

CSO
US AI experts targeted in cyberespionage campaign using SugarGh0st RAT
Threat actors use phishing techniques to obtain non-public information about generative artificial intelligence.


CSO
Threat actors use phishing techniques to obtain non-public information about generative artificial intelligence.


Ars Technica
Alleged $6.8M conspiracy involved "laptop farm," identity theft, and résumé coaching.


HACKRead
New HP report reveals cybercriminals are increasingly leveraging "cat-phishing" techniques, exploiting open redirects in legitimate websites to deceive users and deliver malware.


Bleeping Computer
The U.S. Justice Department charged five individuals today, a U.S. Citizen woman, a Ukrainian man, and three foreign nationals, for their involvement in cyber schemes that generated revenue for North Korea's nuclear weapons program.


Bleeping Computer
The Norwegian National Cyber Security Centre (NCSC) recommends replacing SSLVPN/WebVPN solutions with alternatives due to the repeated exploitation of related vulnerabilities in edge network devices to breach corporate networks.


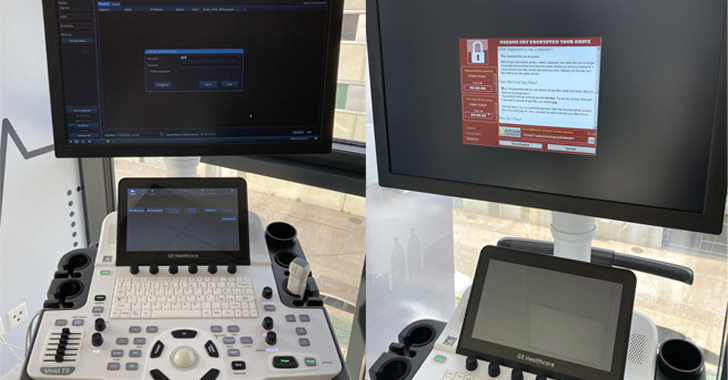
DarkReading
Thankfully, GE ultrasounds aren't Internet-facing. Exploiting most of the bugs to cause serious damage to patients would require physical device access.


HACKRead
Shadow IT involves employees using IT systems without proper security controls, often installing unauthorized software on company computers.


Bleeping Computer
Security researchers discovered two previously unseen backdoors dubbed LunarWeb and LunarMail that were used to compromise a European government's diplomatic institutions abroad.


DarkReading
In a first-ever move, the commission's enforcement bureau has high hopes that official classification will allow law enforcement partners to better combat these kinds of threats.


Cyber Security News
Best MSP for CISO, CTO & IT Managers - 1. Perimeter 812. Secureworks 3. IBM 4. Trustwave 5. Wipro 6. Verizon 7. Sophos 8. Symantec.


Security Affairs
Google released security updates to address a new actively exploited Chrome zero-day vulnerability, the third in a week.


DarkReading
Google has rolled an emergency patch for CVE-2024-4947, the third Chrome zero-day it's addressed in the past week.


The Cyber Express
Researchers recently uncovered two new backdoors implanted within the infrastructure of a European Ministry of Foreign Affairs (MFA) and its

%20(1)%20(1).webp)
Cyber Security News
A newly disclosed vulnerability, identified as CVE-2024-22026, has been found in Ivanti EPMM, formerly known as MobileIron Core.

The Hacker News
Nearly a dozen security flaws have been discovered in the GE HealthCare Vivid Ultrasound product family.


The Cyber Express
A ransomware attack has compromised MediSecure, a leading Australian script provider facilitating electronic prescribing and dispensing of prescriptions. The MediSecure


SecurityWeek
Google releases Chrome 125 to the stable channel with patches for nine vulnerabilities, including a zero-day.


Cyber Security News
Three vulnerabilities have been discovered in SAP Customer Experience (CX) commerce cloud and SAP Netweaver Application which were


The Cyber Express
In response to heightened cyber threats targeting political candidates, election officials and civil society groups, the National Cyber Security Centre


Cyber Security News
Google has released update for its Chrome to patch a high-severity vulnerability that is being actively exploited by attackers in the wild.


