

Infosecurity News
#RSAC: Experts Highlight Novel Cyber Threats and Tactics
Well-funded cybercriminals are adopting more sophisticated techniques, creating a need for defenders to stay informed about the evolving threat landscape


Infosecurity News
Well-funded cybercriminals are adopting more sophisticated techniques, creating a need for defenders to stay informed about the evolving threat landscape


HACKRead
WordPress websites are under attack with a surge of malicious JavaScript being injected using vulnerable versions of the LiteSpeed Cache plugin.


The Hacker News
A critical flaw in the hugely popular LiteSpeed Cache plugin for WordPress is being exploited in the wild to create rogue admin accounts, granting att

.png)
Cyber Security News
The weekly news summary keeps you up to date with what’s happening in cybersecurity, including developments, vulnerabilities, breaches, threats, and defensive strategies. Knowing about new cyber risks and attack vectors helps you put up safeguards and preventive measures as soon as possible to protect your systems. Remaining constantly aware gives you a holistic view of […]


Bleeping Computer
Google has rolled back a recent release of its reCaptcha captcha script after a bug caused the service to no longer work on Firefox for Windows.


Bleeping Computer
Latrodectus malware is now being distributed in phishing campaigns using Microsoft Azure and Cloudflare lures to appear legitimate while making it harder for email security platforms to detect the emails as malicious.


The Cyber Express
Okta reported an "unprecedented scale" of credential stuffing attacks targeting its identity and access management solutions, resulting in the breach

The DFIR Report
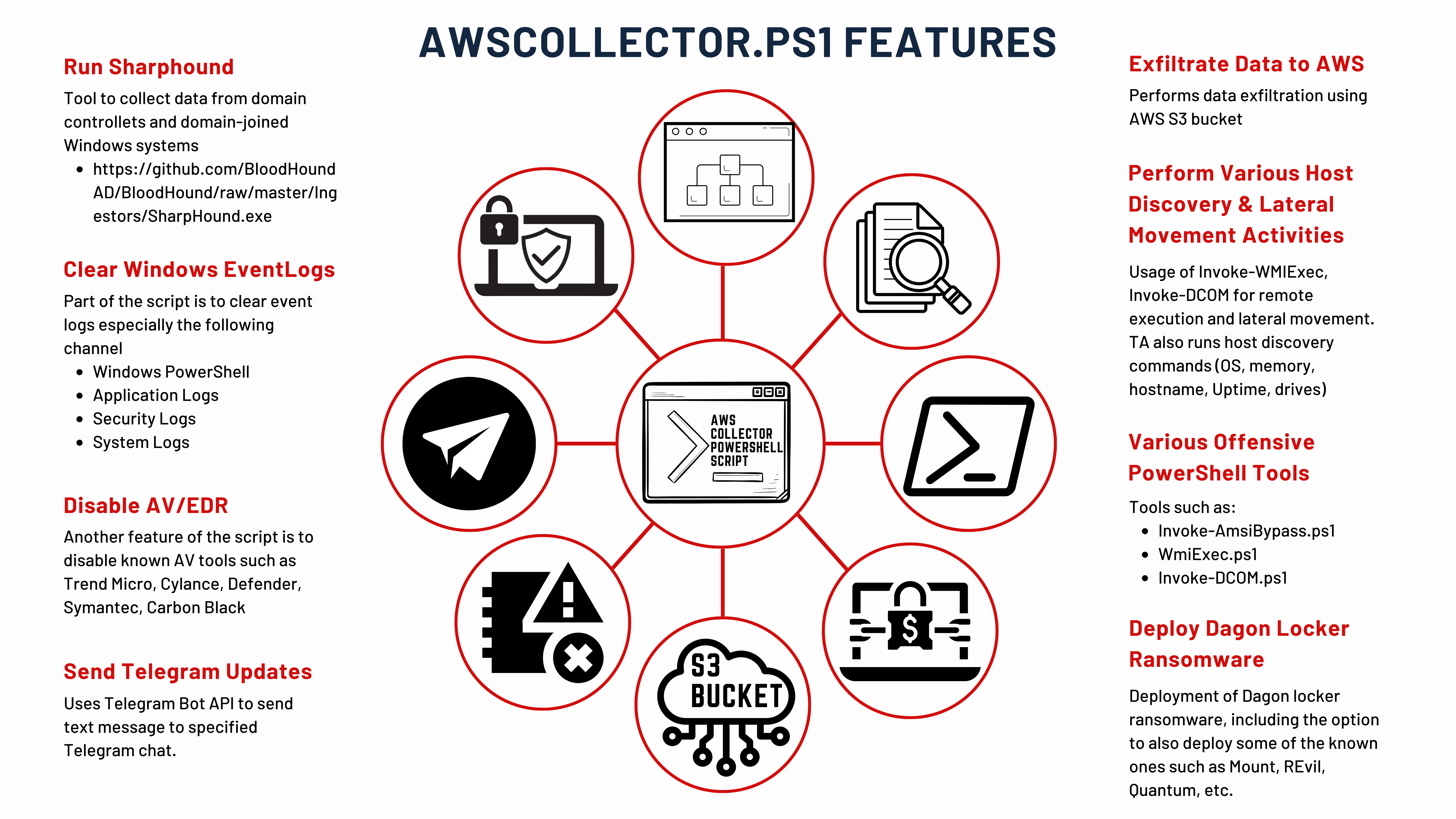
Key Takeaways In August 2023, we observed an intrusion that started with a phishing campaign using PrometheusTDS to distribute IcedID. IcedID dropped and executed a Cobalt Strike beacon, which was … Read More


