

SC Magazine
Scammers offer cash to phone carrier staff to swap SIM cards
T-Mobile and Verizon workers report receiving text messages offering them up to $300 for each illegal SIM swap they complete.


SC Magazine
T-Mobile and Verizon workers report receiving text messages offering them up to $300 for each illegal SIM swap they complete.


SC Magazine
A “cascade of security failures” allowed China’s top cyberespionage operatives to steal high-level U.S. government emails last year.


DarkReading
Several Apple device users have experienced recent incidents where they have received incessant password reset prompts and vishing calls from a number spoofing Apple's legitimate customer support line.


Ars Technica
Rapid-fire prompts sometimes followed with spoofed calls from "Apple support."


SecurityWeek
Artificial intelligence computing giant NVIDIA patches two security bugs in ChatRTX for Windows, warning of risk of code execution attacks.


CyberNews
Apple users are being targeted by MFA bombing attacks, also known as push notification spam. Bad actors might be exploiting a bug in Apple’s password reset feature.

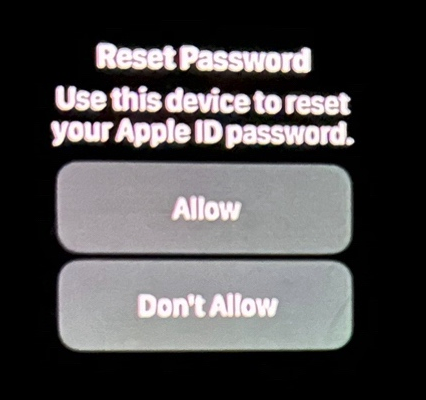
Krebs on Security
Several Apple customers recently reported being targeted in elaborate phishing attacks that involve what appears to be a bug in Apple's password reset feature. In this scenario, a target's Apple devices are forced to display dozens of system-level prompts that…


The Hacker News
Understand how hackers exploit social engineering to circumvent MFA and fortify your cybersecurity defenses accordingly.


HACKRead
The aftermath of the 2023 Okta breach continues to unfold, with Cloudflare disclosing the details of its security compromise.


CyberSecurity Dive
The layoffs come during the company's 90-day overhaul to address lax security following a string of cyberattacks targeting Okta and its customers.


DarkReading
The Middle Eastern developers claim to be building a new version of the antivirus-bypassing remote access Trojan (RAT) attack tool.


The Cyber Express
The year 2023 witnessed a surge in high-profile cyberattacks, leaving organizations shattered and the world in chaos. This digital turmoil


HACKRead
Ubisoft Entertainment SA, a French video game publisher, has confirmed an attempt to breach the company’s security to steal personal and sensitive data from its infrastructure.


Bleeping Computer
The source code for Grand Theft Auto 5 was reportedly leaked on Christmas Eve, a little over a year after the Lapsus$ threat actors hacked Rockstar games and stole corporate data.


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


Security Affairs
Video game publisher Ubisoft is investigating reports of an alleged data breach after popular researchers shared evidence of the hack.


The Hacker News
Two British teens, part of the LAPSUS$ cybercrime gang, sentenced for orchestrating high-profile attacks against companies.


The Cyber Express
As the year nears its end, the cybersecurity sector offers profound lessons through incidents like data breaches, leaks, and cyberattacks,


HACKRead
Arion Kurtaj, a 17-year-old from the United Kingdom, faced accusations of being part of the Lapsus$ gang, hacking industry giants, including Uber, Rockstar Games, Nvidia, BT, Samsung, and others.


SecurityWeek
A British teenage hacker has been sentenced to an indefinite hospital stay to be treated for his inability to control himself online.

Security Affairs
A member of the Lapsus$ cyber extortion group, Arion Kurtaj, has been sentenced to an indefinite hospital order.


The Cyber Express
The 18-year-old GTA 6 hacker, Arion Kurtaj, has been sentenced to life in a hospital prison for his role in


The Record
A U.K. jury found that Arion Kurtaj, 18, had committed crimes attributed to Lapsus$. Psychiatrists had deemed him unfit to fully stand trial.


