

SecurityWeek
Token Security Raises $7 Million Seed Funding for Machine-First Identity Security
Tel Aviv-based Token Security has emerged from stealth with $7 million seed funding led by TLV Partners with participation from SNR and angel investors.


SecurityWeek
Tel Aviv-based Token Security has emerged from stealth with $7 million seed funding led by TLV Partners with participation from SNR and angel investors.


SecurityWeek
Venafi’s 90-Day TLS Readiness solution enhances its existing technology to provide full, demonstrable, and visible compliance with the coming 90-day mandate.

SecurityWeek
Quantum decryption will make all certificates and everything else using RSA encryption vulnerable to everyone.


Security Affairs
This is the advantage of Data Detection and Response (DDR) for organizations aiming to build a real-time data defense.


SecurityWeek
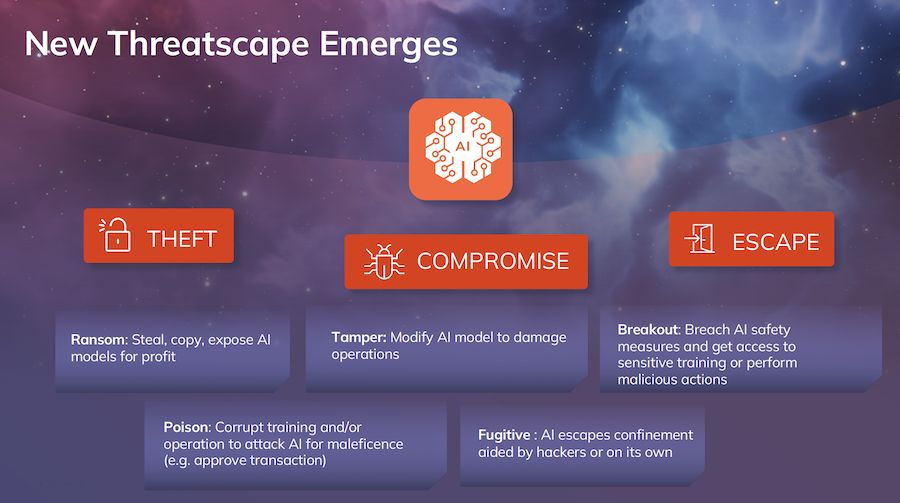
AI's progress in 2024 and beyond: 2023 was a year of hype, 2024 brings the beginning of AI reality, and 2025 likely to be its delivery.


SecurityWeek
Nozomi extends its offering with Guardian Air, a security sensor designed to help organizations detect wireless threats in OT and IoT.

SecurityWeek
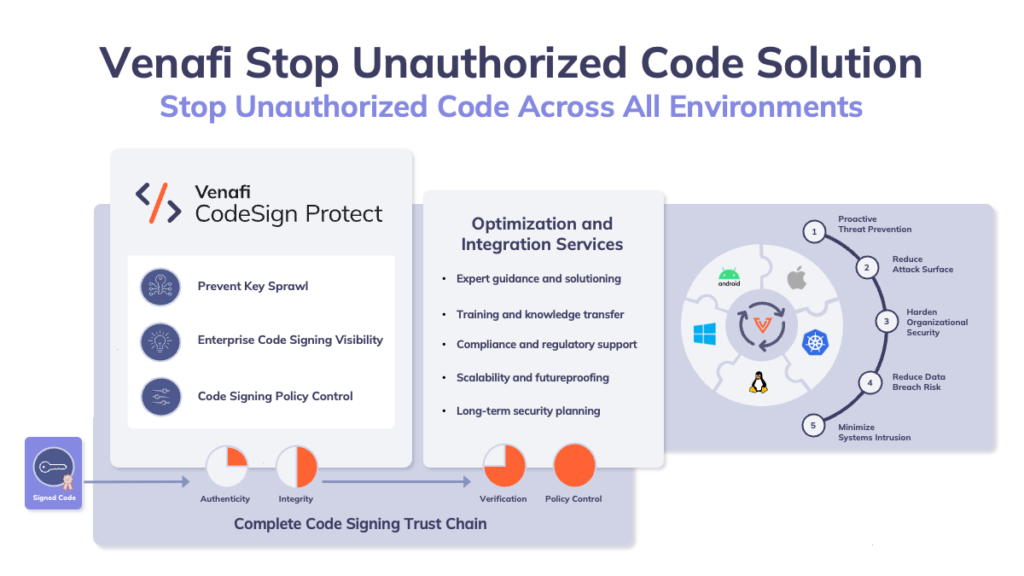
Products from Venafi and Protect AI aim to secure traditional open source software supply chain and the new AI model software supply chain.