Bleeping Computer
Okta warns of an "unprecedented" spike in credential stuffing attacks targeting its identity and access management solutions, with some customer accounts breached in the attacks.


Ars Technica
Campaign used email, SMS, and voice calls to trick targets into divulging master passwords.


HACKRead
Here's a list of 5 effective CAPTCHA plugins for WordPress that can help enhance the security of your website by preventing spam and bot activities:


Cyber Security News
A recent phishing campaign targeting Latin America utilized emails with ZIP attachments containing an HTML file disguised as an invoice using


The Hacker News
Latin America targeted in new phishing attack. Emails contain malicious HTML files disguised as invoices.


DarkReading
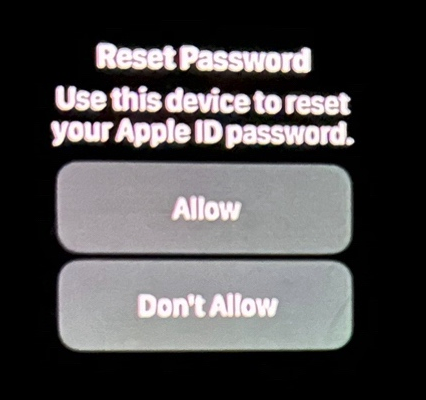
Several Apple device users have experienced recent incidents where they have received incessant password reset prompts and vishing calls from a number spoofing Apple's legitimate customer support line.


Ars Technica
Rapid-fire prompts sometimes followed with spoofed calls from "Apple support."


DarkReading
Threat actors are widely adopting the fast-growing, low-cost phishing-as-a-service (PhaaS) platform, which is sold via Telegram.

Krebs on Security
Several Apple customers recently reported being targeted in elaborate phishing attacks that involve what appears to be a bug in Apple's password reset feature. In this scenario, a target's Apple devices are forced to display dozens of system-level prompts that…


The Hacker News
Researchers at Palo Alto Networks Unit 42 uncover a new wave of phishing attacks delivering StrelaStealer malware, impacting over 100 organizations in


SecurityWeek
CISA, the FBI, and MS-ISAC have released new guidance on how federal agencies can defend against DDoS attacks.


Infosecurity News
The joint advisory sets out how to mitigate and respond to DDoS attacks, limiting disruption to critical services


Cyber Security News
CISA, in collaboration with FBI and the Multi-State Information Sharing and Analysis Center (MS-ISAC), has released a comprehensive guide.


CSO
The advisory describes the critical DDoS tactics, with recommendations to defend against such attacks.


HACKRead
Tax season is underway in the United States, bringing with it the notorious tax returns phishing campaigns targeting taxpayers and businesses.


Infosecurity News
Secureworks is warning of fake obituary sites which expose visitors to fake AV scams


The Hacker News
Researchers uncover a sophisticated malware campaign using fake Google Sites pages and HTML smuggling to distribute AZORult, a notorious info stealer.


SC Magazine
Azorult infostealer aims to steal user credentials and credit card information via HTML smuggling.


