

Security Affairs
Security Affairs newsletter Round 470 by Pierluigi Paganini – INTERNATIONAL EDITION
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


Security Affairs
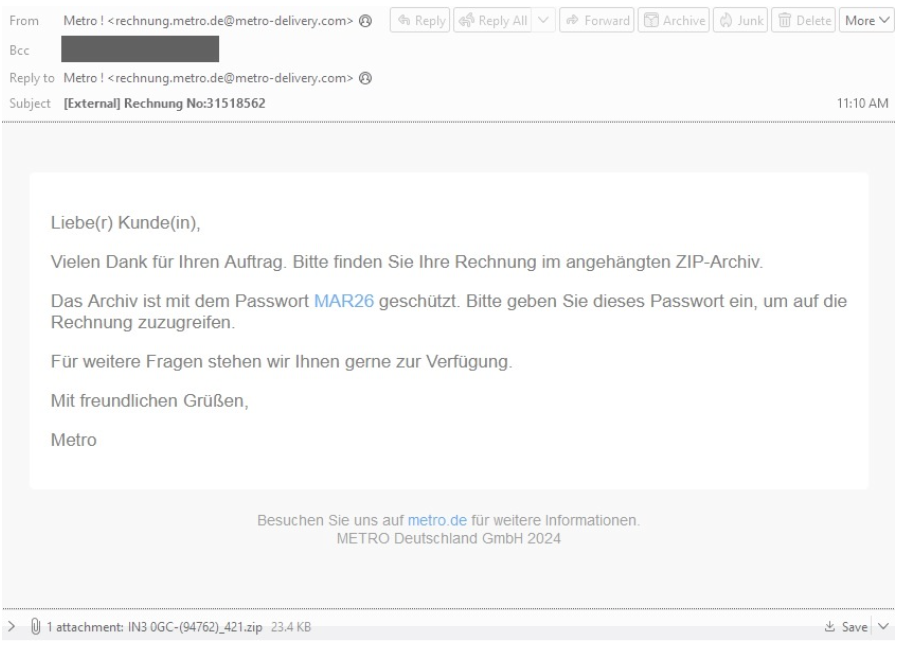
Zloader continues to evolve, its authors added an anti-analysis feature that was originally present in the Zeus banking trojan.


The Hacker News
ZLoader modular malware trojan has resurfaced with anti-analysis feature that prevents execution on machines different from the original infection.

Security Affairs
TA547 group is targeting dozens of German organizations with an information stealer called Rhadamanthys, Proofpoint warns.

The Hacker News
TA547 hacker group adopts new tactics, possibly harnessing the power of generative AI, to deploy the Rhadamanthys info stealer in attacks on German or


DarkReading
It's finally happening: Rather than just for productivity and research, threat actors are using LLMs to write malware. But companies need not worry just yet.


Bleeping Computer
A threat actor is using a PowerShell script that was likely created with the help of an artificial intelligence system such as OpenAI's ChatGPT, Google's Gemini, or Microsoft's CoPilot.


The Hacker News
Bumblebee, QakBot, Zloader, & PikaBot are back, sneakier than ever. Don't trust those shady emails or downloads.

HACKRead
Mispadu Stealer targeted Spanish- and Portuguese-speaking victims, but the new variant aims at URLs associated with Mexican citizens.


The Hacker News
ZLoader malware resurfaces after 2 years, targeting Windows systems with ransomware.


Cyber Security News
Zloader, also known as Terdot, DELoader, or Silent Night, is a modular trojan that reappeared after nearly two years of absence.


The Hacker News
A supply chain breach at 3CX has been linked to the North Korean-associated backdoor, Gopuram. The Lazarus Group is believed to be behind the attack.


Bleeping Computer
Some of the victims affected by the 3CX supply chain attack have also had their systems backdoored with Gopuram malware, with the threat actors specifically targeting cryptocurrency companies with this additional malicious payload.

Bleeping Computer
A 10-year-old Windows vulnerability is still being exploited in attacks to make it appear that executables are legitimately signed, with the fix from Microsoft still "opt-in" after all these years. Even worse, the fix is removed after upgrading to Windows 11.

