

Infosecurity News
SugarGh0st RAT Variant Used in Targeted AI Industry Attacks
Proofpoint said the attackers modified registry key names for persistence


Infosecurity News
Proofpoint said the attackers modified registry key names for persistence


SecurityWeek
Palo Alto Networks and IBM have announced a significant partnership to jointly provide cybersecurity solutions.


Trend Micro
This report describes how Waterbear and Deuterbear — two of the tools in Earth Hundun's arsenal — operate, based on a campaign from 2024.

.webp)
Cyber Security News
The well-known advanced persistent threat (APT) group Turla, which is based in Russia, is said to be going after the European Ministry.


Infosecurity News
Several software security experts have told Infosecurity that no new vulnerabilities have been added to the US NVD since May 9


CyberSecurity Dive
The detail and speed with which companies share information after an attack can prevent future pain. But businesses aren’t always keen on transparency.


The Hacker News
Black Basta ransomware-as-a-service (RaaS) operation has targeted over 500 private industry and critical infrastructure entities in North America, Eur


CyberSecurity Dive
The committee wants to question Brad Smith, Microsoft’s president and vice chair, over the company’s security shortcomings and how it plans to strengthen security measures.


CyberNews
The San Francisco division of the FBI is warning individuals and organizations to be aware of AI used by cybercriminals.


Krebs on Security
Last week, the United States joined the U.K. and Australia in sanctioning and charging a Russian man named Dmitry Yuryevich Khoroshev as the leader of the infamous LockBit ransomware group. LockBit's leader "LockBitSupp" claims the feds named the wrong guy,…


DarkReading
CISA's agreement is voluntary and, frankly, basic. Signatories say that's a good thing.

DarkReading
Kevin Mandia, CEO of Mandiant at Google Cloud, calls for watermarks as the industry braces for a barrage of mind-bending AI-generated fake audio and video.


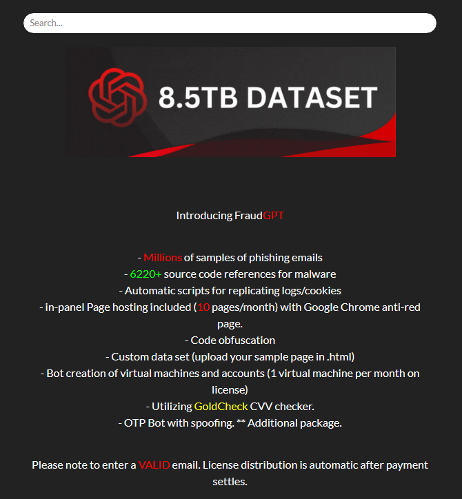
Infosecurity News
Well-funded cybercriminals are adopting more sophisticated techniques, creating a need for defenders to stay informed about the evolving threat landscape


SecurityWeek
Hundreds of companies are showcasing their products and services this week at the 2024 edition of the RSA Conference in San Francisco.


CyberSecurity Dive
CISA Director Jen Easterly pointed to Microsoft’s decision to link security to executive compensation as a meaningful signal of its priorities.


DarkReading
New regulations require companies to turn over incident data to CISA within 3 days or face enforcement. Here's how the agency spins this as a good thing.


The Record
The current cybersecurity situation in the healthcare industry is at least a decade in the making, White House official Anne Neuberger said at the RSA Conference.


The Record
Okta Chief Security Officer David Bradbury discusses lessons from the incident, how nation-state threats are evolving, and how AI is already influencing identity-based attacks.


DarkReading
The latest round of investment prices the fast-growing cloud native application protection platform (CNAPP) at $12 billion with a simple mandate: Grow quickly through acquisition.


Infosecurity News
Experts at the RSA Conference urged cyber professionals to lead the way in securing AI systems today and pave the way for AI to solve huge societal challenges


Infosecurity News
Experts at the RSA Conference discussed what CISOs can do to protect themselves against legal pressure

SecurityWeek
Despite the current lack of large-scale criminal exploitation of gen-AI, researchers highlight indications that this may change.


