

Cyber Security News
Malware Families Adapting To COM Hijacking Technique For Persistence
COM (Component Object Model) hijacking is a technique in which threat actors exploit the core architecture of Windows by adding a new value on


Cyber Security News
COM (Component Object Model) hijacking is a technique in which threat actors exploit the core architecture of Windows by adding a new value on


DataBreaches
Com Sivesind writes: SolarWinds Corporation, which suffered a major breach of its Orion software platform in December 2020, submitted a U.S. Securities and...


Bleeping Computer
Microsoft Sharepoint and OneDrive for Business were briefly interrupted today after a German TLS certificate was mistakenly added to the main .com domains for the Microsoft 365 services.


Security Affairs
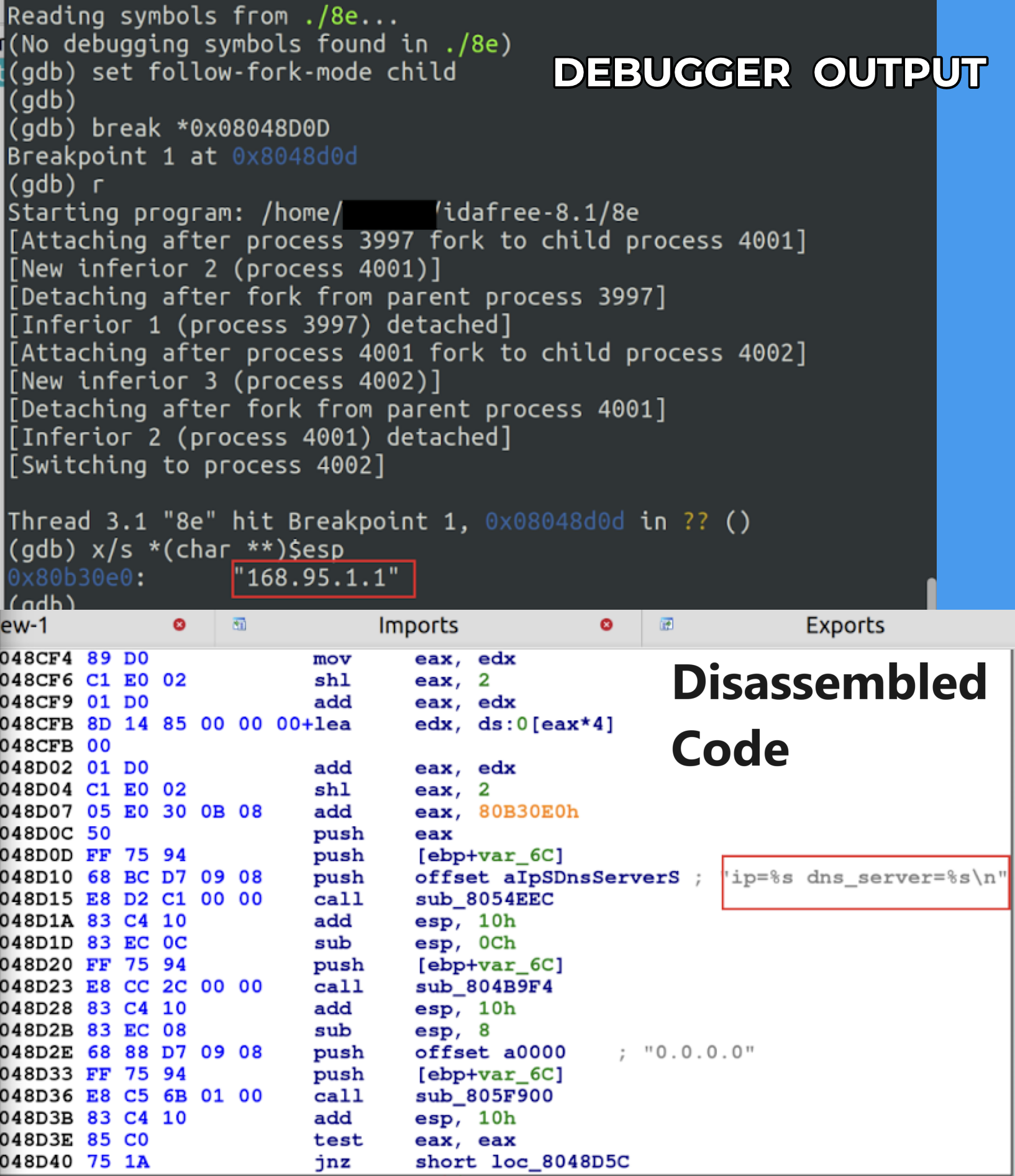
An international law enforcement operation seized the infrastructure associated with the NetWire RAT and resulted in the arrest of its administrator. A coordinated international law enforcement operation resulted in the seizure of the infrastructure associated with the NetWire RAT, the police also arrested its administrator. Law enforcement seized the website www.worldwiredlabs[.]com and its alleged administrator, […]


