

CyberNews
One-fifth of Docker Hub repositories are malicious, researchers find
Nearly three million repositories on Docker Hub, a platform for web developers to collaborate on their code for web applications, contain malicious content.


CyberNews
Nearly three million repositories on Docker Hub, a platform for web developers to collaborate on their code for web applications, contain malicious content.


Cyber Security News
Repositories on Docker Hub, a popular platform for developers to store and share containerized applications, have been exploited to spread malicious software and phishing scams.


DarkReading
The purported metadata for each these containers had embedded links to malicious files.


Bleeping Computer
Three large-scale campaigns have targeted Docker Hub users, planting millions of repositories designed to push malware and phishing sites since early 2021.


SecurityWeek
JFrog raises an alarm after finding three large-scale malware campaigns targeting Docker Hub with imageless repositories.

Infosecurity News
According to JFrog, approximately 25% of all repositories lack useful functionality and serve as vehicles for spam and malware


The Hacker News
Millions of malicious "imageless" containers have been planted on Docker Hub over the past 5 years in multiple cybercriminal campaigns.


CyberNews
How AI and ML models can increase software supply chain risks and lead to cybersecurity incidents


DarkReading
Project behind the Rust programming language asserted that any calls to a specific API would be made safe, even with unsafe inputs, but security researchers found ways to circumvent the protections.


CyberSecurity Dive
Security researchers are raising questions about whether the actor behind an attempted supply chain attack was engaged in a random, solo endeavor.


Infosecurity News
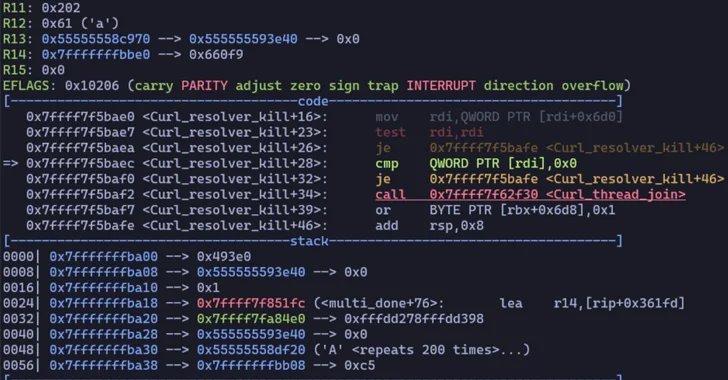
A backdoor in XZ Utils, a widely used file-compressing software in Linux systems, could have led to a critical supply chain attack had a Microsoft researcher not spotted it in time


The Hacker News
Popular Linux compression tool XZ Utils found with backdoor. Threat actors can remotely execute code on your machine, bypassing authentication.


DarkReading
Had a researcher not spotted the malware when he did, the outcome could have been much worse.


CyberSecurity Dive
As the AI ecosystem grows and more tools connect to internal data, threat actors have a wider field to introduce vulnerabilities.


The Hacker News
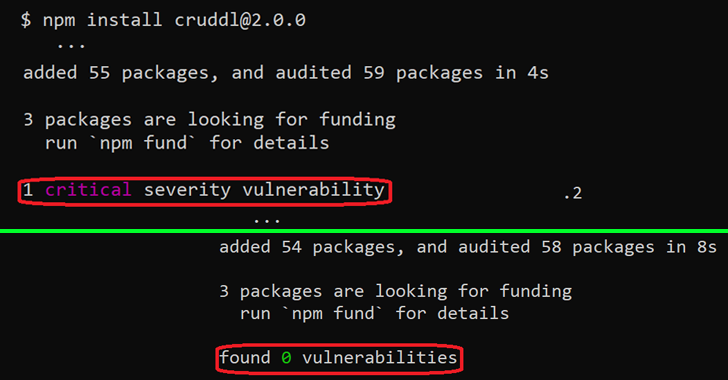
New report reveals 800+ packages in the npm registry contain hidden code discrepancies.


DarkReading
Machine-learning platforms like Hugging Face are suspectible to the same kind of attacks that threat actors have executed successfully for years via npm, PyPI, and other open source repos.


