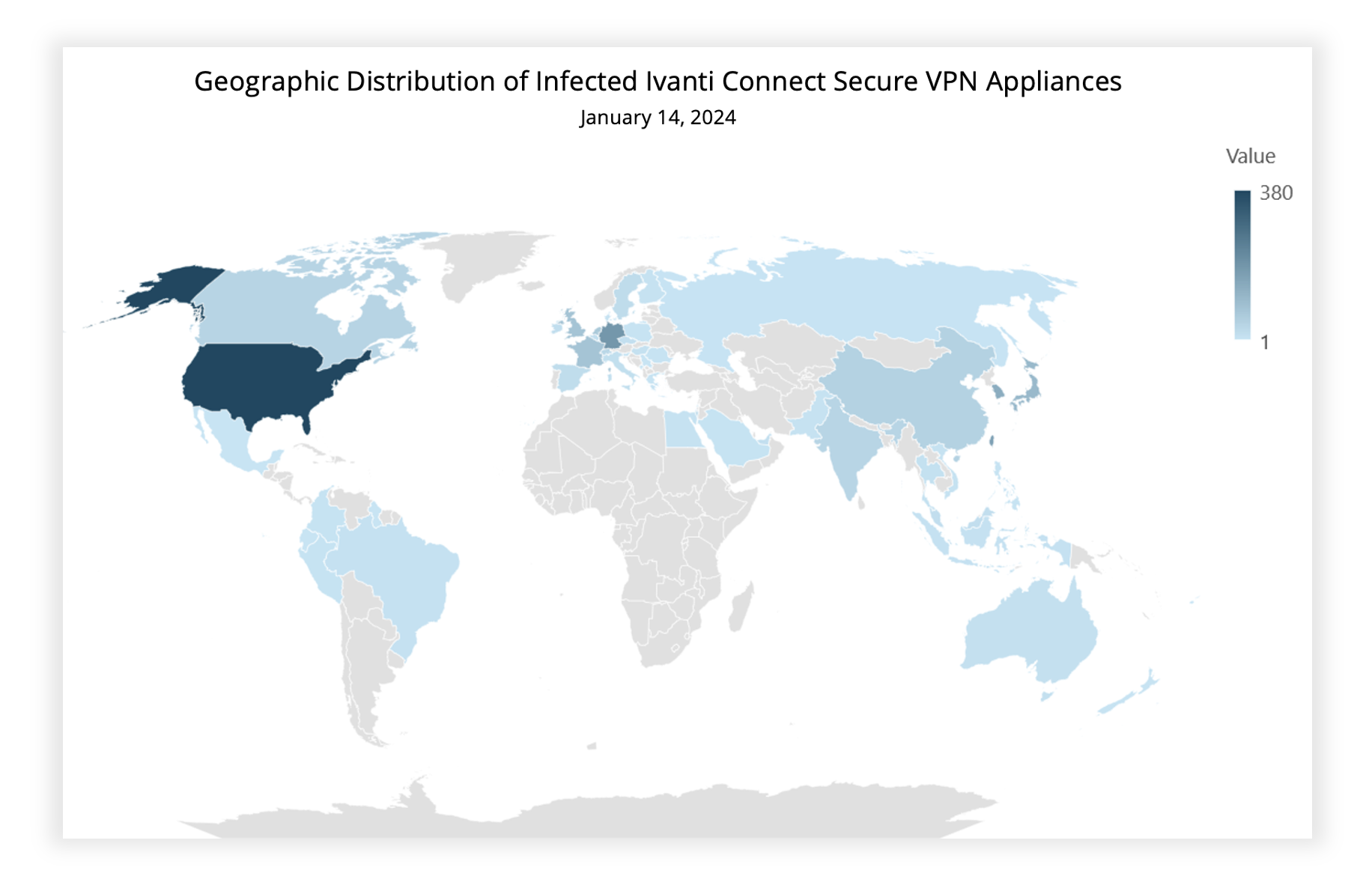
Infosecurity News
Volexity detects 1700 compromised Ivanti VPN devices following publication of two zero-days last week


SecurityWeek
Ivanti VPN zero-days have been exploited to hack at least 1,700 devices, including government, telecoms, defense, and tech.


Bleeping Computer
Two zero-day vulnerabilities affecting Ivanti's Connect Secure VPN and Policy Secure network access control (NAC) appliances are now under mass exploitation.


The Record
IT company Ivanti continues to respond to exploitation of vulnerabilities in its Connect Secure VPN product. Researchers at Volexity began to size up the damage over the weekend.


Bleeping Computer
Hackers have been exploiting the two zero-day vulnerabilities in Ivanti Connect Secure disclosed this week since early December to deploy multiple families of custom malware for espionage purposes.


The Hacker News
Nation-state hackers weaponizing Ivanti Connect Secure VPN zero-days to deploy five malware families in a targeted cyber espionage campaign.


CyberSecurity Dive
Researchers warn the previously unknown actor has developed custom malware designed to maintain persistent access on targeted networks and evade detection.


SecurityWeek
Ivanti zero-day vulnerabilities dubbed ConnectAround could impact thousands of systems and cyberspies are preparing for patch release.


CyberNews
Ivanti software bugs exploited by China hackers.


DarkReading
Patches will be available in late January and February, but until then, customers must take mitigation measures.


PCMag
Ivanti is working to roll out an official fix for the critical flaws later this month.


Security Affairs
US CISA adds Ivanti Connect Secure and Microsoft SharePoint bugs to its Known Exploited Vulnerabilities catalog

Security Affairs
Ivanti revealed that two threat actors are exploiting two zero-day vulnerabilities in its Connect Secure (ICS) and Policy Secure.
Loading more articles....