

SC Magazine
AI-generated code top cloud security concern amid 100% use rate in survey
GenAI, API and identity risks are key concerns, as well as conflicts between DevOps and SecOps.


SC Magazine
GenAI, API and identity risks are key concerns, as well as conflicts between DevOps and SecOps.

HACKRead
DNS tunneling is being used to bypass security filters by hiding malicious traffic in DNS packets, allowing hackers to steal stolen data.


Infosecurity News
Palo Alto Networks warns threat actors are using DNS tunneling techniques to probe for network vulnerabilities

Cyber Security News
Information such as financial records, customer information, and intellectual property that may be sold on the black web markets is what

The Hacker News
The cloud promises agility, but opens a Pandora's box of cyber risks if not secured properly. Understand your responsibility under the shared responsi


Bleeping Computer
Third-party data breaches are increasingly becoming a problem as the enterprise moves applications and storage to the cloud. Learn more from Outpost24 on how to reduce the risk from third-party data breaches.


SecurityWeek
Hundreds of companies are showcasing their products and services this week at the 2024 edition of the RSA Conference in San Francisco.


The Cyber Express
Data sourced from over 40 million exposures that pose high-impact risks to numerous critical business entities revealed that Active Directory


Security Magazine
An analysis of more than 40 million exposures provides a view the current exposure landscape, revealing 80% are driven by misconfigurations.


Infosecurity News
An IBM report found that most organizations are exposing themselves to security risks when implementing generative AI tools

HACKRead
The Paris 2024 Olympics, expected to attract over 1 billion viewers, are a prime target for cyber criminality due to rising online traffic.


DarkReading
Though Olympics officials appear to have better secured their digital footprint than other major sporting events have, significant risks remain for the Paris Games.


SecurityWeek
Horizon3.ai's AISaaS-based, AI-assisted penetration service allows proactive defensive action against exploitation of new vulnerabilities.


Cyber Security News
The explosion of cloud-based applications, or SaaS (Software-as-a-Service), has transformed the way businesses operate.


Cyber Security News
an AWS customer faced a staggering $1,300 bill for S3 usage, despite creating a single, empty bucket for testing purposes.

The Hacker News
Red Teaming or Exposure Management? Find out how combining these powerful approaches can fortify your cybersecurity defenses.


The Hacker News
Multiple critical vulnerabilities discovered in Brocade SANnav SAN management application, impacting all versions up to 2.3.0.


CSO
The new offering is designed to mitigate vulnerabilities and misconfigurations associated with the open authentication (OAuth) authorization framework.


Infosecurity News
This occurs when a private package fetches a similar public one, leading to exploit due to misconfigurations in package managers


The Cyber Express
By Nathan Wenzler, Chief Security Strategist, Tenable India is ranked third globally among nations facing the most severe cyber threats,


SecurityWeek
Malicious hackers are targeting SAP applications at an alarming pace, according to warnings from Onapsis and Flashpoint.


The Hacker News
GenAI isn't just hype—it's a toolbox revolutionizing how we develop software, manage emails, and create content.


The Hacker News
Ever heard of shadow admins? A single slip in settings can create 109 of them, risking your entire network's security! Learn how to prevent this.


CSO
Researcher that helped compile the knowledge base of common misconfigurations in SCCM releases scanner MisconfigurationManager.ps1.

.webp)
Cyber Security News
This acquisition is set to redefine the way enterprises protect their internal traffic, particularly in IT and OT environments.


Infosecurity News
These records belonged to Dublin-based iCabbi, a dispatch and fleet management technology provider

The Hacker News
Discover the secret tunnels hackers use to infiltrate your security defenses! Learn about Shadow Admins, Service Accounts, and more in our webinar.


CyberNews
Google is integrating generative AI into the Google Cloud to assist users across its various products and platforms – including its new Gemini-driven security platform.


Bleeping Computer
Maintaining visibility into container hosts, ensuring best practices, and conducting vulnerability assessments are necessary to ensure effective security. In this article Wazuh explores how its software can help implement best security practices for containerized environments.