CyberSecurity Dive
CISA said companies ranging from Microsoft to Palo Alto Networks signed the voluntary pledge in an effort to boost resiliency and increase transparency around CVEs and cyberattacks.


CyberSecurity Dive
Federal officials rarely criticize tech companies when their mistakes result in attacks. The stinging conclusions CSRB levied at Microsoft are an exception, not the norm.


SecurityWeek
Hundreds of companies are showcasing their products and services this week at the 2024 edition of the RSA Conference in San Francisco.


The Cyber Express
Google has brought together its Gemini AI model with its Mandiant cybersecurity unit and VirusTotal threat Intelligence to enhance threat


SC Magazine
A panel of experts unpack the art of cyber insurance here at RSA Conference and share what's new in coverage and claims.


The Record
CISA Director Jen Easterly said the voluntary pledge by software companies is important because of widespread nation-state hacking campaigns, including the Volt Typhoon operation attributed to China.

The Record
Deputy National Security Advisor Anne Neuberger said the incident is an example of the need for more to be done to protect critical infrastructure.


The Record
The wide-ranging hacking campaign by the state-backed group Volt Typhoon is seen as a prelude of what's to come.

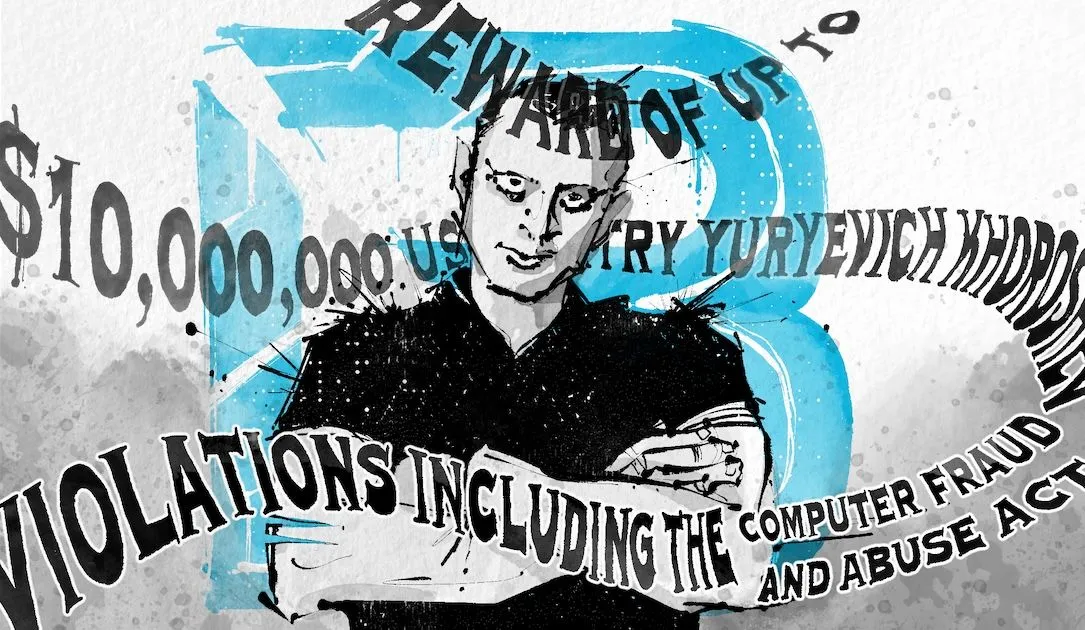
The Record
LockBitSupp, head of the LockBit cybercrime operation, tells the Click Here podcast team that he is not Russian national Dmitry Khoroshev, as claimed by the U.S., U.K. and Australia.


Infosecurity News
Experts at the RSA Conference discussed how governments, the open-source community and end users can work together to drastically improve the security of open-source software


Infosecurity News
CISA launched a new software vulnerability enrichment program to fill the gap left by NIST’s National Vulnerability Database backlog

Infosecurity News
Researchers from Carnegie Mellon University have shared an overview of their new AI Security Incident Response Team (AISIRT)


SecurityWeek
Healthcare cybersecurity company Blackwell Security has raised $13 million and appointed Geyer Jones as its first CEO.