CSO
The new code sign enforcement offering will streamline code authorization to root out malicious third-party scripts.


Infosecurity News
Many say it led to a subsequent data breach


CSO
More than half of security leaders surveyed didn’t understand the security risks associated with shifting to the cloud.


CSO
Venafi’s Athena, based on a new large language model (LLM), offers users a natural language interface and provides developers with automated code generation for important integrations.

SecurityWeek
Venafi launched a proprietary generative AI model to help with the mammoth, complex, and expanding problem of managing machine identities.


Infosecurity News
Experts welcome efforts to safeguard society from emerging technologies


Infosecurity News
The European Parliament adopted the latest draft of the legislation with an overwhelming majority


Security Affairs
Knowing that insider threats are a risk is one thing. Knowing how to fight them off is entirely another. Dealing with issues of insider cyber risk can be different and nuanced. It’s hard to admit that someone from within the company could ‘not be who they say they are’, and it takes a group effort […]


Infosecurity News
Attempt to trick network defenders into allow-listing remote access app


Infosecurity News
Revoking these certificates will invalidate some versions of GitHub Desktop for Mac and Atom


The Record
The FBI accused the notorious North Korean hacker group Lazarus of stealing $100 million from a United States-based cryptocurrency firm last year.


Infosecurity News
The North Korean cyber actors laundered over $60m worth of Ethereum stolen during the heist

SecurityWeek
Thoma Bravo’s shopping spree in the cybersecurity lane is showing no signs of slowing down.


Bleeping Computer
The dark web is getting darker as cybercrime gangs increasingly shop their malware, phishing, and ransomware tools on illegal cybercrime markets.


DarkReading
As ransomware's prevalence has grown over the past decade, leading ransomware groups such as Conti have added services and features as part of a growing trend toward professionalization.


Infosecurity News
The NCSC guidance has been issued amid a significant increase in supply chain attacks in recent years


CyberSecurity Dive
Cloud can give companies insight into current and future threats as the landscape grows more complex, said Bret Arsenault.

SecurityWeek
Report shows that forty-five percent of companies have had four or more cloud incidents in the last year


CyberSecurity Dive
Security leaders consider the risk of cloud-based incidents higher than on-premises incidents, yet they expect to move more applications to the cloud.


Infosecurity News
The use of machine identity tools is growing in state-sponsored cyber-attacks

SecurityWeek
More than three-quarters of security professionals in large organizations believe the world is now in a state of perpetual cyberwar – and 82% consider that geopolitics and cybersecurity are fundamentally linked.


DarkReading
For the right price, threat actors can get just about anything they want to launch a ransomware attack — even without technical skills or any previous experience.


Infosecurity News
North Korea stole millions of dollars in crypto assets in at least one major hack


Infosecurity News
The findings uncovered 475 web pages of elaborate ransomware products and services


Security Affairs
Passwords no longer meet the demands of today’s identity and access requirements. Therefore, strong authentication methods are needed. “Usernames and passwords are insufficient and vulnerable means of authentication on their own; therefore, it is essential to employ strong authentication techniques like multi-factor authentication (MFA) to confirm users’ identities before granting secure access to resources,” Sarah […]


DarkReading
North Korean state-sponsored actors, who help economically prop up Kim Jong Un's dictatorship, continue to pummel US infrastructure.


CyberSecurity Dive
Executives are implementing new strategies to lower software supply chain risk, but evaluating internal operations could prove more effective.

SecurityWeek
The US government has warned that rogue IT workers from North Korea enable DPRK hacking operations and provide logistical support for its threat actors.


Infosecurity News
North Korean IT workers are attempting to generate revenue for DPRK and conduct cyber intrusions

SecurityWeek
API security firm Corsha has raised $12 million in a Series A funding round led by Ten Eleven Ventures and Razor’s Edge Ventures.


Security Affairs
This post explains what is a credential stuffing attack and which are the countermeasures to prevent them. A credential stuffing attempt can be caught as a behavioral anomaly – if you’re looking. Earmarked by the FBI as a particular threat to the financial service industry just over a year ago, the increase of internet traffic, […]


DarkReading
Microsoft meanwhile confirms Lapsus$ group compromised it as well and issues warning on threat actor.


Infosecurity News
Online chatter suggests chip giant “hacked back” at its attacker


DataBreaches
Who would have thought that criminals might lie? Where’s my shocked face? Bill Toulas reports on findings from a survey by Venafi. Here is some of what...

Bleeping Computer
A global survey that looked into the experience of ransomware victims highlights the lack of trustworthiness of ransomware actors, as in most cases of paying the ransom, the extortion simply continues.