The Hacker News
A new malware called "Cuckoo" is on the loose, targeting both Intel and ARM-based Macs.


Security Affairs
Experts uncovered a mass Magecart campaign that compromised over 500 e-store running the Magento 1 eCommerce platform. Researchers from cybersecurity firm Sansec uncovered a massive Magecart campaign that already compromised more than 500 online stores running the Magento 1 eCommerce platform. Threat actors behind this campaign deployed a digital skimmer that was being loaded from the naturalfreshmall(.)com domain. […]

.webp)
Cyber Security News
Cybersecurity researchers have uncovered a new malware strain dubbed "Cuckoo., exhibits characteristics of both spyware and an infostealer


CyberNews
Arm and Intel-based Macs are being targeted by a new dangerous malware, dubbed Cuckoo.


Cyber Security News
a previously undetected malware threat for macOS that exhibits characteristics of both an infostealer and spyware.

Bleeping Computer
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has updated the alert on Conti ransomware with indicators of compromise (IoCs) consisting of close to 100 domain names used in malicious operations.


The Hacker News
The "Muddling Meerkat" threat actor is abusing DNS open resolvers to evade detection and conduct reconnaissance across the globe.


Bleeping Computer
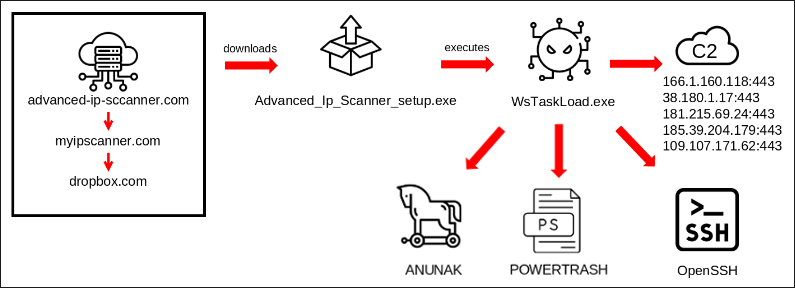
A digitally signed and trojanized version of the 3CX Voice Over Internet Protocol (VOIP) desktop client is reportedly being used to target the company's customers in an ongoing supply chain attack.


Trend Micro
In late March 2023, security researchers revealed that threat actors were actively abusing a popular business communication software from 3CX.


Bleeping Computer
A digitally signed and trojanized version of the 3CX Voice Over Internet Protocol (VOIP) desktop client is reportedly being used to target the company's customers in an ongoing supply chain attack.

Bleeping Computer
The collapse of the Silicon Valley Bank (SVB) on March 10, 2023, has sent ripples of turbulence throughout the global financial system, but for hackers, scammers, and phishing campaigns, it's becoming an excellent opportunity.


The Hacker News
U.S. government seizes 17 website domains and confiscates $1.5 million linked to North Korean IT workers in a massive global fraud scheme


Cyber Security News
Cyble Research & Intelligence Labs (CRIL) discovered a brand-new malware variant called "Rhadamanthys Stealer." This malware stealer variation is now in use and the threat actors who created it are offering it for sale via the Malware as a Service (MaaS) business model.


Bleeping Computer
Hackers are conducting a massive black hat search engine optimization (SEO) campaign by compromising almost 15,000 websites to redirect visitors to fake Q&A discussion forums.


Cyber Security News
The attackers exploited iMessage's zero-click exploits, allowing them to install malware on the devices without any user interaction.


