

Ars Technica
Arizona woman accused of helping North Koreans get remote IT jobs at 300 companies
Alleged $6.8M conspiracy involved "laptop farm," identity theft, and résumé coaching.


Ars Technica
Alleged $6.8M conspiracy involved "laptop farm," identity theft, and résumé coaching.


DarkReading
Researchers believe the attacker is likely China-affiliated, since a previous version of the malware was used by a China nation-state attack group.


Bleeping Computer
Constant training is key to staying current on the changing world of cybersecurity. This instant cybersecurity training library lets you fit in the training you need for $24.97, $95 off the $120 MSRP now through the end of May 22th.


HACKRead
Shadow IT involves employees using IT systems without proper security controls, often installing unauthorized software on company computers.


The Cyber Express
Gone in 60 seconds is a thing of the past. With the world moving towards digital assets and cryptocurrency, “Gone


DarkReading
In a first-ever move, the commission's enforcement bureau has high hopes that official classification will allow law enforcement partners to better combat these kinds of threats.


SecurityWeek
Honoring my father's memory by translating his timeless life lessons into practical wisdom for the cybersecurity profession.


Cyber Security News
Best MSP for CISO, CTO & IT Managers - 1. Perimeter 812. Secureworks 3. IBM 4. Trustwave 5. Wipro 6. Verizon 7. Sophos 8. Symantec.


HACKRead
The Internet of Things (IoT) promises a world of interconnected devices, but with this connectivity comes a dark side such as security vulnerabilities.


SecurityWeek
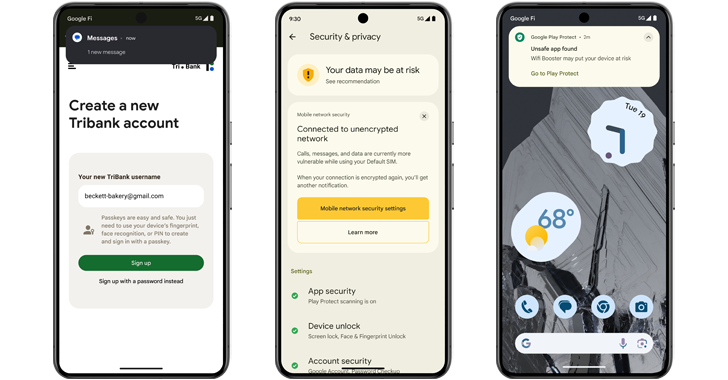
Google is boosting fraud and malware protections in Android 15 with live threat detection and expanded restricted settings.


SecurityWeek
The City of Wichita says files containing personal information were exfiltrated in a recent ransomware attack.


Cyber Security News
LogRhythm and Exabeam, two leading cybersecurity companies to create a powerful force in the security operations and analytics market.

Cyber Security News
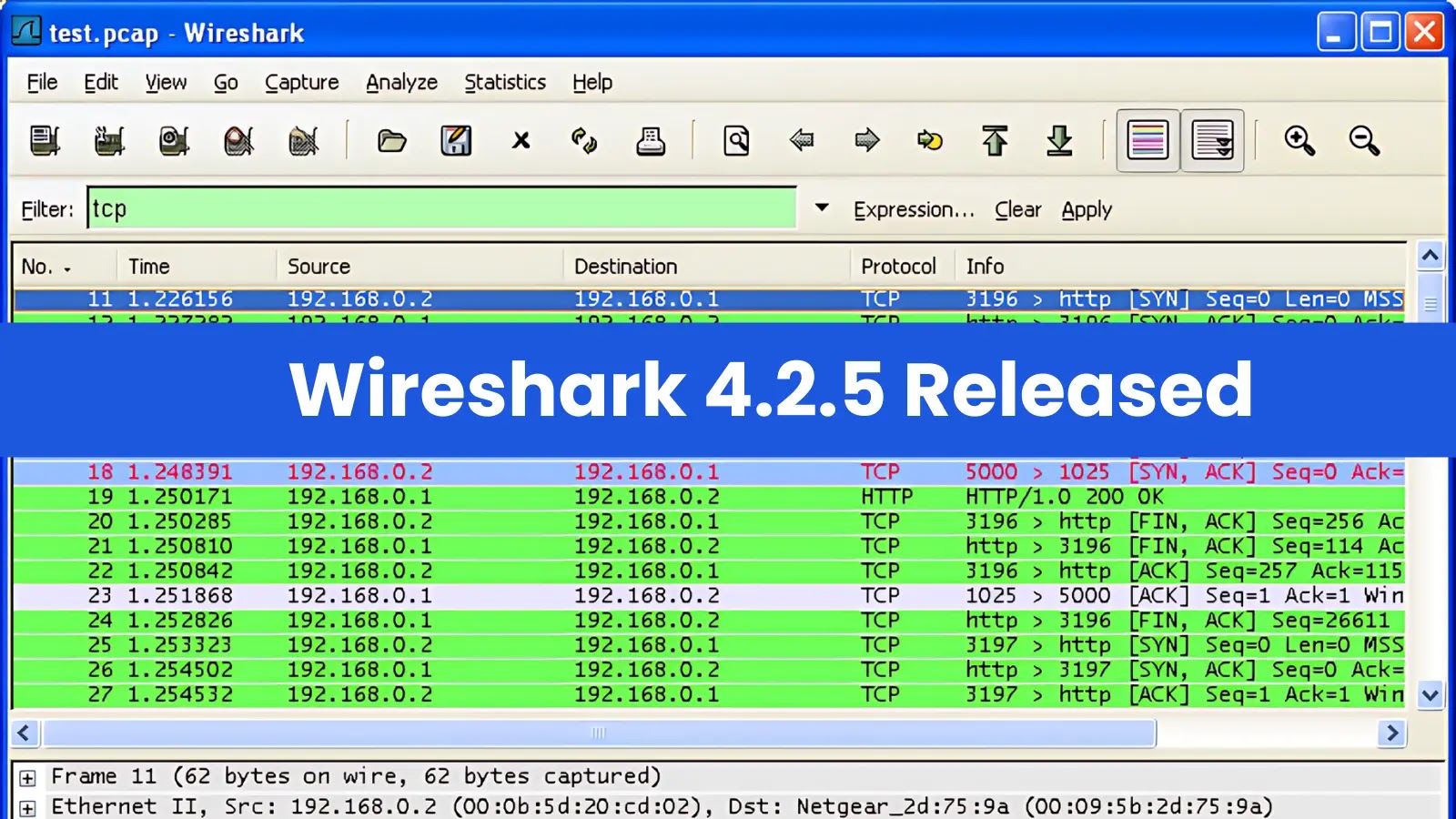
The Wireshark team has announced the release of Wireshark 4.2.5, a maintenance update to the popular network protocol analyzer.