The Hacker News
Over 100 AI/ML models discovered with malicious intent on the Hugging Face platform. The cyber realm faces a new threat.


Ars Technica
Malicious submissions have been a fact of life for code repositories. AI is no different.


DarkReading
The finding underscores the growing risk of weaponizing publicly available AI models and the need for better security to combat the looming threat.


Bleeping Computer
At least 100 instances of malicious AI ML models were found on the Hugging Face platform, some of which can execute code on the victim's machine, giving attackers a persistent backdoor.


SecurityWeek
Supply chain security: A successful attack against a supplier can lead to multiple opportunities against the supplier’s downstream customers

DarkReading
However, not everyone agrees with the NVD's assessment of CVE-2023-40547 being a near-maximum severity bug.


The Hacker News
Malicious code hiding in seemingly innocent PyPI packages steals your passwords, crypto & more


Security Affairs
Multiple proof-of-concept (PoC) exploits for recently disclosed critical Jenkins vulnerability CVE-2024-23897 have been released.


The Hacker News
Researchers uncover a critical SSH protocol vulnerability, "Terrapin" (CVE-2023-48795), allowing attackers to compromise secure connections.


The Hacker News
Malicious NuGet package distributing SeroXen RAT targets .NET developers.

The Hacker News
Security Advisory : Two major security flaws in the Curl data transfer library exposed.


CSO
ML model management capabilities manage the organization’s local and open source ML models and ensure the security of those models through SDLC.


Infosecurity News
Tracked as CVE-2023-34034, the flaw has a CVSS score of 9.8


CSO
JFrog Curation vets and blocks infected open source or third-party packages before they enter development.

CSO
Shadow IT or careless configuration of container and artifact registries could give attackers access to sensitive data and inject malicious code.


DarkReading
Researchers find 250 million artifacts and 65,000 container images exposed in registries and repositories scattered across the Internet.


The Hacker News
Cybersecurity researchers have uncovered a sophisticated typosquatting campaign that deployed cryptocurrency stealer malware via 13 malicious NuGet.


The Hacker News
NuGet Repository under attack! New malicious campaign aims to infect #DotNET developer systems with cryptocurrency stealer malware.


Cyber Security News
There is a concerning trend among cybercriminals targeting individuals working with the .NET framework using a sneaky tactic called typosquatting.

Bleeping Computer
Threat actors are targeting and infecting .NET developers with cryptocurrency stealers delivered through the NuGet repository and impersonating multiple legitimate packages via typosquatting.


CSO
A rogue packet on the machine learning framework allowed the attacker to exfiltrate data, including SSH keys.


The Hacker News
PyTorch, a well-known machine learning framework, fell victim to a supply chain attack between Dec. 25 and Dec. 30, 2022

The Hacker News
An "unexpected behavior" in the npm command line interface could allow malicious NPM libraries to bypass security checks and hide vulnerabilities.


DarkReading
Experts say CVE-2022-42899 is a serious vulnerability, but widespread exploitation is unlikely because of the specific conditions that need to exist for it to happen.


Infosecurity News
The group focuses on utilizing open-source software for malicious purposes

DarkReading
The group has been operating for over a year, promoting their tools in hacking forums, stealing credit card information, and using typosquatting techniques to target open source software flaws.


Bleeping Computer
A threat group using the name 'LofyGang', operating since 2020, is considered responsible for creating and distributing over 200 malicious packages on multiple code hosting platforms, including GitHub and NPM.


The Hacker News
A hacker group called LofyGang distributed nearly 200 trojanized packages on the NPM open source repository that steals credit card information.

SecurityWeek
The non-profit Rust Foundation has scored funding to build a dedicated security team to proactively address security defects in the popular Rust programming language.