HACKRead
These groups launched phishing attacks using stealthy attack patterns to target officials at large US school districts, bypassing MFA protections.

Trend Micro
Discover the fascinating world of AI, ML, and RPA and their real-world applications including the creation of a custom RPA bot for collecting rare sports memorabilia.


SecurityWeek
Advanced phishing kit employs novel tactics in attack targeting cryptocurrency platforms and FCC employees.


Bleeping Computer
A new phishing kit named CryptoChameleon is being used to target Federal Communications Commission (FCC) employees, using specially crafted single sign-on (SSO) pages for Okta that appear remarkably similar to the originals.


HACKRead
Lookout has discovered a phishing campaign, dubbed "CryptoChameleon," that mimics legitimate login pages for cryptocurrency platforms.


The Hacker News
Cryptocurrency users BEWARE! Sophisticated phishing kit actively impersonating major exchanges.


SecurityWeek
The API attack surface is expanding and API vulnerabilities are growing. AI will help criminals find and exploit API vulnerabilities at scale


Infosecurity News
Cybercriminals are increasingly using PDFs to deliver malware, with a 7% rise in threats detected in Q4 2023 compared to Q1, according to a HP Wolf Security report


CyberNews
Legal advertising tools are being leveraged by cybercriminals to conceal their illicit campaigns and track victims.


Security Affairs
Microsoft and OpenAI warn that nation-state actors are using ChatGPT to automate some phases of their attack chains.

Krebs on Security
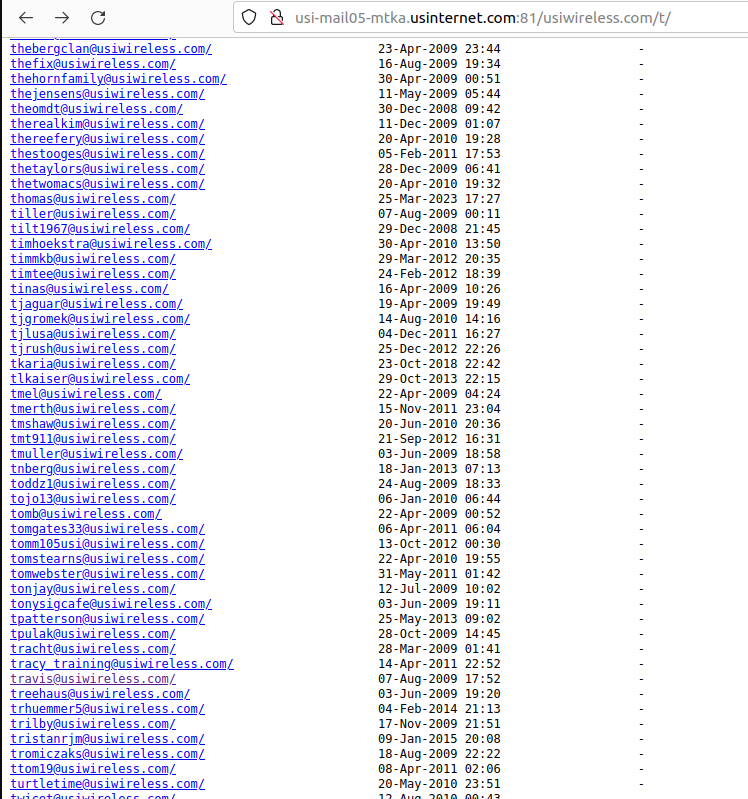
The Minnesota-based Internet provider U.S. Internet Corp. has a business unit called Securence, which specializes in providing filtered, secure email services to businesses, educational institutions and government agencies worldwide. But until it was notified last week, U.S. Internet was publishing…


Cyber Security News
According to the reports shared with Cyber Security News, the threat actor begins the infection chain by delivering the USB drives to the victims by any means of social engineering.


Bleeping Computer
A previously unknown traffic distribution system (TDS) named 'VexTrio' has been active since at least 2017, aiding 60 affiliates in their cybercrime operations through a massive network of 70,000 sites.


SecurityWeek
VexTrio is a massive and complex malicious TDS (traffic direction system) supporting numerous cybercriminal campaigns.


The Cyber Express
Layer7Booter, an IP Stresser previously confined to the dark web, has now surfaced on the open internet. This tool claims


Cyber Security News
Once a serene meadow, the digital landscape has morphed into a battleground where attackers and security vendors engage in a perpetual arms race.


