

SecurityWeek
Threat Actors Abuse Cloudflare Tunnel for Persistent Access, Data Theft
Threat actors have been observed abusing the open source Cloudflare Tunnel tool Cloudflared to maintain persistent access to systems.


SecurityWeek
Threat actors have been observed abusing the open source Cloudflare Tunnel tool Cloudflared to maintain persistent access to systems.


Cyber Security News
The DNS Tunnel Keylogger tool has been released on GitHub, which utilizes DNS tunneling to transmit keystrokes through firewalls.


Bleeping Computer
NordVPN's Meshnet private tunnel feature for Windows, macOS, and Linux is now free for everyone, even users who do not have a subscription to NordVPN.


Security Affairs
Researchers uncovered a new Linux botnet, tracked as B1txor20, that exploits the Log4J vulnerability and DNS tunnel. Researchers from Qihoo 360’s Netlab have discovered a new backdoor used to infect Linux systems and include them in a botnet tracked as B1txor20. The malware was first spotted on February 9, 2022, when 360Netlab’s honeypot system captured […]


The Hacker News
Researchers uncover targeted attacks by cyber espionage hacking group Worok against high-profile Asian companies and governments.


Infosecurity News
Proofpoint has detailed a sophisticated disinformation campaign in which high-profile individuals are duped into embarrassing comments on video


The Hacker News
Two British teens, part of the LAPSUS$ cybercrime gang, sentenced for orchestrating high-profile attacks against companies.


Bleeping Computer
A new trend has emerged on dating apps like Tinder with spammers sneaking in handwritten NSFW links within profile images. Multiple such Tinder spam profiles reviewed by BleepingComputer shared some common characteristics.

SecurityWeek
Recent high-profile cyberattacks have demonstrated the effectiveness of an interesting method for getting past MFA.


Bleeping Computer
A London jury has found that an 18-year-old member of the Lapsus$ data extortion gang helped hack multiple high-profile companies, stole data from them, and demanded a ransom threatening to leak the information.


The Hacker News
Trickbot malware has been targeting customers of 60 high-profile companies since 2020, including cryptocurrency and technology companies.


Security Affairs
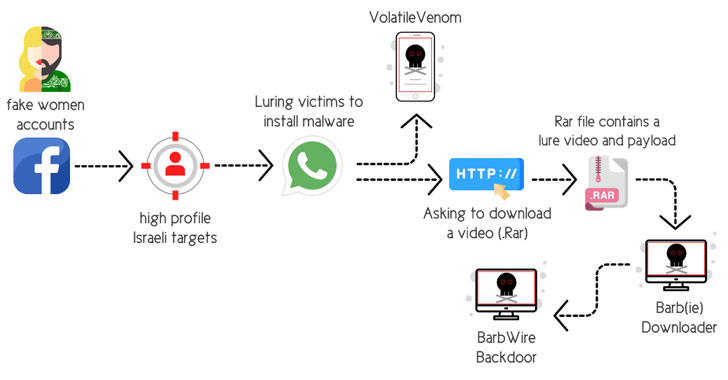
Hamas-linked threat actors conducted an elaborate campaign aimed at high-profile Israeli individuals employed in sensitive sectors. Researchers from Cybereason observed a sophisticated cyberespionage campaign conducted by APT-C-23 group campaigns targeting Israeli high-profile targets working for sensitive defense, law enforcement, and emergency services organizations. The threat actors use sophisticated social engineering techniques to infect Windows and Android […]


Bleeping Computer
A silly Twitter bug allowed previously-verified accounts to add their legacy 'Blue Check' back to their profile for free.


Bleeping Computer
A newly discovered cyber-espionage group has been hacking governments and high-profile companies in Asia since at least 2020 using a combination of custom and existing malicious tools.


Security Affairs
An 18-year-old member of the Lapsus$ gang has been convicted of having helped hack multiple high-profile companies. A teenage member of the Lapsus$ data extortion group, Arion Kurtaj (18), was convicted by a London jury of having hacked multiple high-profile companies, including Uber, Revolut, and blackmailed the developers of the gaming firm Rockstar Games. Since September […]

The Hacker News
Remember the hacks on Uber, Revolut, & Rockstar Games? Two UK teenagers, part of the infamous LAPSUS$ gang, convicted for high-profile hacks.


The Hacker News
A new "B1txor20" Linux botnet has been discovered that spreads via the Log4J vulnerability and uses DNS tunnels for covert C2 communications.