Cyber Security News
Researchers recently conducted an investigation and uncovered alarming information regarding 13 Facebook pages and accounts. These pages and profiles have been compromised by the threat actors, and the most shocking thing about these pages and accounts, they have more than 500k active followers. These compromised pages/accounts were exploited by the threat actors with the help […]


The Cyber Express
A recent analysis by Cyble has revealed a concerning escalation in the fake e-shop campaign, signaling a looming threat to

Cyber Security News
Hackers often target XLSX, HTML, and PDF files as they are widely used and their trustable file formats also attract them.


Cyber Security News
A new phishing campaign targeting Instagram users has been discovered which uses several different techniques to lure victims.


Bleeping Computer
Users of Monzo, one of the UK's most popular digital-only banking platforms, are being targeted by phishing messages supported by a growing network of malicious websites.


Cyber Security News
Threat actors behind this group are actively exploiting the CapraRAT Android malware to hijack Android devices by mimicking the YouTube app.


Cyber Security News
A Chinese state-sponsored cyber-espionage campaign, attributed to TAG-74, targeted South Korean academic, political, and government bodies primarily linked to Chinese military intelligence.


Security Affairs
The Balada Injector is still at large and still evading security software by utilizing new domain names and using new obfuscation. During a routine web monitoring operation, we discovered an address that led us down a rabbit hole of WordPress-orientated “hack waves” caused by the Balada Injector malware. This evidence suggests that the malware is […]

Krebs on Security
One of the largest cybercrime services for laundering stolen merchandise was hacked recently, exposing its internal operations, finances and organizational structure. Here’s a closer look at the Russia-based SWAT USA Drop Service, which currently employs more than 1,200 people across…


Cyber Security News
Cybersecurity analysts at Kaspersky Labs recently discovered Coyote malware that leverages the NodeJS to attack users of more than 60 banks.


The Hacker News
A now-patched vulnerability in Microsoft Edge could have allowed attackers to covertly install browser extensions without user consent.


CSO
Security researchers have found that threat actors have already registered suspicious domains and pages to carry out the attacks.


The Hacker News
FBI has charged 6 individuals and seized 48 domains linked to DDoS-for-hire service platforms


Cyber Security News
Remote assist tools are often targeted by hackers as they create a direct channel that can be used to get into desired systems while using


Bleeping Computer
A new SEO poisoning campaign is underway, dropping the Batloader and Atera Agent malware onto the systems of targeted professionals searching for productivity tool downloads, such as Zoom, TeamViewer, and Visual Studio.


Cyber Security News
Malicious stockpiled domains are the collection of domain names that are acquired by threat actors in advance for several types.


Cyber Security News
The Russia-based threat group TAG-70 has been discovered to be exploiting Roundcube webmail servers with a recently disclosed Cross-Site Scripting vulnerability CVE-2023-5631.

.webp)
Cyber Security News
Cybersecurity researchers at Malwarebytes recently identified a malicious campaign that mimics the WindowsReport.com portal.


Cyber Security News
Threat actors hijack routers to gain unauthorized access to network traffic. This enables them to monitor, manipulate, or intercept sensitive


Cyber Security News
A new backdoor written in Rust has been discovered to be targeting macOS users which has several interesting features.


Cyber Security News
Coinbase, the renowned cryptocurrency exchange platform, has reported that during the recent security breach, the perpetrator managed to obtain contact information associated with several employees.

Krebs on Security
A cybercrook who has been setting up websites that mimic the self-destructing message service Privnote.com accidentally exposed the breadth of their operations recently when they threatened to sue a software company. The disclosure revealed a profitable network of phishing sites…


Cyber Security News
Hackers always keep evolving their tools to stay ahead of defense systems and exploit new vulnerabilities.


Cyber Security News
Hackers have manipulated a popular Notepad++ plugin, injecting malicious code that compromises users' systems upon execution.

Bleeping Computer
Nothing attracts a scammer more than money, and with the NFT craze generating a ton of sales, threat actors are trying to capitalize on it.