The Cyber Express
In response to heightened cyber threats targeting political candidates, election officials and civil society groups, the National Cyber Security Centre


SecurityWeek
US officials raised concerns on China’s “misuse of AI” while Beijing’s representatives rebuked the US over “restrictions and pressure” on AI.


The Record
According to the State Department, a U.S. national named Christina Chapman helped four people fraudulently obtain work as remote software and applications developers with companies in a range of sectors and industries, earning millions of dollars for the North Korean regime.


The Record
The BGP behaves like an internet traffic controller, routing data as efficiently as possible — but it can be "hijacked" for malicious purposes.


Trend Micro
This report describes how Waterbear and Deuterbear — two of the tools in Earth Hundun's arsenal — operate, based on a campaign from 2024.


DarkReading
Cybercriminals are trafficking DocuSign assets that allow for easy extortion and business email compromise.

Bleeping Computer
Today, Google announced new security features coming to Android 15 and Google Play Protect that will help block scams, fraud, and malware apps on users' devices.

Bleeping Computer
Today, Google announced new security features coming to Android 15 and Google Play that will help block scams, fraud, and malware apps on users' devices.


Bleeping Computer
The U.S. Department of Justice has indicted two brothers for allegedly manipulating the Ethereum blockchain and stealing $25 million worth of cryptocurrency within approximately 12 seconds in a "first-of-its-kind" scheme.


Infosecurity News
Despite this setback, the auction house said bids can still be placed by phone and in-person

The Hacker News
Android 15 introduces new features to prevent malicious apps from capturing your sensitive data. Find out more about these crucial updates:


Infosecurity News
CPR said exploit builders in .NET and Python have been employed to deploy this malware


DarkReading
A vulnerability in the HNAP login request protocol that affects a family of devices gives unauthenticated users root access for command execution.


The Cyber Express
The ever-evolving landscape of cybersecurity is shaped by a dedicated group of individuals. These pioneers, through their research, entrepreneurship, and


Bleeping Computer
Banco Santander S.A. announced it suffered a data breach impacting customers after an unauthorized actor accessed a database hosted by one of its third-party service providers.


Bleeping Computer
Organizations need to detect and remove intruders quickly to prevent data loss and minimize the impact of lateral movement attacks. Learn more from Specops Software on blocking lateral movement in networks.


Infosecurity News
Google DeepMind’s SynthID can now be used to watermark AI-generated images, audio, text and video


Security Magazine
According to a cybersecurity and threat intelligence report, the U.S. was the 4th most targeted country in the world regarding phishing attacks.

The Hacker News
CVSS v4.0 evaluates vulnerabilities using a revised scoring system, emphasizing environmental and threat metrics.

SecurityWeek
Senators are recommending that Congress spend at least $32 billion over the next three years to develop AI and place safeguards around it.