DarkReading
Crimeware-as-a-service (CaaS) gang flies past CAPTCHAs, creating fraudulent accounts to sell to the likes of Scattered Spider; Microsoft mounts a counterattack.


The Record
The tech giant published two warnings about threats from hackers and described how it took down a Vietnam-based marketplace for fraudulent credentials.

HACKRead
Microsoft Threat Intelligence, partnered with cybersecurity firm Arkose’s ACTIR, conducted a large-scale operation against online fraudulent login markets, successfully taking down Hotmailbox.me.


Infosecurity News
Microsoft disrupts Vietnam based threat actor Storm-1152, who has sold 750 million fake accounts


Cyber Security News
Hackers sell fake Microsoft products and accounts because it allows them to profit from illicit activities, taking advantage of unsuspecting users.


The Hacker News
Microsoft takes down a major cybercriminal group, Storm-1152, responsible for distributing 750 million fraudulent Microsoft accounts and tools.


Bleeping Computer
Microsoft's Digital Crimes Unit seized multiple domains used by a Vietnam-based cybercrime group (Storm-1152) that registered over 750 million fraudulent accounts and raked in millions of dollars by selling them online to other cybercriminals.


SC Magazine
Cybercriminals posing as job candidates are luring recruiters to install the “more_eggs” backdoor.


HACKRead
Job seekers and recruiters should be vigilant for malicious emails and messages on LinkedIn, where TA4557 threat actors feign interest in a job, but their actual intent is to deliver a backdoor.


Infosecurity News
Recruiters are warned to educate staff about surge in phishing attacks from threat group TA4557


CyberNews
Change of tactics involves building rapport with intended victims via convincing emails, says cybersecurity firm Proofpoint.


CSO
The new technique has the threat actor email malicious URLs directly to recruiters in response to job postings.


Bleeping Computer
The UK National Cyber Security Centre (NCSC) and Microsoft warn that the Russian state-backed actor "Callisto Group" (aka "Seaborgium" or "Star Blizzard") is targeting organizations worldwide with spear-phishing campaigns used to steal account credentials and data.


HACKRead
Currently, the FjordPhantom malware appears to be active in Southeast Asia, covering countries including Malaysia, Thailand, Indonesia, Singapore, and Vietnam.

HACKRead
The conclusion was reached after researchers evaluated over 9,500 of the largest transactional websites in terms of traffic, encompassing sectors such as banking, e-commerce, and ticketing businesses.


Cyber Security News
Carding attacks primarily target information embedded in payment cards, such as credit or debit cards,The attackers, known as carders.


The Hacker News
Phishing attacks are getting smarter! Cybercriminals are now using QR codes, CAPTCHAs, and steganography to trick victims. Learn how to stay safe.


The Hacker News
Meet "Prolific Puma," the secretive threat actor behind a dangerous link shortening service with thousands of malicious domains used for phishing.


Bleeping Computer
A threat actor that security researchers call Prolific Puma has been providing link shortening services to cybercriminals for at least four years while keeping a sufficiently low profile to operate undetected.


The Record
Low-skill cybercriminals are using a new tool to create hundreds of fake social media accounts in just a few seconds.


Trend Micro
This report explores the Kopeechka service and gives a detailed technical analysis of the service’s features and capabilities and how it can help cybercriminals to achieve their goals.


Ars Technica
If a site is redirecting visitors to scam sites, it was likely hacked by Balada.


The Record
Dubbed LoveGPT by researchers at Avast, the tool can get around dating apps' security measures, send likes, read replies from potential matches and create believable profiles.


Ars Technica
"I'm sure it's a special love code that only you and your grandma know."


Cyber Security News
Magento Security Checklist : 1. Update to the Latest Version 2. Ensure a Strong Password 3. Limit Magento Admin Login Attempts 4. Switch 2FA.