Trend Micro
In this blog post, we discuss the technical details of a new banking dropper that we have dubbed DawDropper, give a brief history of banking trojans released in early 2022 that use malicious droppers, and elaborate on cybercriminal activities related to DaaS in the deep web.


Bleeping Computer
The US Department of Justice has seized two Internet domains used in recent phishing attacks impersonating the U.S. Agency for International Development (USAID) to distribute malware and gain access to internal networks.

.webp)
Cyber Security News
A new threat activity has been discovered which relates to the Iran-Nexus espionage activity that targets Aerospace, Aviation and defense

Cyber Security News
Google Ads is a big platform with a wide user base which makes it attractive for threat actors who want to reach many targets at once.


Security Affairs
Security experts from ESET, have temporarily disrupted the operations of the RedLine Stealer with the help of GitHub. ESET researchers announced to have temporarily disrupted the operations of the RedLine Stealer with the help of GitHub. The two companies teamed up with Flare to curb the operations of the malware operators. The experts discovered that […]

Cyber Security News
BlueCharlie is a Russia-linked threat group that has been active since 2017 and associated with several other names.


The Hacker News
The United States Treasury, FBI, and CISA warn against North Korean hackers targeting blockchain companies.


Ars Technica
People who use WordPress should check their sites for unpatched plugins.

Cyber Security News
Researchers from Perception Point identified a new malware campaign, PhantomBlu, targeting US organizations that use novel techniques to deploy NetSupport RAT, a remote access trojan, by exploiting legitimate features of Microsoft Office document templates via OLE manipulation. It allows the attackers to evade detection and gain control of victim machines for various malicious activities, including […]


Ars Technica
It's not clear precisely how the WordPress sites become infected in the first place.


Trend Micro
We break down a new cyberespionage campaign deployed by a cybercriminal group we named Earth Estries. Analyzing the tactics, techniques, and procedures (TTPs) employed, we observed overlaps with the advanced persistent threat (APT) group FamousSparrow as Earth Estries targets governments and organizations in the technology sector.


Cyber Security News
A cyber attack campaign targeting WordPress websites has recently caused significant concern, with experts estimating that up to one million websites may have been compromised.


CyberNews
The supermassive leak contains data from numerous previous breaches, comprising an astounding 12 terabytes of information, spanning over a mind-boggling 26 billion records. The leak is almost certainly the largest ever discovered.


Cyber Security News
The failure of Silicon Valley Bank (SVB) on March 10, 2023, as a result of a bank run on its deposits, is expected to have a significant impact.

Cyber Security News
Researchers at eSentire have identified a shady piece of malware downloader, BatLoader, that has been engaged in a wicked campaign of exploiting Google Ads to distribute malicious secondary payloads


Cyber Security News
Cloud cryptojacking disguises itself as cloud computing resource abuse, where threat actors exploit legitimate tenants for cryptocurrency mining.


The Hacker News
Threat actors are increasingly mimicking popular legitimate applications like Skype, Adobe Reader, and VLC Player in malware attacks.


Cyber Security News
Hackers target 7ZIP due to its widespread use and popularity, making it a lucrative vector for spreading malware.

Trend Micro
We discuss the Batloader malware campaigns we observed in the last quarter of 2022, including our analysis of Water Minyades-related events (This is the intrusion set we track behind the creation of Batloader).


Bleeping Computer
North Korean hackers are using a new version of the DTrack backdoor to attack organizations in Europe and Latin America.


Bleeping Computer
A new multi-platform backdoor malware named 'SysJoker' has emerged in the wild, targeting Windows, Linux, and macOS with the ability to evade detection on all three operating systems.

