

DarkReading
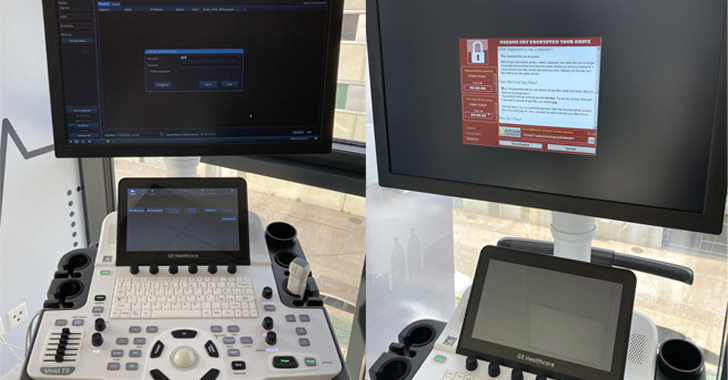
GE Ultrasound Gear Riddled With Bugs, Open to Ransomware & Data Theft
Thankfully, GE ultrasounds aren't Internet-facing. Exploiting most of the bugs to cause serious damage to patients would require physical device access.


DarkReading
Thankfully, GE ultrasounds aren't Internet-facing. Exploiting most of the bugs to cause serious damage to patients would require physical device access.


HACKRead
Shadow IT involves employees using IT systems without proper security controls, often installing unauthorized software on company computers.


Cyber Security News
Best MSP for CISO, CTO & IT Managers - 1. Perimeter 812. Secureworks 3. IBM 4. Trustwave 5. Wipro 6. Verizon 7. Sophos 8. Symantec.


HACKRead
The Internet of Things (IoT) promises a world of interconnected devices, but with this connectivity comes a dark side such as security vulnerabilities.

The Hacker News
Nearly a dozen security flaws have been discovered in the GE HealthCare Vivid Ultrasound product family.


Latest Hacking News
Researchers caught numerous security vulnerabilities riddling Cinterion cellular modems, exploiting which would threaten millions of devices. Since no active patches currently exist for the flaws, the researchers recommend applying the suggested mitigations to prevent potential


The Cyber Express
The ever-evolving landscape of cybersecurity is shaped by a dedicated group of individuals. These pioneers, through their research, entrepreneurship, and


SecurityWeek
The Ebury Linux botnet has ensnared over 400,000 Linux systems in 15 years, with roughly 100,000 still infected.


Cyber Security News
Best Network Security Providers for the Healthcare Industry - 1. Perimeter 81, 2. Palo Alto Networks, 3. Fortinet, 4. Cisco, 5. Trend Micro


Security Affairs
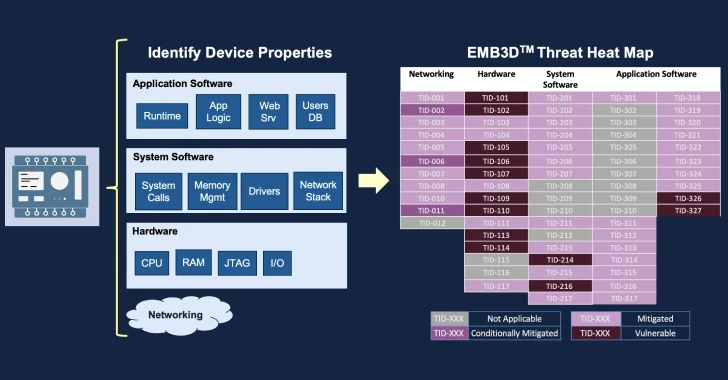
The non-profit technology organization MITRE released the EMB3D threat model for embedded devices used in critical infrastructure.

SecurityWeek
MITRE announced the public availability of the EMB3D threat model for embedded devices used in critical infrastructure.


Cyber Security News
Few Critical vulnerabilities have been discovered in Cinterion Cellular modems that could allow an unauthorized remote attacker to execute


Latest Hacking News
Torrance, California, May 13th, 2024, CyberNewsWireCriminal IP, a renowned Cyber Threat Intelligence (CTI) search engine developed by AI SPERA, has recently signed a technology partnership to exchange threat intelligence data based on domains and potentially


The Cyber Express
Millions of Internet of Things (IoT) devices present across the industrial, healthcare, automotive, financial, and telecommunication sectors are at significant


HACKRead
Kaspersky researchers have identified multiple security vulnerabilities in Cinterion cellular modems, which could be exploited by threat actors.