SecurityWeek
US officials raised concerns on China’s “misuse of AI” while Beijing’s representatives rebuked the US over “restrictions and pressure” on AI.


SC Magazine
Security pros say the uptick in Chrome zero-days this week demonstrates an increased focus by threat actors on attacking browsers.


The Record
The Share and Defend system will provide a list of malicious domains to a range of U.K. communications providers so the domains can be added to blocklists.


The Record
The NYPD said it is trying to phase out the Chinese-made drones, but also defended their use, saying they are far more effective and affordable than any produced by American manufacturers.


Bleeping Computer
Google has released a new emergency Chrome security update to address the third zero-day vulnerability exploited in attacks within a week.


Bleeping Computer
Google has released a new emergency Chrome security update to address the third zero-day vulnerability exploited in attacks within a week.


Ars Technica
Google's video synthesis model creates minute-long 1080p videos from written prompts.


Security Affairs
One of the developers of the Tornado Cash cryptocurrency mixer has been sentenced to 64 months in prison.........


Bleeping Computer
Apple's antifraud technology has blocked more than $7 billion in potentially fraudulent transactions in four years, the company states in its latest annual fraud prevention analysis.


Infosecurity News
Despite this setback, the auction house said bids can still be placed by phone and in-person


Bleeping Computer
Financially motivated cybercriminals abuse the Windows Quick Assist feature in social engineering attacks to deploy Black Basta ransomware payloads on victims' networks.


HACKRead
The cybercrime and hacker forum Breach Forums has been seized by the Federal Bureau of Investigation (FBI) and the Department of Justice.

Ars Technica
Ebury backdoors SSH servers in hosting providers, giving the malware extraordinary reach.


The Cyber Express
The ever-evolving landscape of cybersecurity is shaped by a dedicated group of individuals. These pioneers, through their research, entrepreneurship, and


Infosecurity News
The National Cyber Security Centre launches an opt-in Personal Internet Protection service to safeguard individuals from cyber threats during the upcoming election

SecurityWeek
Intel has published 41 new May 2024 Patch Tuesday advisories covering a total of more than 90 vulnerabilities.

.webp)
Cyber Security News
The well-known advanced persistent threat (APT) group Turla, which is based in Russia, is said to be going after the European Ministry.


Infosecurity News
Santander has warned that customer and employee data has been breached following unauthorized access to a database held by a third-party provider


The Cyber Express
The notorious DragonForce ransomware group has expanded its list of victims, adding two new names to their dark web portal

The Hacker News
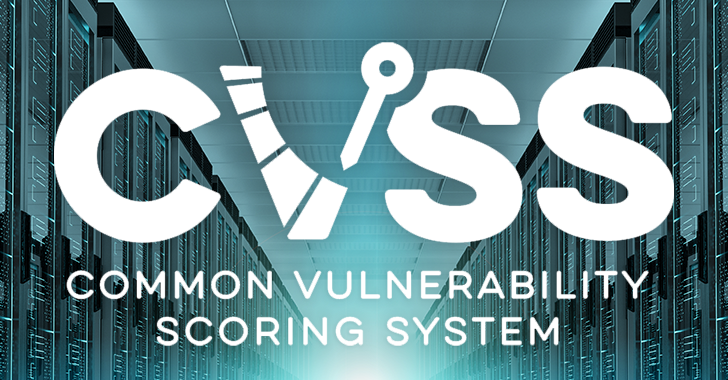
CVSS v4.0 evaluates vulnerabilities using a revised scoring system, emphasizing environmental and threat metrics.