Cyber Security News
Best Network Security Providers for the Healthcare Industry - 1. Perimeter 81, 2. Palo Alto Networks, 3. Fortinet, 4. Cisco, 5. Trend Micro


Cyber Security News
Alert Triage is a process of recognizing the important alerts from a huge pool of security alerts and allocating the resources accurately.


The Cyber Express
A dark web actor named DuckyMummy claimed responsibility for an alleged data breach at Frotcom International, a prominent player in


DarkReading
The nation amends its Cybersecurity Act, giving its primary cybersecurity agency more power to regulate critical infrastructure and third parties, and requiring cyber incidents be reported.


CSO
CISA advisory includes indicators of compromise and TTPs that can be used for threat hunting.


The Record
The U.K. government has warned that the accounts of political candidates and election officials are “almost certainly attractive targets for cyber actors looking to carry out espionage operations.”


The Record
In a data breach notice about the incident, which is still affecting numerous city services, the municipality said hackers copied files from its network.


The Record
“They know what they have to do,” said Sophie in’t Veld, who led the European Parliament investigation into spyware. “The problem is they don't want to do it.”


Cyber Security News
Google revealed its plans to integrate advanced generative AI capabilities into its flagship Search product. This move promises to transform the way users interact with and leverage information on the internet.


DarkReading
Scattered Spider is as active as ever, despite authorities claiming that they're close to nailing its members.


Ars Technica
AI model updates galore at Google I/O, including 2m context window, Imagen 3, Veo, and more.


Infosecurity News
The 15-year-old Ebury botnet is more active than ever, as ESET found 400,000 Linux servers compromised for cryptocurrency theft and financial gain


The Hacker News
Google has released emergency fixes for a new zero-day vulnerability (CVE-2024-4761) that has been actively exploited in the wild.


SecurityWeek
Ron Reiter was a childhood hacker in Israel and recruited into the IDF’s Unit 8200. Now he is CTO and co-founder of cybersecurity firm Sentra.


The Cyber Express
The field of Artificial Intelligence is rapidly evolving, and OpenAI's ChatGPT is a leader in this revolution. This groundbreaking large


The Hacker News
Advanced authentication: The key to addressing the weakest link in cybersecurity - human users. Learn how to fortify your organization's defenses.


The Cyber Express
This May, the heartbeat of the cybersecurity industry will resonate through Dubai, where The Cyber Express is set to host


CyberSecurity Dive
The detail and speed with which companies share information after an attack can prevent future pain. But businesses aren’t always keen on transparency.

.webp)
Cyber Security News
According to the FCC, the Royal Tiger Group and the people who work with it are a C-Communications Information Services Threat (C-CIST).


The Hacker News
pple and Google just rolled out a cross-platform feature called "Detecting Unwanted Location Trackers" (DULT) on iOS and Android to protect users.


Cyber Security News
OpenAI, which is the leading artificial intelligence research lab, recently announced its latest breakthrough in AI technology called GPT-4o.


SC Magazine
Emails from “Jenny Green” delivered LockBit Black through attached ZIP files.


The Record
State-linked hackers from Russia, China, Iran and North Korea are setting their sights set their sights on NGOs, think tanks, human rights activists and journalists, the advisory warned.


The Record
Rep. Zach Nunn arrived in Congress with arguably more cyber experience than any other new member in history. Can he fill the shoes of Rep. Mike Gallagher, the party's longtime House leader on cybersecurity issues?


Bleeping Computer
Apple has backported security patches released in March to older iPhones and iPads, fixing an iOS zero-day tagged as exploited in attacks.


Bleeping Computer
Apple has backported security patches released in March to older iPhones and iPads, fixing an iOS Kernel zero-day tagged as exploited in attacks.


Security Affairs
Apple rolled out urgent security updates to address code execution vulnerabilities in iPhones, iPads, and macOS.


DarkReading
Ransomware groups have always created problems for their victims that only they could solve. Black Basta is taking that core idea in a creative, new direction.


Ars Technica
Threat group has targeted 500 organizations. One is currently struggling to cope.


DarkReading
At least 15 television channels were interrupted in Ukraine alone, which, reportedly, is not out of the norm in this "information war."


SecurityWeek
Apple documents another zero-day flaw being exploited on older iPhones and documents security problems in macOS, iOS and iPadOS.


SecurityWeek
Envoys from the United States and China will meet in Geneva for talks about artificial intelligence, including the risks of the fast-evolving technology.

Ars Technica
GPT-4o demo shows new AI model singing a bedtime story, detecting user's facial expressions.


Bleeping Computer
Threat actors are using Domain Name System (DNS) tunneling to track when their targets open phishing emails and click on malicious links, and to scan networks for potential vulnerabilities.


CyberNews
Wales has become the first nation in the UK to join the metaverse, and the first in Europe to use this virtual platform for advertising, according to its tourism body.


