

CSO
US AI experts targeted in cyberespionage campaign using SugarGh0st RAT
Threat actors use phishing techniques to obtain non-public information about generative artificial intelligence.


CSO
Threat actors use phishing techniques to obtain non-public information about generative artificial intelligence.


DarkReading
Researchers believe the attacker is likely China-affiliated, since a previous version of the malware was used by a China nation-state attack group.


Security Affairs
Google released security updates to address a new actively exploited Chrome zero-day vulnerability, the third in a week.


DarkReading
Google has rolled an emergency patch for CVE-2024-4947, the third Chrome zero-day it's addressed in the past week.


SecurityWeek
Google releases Chrome 125 to the stable channel with patches for nine vulnerabilities, including a zero-day.


Cyber Security News
Google has released update for its Chrome to patch a high-severity vulnerability that is being actively exploited by attackers in the wild.


The Hacker News
Google fixes critical zero-day vulnerability in Chrome. CVE-2024-4947, a type confusion bug in the V8 JavaScript engine, has been actively exploited b


Bleeping Computer
Google has released a new emergency Chrome security update to address the third zero-day vulnerability exploited in attacks within a week.


Bleeping Computer
Google has released a new emergency Chrome security update to address the third zero-day vulnerability exploited in attacks within a week.


The Cyber Express
A new Google Chrome vulnerability has been uncovered and exploited, marking the sixth zero-day incident in 2024 alone. In response,


Bleeping Computer
Today is Microsoft's May 2024 Patch Tuesday, which includes security updates for 61 flaws and three actively exploited or publicly disclosed zero days.


DarkReading
Exploit code is circulating for CVE-2024-4761, disclosed less than a week after a similar security vulnerability was disclosed as being used in the wild.


The Hacker News
Google has released emergency fixes for a new zero-day vulnerability (CVE-2024-4761) that has been actively exploited in the wild.


SecurityWeek
Google has patched CVE-2024-4761, the second exploited vulnerability addressed by the company within one week.


Security Affairs
Google released emergency security updates to address an actively exploited Chrome zero-day vulnerability.


Bleeping Computer
Google has released emergency security updates for the Chrome browser to address a high-severity zero-day vulnerability tagged as exploited in attacks.


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.

.png)
Cyber Security News
Staying informed is the key in this dynamic battle of cybersecurity, and due to this, the weekly news recap provides you with the newest trends, weaknesses, infringements found, and some possible defense mechanisms.


CSO
Details of the use-after-free memory vulnerability were not publicly released, but Google says it’s aware an exploit for the bug exists.


Security Affairs
Since the start of the year, Google released an update to fix the fifth actively exploited zero-day vulnerability in the Chrome browser.


The Hacker News
Google has just released an update to patch a new zero-day flaw, CVE-2024-4671, which hackers are actively exploiting in the wild.


Bleeping Computer
Google has released a security update for the Chrome browser to fix the fifth zero-day vulnerability exploited in the wild since the start of the year.

Cyber Security News
There is a vulnerability in Chrome's Visuals component that is being tracked as CVE-2024-4671. The flaw is related to the use-after-free issue and can potentially lead to remote code execution.


HACKRead
WordPress websites are under attack with a surge of malicious JavaScript being injected using vulnerable versions of the LiteSpeed Cache plugin.


Cyber Security News
WordPress plugins make WordPress more useful, but most of these have flaws that hackers may try to take advantage of to get unauthorized


The Hacker News
A critical flaw in the hugely popular LiteSpeed Cache plugin for WordPress is being exploited in the wild to create rogue admin accounts, granting att


Bleeping Computer
Hackers have been targeting WordPress sites with an outdated version of the LiteSpeed Cache plugin to create administrator users and gain control of the websites.


The Hacker News
Learn how Reflectiz detected a sophisticated malware hidden in an innocent-looking image on a retail site.

%20(1).webp)
Cyber Security News
Critical vulnerabilities in MailCleaner versions before 2023.03.14 allow attackers to take control of appliances through malicious emails

Ars Technica
Easy-to-use language that drove Apple, TRS-80, IBM, and Commodore PCs debuted in 1964.


Bleeping Computer
Latrodectus malware is now being distributed in phishing campaigns using Microsoft Azure and Cloudflare lures to appear legitimate while making it harder for email security platforms to detect the emails as malicious.


The Hacker News
Millions of malicious "imageless" containers have been planted on Docker Hub over the past 5 years in multiple cybercriminal campaigns.