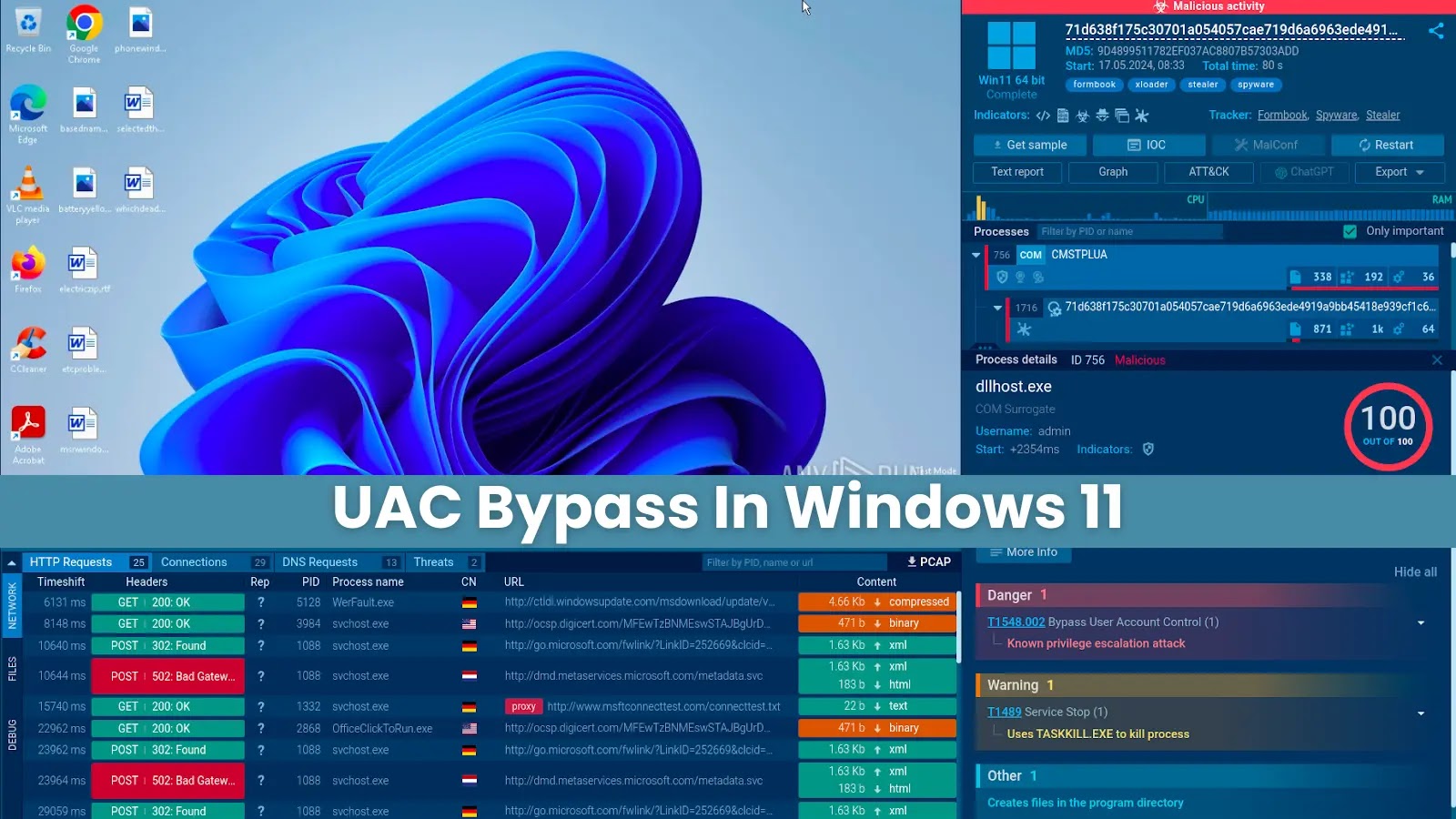
Cyber Security News
User Account Control (UAC) is one of the security measures introduced by Microsoft to prevent malicious software from executing without the user's knowledge.


Bleeping Computer
A new multi-platform backdoor malware named 'SysJocker' has emerged in the wild, targeting Windows, Linux, and macOS with the ability to evade detection on all three operating systems.


Cyber Security News
A new malware called ZenRAT has been discovered. This malware is being spread via fraudulent download packages disguised as Bitwarden installations.

Cyber Security News
Cybersecurity researcher, Aziz Farghly recently discovered an infostealer, "Stealc." Plymouth has promoted Stealc, a new non-resident stealer


CyberNews
Copyright-protected music was available for downloading or streaming on each of the six websites from the Eastern District of Virginia.