The Record
Nikita Kislitsin will face hacking and extortion charges in his home country, according to Moscow’s Prosecutor General’s Office.


Bleeping Computer
Lapsus$ cybercrime and extortion group member, Arion Kurtaj has been sentenced to life in a 'secure hospital' by a UK judge. Kurtaj who is 18 years of age and autistic is among the primary Lapsus$ threat actors, and was involved in the leak of assets associated with the video game, Grand Theft Auto VI.


The Record
The FCC warning comes on the heels of a Cyber Safety Review Board report about the Lapsus$ cybercrime group.


The Cyber Express
The ever-accelerating pace of technological advancement shapes our world, forging a double-edged digital landscape. On one hand, it fuels innovation


SecurityWeek
Okta expands scope of October breach, saying hackers stole names and email addresses of all its customer support system users.


Bleeping Computer
Okta's investigation into the breach of its Help Center environment last month revealed that the hackers obtained data belonging to all customer support system users.


Ars Technica
SIM swaps and port-out scams are a fact of life. New rules aren't likely to change that.


SecurityWeek
With cyberattacks rising, new FCC rules will require wireless carriers to notify customers of any SIM transfer requests


The Hacker News
FCC mandates that wireless providers authenticate customers before transferring phone numbers, thereby protecting against SIM-swapping attacks and por


The Hacker News
U.S. agencies warn about Scattered Spider cybercriminals using advanced phishing to steal data and extort victims.


The Record
The leading cybersecurity officials in the U.S. published a stark warning on Thursday about a group of hackers who have disrupted some of the largest companies in the country through social engineering and other tactics.

Security Affairs
Samsung Electronics disclosed a data breach that exposed customer personal information to an unauthorized individual.


CyberNews
Samsung Electronics, a South Korean multinational tech corporation, has notified some of its customers of a data breach that exposed their personal data to a hacker.


Bleeping Computer
Samsung Electronics is notifying some of its customers of a data breach that exposed their personal information to an unauthorized individual.


Bleeping Computer
Samsung Electronics is notifying some of its customers of a data breach that exposed their personal information to an unauthorized individual.


Infosecurity News
Several suffered follow-on session hijacking attacks


Bleeping Computer
Okta says attackers who breached its customer support system last month gained access to files belonging to 134 customers, five of them later being targeted in session hijacking attacks with the help of stolen session tokens.


SecurityWeek
Redmond's new security initiative promises faster patches, better management of signing keys and products with a higher default security bar.


Bleeping Computer
Okta is warning nearly 5,000 current and former employees that their personal information was exposed after a third-party vendor was breached.


Bleeping Computer
Okta is warning nearly 5,000 current and former employees that their personal information was exposed after a third-party vendor was breached.


Infosecurity News
Threat actor accessed case management system


Ars Technica
Hackers obtained valid credentials, but Okta doesn't say how.


SecurityWeek
Okta warns that hackers broke into its support case management system and stole sensitive data that can be used to impersonate valid users.


Bleeping Computer
Okta says attackers accessed files containing cookies and session tokens uploaded by customers to its support management system after breaching it using stolen credentials.


Krebs on Security
Okta, a company that provides identity tools like multi-factor authentication and single sign-on to thousands of businesses, has suffered a security breach involving a compromise of its customer support unit, KrebsOnSecurity has learned. Okta says the incident affected a "very…


The Record
Human-operated attacks typically involve the active abuse of remote monitoring and management tools. Microsoft said its data could point to a shift in how the cybercrime underground works.


The Record
T-Mobile attributed a leak, which didn't affect company data, to an April attack on an independent retailer.


Bleeping Computer
T-Mobile customers today were able to see other people's account and billing information after logging into the company's official mobile application.


CyberSecurity Dive
Multiple threat groups have employed the same criminal tool kit to target vulnerable systems.