CyberSecurity Dive
A report from the Office of the National Cyber Director highlights persistent threats targeting healthcare and water, echoing warnings from cyber officials earlier this year.


SecurityWeek
Hundreds of companies are showcasing their products and services this week at the 2024 edition of the RSA Conference in San Francisco.


CSO
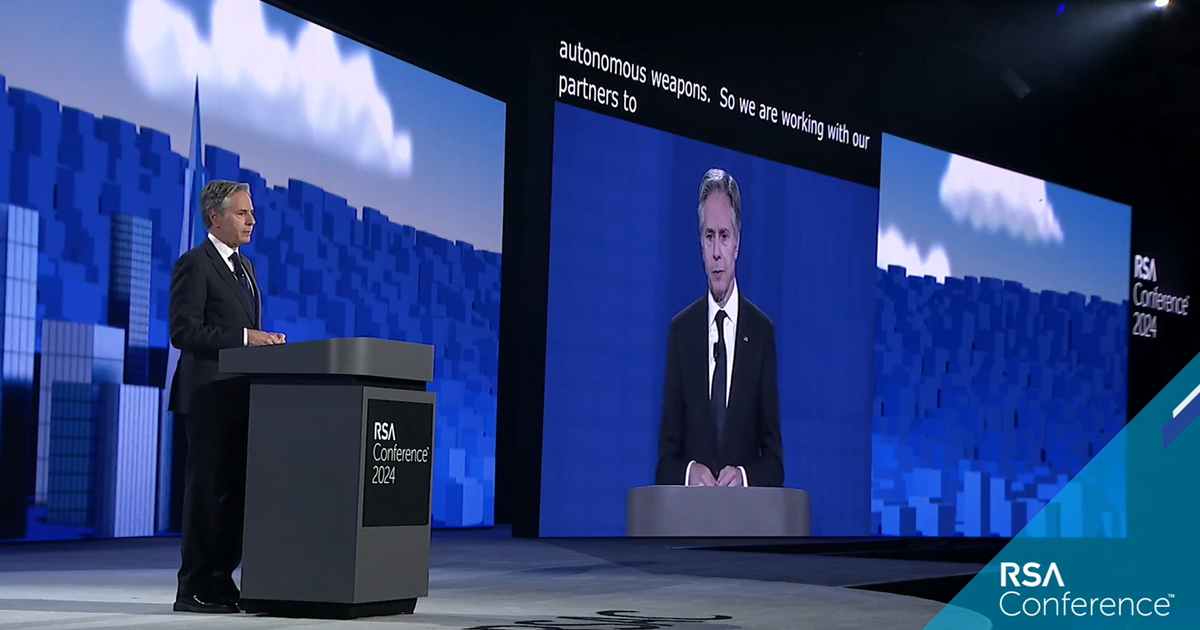
The US government is moving to address the challenges of quantum computing, cloud strategies, and generative AI, Anthony Blinken said in a speech that was light on specifics.


The Record
Industry asked for an extension of the comment period for a key rule on cybersecurity incident reporting, and "in the interest of supporting the community out there, we decided to give them an extra 30 days,” said Brandon Wales, CISA’s executive director, at the 2024 RSA Conference.


The Record
The former U.S. Cyber Command and National Security Agency chief will be the founding director of a national security-focused hub at the Nashville-based campus.

