

CyberSecurity Dive
CISA, FBI urge software companies to eliminate directory traversal vulnerabilities
The software defects are linked to recent exploitation campaigns against critical infrastructure providers, including healthcare and schools.


CyberSecurity Dive
The software defects are linked to recent exploitation campaigns against critical infrastructure providers, including healthcare and schools.


SecurityWeek
Thirty-three cybersecurity-related merger and acquisition (M&A) transactions were announced by companies in April 2024.


SecurityWeek
IBM is acquiring HashiCorp for $6.4 billion for its infrastructure lifecycle management and security lifecycle management capabilities.


SecurityWeek
Armis has acquired cyber risk prioritization and remediation company Silk Security for $150 million.


SecurityWeek
Veracode announces a deal to acquire Låç≈ongbow Security, a seed-stage startup working on automated root cause analysis technology.


CSO
Software security debt, defined in the research as any flaw that persisted unremediated for over a year, was found in 42% of all applications.

DarkReading
Threat actors linked to the People's Republic of China, such as Volt Typhoon, continue to "pre-position" themselves within the critical infrastructure of the United States, according to military and law enforcement officials.


SC Magazine
The Justice Department and FBI confirmed they had disrupted the botnet run by a Chinese APT group targeting U.S. critical infrastructure.


DarkReading
Zoom's Vulnerability Impact Scoring System calculates the impact of a vulnerability to assign a cash payouts for bugs, leading hackers to prioritize more severe flaws. Can it do the same for companies?


CSO
The company warns that HTTP/2 Rapid Reset is emerging as significant new vulnerability.


The Hacker News
Lazarus Group launched a new global campaign involves exploiting security flaws in Log4j to deploy previously undocumented RAT on compromised hosts.


Infosecurity News
Two years after a critical vulnerability was found in utility Log4j, 38% of apps still use buggy versions


The Record
Hackers connected to North Korea’s Lazarus Group have been exploiting the Log4j vulnerability in a campaign of attacks targeting companies in the manufacturing, agriculture and physical security sectors.


Bleeping Computer
Roughly 38% of applications using the Apache Log4j library are using a version vulnerable to security issues, including Log4Shell, a critical vulnerability identified as CVE-2021-44228 that carries the maximum severity rating, despite patches being available for more than two years.


CyberSecurity Dive
Research from Veracode shows nearly 2 in 5 applications are still running vulnerable versions.


SecurityWeek
Chris Wysopal (AKA Weld Pond) founder and CTO of Veracode and member of the hacker collective L0pht Heavy Industries.

-1-1.webp)
Cyber Security News
Top 10 Best SaaS Security Tools. 1. DoControl, 2. Splunk, 3. Zscaler, 4. Qualys, 5. Proofpoint, 6. Veracode, 7. Okta, 8. Trend Micro.


Cyber Security News
DevOps refers to a collection of processes and technologies used in software development and IT operations that reduce the system development life cycle and enable continuous delivery.

The Record
Initial alerts about a bug in the obscure but widely used libwebp library have expanded into concerns that it affects not only web browsers like Chrome, but also many other common pieces of software.


SecurityWeek
Conversation with Cris Thomas, also known as Space Rogue, who was a founding member of the Lopht Heavy Industries hacker collective.


The Record
The White House and a handful of government agencies on Thursday called for experts to help them create policies around the cybersecurity of open source software and promote the use of more security programming languages.


Cyber Security News
Best Penetration Testing Companies: 1. Crowdstrike 2. Secureworks 3. Rapid7 4. Acunetix 5. Trellix 6. Invicti 7. Cobalt 8. Intruder.


CyberSecurity Dive
The global effort to promote secure by design is seen as a potential game changer for software security, but may require substantial investments and considerable cultural changes.


CSO
2022 was a particularly leaky year in relation to secrets, GitGuardian’s latest State of Secrets Sprawl report finds.