Latest Hacking News
In recent times, the world of cybersecurity has been rocked by a series of audacious cyberattacks. At the heart of these attacks is the notorious Lapsus$ teen hackers group, primarily composed of teenagers. Their high-profile


DataBreaches
The following is not a paragraph from a story about fictional cybercriminals called Evil Corp. The following paragraph is from a white paper released this week...


ThreatPost
Electronic Arts blamed “human error” after attackers compromised customer support and took over and drained some of the top FIFA Ultimate Team player accounts.


Trend Micro
In this entry, we discuss how a threat actor abuses paid Facebook promotions featuring LLMs to spread malicious code, with the goal of installing a malicious browser add-on and stealing victims’ credentials.


DataBreaches
HC3: Analyst Note TLP: White Report: 202208241200 Executive Summary Karakurt ransomware group, also known as the Karakurt Team and Karakurt Lair, is a...


The Record
The international operation, centered on Kyiv, essentially neutralized a group known for deploying variants of LockerGoga, MegaCortex, Hive and Dharma ransomware, authorities said.


Security Affairs
TrickBot malware is targeting customers of 60 financial and technology companies with new anti-analysis features. The infamous TrickBot malware was employed in attacks against customers of 60 financial and technology companies with new anti-analysis features. The news wave of attacks aimed at cryptocurrency firms, most of them located in the U.S.. Trickbot is a sophisticated, […]


Trend Micro
We analyze an information stealer written in Node.js, packaged into an executable, exfiltrated stolen data via both Telegram bot API and a C&C server, and employed GraphQL as a channel for C&C communication.


CyberSecurity Dive
Flashpoint observed 27 vulnerability exploits listed for sale or purchased on the dark web during the first half of the year. One-third were linked to Microsoft products.


CyberSecurity Dive
Microsoft researchers described Octo Tempest, or Oktapus, as one of the most dangerous financial criminal groups currently in operation.


ZDNet
Notable FIFA players around the world said hackers were spamming EA customer service channels to change account details.


The Record
Experts working on Middle Eastern affairs at universities and research organizations in Belgium, France, Gaza, Israel, the U.K. and the U.S. were targeted with phishing lures, in some cases about the Israel-Hamas war.


Bleeping Computer
Cryptocurrency scammers are abusing a legitimate Twitter "feature" to promote scams, fake giveaways, and fraudulent Telegram channels used to steal your crypto and NFTs.


Bleeping Computer
Cryptocurrency scammers are abusing a legitimate X "feature" to promote scams, fake giveaways, and fraudulent Telegram channels used to steal your crypto and NFTs.


The Record
Hackers in North Korea's Lazarus Group exploited a vulnerability in an unnamed vendor's software, researchers found.

-1.webp)
Cyber Security News
Threat actors have shifted from using malicious macros to malicious LNK files for initial access. This is due to Microsoft's announcement in 2022 to disable macros by default for Office documents downloaded from unknown sources or the internet.


SC Magazine
Security pros say APT group could move from university researchers to critical infrastructure sectors and other verticals.


Bleeping Computer
Electronic Arts (EA) has published an official response to numerous reports about hacked player accounts, confirming the problem and attributing it to phishing actors.


CyberNews
Contrary to popular belief, the cyber attackers did not breach all these companies individually.


Ars Technica
Once-unknown group uses a tunnel fetish and a chameleon's ability to blend in.


The Record
A cybersecurity firm released a decryptor for the Akira ransomware, providing a way forward for dozens of victims that have dealt with attacks since the gang emerged in March 2023.


Bleeping Computer
Hackers are more frequently using social engineering attacks to gain access to corporate credentials and breach large networks. One component of these attacks that is becoming more popular with the rise of multi-factor authentication is a technique called MFA Fatigue.


Bleeping Computer
A refurbished Lenovo ThinkCentre M900 is a great option for anyone who needs the features of a desktop with the portability of a laptop for $189.99, $160 off the $349 MSRP.


CyberSecurity Dive
Researchers from VirusTotal show how attackers use social engineering techniques to launch malicious attacks behind trusted applications.


The Hacker News
Most mature enterprises with plenty of resources are also interested in automating, customizing, and scaling up their red team activities.


DarkReading
LockBit, Babuk, and Hive ransomware used by Russian to target critical US organizations, DOJ says.


DarkReading
A literal seven-nation (cyber) army wasn't enough to hold back the famous initial access broker (IAB) for long — it's been chugging along, spreading ransomware, despite a massive takedown in August.


CyberNews
News Corp's British newspaper group settled claims of phone-hacking brought by celebrities, including "Spice Girl" Mel C., a former British minister, and others.

The Hacker News
Jamf Threat Defense protects against mobile endpoint (iOS, iPadOS, Android) threat vectors through a highly effective mobile application.