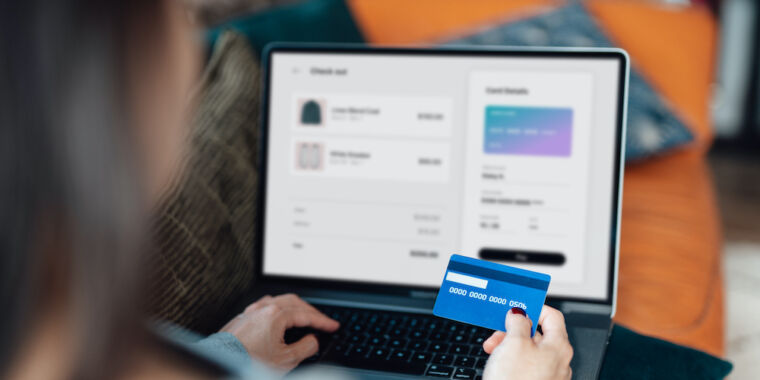
Ars Technica
Magecart hackers strike again.


Bleeping Computer
A new malware distribution campaign is underway impersonating the CapCut video editing tool to push various malware strains to unsuspecting victims.


The Hacker News
BlueCharlie, a Russian adversary associated with Russia's Federal Security Service, has resurfaced with 94 new domains.


Bleeping Computer
GitHub is warning of an ongoing phishing campaign that started on September 16 and is targeting its users with emails that impersonate the CircleCI continuous integration and delivery platform.


DataBreaches
Joseph Menn reports on the group of hackers some have called “Scattered Spider:” … New research being presented Friday at the LABScon...


Bleeping Computer
A massive, malicious campaign is underway using over 200 typosquatting domains that impersonate twenty-seven brands to trick visitors into downloading various Windows and Android malware.

.webp)
Cyber Security News
Google Chrome has been the dominant web browser for years now, which is why it may come as a surprise to hear of a startup.

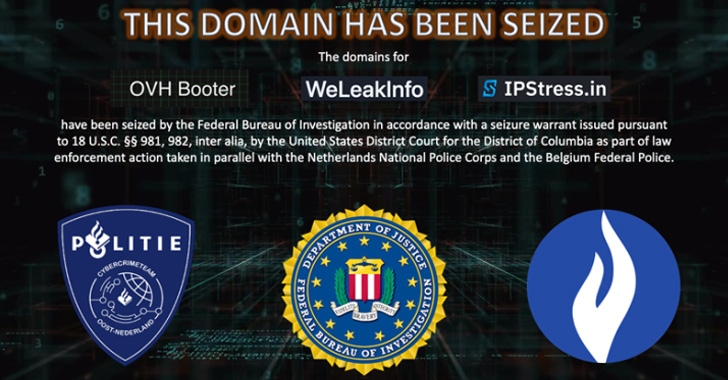
The Hacker News
U.S. Department of Justice seizes three web domains used by cybercriminals to trade stolen information and offer DDoS services.


Bleeping Computer
Fake cryptocurrency giveaways are stealing millions of dollars simply by replaying old Elon Musk and Jack Dorsey Ark Invest videos on YouTube.


Cyber Security News
PDF files are commonly used for their versatility, making them a prime target for malware delivery because they can embed malicious scripts or links.


Bleeping Computer
Coinbase cryptocurrency exchange platform has disclosed that an unknown threat actor stole the login credentials of one of its employees in an attempt to gain remote access to the company's systems.

.png)
Cyber Security News
Threat actors target Notepad++ as it is a widely used text editor among developers and users, offering a large potential victim pool.


Security Affairs
Russia-linked APT group BlueCharlie was observed changing its infrastructure in response to recent reports on its activity. Researchers from Recorded Future reported that Russia-linked APT group BlueCharlie (aka Blue Callisto, Callisto, COLDRIVER, Star Blizzard (formerly SEABORGIUM), ColdRiver, and TA446) continues to change its attack infrastructure following recent reports on its activity. The APT group has […]


The Hacker News
Researchers have discovered a new high-severity vulnerability in the Amazon Ring app for Android, allowing rogue apps to access sensitive information


The Hacker News
Chinese users searching for Notepad++ & VNote on engines like Baidu face malicious ads leading to fake versions with trojans.