Cyber Security News
GitLab is a prominent web-based Git repository manager that is exploited by hackers to gain unauthorized access to confidential source code,


SC Magazine
Security pros say threat actors could use the leaked data to run phishing attacks that would steal Home Depot corporate credentials and launch ransomware attacks.


DarkReading
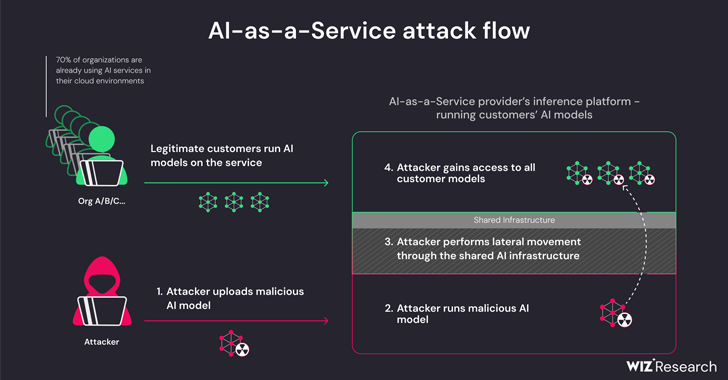
One issue would have allowed cross-tenant attacks, and another enabled access to a shared registry for container images; exploitation via an insecure Pickle file showcases emerging risks for AI-as-a-service more broadly.

The Hacker News
New research reveals critical security risks for AI-as-a-service providers like Hugging Face. Attackers could gain access to hijack models, escalate


The Hacker News
Operational Technology (OT) Cybersecurity: A Balancing Act! OT systems' unique traits demand tailored security measures. Learn why safeguarding OT req


SC Magazine
Cloud computing improves scalability and may cut costs, but network-security practitioners may have difficulty adjusting. Here are some challenges and solutions of cloud-based network security.


Trend Micro
Explore how a cybersecurity platform with attack surface management and runtime protection capabilities can enhance your cloud security posture.


The Hacker News
Tired of chasing endless vulnerabilities? Enter Continuous Threat Exposure Management (CTEM). Prioritize critical exposures, streamline remediation, a


DarkReading
A majority of enterprises that employ cloud-based email spam filtering services are potentially at risk, thanks to a rampant tendency to misconfigure them.


SecurityWeek
Los Angeles firmware and software supply chain firm banks $10.5 million in seed-stage venture capital funding led by Two Bear Capital.

%20(1)%20(1).webp)
Cyber Security News
Firstly, it is used for remote access to servers and systems at large hence a great ground for infiltration.


SC Magazine
Threat actor targets AI workloads, believed to be first exploited in the wild.

.png)
Cyber Security News
cybersecurity news will keep you posted on the latest developments, exposures, advances, occurrences, threats, and narratives in this field.


SC Magazine
Several AWS, Azure and Google Cloud domains were found to lack a key guardrail against XSS.


SC Magazine
Several AWS, Azure and Google Cloud domains were found to lack a key guardrail against XSS.


Cyber Security News
A new research has revealed that more than 900 websites had a serious misconfiguration which exposed a massive of 125 million user records


SecurityWeek
Hundreds of websites misconfigured Google Firebase, leaking more than 125 million user records, including plaintext passwords, security researchers warn. It all started with the hacking of Chattr, the AI hiring system that serves multiple organizations in the US, including fast food chains such as Applebee’s, Chick-fil-A, KFC, Subway, Taco Bell, and Wendy’s, three security researchers […]


SC Magazine
Researchers say they reported their findings to Chattr.ai on Jan. 10, then followed up with a full scan of the internet.


CSO
Researchers from SpecterOps have put together a comprehensive resource that catalogs SCCM attacks and provides defensive strategies and hardening guidance.


DarkReading
Whoopsies in Ireland and Scotland speak to a tenuousness of cyber protections for sensitive private healthcare data.


Infosecurity News
An AppOmni researcher detailed a misconfiguration in the HSE COVID Vaccination Portal, exposing the health and personal data of over a million Irish citizens


DarkReading
Misconfigurations, insecure services leave UAE organizations and critical infrastructure vulnerable to bevy of cyber threats.