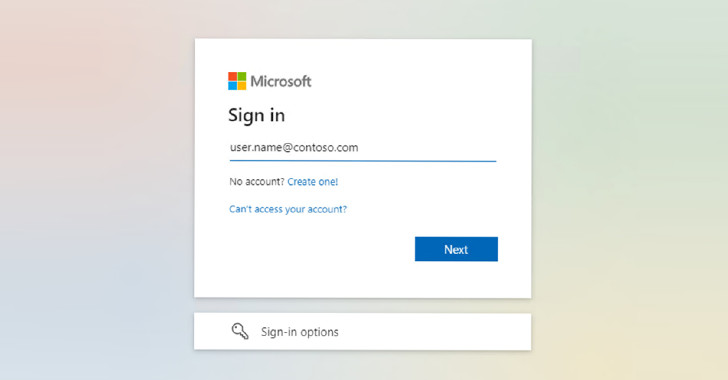
Bleeping Computer
A threat actor known as W3LL developed a phishing kit that can bypass multi-factor authentication along with other tools that compromised more than 8,000 Microsoft 365 corporate accounts.

The Hacker News
ChatGPT and similar AI models are empowering cybercriminals to launch damaging attacks on online businesses. Learn how they're leveraging these tools

Cyber Security News
Tor has officially introduced a Proof-of-Work (PoW) mechanism in order to defend from attackers doing Denial of Service attacks.


Cyber Security News
Threat actors behind these phishing campaigns exploit Cloudflare R2's free hosting service. While apart from this, with the help of two exceptional techniques, the operators evade the scanners and URL analyzers.

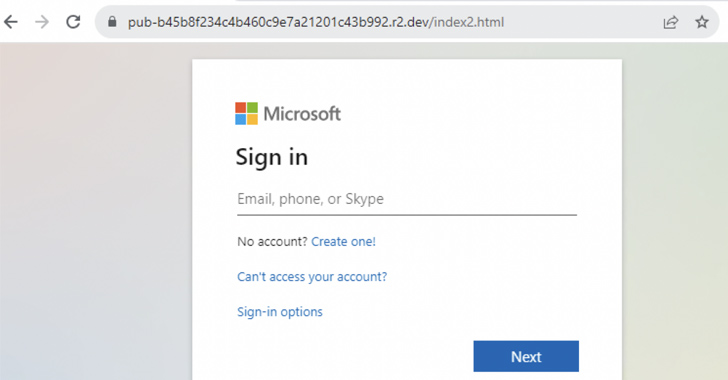
The Hacker News
The use of Cloudflare R2 for hosting phishing pages has surged by 61x in just six months.


Cyber Security News
DDoS attacks pack a punch. The Ponemon Institute estimates that each minute of downtime during a DDoS assault rings in at a whopping $22,000. On top of that, recovery from such an attack can set back a small or midsize business by $120,000. Implementing robust DDoS protection isn’t optional — it’s a necessity. But it’s […]

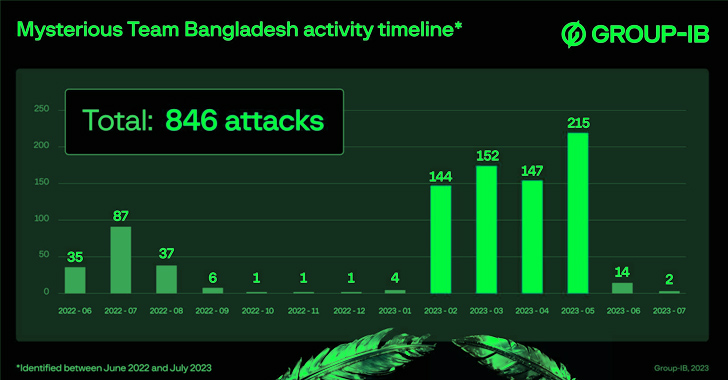
The Hacker News
The enigmatic Team Bangladesh, a group of hacktivists, has carried out over 750 DDoS attacks and defaced 78 websites.


SecurityWeek
Threat actors are using Google AMP URLs in phishing campaigns aimed at enterprises as a new detection evasion tactic.

-1.webp)
Cyber Security News
A new phishing tactic was discovered that takes advantage of Google Accelerated Mobile Pages (AMP), bypassing email security infrastructure.


Bleeping Computer
Security researchers are warning of increased phishing activity that abuses Google Accelerated Mobile Pages (AMP) to bypass email security measures and get to inboxes of enterprise employees.


CSO
HEAT Shield and HEAT Visibility prevent attacks from infiltrating enterprise networks and provide actionable intelligence on threats.


Ars Technica
GPT-4's image capabilities can recognize certain individuals, according to NYT.


