

SC Magazine
LockBit ransomware spread in millions of emails via Phorpiex botnet
Emails from “Jenny Green” delivered LockBit Black through attached ZIP files.


SC Magazine
Emails from “Jenny Green” delivered LockBit Black through attached ZIP files.


DarkReading
As Verizon Business redefines "supply chain breach," it could either help organizations address third-party risk holistically or just conflate and confuse.


DarkReading
Our collection of the most relevant reporting and industry perspectives for those guiding cybersecurity strategies and focused on SecOps. Also included: a Tech Tip on setting up DMARC, a DNS mystery from Muddling Meerkat, and a cybersecurity checklist for M&A transitions.

Security Magazine
The 2024 Data Breach Investigations Report reveals the role that the human element plays in cyber threats, and security leaders are weighing in.


SecurityWeek
Horizon3.ai's AISaaS-based, AI-assisted penetration service allows proactive defensive action against exploitation of new vulnerabilities.

SecurityWeek
Verizon 2024 DBIR shows that vulnerability exploitation increased three times and confirmed data breaches doubled compared to 2023.

Infosecurity News
The growth of software supply chain attacks pushed vulnerability exploits to the third most used initial access method, Verizon found


DarkReading
MOVEit drove a big chunk of the increase, but social engineering and failure to patch led to a doubling of data breaches since 2023, said Verizon Business.


SC Magazine
Vulnerability exploits, pure extortion and internal risks are on the rise, while AI threats fall short.


CSO
Absence of multi-factor authentication reportedly left a remote access application exposed.

The Hacker News
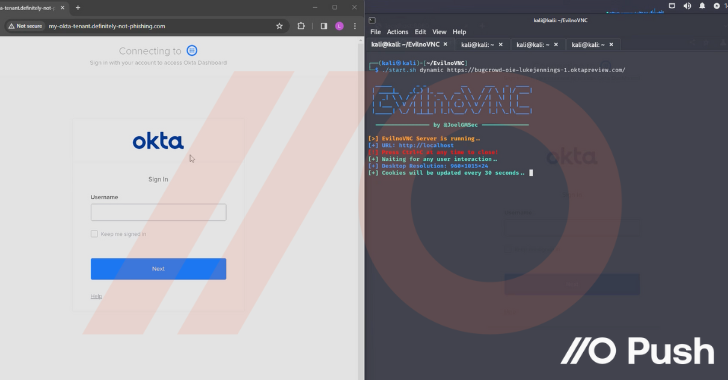
How attackers are hacking organizations without touching the endpoint by targeting cloud identities.

Cyber Security News
we’ll dissect a timely example of credential theft—StrelaStealer—to identify the malware’s characteristics and capabilities.


The Cyber Express
ETISALAT, the state-owned Emirates Telecommunications Group Company PJSC in the UAE, is reportedly grappling with a ransomware assault attributed to


The Hacker News
83% of breaches in 2023 fueled by stolen credentials! Uncover the latest attacker tactics and fortify your defenses against this escalating threat.


CyberSecurity Dive
Golden Ticket attacks hit the Key Distribution Service Account of the KDC, here's how to stop them.


Infosecurity News
The Cyber Threat Intelligence Summit discussed how automation and generative AI could help CTI practitioners tackle the overload of data they have to process


Cyber Security News
Endpoint Security Best Practices: Endpoint security serves as the first line of defense against cyberattacks for businesses.


Bleeping Computer
Business Email Compromise (BEC) poses a growing threat to businesses of all sizes. Learn more from Specops Software about the types of BEC attacks and how to avoid them.


DarkReading
Threat actors have grown increasingly sophisticated in applying social engineering tactics against their victims, which is key to this oft-underrated cybercriminal scam's success.


DataBreaches
Verizon’s top-notch annual Data Breach Investigations Report (DBIR) is out. You can jump to the Executive Summary of the report, download the entire...


DarkReading
Ransomware continues its runaway growth with median payments reaching $50,000 per incident.


The Hacker News
Find out why manufacturers are becoming prime targets and what they can do to mitigate the risk.


DarkReading
As companies increasingly adopt MFA (even as companies like Twitter disable it), cybercriminals are developing a variety of strategies to steal credentials and gain access to high-value accounts anyway.


DarkReading
As ransomware's prevalence has grown over the past decade, leading ransomware groups such as Conti have added services and features as part of a growing trend toward professionalization.


Security Affairs
Passwords no longer meet the demands of today’s identity and access requirements. Therefore, strong authentication methods are needed. “Usernames and passwords are insufficient and vulnerable means of authentication on their own; therefore, it is essential to employ strong authentication techniques like multi-factor authentication (MFA) to confirm users’ identities before granting secure access to resources,” Sarah […]


ThreatPost
Attackers gained access to private account details through an email compromise incident that occurred in April.


ThreatPost
Verizon’s annual report for 2022 confirms trends that have been years in the making.


CSO
From a new ransomware group that demands donations instead of cryptocurrency to the possible resurgence of an infamous gang, these are the stories that caught the attention of infosec pros.


DarkReading
The cloud instances were left open to the public Internet with no authentication, allowing attackers to wipe the data.


DarkReading
Global ransomware incidents target everything from enterprise servers to grounding an airline, with one India-based group even taking a Robin Hood approach to extortion with the "GoodWill" strain.


The Record
It's the latest move by international law enforcement and Nigerian authorities against a group cybersecurity researchers call SilverTerrier.


ThreatPost
2022’s DBIR also highlighted the far-reaching impact of supply-chain breaches and how organizations and their employees are the reasons why incidents occur.


DarkReading
Ransomware has become so efficient, and the underground economy so professional, that traditional monetization of stolen data may be on its way out.


Infosecurity News
Ransomware breaches have increased by 13% – more than last five years combined – according to new report


CyberNews
No wonder the crooks are getting away with the same old phishing scams - company decision-makers seem to think security training is a joke.