SecurityWeek
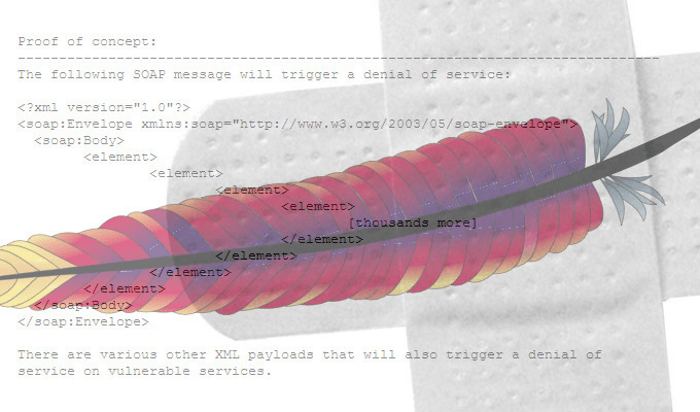
JFrog has disclosed the details of several DoS and remote code execution vulnerabilities affecting OPC UA, including flaws exploited at an ICS hacking competition.


Security Affairs
10 packages have been removed from the Python Package Index (PyPI) because they were found harvesting data. Check Point researchers have discovered ten malicious packages on the Python Package Index (PyPI). The packages install info-stealers that allow threat actors to steal the private data and personal credentials of the developers. The researchers provide details about […]


Infosecurity News
Some of these packages were capable of stealing user credentials and environment variables


ThreatPost
Recent LofyLife campaign steals tokens and infects client files to monitor various user actions, such as log-ins, password changes and payment methods.


CSO
GitGuardian says its new open-source canary tokens project helps businesses detect breaches as they unfold.


Security Affairs
Researchers disclosed a remote code execution vulnerability, tracked as CVE-2022-25845, in the popular Fastjson library. Cybersecurity researchers from JFrog disclosed details of a now patched high-severity security vulnerability in the popular Fastjson library that could be potentially exploited to achieve remote code execution. Fastjson is a Java library that can be used to convert Java Objects into their JSON representation. […]


CSO
Mend, formerly WhiteSource, announces new service designed to detect and fix code security issues, reduce the software attack surface and application security burden.

The Hacker News
Two trojanized Python and PHP packages, "ctx" and "phpass," have been uncovered in another instance of a software supply chain attack.


DarkReading
The PyPI "pymafka" package is the latest example of growing attacker interest in abusing widely used open source software repositories.


ZDNet
Open-source software supply chain security is now a vital issue of national security.


The Record
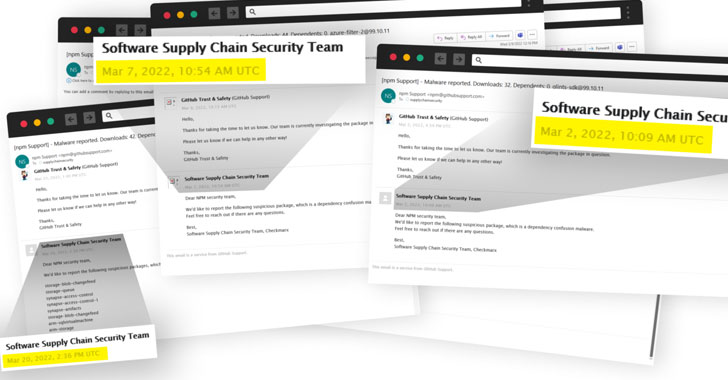
Pentersters working for a threat intelligence firm are facing backlash after several researchers were fooled into thinking an npm supply chain attack on German companies was a legitimate hack.


Ars Technica
Dependency confusion attacks exploit our trust in public code repositories.


The Hacker News
Researchers uncover a new NPM supply-chain attack campaign in which attackers distribute malicious packages to compromise leading German companies.

ZDNet
Docker is finally bringing its container development and deployment tool, Docker Desktop, to Linux.

SecurityWeek
For providers of DevSecOps services and solutions, the focus should be on removing friction from integrating security and helping teams come together to make security everyone’s responsibility.


CSO
More tools to identify vulnerable applications and options to mitigate the risk from Spring4Shell are also now available.


DarkReading
Internet scan indicates hundreds of thousands of vulnerable installations, while data from the major Java repository suggests millions, firms say.

CSO
Users are urged to update both the Spring Framework and Spring Boot tool.

The Hacker News
Researchers uncover an ongoing large-scale supply-chain attack which exploits dependency confusion attacks against the NPM package repository.