%20(1).webp)
Cyber Security News
"Our partnership with Quad9 is a recognition of the accuracy of Criminal IP's data," stated Byungtak Kang, CEO of AI SPERA.

The Hacker News
MITREcorp has launched EMB3D, a new threat-modeling framework for embedded devices used in critical infrastructure.


CyberNews
A study on dogs in Lima, Peru, wants to find out whether IoT devices on pets can indicate seismic activity.


Bleeping Computer
The Criminal IP Threat Intelligence (CTI) search engine to integrate with Quad9's threat-blocking service. Learn more from Criminal IP about how this integration can help you.


HACKRead
Torrance, California, May 13th, 2024, CyberNewsWire


SecurityWeek
A critical vulnerability in the Cinterion cellular modems can be exploited for remote code execution via SMS messages.


Bleeping Computer
White-hat hacking is one of the best skills you can learn to advance your cybersecurity career. These nine cybersecurity courses teach you how for $49.99, $301 off the $351 MSRP.


The Hacker News
Kaspersky researchers have uncovered multiple security flaws in Cinterion cellular modems that could put your communication networks and IoT devices a


SecurityWeek
Chinese hacking contest Matrix Cup is offering rewards for exploits targeting OS, smartphones, enterprise software, and security products.


SC Magazine
Security pros say critical flaws in cellular these modems could cut across the industrial, healthcare, automotive, financial, and telecom sectors.


DarkReading
Researchers discovered seven vulnerabilities — including an unauthenticated RCE issue — in widely deployed Telit Cinterion modems.


Bleeping Computer
Security flaws in Telit Cinterion cellular modems, widely used in sectors including industrial, healthcare, and telecommunications, could allow remote attackers to execute arbitrary code via SMS.


The Cyber Express
Lenovo takes a bold step towards fortifying cybersecurity by joining the Secure by Design pledge, initiated by the US Cybersecurity


Computerworld
It’s bad enough when an employee goes rogue and does an end-run around IT; but when a vendor does something similar, the problems could be broadly worse.


SecurityWeek
Healthcare cybersecurity company Blackwell Security has raised $13 million and appointed Geyer Jones as its first CEO.


The Cyber Express
Cyber Defense Magazine (CDM), marking its 12th anniversary as the leading electronic information security magazine, announced the winners of the


SecurityWeek
As cyber threats grow more sophisticated, America can't afford complacency. The time for decisive action and enhanced cyber resilience is now.

%20(1).webp)
Cyber Security News
Microsoft has announced an expansion of its Defender Extended Detection & Response (XDR) capabilities to include advanced AI-powered detection

.png)
Cyber Security News
The weekly news summary keeps you up to date with what’s happening in cybersecurity, including developments, vulnerabilities, breaches, threats, and defensive strategies. Knowing about new cyber risks and attack vectors helps you put up safeguards and preventive measures as soon as possible to protect your systems. Remaining constantly aware gives you a holistic view of […]


Cyber Security News
Solutions for each challenge are explained in more depth by Cynet’s new guide, “Top 10 Cybersecurity Challenges Faced by K-12 Institutions.”


The Hacker News
Our webinar unveils the latest DDoS attack strategies like IoT botnets & amplification tactics. Get real-world examples & proactive defense tips.


SecurityWeek
A botnet dismantled in January and used by Russia-linked APT28 consisted of more than just Ubiquiti Edge OS routers.


SecurityWeek
Malware platform roaming around enterprise SOHO routers capable of covertly harvesting public cloud authentication data from internet traffic.


The Cyber Express
National Supply Chain Day, which was recently observed on April 29, serves as a dedicated day to recognize the critical


Security Affairs
The UK National Cyber Security Centre (NCSC) orders smart device manufacturers to ban default passwords starting from April 29, 2024.


The Hacker News
The U.K. is the first country to ban default passwords on smart devices starting April 29, 2024. Manufacturers must provide unique passwords and secur


CyberNews
How AI and ML models can increase software supply chain risks and lead to cybersecurity incidents


Infosecurity News
IoT manufacturers, retailers and importers must comply with new security legislation, the PSTI act, from today

The Record
Britain now has IoT hardware standards that ban weak or easily guessable default passwords such as “admin” or “12345." Manufacturers are also required to publish contact details so users can report bugs.