CyberNews
A study on dogs in Lima, Peru, wants to find out whether IoT devices on pets can indicate seismic activity.


SecurityWeek
Weakening liberal democracies and weakening the NATO alliance are conjoined in the hybrid war that Russia is conducting against Ukraine.


CyberNews
Netflix, the largest streamier out there, has always claimed it wasn't seeking to show big sports. Now, though, it’s nearing a deal to stream NFL games on Christmas Day.


CyberSecurity Dive
The threat group has impacted more than 500 targets worldwide and the vast majority of critical infrastructure sectors. Numerous attacks have exploited vulnerabilities in ConnectWise ScreenConnect.


The Cyber Express
Just days before its highly anticipated spring art auctions, Christie's, the renowned auction house, had fallen victim to a cyberattack,


Cyber Security News
Black Basta ransomware is used by threat actors because of its powerful abilities and inconspicuous moves.

%20(2).webp)
Cyber Security News
A major mistake in setup caused Google Cloud and UniSuper to delete the financial service provider's private cloud account.


The Hacker News
Researchers found a malicious Python package called requests-darwin-lite hiding a sneaky malware.


CSO
The agency said core operations remain unaffected even as IntelBroker claimed to possess classified, law enforcement data.


The Cyber Express
This week on TCE Cyberwatch we’re covering the different data breaches and vulnerabilities faced by different companies. Along with this,


CyberSecurity Dive
Don’t fall for scare headlines about GenAI code—it offers multiple benefits—but also be aware of its limits and risks.


Krebs on Security
Last week, the United States joined the U.K. and Australia in sanctioning and charging a Russian man named Dmitry Yuryevich Khoroshev as the leader of the infamous LockBit ransomware group. LockBit's leader "LockBitSupp" claims the feds named the wrong guy,…


HACKRead
On Thursday, someone hacked into the system and switched the channels to show the Russian Victory Day parade instead of Latvian programs.


Bleeping Computer
Europol, the European Union's law enforcement agency, confirmed that its Europol Platform for Experts (EPE) portal was breached and is now investigating the incident after a threat actor claimed they stole For Official Use Only (FOUO) documents containing classified data.


Bleeping Computer
Through May 22 only, new users can get a lifetime license to Microsoft Project Pro 2021 on a single PC for $19.97 (reg. $29.99).


The Cyber Express
The ever-evolving digital landscape presents a constant challenge for businesses and individuals alike: staying secure in the face of increasingly


The Cyber Express
Treacle, a cybersecurity startup founded in 2021 by Subhasis Mukhopadhyay, Subhajit Manna, and Partha Das, has raised about 40 million


CSO
CISA’s pledge drew some big names, but the impact on software security could be limited. Meanwhile the org has extended its comment period on the CIRCIA cyberattack reporting law.


HACKRead
Researchers have discovered a novel cyberattack scheme, dubbed, LLMjacking, in which, threat actors gain access to the cloud environment.

Infosecurity News
The UK's open source AI safety evaluation platform, Inspect, is set to empower global collaboration for safer AI development

DarkReading
Kevin Mandia, CEO of Mandiant at Google Cloud, calls for watermarks as the industry braces for a barrage of mind-bending AI-generated fake audio and video.


Infosecurity News
Well-funded cybercriminals are adopting more sophisticated techniques, creating a need for defenders to stay informed about the evolving threat landscape


Bleeping Computer
Ethical hacking takes the battle to the black hats and keeps them from taking over the internet. These 18 cybersecurity training courses show you how to fight back for $39.97, $1059 off the $1098 MSRP now through 5/12.


The Hacker News
Google has just released an update to patch a new zero-day flaw, CVE-2024-4671, which hackers are actively exploiting in the wild.


The Hacker News
EDR solutions can detect threats that traditional defenses like antivirus often miss. Find out how EDR provides a deeper level of security.


The Cyber Express
In an unexpected turn of events, LockBitSupp, the administrator of the notorious LockBit ransomware group, responded publicly to the Federal


SecurityWeek
Hundreds of companies are showcasing their products and services this week at the 2024 edition of the RSA Conference in San Francisco.


CyberSecurity Dive
CISA Director Jen Easterly pointed to Microsoft’s decision to link security to executive compensation as a meaningful signal of its priorities.

.png)
Cyber Security News
AFS, a subsidiary of global professional services company Accenture, has been awarded a $789 million contract to bolster the cybersecurity.


The Cyber Express
Lenovo takes a bold step towards fortifying cybersecurity by joining the Secure by Design pledge, initiated by the US Cybersecurity


The Cyber Express
Dell has issued a warning to its customers regarding a data breach following claims by a threat actor of pilfering

Cyber Security News
Dell Technologies is investigating a data breach incident involving a company portal containing limited customer information related to purchases.
Loading more articles....