Infosecurity News
The top malicious domains attracted over 100,000 hits each, according to Akamai Security


Cyber Security News
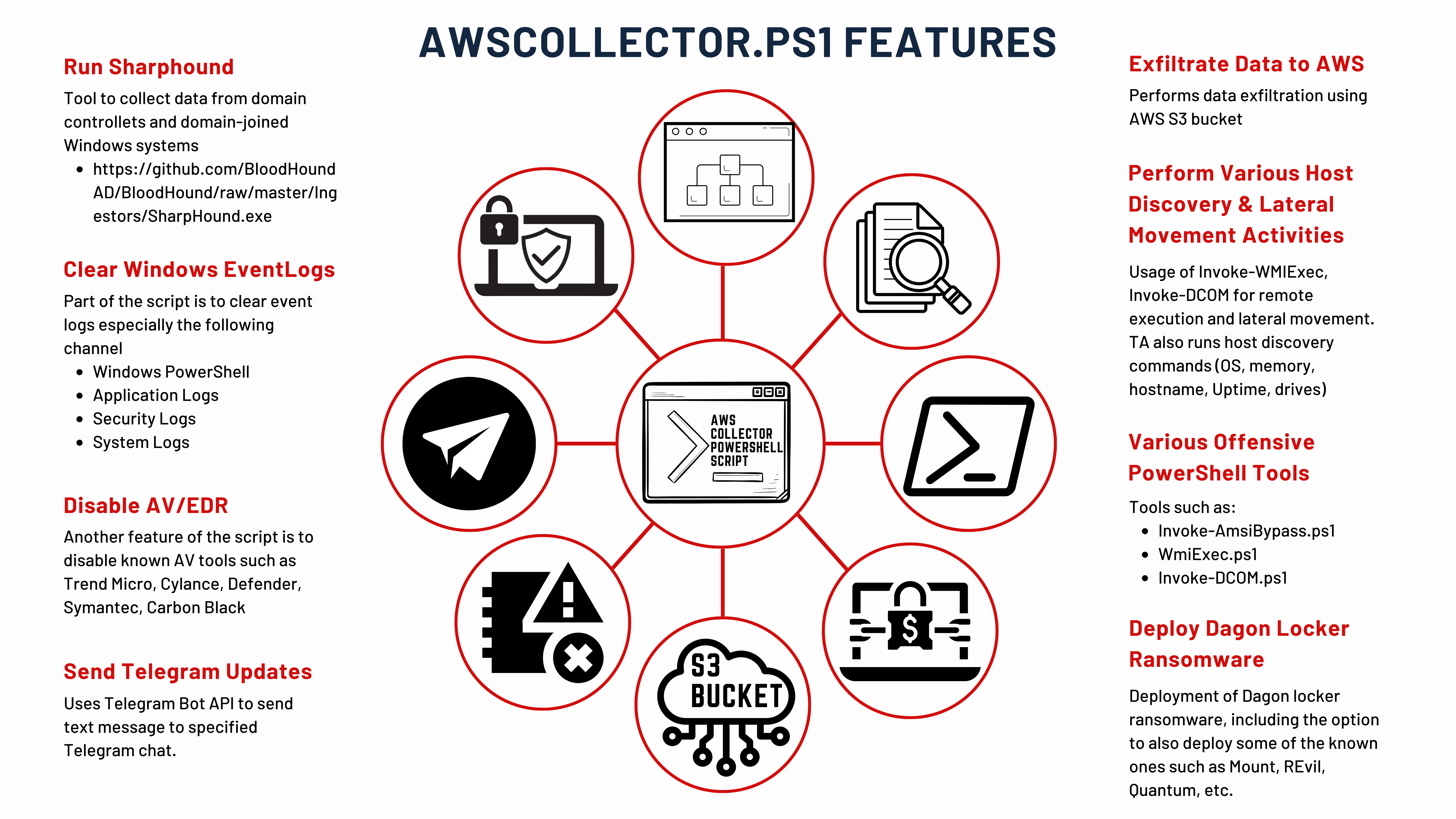
In a sophisticated cyberattack that unfolded over 29 days, cybersecurity analysts have meticulously traced the steps of threat actors from the initial infection with IcedID malware to the eventual deployment of Dagon Locker ransomware. The detailed account of this cyber intrusion provides a chilling example of how quickly and stealthily cybercriminals can compromise an organization’s […]


Cyber Security News
A new vulnerability has been discovered in Telegram which allows a threat actor to hijack a Telegram user session via XSS

The DFIR Report
Key Takeaways In August 2023, we observed an intrusion that started with a phishing campaign using PrometheusTDS to distribute IcedID. IcedID dropped and executed a Cobalt Strike beacon, which was … Read More


SC Magazine
A look back at the Heartbleed bug and measuring its’ legacy, impact and how some view one of cybersecurity’s biggest headaches as an important learning moment.


