

SC Magazine
RSA Conference 2024: What to expect
RSA Conference will tackle everything AI, but will also go deep on government policy, innovative new security solutions and explore "The Art of Possible."


SC Magazine
RSA Conference will tackle everything AI, but will also go deep on government policy, innovative new security solutions and explore "The Art of Possible."


HACKRead
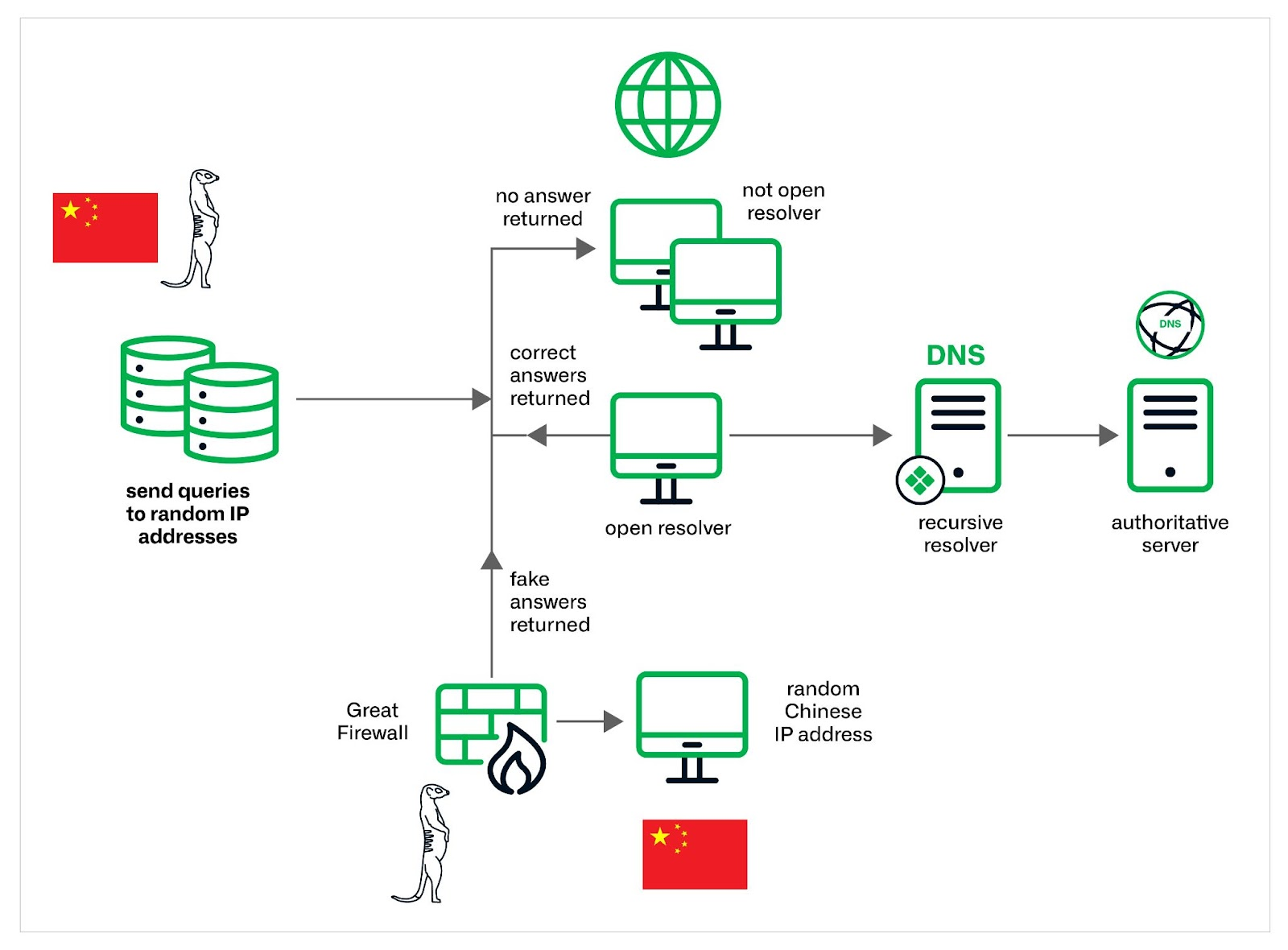
Uncover the "Muddling Meerkat," a China-linked threat actor manipulating the DNS. Infoblox research reveals a sophisticated group with deep DNS expertise and potential ties to the Great Firewall. Learn their tactics and how to stay protected.