DarkReading
Open source software dependencies are affecting the software security of different industries in different ways, with mature industries becoming more selective in their open source usage.


DarkReading
Thistle's technology will give device makers a way to easily integrate features for secure updates, memory management, and communications into their products, Snyder says.


CyberSecurity Dive
The incident closely follows a series of indirect source code repository breaches impacting Slack and Okta.


DarkReading
About three-quarters of Java and .NET applications have vulnerabilities from the OWASP Top 10 list, while only 55% of JavaScript codebases have such flaws, according to testing data.


CyberSecurity Dive
Inconsistent or delayed code commits create risk as repositories age, Veracode research found.


Infosecurity News
Veracode’s 2023 State of Software Security Report is focused on flaw introduction

SecurityWeek
Sixteen cybersecurity-related merger and acquisition (M&A) deals were announced in December 2022.

SecurityWeek
A dozen cybersecurity-related merger and acquisition (M&A) deals were announced in the first half of December 2022.


Computerworld
With its decision to introduce powerful new data protection tools for iMessage and to enable users to encrypt more of their information in iCloud, Apple has set the scene for security to be the big trend in tech in the year ahead.


CyberSecurity Dive
Nearly 1 in 5 vulnerabilities in the retail and hospitality industry are considered high severity, Veracode found, creating considerable risks to the organization.


CSO
The guidance aims to improve the security of software federal agencies use, but expects self-attestation for compliance.


CyberSecurity Dive
Technical complexities abound as the perceived level of risk rises in an unrelenting fashion.

SecurityWeek
SecurityWeek is publishing a digest summarizing some of the announcements made by vendors at Black Hat USA 2022.


Computerworld
Given that one of the uglier threats to enterprise cybersecurity involves re-purposed third-party code and open-source code, you might think that Google addressing the issue would be a big help. Think again.

CSO
Notable experts say the cybersecurity executive order has improved the nation's security posture, but more work is to be done.

SecurityWeek
For providers of DevSecOps services and solutions, the focus should be on removing friction from integrating security and helping teams come together to make security everyone’s responsibility.

SecurityWeek
Code quality software firm SonarSource announced a $412 million funding round at a $4.7 billion valuation, as investors continue to pour money into startups tackling software supply chain security.


CyberSecurity Dive
Enterprise adoption of open source has not cooled, but flaws have highlighted the need for a better understanding of dependencies.


Cyber Security News
When we talk about the penetration Testing tools, that the first thing that comes up to our mind is the threat. Here the Top 10 best Pentestinng tools.


Infosecurity News
The researchers also found the public sector takes twice as long to fix flaws once detected compared to other industries


CSO
The new guidance aims to tighten security requirements for federally purchased software and give consumers better insight into the security of software and devices they buy.

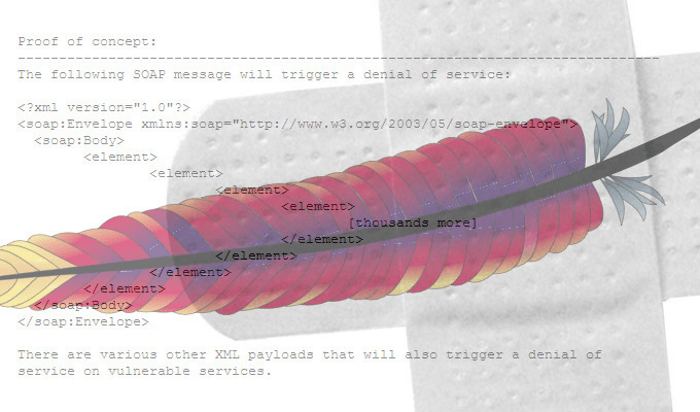
ThreatPost
The Log4Shell vulnerability critically threatens anybody using the popular open-source Apache Struts framework and could lead to a “Mini internet meltdown soonish.”


ZDNet
Preventing a cyberattack is more cost effective than reacting to one - but many boardrooms still aren't willing to free up budget.