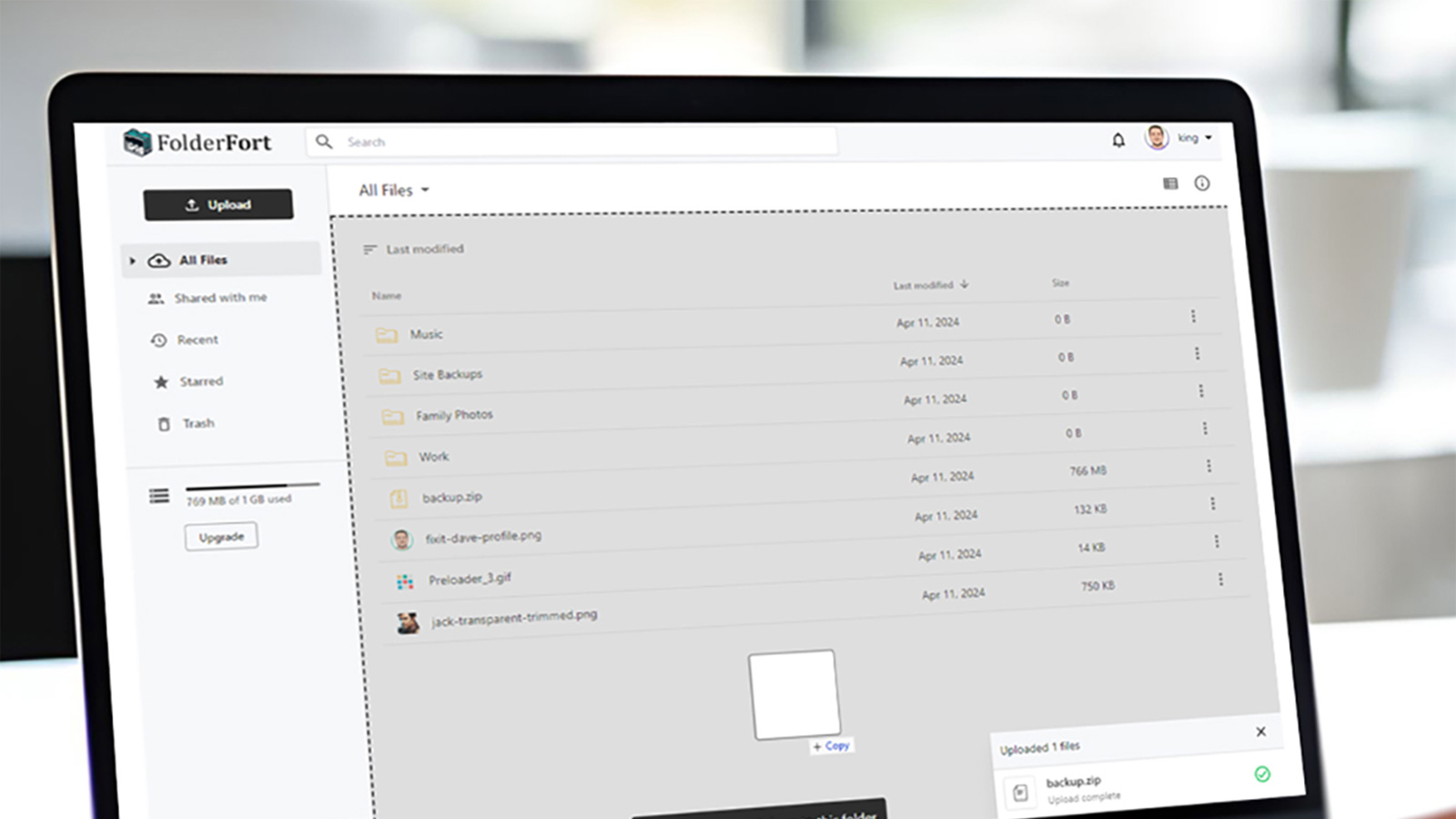
Bleeping Computer
As our gadgets multiply and our jobs grow in complexity, we need file storage that's friendly on the wallet and easy to use. Get 1TB of fast file storage with FolderFort for $79.99, $171 off the $251 MSRP.


Infosecurity News
Trend Micro research claims CISOs are often ignored or dismissed as “nagging” by their board

SecurityWeek
Several ICS vendors have released advisories on Tuesday to inform customers about vulnerabilities found in their products.