Trend Micro
Trend Micro collaborates with INTERPOL to defend FIFA World Cup by preventing attacks & mitigating risks to fight against the rising threat of cybercrime.


Bleeping Computer
The U.S. Justice Department and international partners dismantled the 911 S5 proxy botnet and arrested 35-year-old Chinese national YunHe Wang, its administrator.


Security Affairs
Iran-linked threat actor Tortoiseshell targeted shipping, logistics, and financial services companies in Israel with watering hole attacks. ClearSky Cyber Security uncovered a watering hole attack on at least eight Israeli websites belonging to shipping, logistics, and financial services companies and attributed them with low confidence to the Iran-linked APT group Tortoiseshell (aka TA456 or Imperial […]


Cyber Security News
The persistent search for money and the threat actors becoming more sophisticated are driving the alarming rate of malware change.


Bleeping Computer
Fake cryptocurrency giveaways are stealing millions of dollars simply by replaying old Elon Musk and Jack Dorsey Ark Invest videos on YouTube.

Security Affairs
A new Linux variant of the remote access trojan (RAT) BIFROSE (aka Bifrost) uses a deceptive domain mimicking VMware.

Security Affairs
BlackBerry reported that financially motivated group FIN7 targeted the IT department of a large U.S. carmaker with spear-phishing attacks.


The Hacker News
Hacker using fraudulent domains masquerading Microsoft Windows 11 download portal to trick users into installing the Vidar malware.


Cyber Security News
TA450, also recognized by aliases such as MuddyWater, Mango Sandstorm, and Static Kitten, has been reported to employ a new strategy in its phishing campaigns.


Bleeping Computer
TikTok is flooded by a surge of fake cryptocurrency giveaways posted to the video-sharing platform, with almost all of the videos pretending to be themes based on Elon Musk, Tesla, or SpaceX.

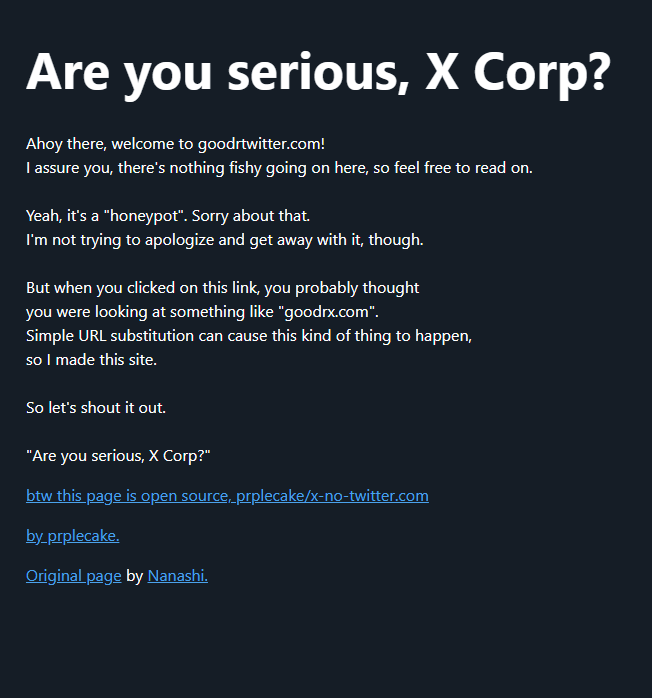
Krebs on Security
On April 9, Twitter/X began automatically modifying links that mention "twitter.com" to redirect to "x.com" instead. But over the past 48 hours, dozens of new domain names have been registered that demonstrate how this change could be used to craft…

.webp)
Cyber Security News
Investigation unveiled a trend of fake trading apps on Google Play and the App Store, unsuspecting users out of their hard-earned money.


Bleeping Computer
A new phishing campaign impersonating the United States Department of Labor asks recipients to submit bids to steal Office 365 credentials.

-1.webp)
Cyber Security News
SysJoker malware was initially discovered to be used by the APT group dubbed "WildCard" and was targeting the educational sector of Israel.


Bleeping Computer
Interpol, in coordination with the Nigerian Police Force, have arrested eleven individuals who are suspects of participating in an international BEC (business email compromise) ring.
Loading more articles....