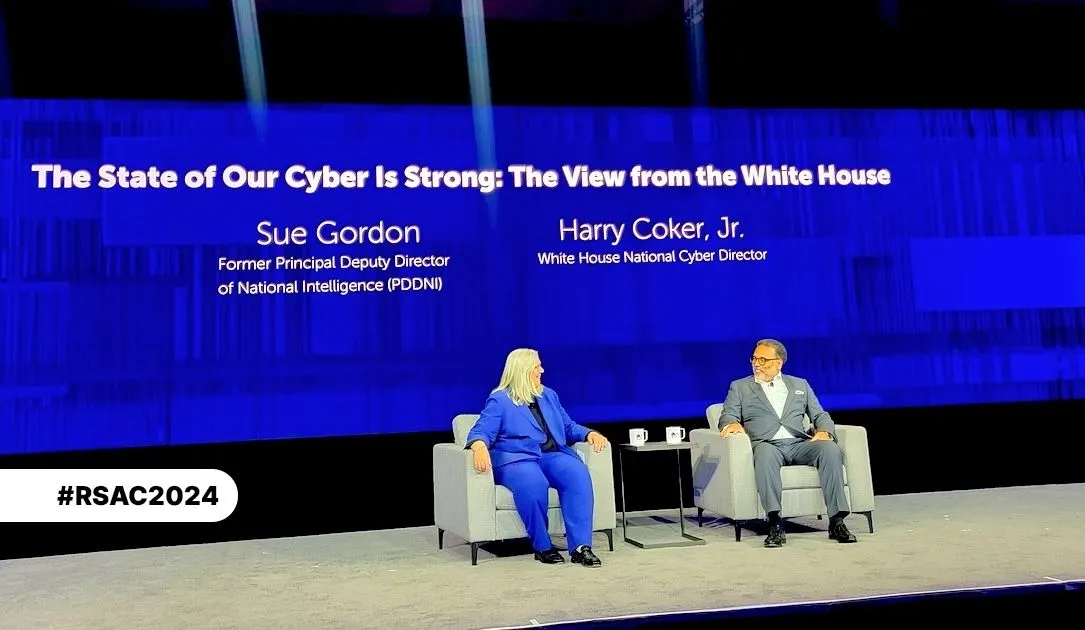
The Record
The Office of the National Cyber Director has had four different leaders in less than a year. The current chief, Harry Coker, says it can move past that turmoil by sticking to its marching orders.


SC Magazine
Zero trust, access certification campaigns and regular AD risk assessments are more critical than ever.


SC Magazine
AI and “secure by design” will be crucial to defend against ransomware, CI attacks and AI threats in the coming years.


The Record
The campaign by Chinese hackers to target U.S. critical infrastructure is intended to “cause disruption and sow societal panic,” a senior cybersecurity official said Tuesday.


Infosecurity News
US government officials discussed plans on how to incentivize security by design principles in the software manufacturing process during RSA


DarkReading
Vulnerabilities added to the CISA known exploited vulnerability (KEV) list do indeed get patched faster, but not fast enough.


DarkReading
A panel of former CISOs will lead the closing session of this week's RSA Conference to discuss challenges and opportunities.

Infosecurity News
A new report by Cato Networks found that exploiting old vulnerabilities in unpatched systems is one of threat actors’ favorite initial access vectors


Infosecurity News
CISOs share their experience of managing real-life cyber incidents provide their recommendations to survive cyber-attacks


The Cyber Express
Cyber Defense Magazine (CDM), marking its 12th anniversary as the leading electronic information security magazine, announced the winners of the

DarkReading
The four goals of the US International Cyberspace and Digital Policy Strategy are to advance economic prosperity; enhance security and combat cybercrime; promote human rights, democracy, and the rule of law; and address other transnational challenges.


The Cyber Express
The U.S. Secretary of State Antony Blinken unveiled an International Cyberspace and Digital Policy Strategy on Monday, outlining the Biden


SecurityWeek
Hundreds of companies are showcasing their products and services this week at the 2024 edition of the RSA Conference in San Francisco.


CyberSecurity Dive
Espionage groups linked to China are heavily exploiting zero days, focusing on devices that lack endpoint detection and response capabilities, one expert said.


The Cyber Express
The RSA Conference 2024, the world's biggest cybersecurity event, is currently underway at the Moscone Center in San Francisco. Over


Infosecurity News
US Secretary of State Antony Blinken said that the US and its allies must ensure foundational technologies are used for the betterment of society


CSO
The new addition to Google Cloud Security is designed to give security teams information to inform approaches to protecting against external threats, managing attack surfaces, and mitigating digital risks.


The Record
Recorded Future News will be providing live coverage from the 2024 RSA Conference in San Francisco.


The Record
The secretary of Homeland Security told an RSA Conference crowd that he was encouraged by the discussion in the first meeting of the department's AI advisory board.