Security Affairs
The China-linked threat actors Muddling Meerkat are manipulating DNS to probe networks globally since 2019..


SecurityWeek
Muddling Meerkat conducts operations through DNS by creating large volumes of widely distributed queries that are propagated using open DNS resolvers.


Cyber Security News
Hackers exploit DNS vulnerabilities to redirect users to malicious websites, launch distributed denial-of-service (DDoS) attacks by

Bleeping Computer
A new cluster of activity tracked as "Muddling Meerkat" is believed to be linked to a Chinese state-sponsored threat actor's manipulation of DNS to probe networks globally since October 2019, with a spike in activity observed in September 2023.


DarkReading
Likely China-linked adversary has blanketed the Internet with DNS mail requests over the past five years via open resolvers, furthering Great Firewall of China ambitions. But the exact nature of its activity is unclear.


The Hacker News
The "Muddling Meerkat" threat actor is abusing DNS open resolvers to evade detection and conduct reconnaissance across the globe.


DarkReading
A spate of recent typosquatting attacks shows the scourge of this type of attack is still very much with us, even after decades of cyber defender experience with it.

Infosecurity News
Infoblox said Savvy Seahorse uses fake ChatGPT and WhatsApp bots to lure victims


HACKRead
Savvy Seahorse employs advanced techniques like fake ChatGPT and WhatsApp bots to entice users into high-return investment scams.


Cyber Security News
Cybersecurity researchers unveiled a sophisticated scam operation, "Savvy Seahorse," exploiting victims through advanced DNS manipulation techniques.


CyberNews
A threat actor called Savvy Seahorse creates fake investment platforms, lures in victims through Facebook, and transfers their deposits to a Russian state-owned bank.


Bleeping Computer
A threat actor named Savvy Seahorse is abusing CNAME DNS records Domain Name System to create a traffic distribution system that powers financial scam campaigns.


DarkReading
Petty scammers have figured out how to leverage a core function of DNS in order to maintain scalable, stealthy, pliable malicious infrastructure.


Bleeping Computer
A previously unknown traffic distribution system (TDS) named 'VexTrio' has been active since at least 2017, aiding 60 affiliates in their cybercrime operations through a massive network of 70,000 sites.


SecurityWeek
VexTrio is a massive and complex malicious TDS (traffic direction system) supporting numerous cybercriminal campaigns.


The Hacker News
Massive "Criminal Affiliate Program" Exposed: VexTrio Brokers Traffic for 60+ Cybercriminals, Including ClearFake & SocGholish.


DarkReading
The traffic distribution system supports tens of thousands of malicious domains and cyberattack campaigns that reach far and wide globally.


DarkReading
Malicious insider threats are increasingly becoming a cause for concern among businesses in the United Arab Emirates.


SecurityWeek
Seattle analytics and network detection and response firm secures $100 million in growth funding and adds to its executive team.


The Hacker News
Active malware campaign exploits zero-day vulnerabilities to create a Mirai-based DDoS botnet targeting routers and NVR devices.