The Hacker News
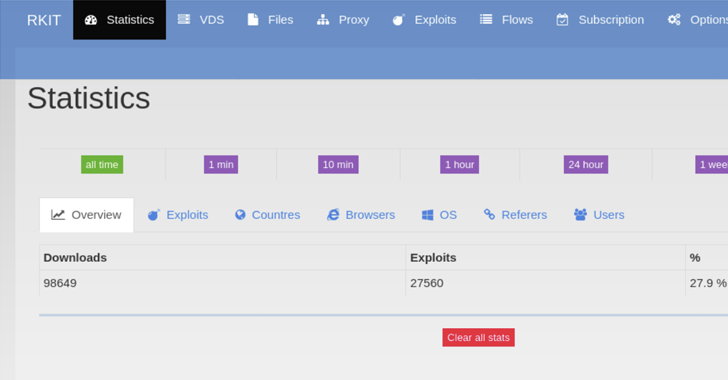
Researchers have uncovered crucial insights into the inner workings of RIG Exploit Kit and its administrators.


Bleeping Computer
The RIG Exploit Kit is undergoing its most successful period, attempting roughly 2,000 intrusions daily and succeeding in about 30% of cases, the highest ratio in the service's long operational history.


The Record
Google's Threat Analysis Group reports that cyberattacks on Ukraine and its supporters increased aggressively as Russia waged war.

The Hacker News
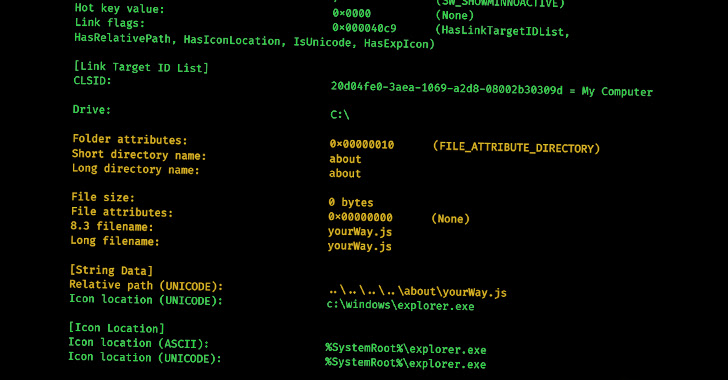
New study by cybersecurity experts shows potential to identify relationships among threat actors by analyzing metadata of malicious LNK files.

Trend Micro
We discuss the Batloader malware campaigns we observed in the last quarter of 2022, including our analysis of Water Minyades-related events (This is the intrusion set we track behind the creation of Batloader).


Security Affairs
Microsoft warns that a threat actor, tracked as DEV-0569, is using Google Ads to distribute the recently discovered Royal ransomware. Researchers from the Microsoft Security Threat Intelligence team warned that a threat actor, tracked as DEV-0569, is using Google Ads to distribute various payloads, including the recently discovered Royal ransomware. The DEV-0569 group carries out […]


DarkReading
How far can its government — or any government or private company — go to proactively disrupt cyber threats without causing collateral damage?


DarkReading
BatLoader has spread rapidly to roost in systems globally, tailoring payloads to its victims.


Bleeping Computer
The Microsoft Digital Crimes Unit (DCU) has disrupted a spear-phishing operation linked to an Iranian threat actor tracked as Bohrium that targeted customers in the U.S., Middle East, and India.


The Hacker News
Ukraine government has warned of a new wave of hacking campaigns that spread IcedID malware and exploit Zimbra exploits to steal sensitive information


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs free for you in your email box. If you want to also receive for free the newsletter with the international press subscribe here. U.S. Gov believes North Korea-linked Lazarus APT is behind Ronin Validator cyber heist The […]


ZDNet
Microsoft takes control of ZLoader's botnet infrastructure, which is used to spread malware and ransomware.

Infosecurity News
Tech giant takes control of 65 C&C domains


DarkReading
The banking Trojan-turned-ransomware-distribution tool has been a potent threat since late 2019.


CyberSecurity Dive
Ryuk was behind major attacks on healthcare, while the botnet focused on credentials and financial theft.


The Hacker News
Microsoft, Adobe, Android, Mozilla, Intel, SAP, Citrix, and other major software firms release February 2022 Patch Tuesday Security Updates.


Bleeping Computer
Microsoft has announced that Excel 4.0 (XLM) macros will now be disabled by default to protect customers from malicious documents.


ZDNet
This month's round of security fixes includes patches for publicly-known remote code execution bugs.