The Cyber Express
CISA, in collaboration with DHS, FBI, and international cybersecurity entities, has revealed a comprehensive guide aimed at bolstering cybersecurity for


The Cyber Express
Microsoft patched a zero-day vulnerability exploited by attackers to distribute QakBot and other malware payloads on susceptible Windows systems. Identified


Cyber Security News
Best Network Security Providers for the Healthcare Industry - 1. Perimeter 81, 2. Palo Alto Networks, 3. Fortinet, 4. Cisco, 5. Trend Micro


The Cyber Express
A new Google Chrome vulnerability has been uncovered and exploited, marking the sixth zero-day incident in 2024 alone. In response,


The Hacker News
Microsoft has patched 61 new security flaws, including two zero-days actively exploited in the wild.


Cyber Security News
Alert Triage is a process of recognizing the important alerts from a huge pool of security alerts and allocating the resources accurately.

.webp)
Cyber Security News
WPS Office is a office suite developed by Kingsoft that supports spreadsheets, presentations, documents and others. It has been used


The Record
The U.K. government has warned that the accounts of political candidates and election officials are “almost certainly attractive targets for cyber actors looking to carry out espionage operations.”


The Record
Researchers with cybersecurity company ESET have labeled two new pieces of suspected Russian malware as LunarWeb and LunarMail.


SC Magazine
The infamous data leak site’s domain and Telegram account were seized Wednesday morning.


The Record
Sonne Finance, which allows people to lend and borrow funds without the need for intermediaries, said it would commit to not pursuing the heist any further if the perpetrator accepted an undisclosed bounty and returned the stolen cryptocurrency.


DarkReading
CVE-2024-30051 is the most concerning out of this month's Patch Tuesday offerings, and is already under active exploit by several QakBot actors.


Bleeping Computer
The D-Link EXO AX4800 (DIR-X4860) router is vulnerable to remote unauthenticated command execution that could lead to complete device takeovers by attackers with access to the HNAP port.


Security Affairs
Microsoft Patch Tuesday security updates for May 2024 fixed 59 flaws across various products including an actively exploited zero-day.


Bleeping Computer
Microsoft has fixed a known issue causing NTLM authentication failures and domain controller reboots after installing last month's Windows Server security updates.


Ars Technica
AI model updates galore at Google I/O, including 2m context window, Imagen 3, Veo, and more.

SecurityWeek
Microsoft patched 60 security bugs in multiple products and waned of an actively exploited Windows zero-day (CVE-2024-30051)


Bleeping Computer
Today is Microsoft's May 2024 Patch Tuesday, which includes security updates for 61 flaws and three actively exploited or publicly disclosed zero days.


SecurityWeek
Adobe documents multiple code execution flaws in a wide range of products, including the widely deployed Adobe Acrobat and Reader software.


Infosecurity News
The 15-year-old Ebury botnet is more active than ever, as ESET found 400,000 Linux servers compromised for cryptocurrency theft and financial gain


DarkReading
Exploit code is circulating for CVE-2024-4761, disclosed less than a week after a similar security vulnerability was disclosed as being used in the wild.

Bleeping Computer
A malware botnet known as 'Ebury' has infected almost 400,000 Linux servers since 2009, with roughly 100,000 still compromised as of late 2023.


Infosecurity News
The guide is designed to provide high-risk communities with actionable steps to bolster their cybersecurity defenses


Infosecurity News
Several software security experts have told Infosecurity that no new vulnerabilities have been added to the US NVD since May 9


Bleeping Computer
VMware fixed four security vulnerabilities in the Workstation and Fusion desktop hypervisors, including three zero-days exploited during the Pwn2Own Vancouver 2024 hacking contest.

HACKRead
DNS tunneling is being used to bypass security filters by hiding malicious traffic in DNS packets, allowing hackers to steal stolen data.


Ars Technica
Rare bitcoin fragments are worth many times their face value.


DarkReading
Several campaigns are leveraging the evasive tactic to provide useful insights into victims' online activities, and find new ways to compromise organizations.


SecurityWeek
SAP has released 14 new and three updated security notes on its May 2024 Security Patch Day, including for critical vulnerabilities.