The Record
Ukraine’s government uses the bots to collect and share real-time information about Russian military activity.


HACKRead
As we progress through 2024, home security is rapidly advancing, with a notable shift towards integrated residential security solutions.


The Cyber Express
Networking giant Cisco warned that a group of state-sponsored hackers exploited zero-days in its firewall appliances to spy on government

DarkReading
Dark Reading talks cloud security with John Kindervag, the godfather of zero trust.


The Record
The cybersecurity firm Mandiant saw a more than 50% growth in zero-day usage compared to 2022.


CyberSecurity Dive
A CYE analysis of 101 breaches across various sectors revealed insurance gaps resulting in an average of $27.3 million in uncovered losses per incident.


The Cyber Express
by Neelesh Kripalani, Chief Technology Officer, Clover Infotech As businesses grapple with an ever-changing and increasingly hostile threat environment, the


The Record
Hans de Vries says ENISA wants to create a notification platform for vulnerabilities, not a central database that would otherwise be a security risk itself.


DarkReading
Moobot, Miori, AGoent, and a Gafgyt variant have joined the infamous Mirai botnet in attacking unpatched versions of vulnerable Wi-Fi routers.

.webp)
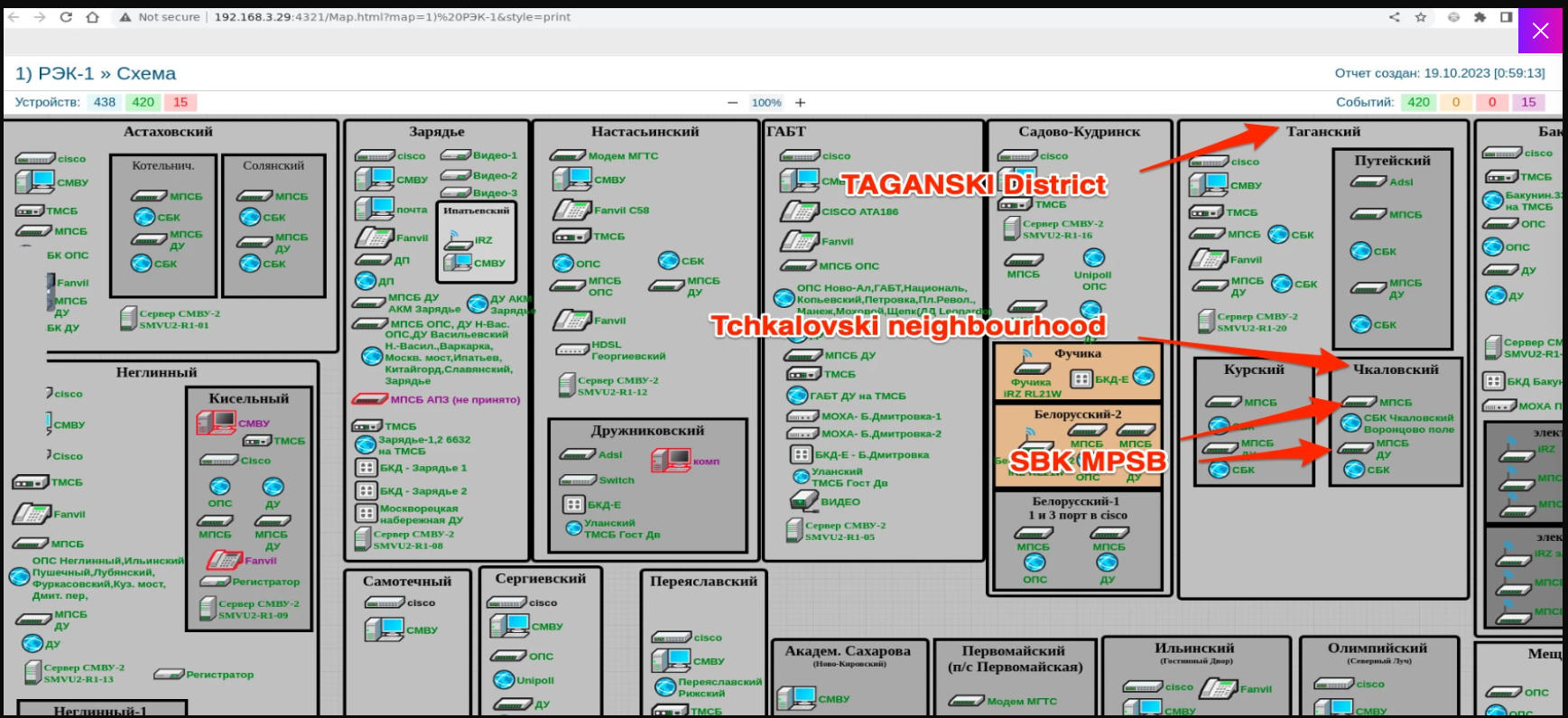
Cyber Security News
Exploitation of a critical vulnerability in TP-Link Archer routers, leading to the proliferation of various botnet threats.