The Hacker News
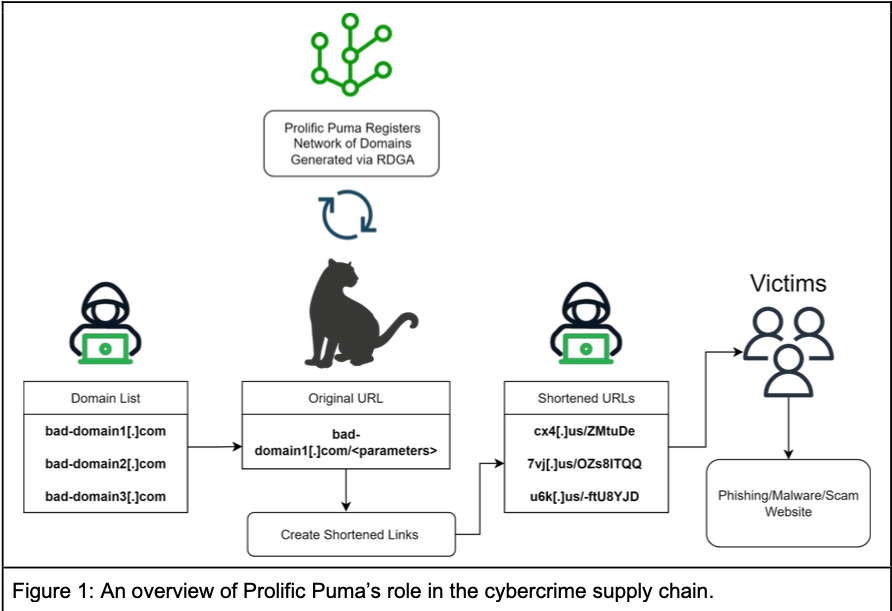
Meet "Prolific Puma," the secretive threat actor behind a dangerous link shortening service with thousands of malicious domains used for phishing.


DarkReading
Cybercriminals are upping their phishing with shortened links and showing that coveted, regulated top-level domains aren't as exclusive as you'd think.


Bleeping Computer
A threat actor that security researchers call Prolific Puma has been providing link shortening services to cybercriminals for at least four years while keeping a sufficiently low profile to operate undetected.

Krebs on Security
The top-level domain for the United States -- .US -- is home to thousands of newly-registered domains tied to a malicious link shortening service that facilitates malware and phishing scams, new research suggests. The findings come close on the heels…


The Hacker News
Decoy Dog, a powerful malware, outperforms the Pupy RAT, featuring previously unknown capabilities.


DarkReading
At least three actors are using the new, improved version, prompting researchers to conclude it was likely developed by a nation-state.

Infosecurity News
Decoy Dog used DNS for C2 and is suspected to be employed in ongoing nation-state cyber-attacks


Bleeping Computer
New details have emerged about Decoy Dog, a largely undetected sophisticated toolkit likely used for at least a year in cyber intelligence operations, relying on the domain name system (DNS) for command and control activity.


Infosecurity News
The latest study from Infosecurity Europe exhibitor Infoblox reveals that cyber-attacks using lookalike domains are on the rise


Infosecurity News
The British tech trade association called for more collaboration between government and industry actors to improve the security of critical sectors


DarkReading
Watch News Desk interviews with Dark Reading and cybersecurity leaders as they discuss trends and industry drivers druing RSA Conference 2023 in San Francisco.


Security Affairs
Infoblox researchers discovered a new sophisticated malware toolkit, dubbed Decoy Dog, targeting enterprise networks. While analyzing billions of DNS records, Infoblox researchers discovered a sophisticated malware toolkit, dubbed Decoy Dog, that was employed in attacks aimed at enterprise networks. Threat actors behind the malware were observed using known tricks to avoid detection such as registering a domain, […]


The Hacker News
Newly discovered malware toolkit, Decoy Dog, is highly sophisticated and evasive, using strategic domain aging and DNS query dribbling.


Latest Hacking News
A new malware tool kit, “Decoy Dog,” has been actively targeting enterprise networks for a year. The researchers identified Decoy Dog after analyzing billions of DNS queries. Decoy Dog Malware Actively Targeting Enterprises Sharing the details in


Bleeping Computer
A new enterprise-targeting malware toolkit called 'Decoy Dog' has been discovered after inspecting anomalous DNS traffic that is distinctive from regular internet activity.


ZDNet
Some 65% of organisations in Singapore have experienced at least six cybersecurity incidents in the past year, but just 49% are able to respond to threats within a day, compared to an average of 70% across 11 global markets.


CyberScoop
The scams have picked up on Telegram.