Infosecurity News
Red Canary said cloud account compromise detections rose 16-fold in 2023, becoming the fourth most prevalent technique used by threat actors


CyberNews
The Health Service Executive (HSE) in Ireland accidentally exposed the private information of an estimated one million citizens in December 2021, a researcher has shared.


CSO
Google Cloud's SCC Enterprise aims to streamline response to threats and misconfigurations across IaaS platforms, including AWS and Azure.


Infosecurity News
Sysdig said the rise of the Meson Network in blockchain signals a new frontier for attackers


The Hacker News
Curious about CTEM? It’s not just a buzzword—it’s a proactive strategy to identify, prioritize, and mitigate cyber risks.


Infosecurity News
The advisory is associated with ten companion cybersecurity information sheets detailing how to implement each strategy


Cyber Security News
NSA and CISA released "Top Ten Cloud Security Mitigation Strategies" to advise cloud users on critical security practices for migrating data.


Cyber Security News
Stay updated with the most recent advancements in the cybersecurity industry with our weekly recap of cybersecurity news.


CyberNews
Online dictionary Glosbe leaks user data.


HACKRead
Cado Security Labs has discovered an emerging Linux malware campaign dubbed Spinning Yarn targeting misconfigured servers.


Cyber Security News
Best AWS Network Access Security : 1. Perimeter 81 2. Amazon Web Services (AWS) Security 3. Palo Alto Networks 4. Fortinet 5. CheckPoint.


The Hacker News
A tool intended for security, SSH-Snake, now aids attackers in exploiting networks. Discover the depths of its reach and how to safeguard your infrast


DarkReading
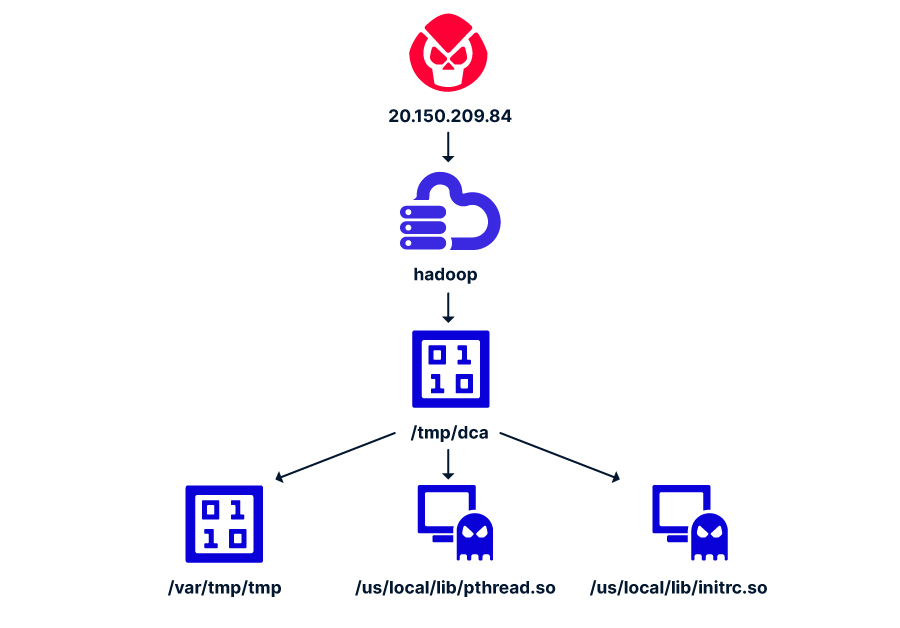
More than 3,000 unique attacks hitting Hadoop and Druid honeypots in just the past month indicate an attacker testing phase.


CSO
Abusing valid accounts became the most common entry point into victim environments in 2023.


The Hacker News
VMware has identified a critical security flaw in its Enhanced Authentication Plugin (EAP), urging users to uninstall it.


DarkReading
Enterprises typically use the Java-like programming language to customize their Salesforce instances, but attackers are hunting for vulnerabilities in the apps.


The Cyber Express
The National Cyber Security Centre (NCSC) in the UK has issued a comprehensive blog aimed at educating individuals and organizations

The Hacker News
Strengthen your SaaS security like a pro! Discover how aligning with NIST standards can fortify your applications against cyber threats.