The Hacker News
UNC3944 threat actor now turns to ransomware attacks, targeting critical systems. Understand their tactics, and learn how to protect your organization


Bleeping Computer
An affiliate of the BlackCat ransomware group, also known as APLHV, is behind the attack that disrupted MGM Resorts' operations, forcing the company to shut down IT systems.


Bleeping Computer
An affiliate of the BlackCat ransomware group, also known as APLHV, is behind the attack that disrupted MGM Resorts' operations, forcing the company to shut down IT systems.


SecurityWeek
The hijacked data includes driver’s license numbers and/or social security numbers from a Caesars Entertainment loyalty database.


SecurityWeek
Okta says US-based customers have been targeted in social engineering attacks whose goal was to disable MFA and obtain high privileges.

The Hacker News
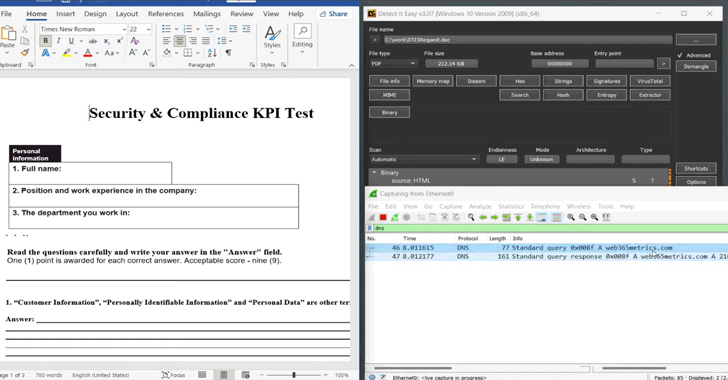
Hackers are now using a sneaky "MalDoc in PDF" technique to hide malicious Word files within PDFs.

The Record
Dustin Childs, the head of threat awareness for the Zero Day Initiative, explains to the Click Here podcast team how zero-day vulnerabilities make it into the hands of cybercriminals.

The Hacker News
Remember the hacks on Uber, Revolut, & Rockstar Games? Two UK teenagers, part of the infamous LAPSUS$ gang, convicted for high-profile hacks.


CSO
The two, including a 17-year-old, were convicted for their part in attacks on Uber, Nvidia, and other companies.

Latest Hacking News
In recent times, the world of cybersecurity has been rocked by a series of audacious cyberattacks. At the heart of these attacks is the notorious Lapsus$ teen hackers group, primarily composed of teenagers. Their high-profile


SecurityWeek
A UK court found a teenager responsible for a hacking campaign that included one of the biggest breaches in the history of the game industry.


Infosecurity News
Arion Kurtaj was deemed not fit to stand trial


Security Affairs
An 18-year-old member of the Lapsus$ gang has been convicted of having helped hack multiple high-profile companies. A teenage member of the Lapsus$ data extortion group, Arion Kurtaj (18), was convicted by a London jury of having hacked multiple high-profile companies, including Uber, Revolut, and blackmailed the developers of the gaming firm Rockstar Games. Since September […]


Bleeping Computer
A London jury has found that an 18-year-old member of the Lapsus$ data extortion gang helped hack multiple high-profile companies, stole data from them, and demanded a ransom threatening to leak the information.


DataBreaches
Joe Tidy reports: A court has found an 18-year-old from Oxford was a part of an international cyber-crime gang responsible for a hacking spree against major...

The Record
Two teenagers, ages 18 and 17, were found guilty of hacking into major corporations. The cases involved Uber, Nvidia and more.


SecurityWeek
US government's CSRB will conduct a review of cloud security to provide recommendations on improving identity management and authentication.


Security Affairs
The DHS’s CSRB will review cloud security practices following recent hacks of Microsoft Exchange accounts used by US govt agencies. The US DHS announced that the Cyber Safety Review Board (CSRB) will review the security measure to protect cloud computing environments following the recent compromise of Microsoft Exchange accounts used by US govt agencies. “The […]


Bleeping Computer
The Department of Homeland Security's Cyber Safety Review Board (CSRB) has announced plans to conduct an in-depth review of cloud security practices following recent Chinese hacks of Microsoft Exchange accounts used by US government agencies.