The Hacker News
Generative AI poses major security risks to enterprises. Threat actors can exploit it to hack weak SaaS authentication protocols, jeopardizing sensiti


DarkReading
On-demand human solvers are now augmenting automated website cyberattacks, offering a better way around tougher anti-bot puzzles.

The Hacker News
Cybercriminals are breaking CAPTCHAs with ease! Discover the shocking truth behind the rise of CAPTCHA-breaking services


Bleeping Computer
Artificial intelligence has brought forth a new era of innovation. However, its rise has also led to an evolving landscape of emerging cyber threats.


Infosecurity News
Trellix said the businesslike approach of the group shows its organizational maturity


DarkReading
A wide-ranging campaign to inject malicious code into WordPress-run websites has been ongoing for at least five years.


The Hacker News
Summary: Balada Injector has been compromising WordPress sites since 2017, exploiting theme and plugin vulnerabilities.


Security Affairs
Threat actors are abusing the legitimate Adobe Acrobat Sign service to distribute the RedLine information stealer. Avast researchers reported that threat actors are abusing the legitimate Adobe Acrobat Sign service to distribute the RedLine information stealer. Adobe Acrobat Sign allows registered users to sign documents online and send a document signature request to anyone. This […]


Bleeping Computer
Cybercriminals are abusing Adobe Acrobat Sign, an online document signing service, to distribute info-stealing malware to unsuspecting users.


Ars Technica
"ARC's evaluation has much lower probability of leading to an AI takeover than the deployment itself."


Ars Technica
Some forms of multi-factor authentication only go so far in preventing account takeovers.


Infosecurity News
The kit is written in NodeJS and has automated setup and detection evasion capabilities


Security Affairs
Microsoft warns of large-scale phishing attacks orchestrated with an open-source adversary-in-the-middle (AiTM) phishing kit available in the cybercrime ecosystem Adversary-in-the-middle (AiTM) phishing kits are becoming an essential technology in the cybercrime ecosystem that is used by multiple threat actors to launch phishing attacks. AiTM phishing allows threat actors to circumvent multifactor authentication (MFA) through reverse-proxy functionality. […]

The Hacker News
Microsoft Raises Alarm Over Hackers Using Phishing Kits to Send Millions of Malicious Emails Daily

Trend Micro
In this investigation, we analyzed several prominent "passive income" applications and found out that there may be security risks upon participating in these programs.


Cyber Security News
Best Firewall as a Service Provider - Best FWaaS Solutions - 1. Perimeter81 2. Check Point NGFWs 3. Zscaler 4. Palo Alto Networks 5.CrowdSec

The Hacker News
Warning: A massive malware campaign has infected more than 4,500 WordPress websites and is redirecting their visitors to sketchy ad pages.

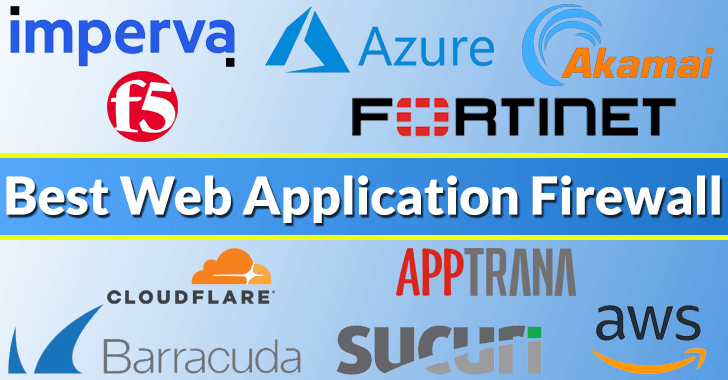
Cyber Security News
Best Web Application Firewall Solutions - 1.AppTrana, 2.Imperva Cloud WAF, 3.Cloudflare WAF, 4.F5 WAF, 5.Azure WAF, 6.Akamai , 7.Fortinet waf


Ars Technica
Exploiting vulnerability with 9.8 severity rating isn't particularly hard.


Bleeping Computer
Over 4,000 Sophos Firewall devices exposed to Internet access are vulnerable to attacks targeting a critical remote code execution (RCE) vulnerability.


CSO
A feature that allows developers to make applications accessible by a public GitHub URL could enable attackers to deliver malware and avoid detection.
Loading more articles....