Bleeping Computer
You can get DDoS protection remotely for your collocated server using a generic routing encapsulation (GRE) tunnel. We will explain how GRE tunnels combined with Gcore scrubbing centers can help keep your data safe.


Bleeping Computer
Security researchers are seeing an uptick in the use of reverse tunnel services along with URL shorteners for large-scale phishing campaigns, making the malicious activity more difficult to stop.

Bleeping Computer
Six malicious packages on PyPI, the Python Package Index, were found installing information-stealing and RAT (remote access trojan) malware while using Cloudflare Tunnel to bypass firewall restrictions for remote access.


CyberNews
A security researcher Michael Horowitz called VPNs on iOS “a scam.” In a blog post, he exposed the VPN tunnel leaks on iOS devices, with the latest investigated version being 15.6.


Bleeping Computer
A new attack dubbed "TunnelVision" can route traffic outside a VPN's encryption tunnel, allowing attackers to snoop on unencrypted traffic while maintaining the appearance of a secure VPN connection.


Cyber Security News
As social media becomes increasingly popular, so do the risks associated with it. Hackers target social media accounts for a variety of reasons, from stealing personal information to spreading malware. Facebook, being one of the most popular social networking platforms, is a prime target for hackers. In fact, it seems like hardly a week goes […]


Ars Technica
No message, profile, or other data exposed—but SMS remains a weakness.


SecurityWeek
Russian-speaking threat actors are caught abusing a GitHub profile to distribute information stealers posing as legitimate software.

Bleeping Computer
Recent high-profile malware attacks teach us lessons on limiting malware risks at organizations. Learn more from Blink Ops about what these attacks taught us.


Bleeping Computer
A silly Twitter bug allowed previously-verified accounts to add their legacy 'Blue Check' back to their profile for free.


Bleeping Computer
A silly Twitter bug allows previously-verified accounts to add their legacy 'Blue Check' back to their profile for free.


ZDNet
Cybersecurity might just be the most stressful job in tech right now. But there might be a (tiny) glimmer of light at the end of the tunnel.


The Record
The SEC account takeover is the latest in a string of high-profile security incidents on X (formerly Twitter).


CSO
The previously undocumented APT group has been targeting high-profile organizations in Asia and Europe for over a year.


The Hacker News
North Korea-aligned Lazarus Group is behind malicious campaigns targeting software vendors, exploiting security flaws in high-profile software.


Cyber Security News
A North Korea based threat actor targeting personal accounts of technology firms through low-profile social engineering attempts.


Infosecurity News
Country bucks the global trend thanks to high-profile incidents


Infosecurity News
A cyber espionage campaign tied to the Chinese group ToddyCat is targeting high-profile organizations in Kazakhstan, Uzbekistan, Pakistan, and Vietnam


DataBreaches
Written by Jon DiMaggio. Conducting a behavioral profile of ransomware attackers will give you a better understanding of who is behind the attacks threatening...


CyberSecurity Dive
The brains behind high-profile attacks last year, teenagers and young adults use sophisticated social engineering techniques for intrusions.


Ars Technica
Cloud giant says its verification tool doesn't challenge or profile users.


CyberSecurity Dive
The second international summit follows a series of high profile attacks against CommonSpirit Health and the Los Angeles Unified School District.


DataBreaches
Michael Elsen-Rooney reports: Following two high-profile data breaches, New York City’s Education Department has moved to shore up its cybersecurity...


The Cyber Express
The year 2023 witnessed a surge in high-profile cyberattacks, leaving organizations shattered and the world in chaos. This digital turmoil


PCMag
The hack, which provided unauthorized access to 'files containing profile information about other users’ ancestry,' impacted 0.1% of 23andMe's users worldwide.


CyberNews
A threat actor on the dark web has claimed possession of data affiliated with numerous high-profile universities in the US.


DataBreaches
Jonathan Greig reports: HR management platform Kronos has been hit with a ransomware attack, revealing that information from many of its high-profile customers...


CyberScoop
Officials attributed the botnet, called Cyclops Blink, to Russia's GRU, which has a long history of high-profile cyberattacks.


CyberSecurity Dive
The data storage firm will face added pressure to its credit profile if the security incident further disrupts operations, one analyst said.


SecurityWeek
A cross-site scripting vulnerability in the WP-Members Membership plugin could allow attackers to inject scripts into user profile pages.


Infosecurity News
Jake Moore, global cybersecurity advisor at ESET, shared at DTX Europe 2022 how he used a fake social media profile to hack employees of a company


CyberSecurity Dive
Lapsus$, one of the most prolific ransomware actors of 2022, has utilized such tactics to breach a number of high-profile organizations.