The Hacker News
Researchers alert of a global rise in brute-force attacks from TOR nodes targeting VPNs, web interfaces, and SSH services

The Record
The bug affects the the Archer AX21, a popular router model manufactured by TP-Link.

Security Affairs
The Ukrainian hacking group Blackjack used a destructive ICS malware dubbed Fuxnet in attacks against Russian infrastructure.


HACKRead
Palo Alto Networks has released patches for a 0-day vulnerability (CVE-2024-3400) that threatened to leave firewalls exposed to cyberattacks.


SecurityWeek
ICS malware Fuxnet allegedly used by Ukrainian hackers to disrupt industrial sensors and other systems belonging to a Russian firm.


Latest Hacking News
This month’s Patch Tuesday update bundle from Microsoft is a huge one, requiring immediate user attention for device updates. Specifically, with April 2024 Patch Tuesday, Microsoft addressed 150 different security flaws, including over 60 remote

Bleeping Computer
Raspberry Pi and Arduino are amazing on their own, but intimidating to learn. These nine coding and robotics courses help you get the most from them for $59.97, $363 off the $423 MSRP, now through the end of April 21st.


Cyber Security News
The weekly cybersecurity news wrap-up provides readers with the latest information on emerging risks, vulnerabilities, ways to reduce them, and harmful schemes to help make defensive measures proactive.


SecurityWeek
Second identifier, CVE-2024-3272, assigned to unpatched D-Link NAS device vulnerabilities, just as exploitation attempts soar.

.webp)
Cyber Security News
Ukrainian hackers have successfully infiltrated and disabled a vast network of industrial sensors and monitoring infrastructure in Russia.

.webp)
Cyber Security News
This acquisition is set to redefine the way enterprises protect their internal traffic, particularly in IT and OT environments.


Trend Micro
Learn how far cybersecurity has come from scattered resources to consolidation the future.

Bleeping Computer
There's nothing like building your own equipment to your exact specifications. This 10-course open-source IoT bundle shows you how for $29.99, $220 off the $250 MSRP.


The Cyber Express
A significant data leak, purportedly affecting tech giant Microsoft, has been uncovered by cybersecurity researchers. The leak allegedly exposed sensitive


The Cyber Express
Microsoft has released the latest Patch Tuesday update, addressing a large number of vulnerabilities across various products and services. The


Infosecurity News
The issues identified permit unauthorized access to the TV’s root system by bypassing authorization mechanisms


Infosecurity News
April’s Patch Tuesday saw fixes for 150 CVEs, including two being actively exploited in the wild


Security Affairs
As technology evolves and our dependence on digital systems increases, the cybersecurity threat landscape also rapidly changes.


Computerworld
Unified endpoint management software lets IT manage all endpoint devices — smartphones, laptops, desktops, printers, IoT devices, and others — from a single management console. Here’s what to look for in a UEM platform and key vendors to consider.


SC Magazine
The HP Threat Research team says security pros should take note because Raspberry Robin has been used to deliver multiple families of malware – and as a precursor to ransomware.


SC Magazine
This month’s bumper crop of patches includes two Microsoft didn’t initially acknowledge were being exploited in the wild.


DarkReading
As more electric vehicles are sold, the risk to compromised charging stations looms large alongside the potential for major cybersecurity exploits.


SecurityWeek
Microsoft documents a serious vulnerability that allows unauthenticated hackers to take complete control of Azure Kubernetes clusters.


Bleeping Computer
Today is Microsoft's April 2024 Patch Tuesday, which includes security updates for 150 flaws and sixty-seven remote code execution bugs.

%20(3)%20(1).webp)
Cyber Security News
Bitdefender Labs has revealed a critical security flaw in over 90k LG smart TVs running the company's proprietary WebOS platform.