The Record
Nathaniel Fick, the State Department’s ambassador-at-large for cyberspace and digital policy, told reporters at the RSA Conference that U.S. and Chinese officials "did speak about Volt Typhoon directly" during a recent meeting.


The Record
“It's very difficult to dismantle large organizations like this," said Brett Leatherman, deputy assistant director of the FBI’s cyber division.


The Record
"We're working on it," says the Senate Intelligence Committee chairman about the recently renewed law's handling of “electronic communications service providers” — a sticking point for privacy advocates.


SC Magazine
Identity security firm Silverfort shows how an adversary could bypass FIDO2 protections and SSO to hijack a session token for abuse.


SC Magazine
Large language models (LLM) provide context that could expose overlooked threats.


Infosecurity News
Recorded Future’s Alexander Leslie highlights the increasingly blurred lines between hacktivism, financial cybercrime and nation-state activities during the RSA Conference 2024

DarkReading
Large language models promise to enhance secure software development life cycles, but there are unintended risks as well, CISO warns at RSAC.


Infosecurity News
A new Chainalysis report showed that recent law enforcement operations have pushed ransomware affiliates to increasingly use multiple strains in order to stay afloat


SecurityWeek
Google rolls out new threat-intel and security operations products and looks to the magic of AI to tap into the booming cybersecurity market.


The Cyber Express
The RSA conference 2024 , the world's largest cybersecurity gathering, commenced in San Francisco from May 6 to 9, 2024.


The Cyber Express
San Francisco, May 6, 2024 — Cyble, the leading provider of AI-driven cybersecurity solutions, is excited to announce its participation


SC Magazine
RSA Conference will tackle everything AI, but will also go deep on government policy, innovative new security solutions and explore "The Art of Possible."


The Record
U.S. Secretary of State Antony Blinken told the audience at the 2024 RSA Conference in San Francisco about the Biden administration's broad plan to build “digital solidarity” with allies and partners.


SC Magazine
Taking a sober look at where and how offensive and defensive GenAI is being used to keep security professionals on their toes.


SC Magazine
For more real-time RSAC coverage from SC Media please visit here.


SC Magazine
By promoting a vision of cooperation and innovation, the U.S. can best navigate the complexities of AI and quantum computing and safeguard domestic private and public interests, Blinken said.


DarkReading
Actual legislation is a long shot and a decade away, but policy experts are looking to jump-start the conversation around greater legal liability for insecure software products.


SecurityWeek
With so many vendors, approaches and solutions, how do you know what cybersecurity solutions you should be investing in?


SecurityWeek
Cybersecurity startups Insane Cyber, Resonance Security, RunReveal and StepSecurity announce pre-seed, early-stage, and seed funding rounds.


DarkReading
DMARC adoption is more important than ever following Google's and Yahoo's latest mandates for large email senders. This Tech Tip outlines what needs to be done to enable DMARC on your domain.


The Hacker News
Attention SOHO router users! A new malware called Cuttlefish is on the prowl, stealthily monitoring your traffic and stealing authentication data.


DarkReading
Unmanaged and unknown Web services endpoints are just some of the challenges organizations must address to improve API security.


CSO
Tools, platforms, and services that the CSO team recommends 2024 RSA Conference attendees check out.


The Hacker News
ZLoader modular malware trojan has resurfaced with anti-analysis feature that prevents execution on machines different from the original infection.


SecurityWeek
Jennifer Leggio says we need more alcohol-free networking events at conferences, and community-building opportunities for sober individuals.


DarkReading
Our collection of the most relevant reporting and industry perspectives for those guiding cybersecurity strategies and focused on SecOps. Also included: security license mandates; a move to four-day remediation requirements; lessons on OWASP for LLMs.


DarkReading
Attackers will likely use software bills-of-material (SBOMs) for searching for software potentially vulnerable to specific software flaws.


Cyber Security News
Researchers identified a cyberattack by the Sandworm group targeting critical infrastructure in Ukraine in March 2024, which aimed to disrupt

Bleeping Computer
Russian hacker group Sandworm aimed to disrupt operations at around 20 critical infrastructure facilities in Ukraine, according to a report from the Ukrainian Computer Emergency Response Team (CERT-UA).