Infosecurity News
The CSRB proposed ten concrete recommendations for both governmental bodies and industries


Infosecurity News
The review will also conduct a broader review of issues relating to cloud-based identity and authentication infrastructure


CyberScoop
The decision comes in the wake of a high-profile Chinese breach of U.S. officials' Microsoft email accounts.


DataBreaches
Executive Summary Beginning in late 2021 and continuing late into 2022, a globally active, extortion-focused cyber threat actor group attacked dozens of...


Bleeping Computer
The U.S. government released a report after analyzing simple techniques, e.g. SIM swapping, used by the Lapsus$ extortion group to breach dozens of organizations with a strong security posture.


Ars Technica
With no skill in software exploitation or encryption busting, Lapsus$ wins anyway.


The Record
The China-linked attack on Microsoft email services will get a full review by the Cyber Safety Review Board, the Department of Homeland Security announced.


The Record
In its latest report, the Cyber Safety Review Board called on the FCC and FTC to strengthen their oversight and enforcement activities around SIM swapping.

The Record
A leading U.S. senator asked the Justice Department and several other agencies to investigate a recent hack of Microsoft-provided email accounts used by top government officials.


DataBreaches
Katharine Gemmell reports: Two UK teenagers were accused of being key members of the notorious hacking group Lapsus$, with prosecutors alleging that the pair...


The Record
A British Crown Court on Tuesday lifted a reporting restriction, allowing the naming of teenager Arion Kurtaj who is accused of hacking Uber, Revolut, and video games developer Rockstar in a short period of time last September.


DarkReading
Organizations are largely deluded about their own security postures, according to an analysis, with the average SIEM failing to detect a whopping 76% of attacker TTPs.


Bleeping Computer
Microsoft has started enforcing number matching in Microsoft Authenticator push notifications to fend off multi-factor authentication (MFA) fatigue attacks.


Ars Technica
Hack affecting 836 subscribers, lasted for more than a month before it was discovered.


Bleeping Computer
T-Mobile disclosed the second data breach of 2023 after discovering that attackers had access to the personal information of hundreds of customers for more than a month, starting late February 2023.


CyberSecurity Dive
The brains behind high-profile attacks last year, teenagers and young adults use sophisticated social engineering techniques for intrusions.


The Hacker News
Twitter source code leaked on GitHub for months by user "FreeSpeechEnthusiast". Is your company prepared for a similar breach?


Infosecurity News
Jose Luis Huertas boasted of accessing 90% of Spaniards' info


DarkReading
The homepage of a widely used Dark Web forum for stolen cookies and other compromised data has been replaced by a seizure notice by the US federal law enforcement agency.


DarkReading
Enables enterprises to operationalize MITRE ATT&CK and build a multi-layered, threat-informed defense to eliminate gaps based on organizational risk and priorities.


DarkReading
Indicators point to Twitter's source code being publicly available for around 3 months, offering a developer security object lesson for businesses.


DarkReading
Accidentally typing a password in the username field of the platform saves them to audit logs, to which threat actors can gain access and use to compromise enterprise services.

CSO
New research shows that criminal gangs are focusing more on acquiring stolen credentials to bypass security measures.


The Hacker News
Hackers are getting smarter, and vishing attacks are becoming more convincing. Don't let your company be the next victim.


CyberSecurity Dive
A series of security incidents hit the identity and access management platform last year. But financial results are improving and the customer base is growing.


Bleeping Computer
Riot Games says it will not pay the ransom demanded by the attackers responsible for the security breach the company disclosed last week.


DarkReading
Use threat intelligence to reduce chance of success for malicious insider and Dark Web threats.


Infosecurity News
Compromise impacts developer's ability to release updates


CSO
Customer data such as customer name, billing address, email, phone number, date of birth, T-Mobile account number and information such as the number of lines on the account and plan features were exposed in the breach.
Loading more articles....