The Cyber Express
IntelBroker, a shadowy figure in the cybersecurity world, has gained notoriety for a string of high-profile cyberattacks and subsequent data


Bleeping Computer
Europol has announced today the arrest of a Russian national linked to LockBit ransomware attacks targeting critical infrastructure organizations and high-profile companies worldwide.

Bleeping Computer
Attackers could abuse vulnerabilities discovered in the Bluetooth Core and Mesh Profile specifications to impersonate legitimate devices during the pairing process and launch man-in-the-middle (MitM) attacks.


DataBreaches
Ben Lovejoy reports: Twitter GodMode – an internal tool that hackers used to tweet from high-profile accounts, including Apple, back in 2020 – remains...

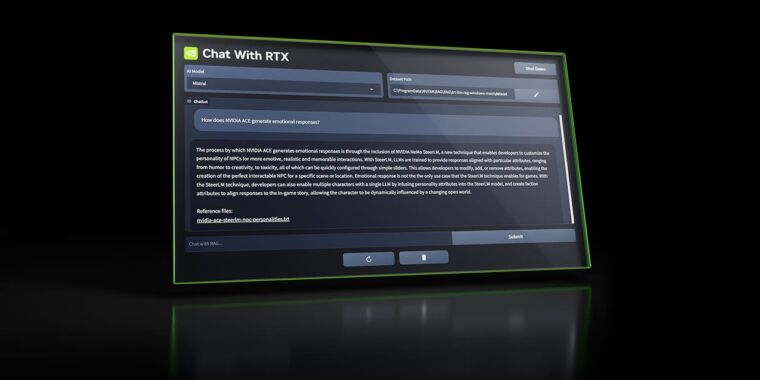
Ars Technica
Nvidia's local private AI chatbot is a high-profile step toward cloud independence.


SC Magazine
The gang claimed responsibility for a high-profile attack against Change Healthcare Wednesday.


The Cyber Express
The NoName group claims to have launched a sophisticated cyberattack on multiple high-profile websites in the Netherlands. The targeted organizations

Bleeping Computer
DuckDuckGo is rolling out an email privacy feature that strips incoming messages of trackers that can help profile you for better profiling and ad targeting.

The Hacker News
Researchers uncover details of a hacking campaign targeting a group of high-profile Israeli targets working for sensitive defense, law enforcement.


The Record
An Iranian nation-state threat actor is targeting high-profile organizations in the Middle East in an ongoing espionage campaign, according to a new report.


Security Affairs
US DHS Cyber Safety Review Board will review attacks linked to the Lapsus$ extortion gang that hit multiple high-profile companies. The Department of Homeland Security (DHS) Cyber Safety Review Board announced that it will review cyberattacks linked to the extortion gang Lapsus$, the gang breached multiple high-profile companies in recent years. “Today, the U.S. Department […]


DataBreaches
Hannah Miller reports: Following a high-profile hack last week, crypto wallet-maker Ledger said it will cover the roughly $600,000 worth of assets lost by...


The Cyber Express
In a recent cyber incident, a hacker associated with high-profile breaches including those of the FBI and Airbus, has purportedly


CyberSecurity Dive
NewYork-Presbyterian’s Daniel Barchi will take the new position starting Monday, just one month after the hospital chain suffered a high-profile ransomware attack.


Bleeping Computer
Microsoft says Samsung devices enrolled in Microsoft Intune using a work profile will experience email and VPN connectivity issues due to missing certificates after upgrading to Android 12.


CyberSecurity Dive
A series of high-profile and damaging cyberattacks has underscored the critical role cybersecurity teams play, and top brass are taking notice.


CyberScoop
The crackdown on foreign commercial surveillance comes in the wake of high-profile attacks on diplomats and government officials abroad.


The Hacker News
London police have arrested a 17-year-old Oxfordshire teenager on suspicion of hacking, possibly in connection with the recent high-profile hacking at


DataBreaches
Angus Liu reports: Merck may finally be entitled to a hefty insurance payout from the high-profile NotPetya cyberattack—if an appeals court ruling stands. A...


Bleeping Computer
OpenTable has reversed its decision to show members' first names and profile pictures in past anonymous reviews after receiving backlash from members who felt it was a breach of privacy.


CyberSecurity Dive
While officials echo urgent mitigation steps to contain the zero-day vulnerability, high-profile organizations continue to bear the impact.


Bleeping Computer
Restaurant reservation platform OpenTable says that all reviews on the platform will no longer be fully anonymous starting May 22nd and will now show members' profile pictures and first names.
Loading more articles....