The Hacker News
Google has released emergency fixes for a new zero-day vulnerability (CVE-2024-4761) that has been actively exploited in the wild.


SecurityWeek
VMware has patched three critical and high-severity vulnerabilities exploited earlier this year at the Pwn2Own hacking competition.


HACKRead
The Israel-Hamas conflict has fueled a wave of hacktivism activity, with groups like SiegedSec launching attacks and leaking sensitive information.


SecurityWeek
Threat actors are using DNS tunneling to track victims’ interaction with spam and to scan network infrastructures.


SecurityWeek
Google has patched CVE-2024-4761, the second exploited vulnerability addressed by the company within one week.

The Hacker News
12 security flaws addressed, including two critical issues leading to remote code execution. Update to version 1.2.27 now to stay protected

.webp)
Cyber Security News
A severe security vulnerability has been identified in the Linksys EA7500 routers, affecting the model's firmware across all versions.


Security Affairs
Google released emergency security updates to address an actively exploited Chrome zero-day vulnerability.


The Hacker News
Advanced authentication: The key to addressing the weakest link in cybersecurity - human users. Learn how to fortify your organization's defenses.


The Hacker News
A new social engineering campaign is targeting enterprises with spam emails to gain initial access. The threat actor overwhelms users' email and calls


Cyber Security News
Few Critical vulnerabilities have been discovered in Cinterion Cellular modems that could allow an unauthorized remote attacker to execute


Cyber Security News
Google has released an urgent security update for the Chrome browser to address a high-severity vulnerability that is being actively exploited in the wild.


The Cyber Express
The IntelBroker hacker has allegedly leaked a database belonging to the National Parent Teacher Association (PTA), a cornerstone of child

.webp)
Cyber Security News
A threat actor has reportedly put up for sale a RCE 0-day exploit targeting various versions of Microsoft Outlook..


CyberSecurity Dive
The detail and speed with which companies share information after an attack can prevent future pain. But businesses aren’t always keen on transparency.


Bleeping Computer
Google has released emergency security updates for the Chrome browser to address a high-severity zero-day vulnerability tagged as exploited in attacks.


Latest Hacking News
Chrome users must ensure that their devices are updated with the latest browser release. Google addressed an actively exploited zero-day flaw with the latest build, which applies to all Chrome users with various devices. The


Latest Hacking News
Torrance, California, May 13th, 2024, CyberNewsWireCriminal IP, a renowned Cyber Threat Intelligence (CTI) search engine developed by AI SPERA, has recently signed a technology partnership to exchange threat intelligence data based on domains and potentially

.webp)
Cyber Security News
According to the FCC, the Royal Tiger Group and the people who work with it are a C-Communications Information Services Threat (C-CIST).


SecurityWeek
Zscaler has completed its investigation into the recent hacking claims and found that only an isolated test environment was compromised.


SC Magazine
Security pros say the industry can expect to see this bug exploited soon, so patch, monitor and conduct other measures, like browser isolation and sandboxing.


SC Magazine
Emails from “Jenny Green” delivered LockBit Black through attached ZIP files.


The Record
State-linked hackers from Russia, China, Iran and North Korea are setting their sights set their sights on NGOs, think tanks, human rights activists and journalists, the advisory warned.


The Record
Rep. Zach Nunn arrived in Congress with arguably more cyber experience than any other new member in history. Can he fill the shoes of Rep. Mike Gallagher, the party's longtime House leader on cybersecurity issues?


Bleeping Computer
Apple has backported security patches released in March to older iPhones and iPads, fixing an iOS zero-day tagged as exploited in attacks.


Bleeping Computer
Apple has backported security patches released in March to older iPhones and iPads, fixing an iOS Kernel zero-day tagged as exploited in attacks.


DarkReading
Ransomware groups have always created problems for their victims that only they could solve. Black Basta is taking that core idea in a creative, new direction.


Bleeping Computer
A cybercriminal using the name "salfetka" claims to be selling the source code of INC Ransom, a ransomware-as-a-service (RaaS) operation launched in August 2023.
Loading more articles....