Bleeping Computer
Security researchers analyzing phishing campaigns that target United States Postal Service (USPS) saw that the traffic to the fake domains is typically similar to what the legitimate site records and it is even higher during holidays.


Cyber Security News
Welcome to this week's edition of the Cyber Security News Weekly Round-Up. This issue covers the latest vulnerabilities, cyber attacks, and emerging threats that have been making headlines. Stay informed and stay secure!

Security Affairs
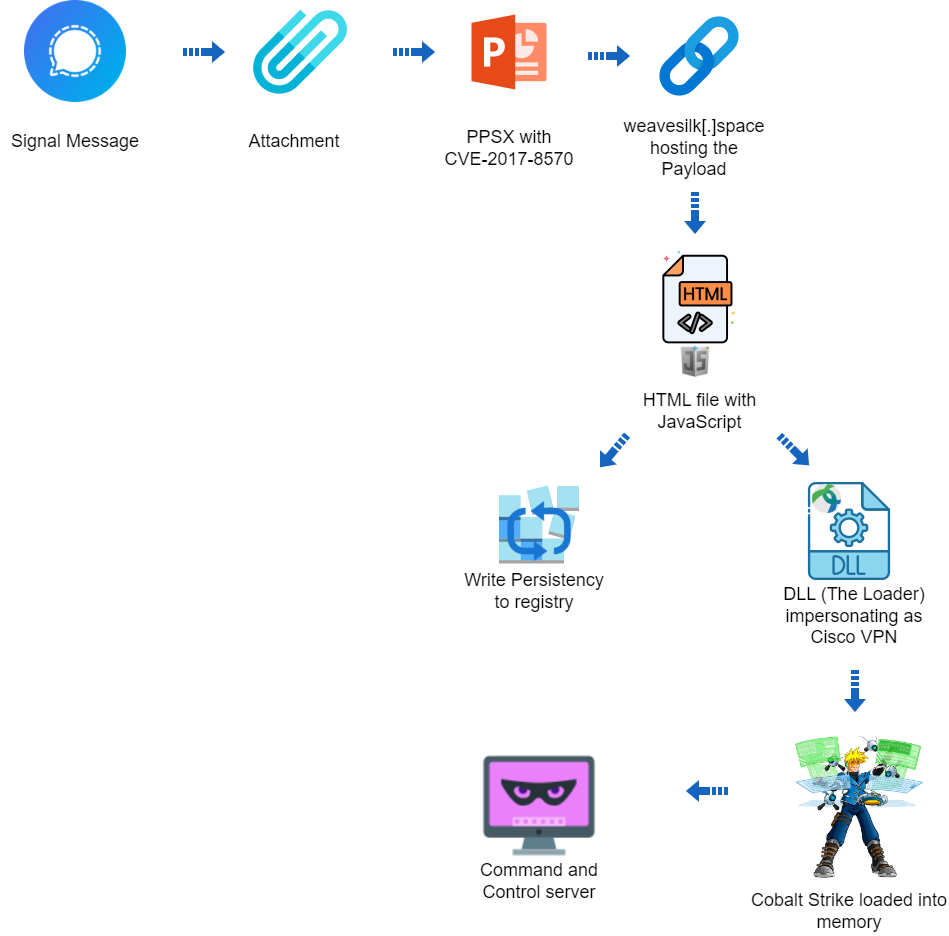
A hacking campaign targeted Ukraine exploiting a seven-year-old vulnerability in Microsoft Office to deliver Cobalt Strike.


The Hacker News
Cybersecurity researchers have uncovered a targeted cyber attack against Ukraine that leveraged a 7-year-old Microsoft Office flaw to deploy Cobalt St


The Hacker News
Hackers are disguising Python backdoors as legitimate npm packages to target developers during fake job interviews.


Bleeping Computer
A new campaign tracked as "Dev Popper" is targeting software developers with fake job interviews in an attempt to trick them into installing a Python remote access trojan (RAT).


Security Affairs
U.S. CISA added the Windows Print Spooler flaw CVE-2022-38028 to its Known Exploited Vulnerabilities catalog.


HACKRead
A critical vulnerability (CVE-2024-4058) has been patched in the latest update (version 124). This flaw could allow attackers to take control of your system.


DarkReading
Unlike the SolarWinds and CodeCov incidents, all that it took for an adversary to nearly pull off a massive supply chain attack was some slick social engineering and a string of pressure emails.