ZDNet
Researchers believe the focus is moving from cryptocurrency to traditional botnet attacks.


Trend Micro
This week, read about Log4j vulnerabilities in connected cars and charging stations and how iOS malware can fake iPhone shutdowns to snoop on cameras and microphones.


ThreatPost
The info-stealing campaign using ZLoader malware – previously used to deliver Ryuk and Conti ransomware – already has claimed more than 2,000 victims across 111 countries.

Bleeping Computer
A new Zloader campaign exploits Microsoft's e-signature code verification to steal user credentials from over two thousand victims in 111 countries.


ZDNet
Malware exploits the system to steal credentials and other data.


Bleeping Computer
Microsoft will soon begin disabling Excel 4.0 XLM macros by default in Microsoft 365 tenants to protect customers from malicious documents.

Bleeping Computer
An ongoing Zloader campaign uses a new infection chain to disable Microsoft Defender Antivirus (formerly Windows Defender) on victims' computers to evade detection.

The DFIR Report
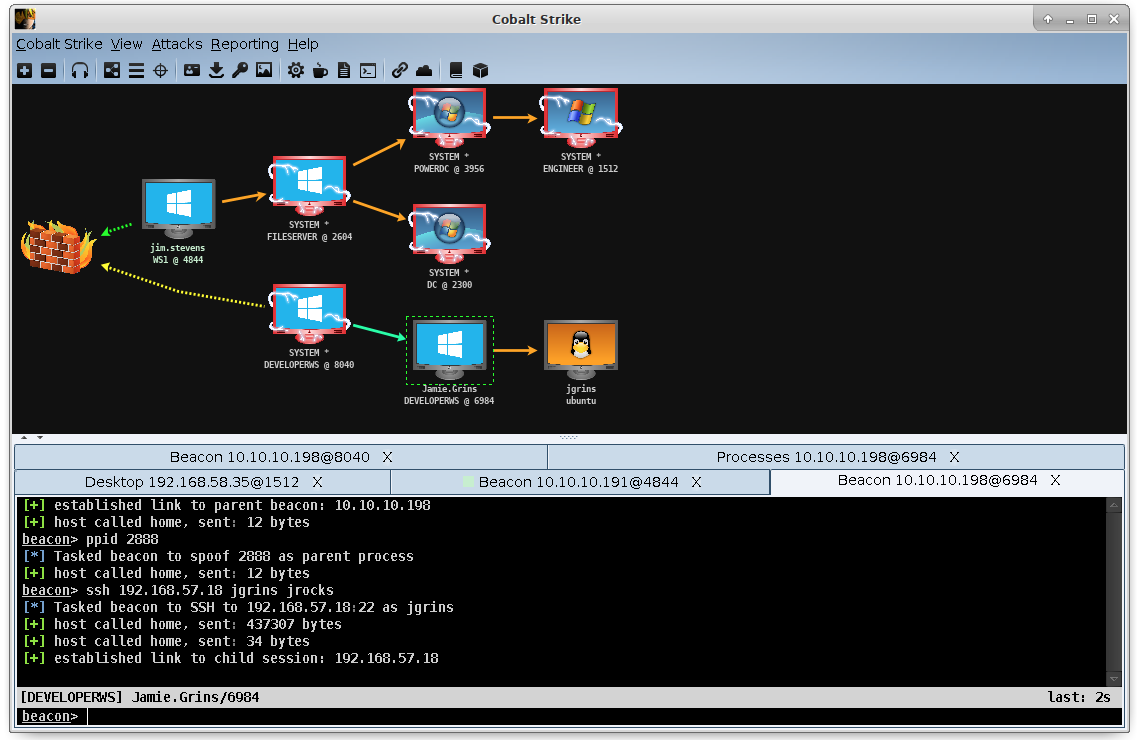
As you have noticed from our reporting so far, Cobalt Strike is used as a post-exploitation tool with various malware droppers responsible for the initial infection stage. Some of the most common droppers we see are IcedID (a.k.a. BokBot), ZLoader, Qbot (a.k.a. QakBot), Ursnif, Hancitor, Bazar and TrickBot.


Bleeping Computer
Threat actors are using legitimate corporate contact forms to send phishing emails that threaten enterprise targets with lawsuits and attempt to infect them with the IcedID info-stealing malware.