CyberNews
Researchers observe a flood of crude and amateurish ransomware. But it’s cheap, difficult to trace, and comes in many flavors.

Security Affairs
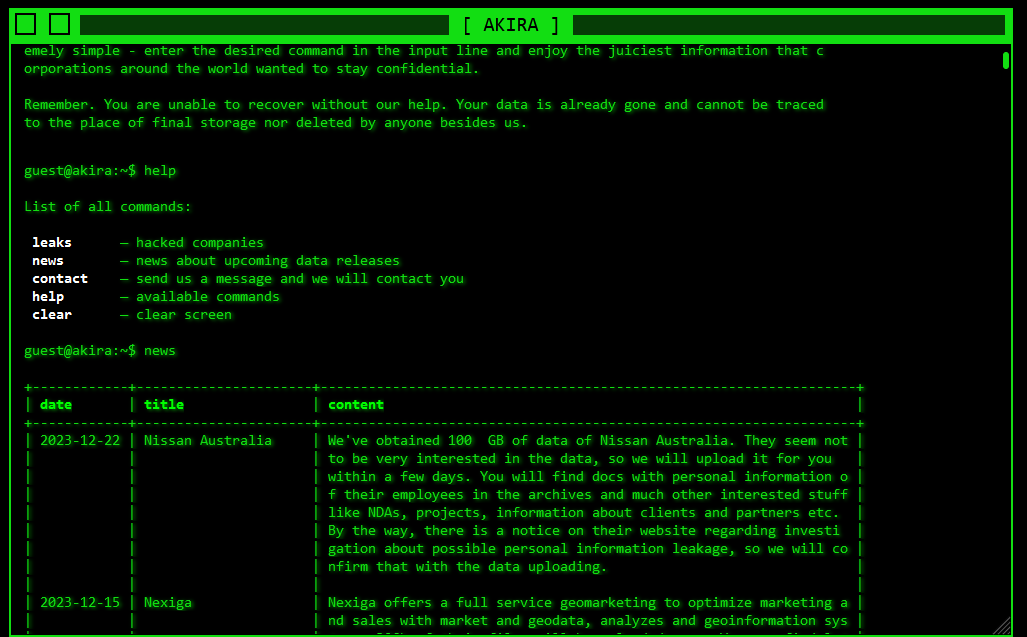
Government agencies revealed that Akira ransomware has breached over 250 entities worldwide and received over $42 million in ransom payments.


DarkReading
SecOps highlights this week include the executive role in "cyber readiness;" Cisco's Hypershield promise; and Middle East cyber ops heat up.


The Cyber Express
The Akira ransomware group has been identified as the culprit behind a series of cyberattacks targeting businesses and critical infrastructure


The Hacker News
Akira Ransomware group has already extorted roughly $42 million from over 250 victims globally. They are now targeting both Windows and Linux systems.


Infosecurity News
The figures come from Egress’s latest report, which also suggests secure email gateways lag behind tech advancements


DarkReading
A third-party telephony service provider for Cisco Duo falls prey to social engineering, and the company advises customer vigilance against subsequent phishing attacks.


SecurityWeek
Startup Knostic emerges from stealth mode with $3.3 million in funding and a gen-AI access control product for enterprises.


Trend Micro
Our blog entry provides an in-depth analysis of Earth Hundun's Waterbear and Deuterbear malware.


Infosecurity News
Proofpoint said this is the first time the threat actor has been seen using LLM-generated PowerShell scripts


Ars Technica
Summer 2023 intrusion pinned to corporate culture, "avoidable errors."


Cyber Security News
The Leading Company for Securing Access Between Workloads Recognized for the Aembit Workload IAM Platform Aembit, the Workload Identity and Access Management (IAM) Company, has been named one of the Top 10 Finalists for the RSA Conference™ 2024 Innovation Sandbox contest for its platform that manages and secures access between critical software resources, like applications […]
Loading more articles....