The Hacker News
A sophisticated attack campaign dubbed "FROZEN#SHADOW" is underway, using phishing emails to infect systems with the stealthy malware SSLoad.


Cyber Security News
A significant vulnerability was detected in IBM QRadar Suite Software and Cloud Pak for Security that allows attackers to execute arbitrary


SecurityWeek
Google patches CVE-2024-4058, a critical Chrome vulnerability for which researchers earned a $16,000 reward.


HACKRead
Microsoft issued a security warning about a vulnerability (CVE-2022-38028) in the Windows Print Spooler service that Russian APT28 are exploiting.


SecurityWeek
CISA warns organizations of a two-year-old Windows Print Spooler vulnerability being exploited in the wild.


CyberSecurity Dive
State-linked actors are using a custom tool for post exploitation activity of a vulnerability in Windows Print Spooler, which could result in credential theft and backdoor installs.


The Hacker News
A suspected Vietnamese hacking group is leveraging CDN cache to distribute malware undetected.


CyberNews
Microsoft identifies the 'GooseEgg' tool created by Russian threat group APT 28, Forrest Blizzard to exploit known vulnerabilities in Windows printer spooler service.


SC Magazine
Security pros say there’s a high potential that attackers could launch arbitrary code execution.


SC Magazine
A new CryptBot variant targets password managers and authentication apps in the new campaign.


Bleeping Computer
A threat actor has been using a content delivery network cache to store information-stealing malware in an ongoing campaign targeting systems U.S., the U.K., Germany, and Japan.


Infosecurity News
Microsoft has warned of a long-running credential stealing campaign from Russia’s APT28


Cyber Security News
Hackers abuse Windows Print Spooler vulnerabilities because it runs with elevated SYSTEM privileges which allows privilege escalation.


The Hacker News
Hackers linked to Russia have been exploiting a Windows bug for YEARS to deploy GooseEgg malware for escalating attack access.


SC Magazine
Microsoft says the launcher application is unique to Russia’s APT28 threat group and can lead to remote code execution.


Security Affairs
Russia-linked APT28 group used a previously unknown tool, dubbed GooseEgg, to exploit Windows Print Spooler service flaw.

Krebs on Security
The head of counterintelligence for a division of the Russian Federal Security Service (FSB) was sentenced last week to nine years in a penal colony for accepting a USD $1.7 million bribe to ignore the activities of a prolific Russian…


SecurityWeek
OpenSSF and OpenJS incidents similar to XZ backdoor, Moldovan botnet operator charged, US automotive company targeted by FIN7.


Infosecurity News
Zscaler also confirmed MadMxShell uses DLL sideloading and DNS tunneling for C2 communication


The Hacker News
Ever worried about malware in PDFs? ANY.RUN's sandbox can expose hidden threats just by analyzing the file's structure.

.webp)
Cyber Security News
Security researchers uncovered a sophisticated malvertising campaign targeting IT professionals, particularly those in security.


The Hacker News
Hackers are using fake domains of popular IP scanners like Advanced IP Scanner & ManageEngine in a Google Ads malvertising scheme to spread malware.

.webp)
Cyber Security News
Attackers tried to take over the JavaScript project from OpenJS Foundation, which is home to JavaScript projects utilized by billions of


SecurityWeek
Chrome and Firefox security updates resolve over 35 vulnerabilities, including a dozen high-severity bugs.


The Hacker News
Security researchers uncover a "credible" takeover attempt on the OpenJS Foundation, mirroring a recent incident with XZ Utils.


HACKRead
The OpenSSF issued alerts for social engineering takeovers of open-source projects after hackers tried to gain control of an OpenJS-hosted project.


CyberSecurity Dive
Federal officials are said to be investigating potential links between the recent XZ Utils campaign and new threat activity against JavaScript project maintainers.


Infosecurity News
Two open source organizations have revealed attempts to socially engineer project takeovers

Cyber Security News
we’ll dissect a timely example of credential theft—StrelaStealer—to identify the malware’s characteristics and capabilities.


CyberSecurity Dive
The attempted malicious backdoor may have been part of a wider campaign using social engineering techniques, the open source community warned.


The Record
The thwarted social engineering attempts highlight the urgent need to address weaknesses in the management of open source software.


Cyber Security News
The weekly cybersecurity news wrap-up provides readers with the latest information on emerging risks, vulnerabilities, ways to reduce them, and harmful schemes to help make defensive measures proactive.


The Hacker News
E-commerce website owners and admins – BEWARE! Reseachers uncover a credit card skimmer hidden within a bogus Meta Pixel tracker script.


SecurityWeek
Google releases a Chrome 123 update to resolve three high-severity memory safety vulnerabilities worth $41,000.