SecurityWeek
US hacks Iranian military vessel used for spying, Rhysida ransomware free decryption tool, NIST guidance on HIPPA and supply chain security.


The Hacker News
2023's cyber attacks put SaaS vulnerabilities in the spotlight. Find out why SaaS is the new supply chain and how to safeguard your organization.


Bleeping Computer
Microsoft Teams is susceptible to a growing number of cybersecurity threats as its massive user base is an attractive target for cybercriminals. Learn more from Adaptive Shield on how to increase your Microsoft Teams security posture.


The Hacker News
Password spraying, OAuth hijacking, and nation-state attacks – the cybersecurity world is under siege. Learn how to protect your organization.


The Hacker News
Discover how Silverfort's Unified Identity Protection Platform revolutionizes Incident Response by swiftly detecting compromised accounts and bolsteri


The Cyber Express
By Ashish Tandon, Founder & CEO, Indusface In the ever-evolving landscape of digital threats and cyberattacks, the year 2024 demands

Cyber Security News
Network as a Service for MSSP : 1. Perimeter 81 2. Cloudflare 3. Prisma Cloud 4. Megaport 5. Akamai 6. Aryaka 7. Converged Cloud.


HACKRead
The cloud database belonging to Credit Union Service was left exposed without any security authentication or passwords, allowing public access.


DarkReading
How a light railway in Israel is fortifying its cybersecurity architecture amid an increase in OT network threats.


CyberNews
A misconfigured database on the LectureNotes Learning App, a platform for sharing class notes, has exposed more than two million user records.


The Hacker News
Protecting your data in the cloud is crucial. Learn how a $10B media firm achieved a 201% ROI with SaaS Security Posture Management.

HACKRead
According to the report, in 2023, 835 vulnerability reports were submitted by 93 ethical hackers, with 96 cases reported in the HackerOne repository.


The Hacker News
Cybersecurity is a continuous battle. Discover the top 6 vulnerabilities organizations should address

Bleeping Computer
Leveraging open source solutions and tools to build a cybersecurity architecture offers organizations several benefits. Learn more from Wazuh about the benefits of open source solutions.


SecurityWeek
Attackers could take over a Kubernetes cluster if access privileges are granted to all authenticated users in Google Kubernetes Engine.


The Hacker News
Cybersecurity researchers have discovered a critical loophole in Google Kubernetes Engine (GKE) that could potentially be exploited by threat actors


HACKRead
Hailing from Wilmington, Delaware BuyGoods.com boasts a user base of 3 million consumers spanning across 17 countries.


Cyber Security News
Infrastructure as Code (IaC) is a DevOps practice used for managing & provisioning IT infrastructure through code instead of Manual Process.


Trend Micro
Explore why Trend Micro is recognized—for the 18th time—as a Leader in the Gartner Magic Quadrant for Endpoint Protection Platforms.


DarkReading
Australia's Essential Eight Maturity Model still doesn't address key factors needed to protect today's cloud and SaaS environments.


SecurityWeek
CISA, FBI and EPA document aims to help water and wastewater organizations improve their cyber resilience and incident response.


The Hacker News
Vulnerabilities found in TensorFlow CI/CD pipeline allow malware upload and token theft.


CyberNews
Erasmus Student Network leaked sensitive data.


SecurityWeek
Exposed credentials for an email address at an Indian Toyota insurance broker led to customer information compromise.

Security Affairs
Researchers devised a new attack that exploits misconfigurations in Apache Hadoop and Flink to deploy cryptocurrency miners.


The Hacker News
New cyberattack targets Apache Hadoop & Flink using misconfigurations to deploy crypto miners


Infosecurity News
Mandiant has shared its findings following X account hijacking, firm blames misconfigured 2FA and X's policy change


DarkReading
The adversary is exploiting two known misconfigurations in the big data technologies to drop a Monero cryptominer.


SecurityWeek
Mortgage lending firm LoanDepot has disclosed a cyberattack resulting in data encryption and system disruptions.


CyberNews
Saudi Arabia’s Ministry of Industry and Mineral Resources (MIM) data exposed.


The Hacker News
Explore how Zero Trust Security can minimize your attack surface and safeguard against sophisticated attacks.
Loading more articles....