HACKRead
LG TVs vulnerable! Update now to block hackers from taking control & stealing data (webOS 4-7). Millions at risk!


The Record
Four new vulnerabilities affecting thousands of LG TVs have been found by researchers who said the issues allow hackers to add themselves as users and take other actions.


DarkReading
As manufacturers sprint to add software-defined features for vehicles, the ability for third-party maintenance and repair falls behind, leaving businesses with few choices to manage their cybersecurity.

Cyber Security News
Chinese devices are suspected of administering cyber espionage due to concerns over potential backdoors, supply chain vulnerabilities, and the


CyberNews
KidSecurity has leaked sensitive information about children for the second time.


The Hacker News
Operational Technology (OT) Cybersecurity: A Balancing Act! OT systems' unique traits demand tailored security measures. Learn why safeguarding OT req


Infosecurity News
The findings from Netskope also show a shift in the retail sector’s use of cloud applications

SecurityWeek
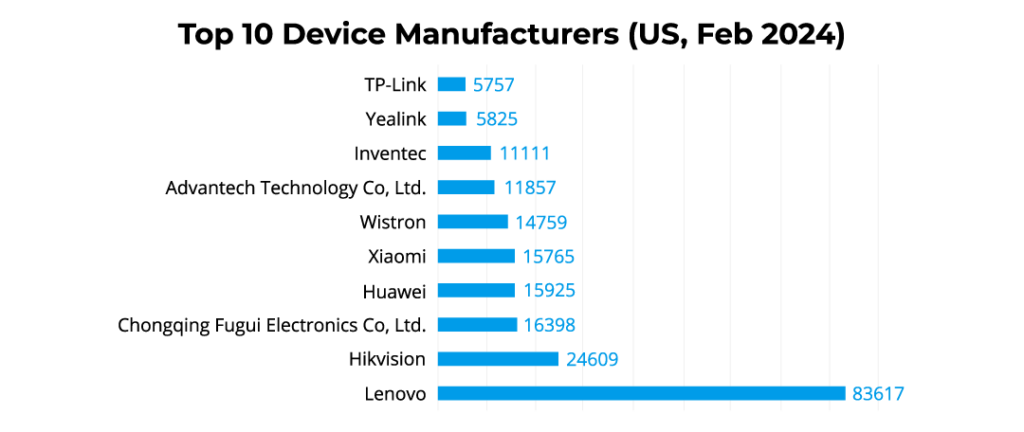
An analysis by Forescout shows 300,000 Chinese devices in the US, up 40% compared to the previous year, despite bans.


Cyber Security News
Hackers exploit security flaws in Qualcomm to gain unauthorized access, execute malicious code, or potentially compromise data integrity and


Cyber Security News
A prominent provider of cybersecurity and compliance services, recently expanded its portfolio by introducing iTrust and GhostWatch.


SecurityWeek
The OWASP Foundation says a wiki misconfiguration exposed resumes filed over a decade ago by aspiring members.


CyberSecurity Dive
Small businesses can be especially vulnerable to cyberattacks because of their limited resources, and few have employees on staff who truly understand the value of secure business operations.


The Hacker News
Android VPN apps hijacking devices, covertly turning them into proxy nodes for threat actors and fueling botnet operations.


Cyber Security News
The European Union Agency for Cybersecurity (ENISA) has published a list of the top ten emerging threats anticipated to impact the digital.


HACKRead
A new variant of "TheMoon Malware" has emerged, specifically targeting vulnerable IoT devices, particularly Asus routers.


DarkReading
Outdated SOHO routers and IoT devices being hijacked by TheMoon to operate an anonymous hacker botnet service called Faceless.


The Hacker News
TheMoon botnet, previously thought to be inactive, is back. Over 40,000 routers & IoT devices hijacked to power Faceless - a criminal proxy service.


The Cyber Express
By Shrikant Navelkar, Director, Clover Infotech Due to the significant advancements in the IT industry, the adoption of cloud computing


SC Magazine
Malware first identified in 2014 re-emerges and gets delivered by the criminal proxy service Faceless, now growing at 7,000 users per week.


CyberNews
Old routers and IoT devices have been identified as key targets for six large malware campaigns. Cybersecurity experts are urging users to update their devices.


DarkReading
Government proposes more modern and comprehensive cybersecurity regulations for businesses, government, and critical infrastructures providers Down Under.
Loading more articles....