The Hacker News
TA547 hacker group adopts new tactics, possibly harnessing the power of generative AI, to deploy the Rhadamanthys info stealer in attacks on German or


Security Affairs
Apple is warning iPhone users in over 90 countries of targeted mercenary spyware attacks, Reuters agency reported.


CyberNews
Cybercriminals impersonating legitimate German companies are attacking organizations in the country.

Security Affairs
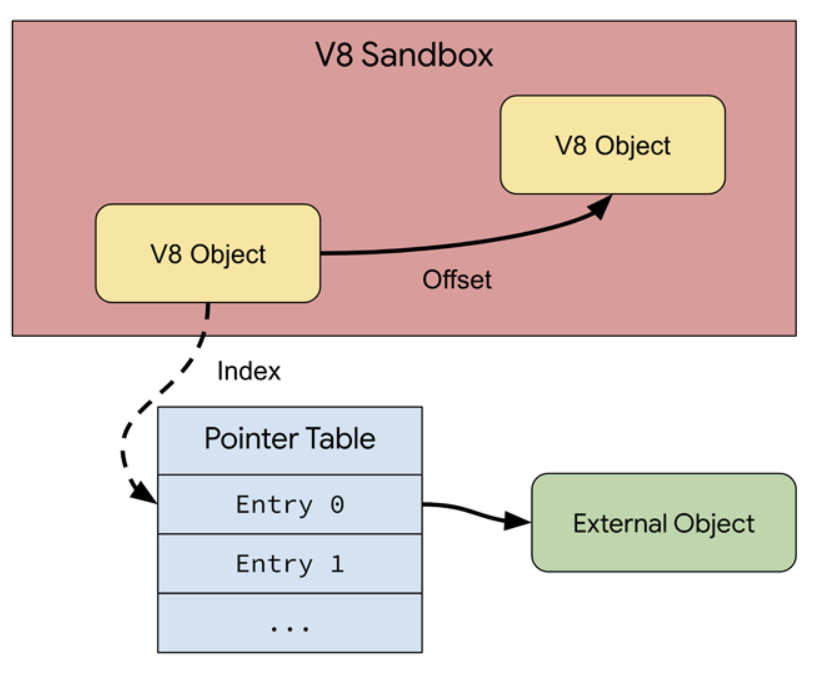
Google announced support for a V8 Sandbox in the Chrome web browser to protect users from exploits triggering memory corruption issues.


Cyber Security News
In a significant move to bolster the security of its widely-used V8 JavaScript engine, Google has unveiled the V8 Sandbox.


The Hacker News
Google tackles Chrome security with new V8 Sandbox. This aims to stop memory issues from spreading, protecting your browser experience.


The Hacker News
'Latrodectus' strikes via phishing emails. This powerful downloader can execute commands, evade detection, and pave the way for further attacks.


SecurityWeek
Google fights Chrome V8 engine memory safety bugs with a new sandbox and adds it to the bug bounty program.


DarkReading
An ongoing cyberattack with ties to China uses new version of sophisticated JSOutProx Trojan, now targeting banks in the Middle East.


Cyber Security News
GitLab is a prominent web-based Git repository manager that is exploited by hackers to gain unauthorized access to confidential source code,


The Hacker News
Financial organizations in APAC & MENA are under attack. A sophisticated threat dubbed JSOutProx combines JavaScript & .NET to infiltrate systems.

The Record
Russian authorities took the rare step of publicly identifying suspects in a cybercrime case involving credit card information.


Bleeping Computer
A relatively new malware called Latrodectus is believed to be an evolution of the IcedID loader, seen in malicious email campaigns since November 2023.


Bleeping Computer
Visa is warning about a spike in detections for a new version of the JsOutProx malware targeting financial institutions and their customers.


Infosecurity News
First found in 2019, JSOutProx combines JavaScript and .NET functionalities to infiltrate systems


Cyber Security News
Google fixed three vulnerabilities in the Chrome browser on Tuesday, along with another zero-day exploit that was exploited during the Pwn2Own


SC Magazine
Proofpoint researchers say new malware aligns with trend by cybercriminals to find more creative ways to bypass defenders.


Security Affairs
Google fixed another Chrome zero-day vulnerability exploited during the Pwn2Own hacking competition in March.


Security Affairs
Resecurity researchers warn that a new Version of JsOutProx is targeting financial institutions in APAC and MENA via Gitlab abuse.


Bleeping Computer
Google has fixed another zero-day vulnerability in the Chrome browser, which was exploited by security researchers during the Pwn2Own hacking contest last month.
Loading more articles....