ZDNet
Over 600 malicious packages were published in only five days.


ThreatPost
A large-scale, automated typosquatting attack saw 200+ malicious packages flood the npm code repository, targeting popular Azure scopes.


CyberNews
Extortion gangs continue to wreak havoc with the ever-expanding ecosystem and ballooning ransom demands.


CyberNews
Over 200 hundred malicious NPM packages were crafted to steal developers’ PII.


ZDNet
Typosquatting and automatic tools are the weapons of choice.


The Hacker News
Researchers identified over 200 malicious NPM packages distributed through official repositories that targeted Azure developers.


ZDNet
From ethical concerns, a desire for more money, and simple obnoxiousness, a handful of developers are ruining open-source for everyone.


The Hacker News
Multiple high-severity vulnerabilities uncovered in widely used open-source ClickHouse OLAP Database Management System (DBMS) for Big Data.


Cyber Security News
The PJSIP open-source library is one of the most used libraries which is used by WhatsApp and several other VoIP applications. But, recently, several critical RCE flaws have been detected in PJSIP open source library.

SecurityWeek
OpenSSF announces that 19 more organizations have joined the initiative, which now has a total of 60 members.

The Hacker News
Critical Bugs Reported in Popular Open Source PJSIP SIP and Media Stack

ThreatPost
Three of the vulnerabilities can lead to remote-code execution if successfully exploited, and the other two are DoS vulnerabilities.


ZDNet
Trojan packages reveal what could be internal rivalry between cybercriminals.


The Hacker News
A new batch of malicious JavaScript libraries has been found in NPM's package repository.


ZDNet
JFrog's Security Research found a remote code execution vulnerability in Apache Cassandra.

ThreatPost
On the plus side, only instances with non-standard not recommended configurations are vulnerable. On the downside, those configurations aren't easy to track down, and it's easy as pie to exploit.


Security Affairs
Researchers disclose a now-patched remote code execution (RCE) vulnerability in the Apache Cassandra database software. JFrog researchers publicly disclosed details of a now-patched high-severity security vulnerability (CVE-2021-44521) in Apache Cassandra database software that could be exploited by remote attackers to achieve code execution on affected installations. Apache Cassandra is an open-source NoSQL distributed database used […]

SecurityWeek
Researchers have published full technical details on a high-severity remote code execution vulnerability addressed in the latest version of Apache Cassandra.


The Hacker News
A new high-severity remote code execution vulnerability (CVE-2021-44521) has been reported in Apache Cassandra NoSQL database software.

SecurityWeek
2021 was a record year for cybersecurity M&A and financing activity, according to financial advisory firm Momentum Cyber.


ZDNet
JavaScript developer Marak Squires wasn't happy about not making money from his open-source libraries, so he deliberately corrupted them, leaving programmers and end-users with dead-in-the-water programs.


ZDNet
The vulnerability is present in software licensed to multiple router vendors.


ThreatPost
Critical flaw in the H2 open-source Java SQL database are similar to the Log4J vulnerability, but do not pose a widespread threat.


ZDNet
JFrog's senior director of security research said the vulnerability has a root cause similar to Log4Shell.


ZDNet
A new analysis shows why the Log4j flaw for Java web applications will haunt tech people for years.


ZDNet
JFrog researchers found 17 malicious packages in the npm repository that intentionally seek to attack and steal a user's Discord tokens.


ThreatPost
The lurking code-bombs lift Discord tokens from users of any applications that pulled the packages into their code bases.


The Record
The Node Package Manager (npm) security team has removed 17 JavaScript libraries this week that contained malicious code to collect and steal Discord access tokens and environment variables from users' computers.


Bleeping Computer
High-severity and critical vulnerabilities collectively referred to as INFRA:HALT are affecting all versions of NicheStack below 4.3, a proprietary TCP/IP stack used by at least 200 industrial automation vendors, many in the leading segment of the market.

Bleeping Computer
The Python Package Index (PyPI) registry has removed several Python packages this week aimed at stealing users' credit card numbers, Discord tokens, and granting arbitrary code execution capabilities to attackers. These malicious packages were downloaded over 30,000 times according to the researchers who caught them.