

DarkReading
TA547 Uses an LLM-Generated Dropper to Infect German Orgs
It's finally happening: Rather than just for productivity and research, threat actors are using LLMs to write malware. But companies need not worry just yet.


DarkReading
It's finally happening: Rather than just for productivity and research, threat actors are using LLMs to write malware. But companies need not worry just yet.


DarkReading
Nearly three months after Operation Cronos, it's clear the gang is not bouncing back from the innovative law-enforcement action. RaaS operators are on notice, and businesses should pay attention.


Trend Micro
Our new article provides key highlights and takeaways from Operation Cronos' disruption of LockBit's operations, as well as telemetry details on how LockBit actors operated post-disruption.


SecurityWeek
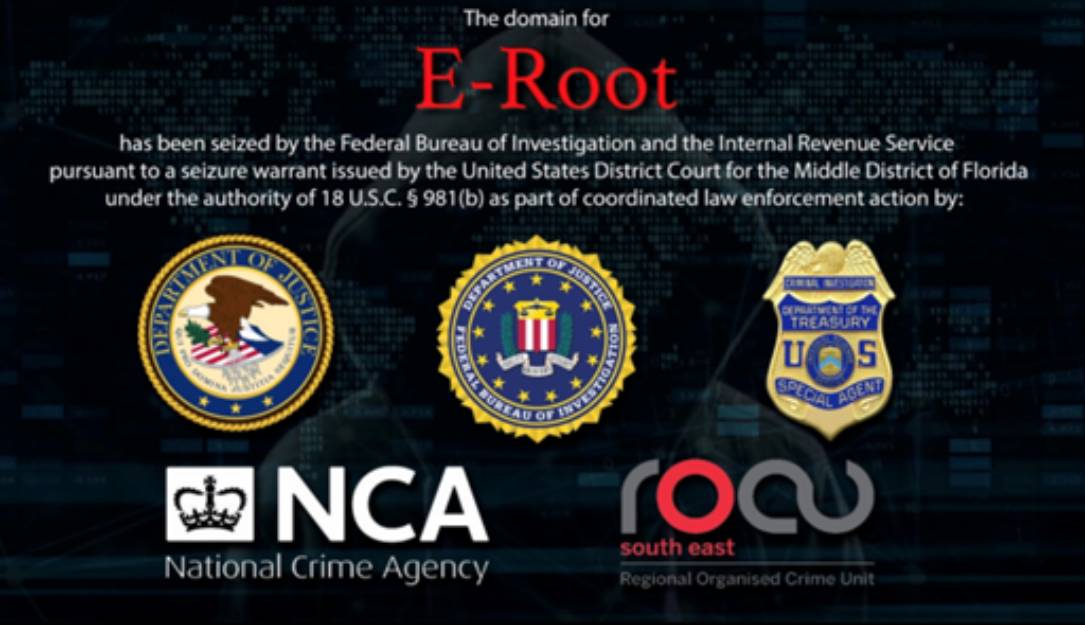
Sandu Diaconu has been sentenced to 42 months in prison for operating a marketplace for compromised credentials.


The Hacker News
In a dramatic turn of events, LockBitSupp, a key figure in the notorious LockBit ransomware operation, is reportedly cooperating with law enforcement.


The Cyber Express
ThreeAM ransomware group has struck again, this time targeting Abcor in Australia and MTM Robotics in the United States. The


The Record
Nearly two years after its creation, a task force meant to streamline federal efforts to combat ransomware hopes to further cement how the government handles key aspects of such attacks and do a better job trumpeting its contributions to the broader fight.


The Hacker News
Bumblebee, QakBot, Zloader, & PikaBot are back, sneakier than ever. Don't trust those shady emails or downloads.


SecurityWeek
Patch Tuesday: Microsoft pushes a massive batch of security-themed updates and calls urgent attention to exploits bypassing security features.


Bleeping Computer
The Bumblebee malware has returned after a four-month vacation, targeting thousands of organizations in the United States in phishing campaigns.


SecurityWeek
Two individuals involved in hacking the taxi dispatch system at JFK airport have been sentenced to prison.


The Cyber Express
Garon Products Inc. finds itself ensnared in the web of cybercrime as it becomes the latest target of the ThreeAM

SecurityWeek
The US government slaps sanctions against six Iranian government officials linked to cyberattacks against Israeli PLC vendor Unitronics.


SecurityWeek
Joseph Garrison has received an 18-month prison sentence for accessing 60,000 DraftKings user accounts using credential stuffing.


SecurityWeek
Daniel James Junk sentenced to six years in prison for stealing millions in cryptocurrency through SIM swapping.


Infosecurity News
The US said the two Egyptian nationals provided cybersecurity training and support to ISIS leadership and supporters, as well as helping enable the group to use cryptocurrency


SecurityWeek
Matthew Philbert was sentenced to two years for launching cyberattacks on Canadian businesses and government entities.


The Hacker News
Faust, the untargeted ransomware variant, highlights the need for comprehensive protection.


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


Bleeping Computer
Governments struck back this week against members of ransomware operations, imposing sanctions on one threat actor and sentencing another to prison.

Security Affairs
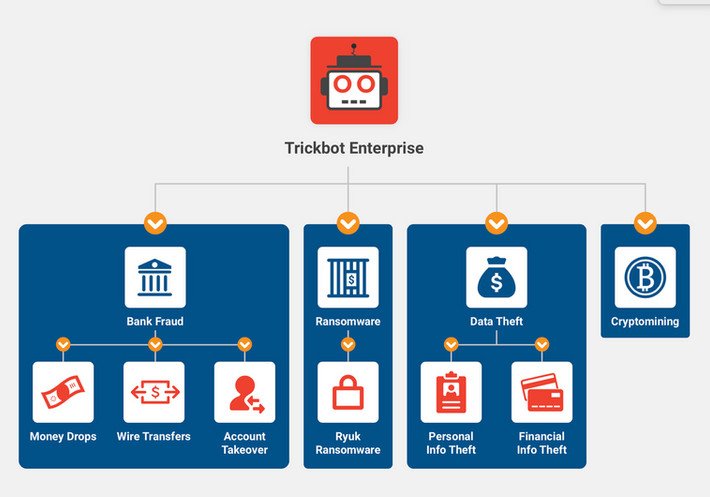
The Russian national malware developer Vladimir Dunaev was sentenced to more than 5 years in prison for his role in the TrickBot operation.


Infosecurity News
Ukraine’s security services said that the hacker targeted government websites and provided intelligence to Russia to carry out missile strikes


SecurityWeek
Vladimir Dunaev sentenced to 5 years in prison after admitting to participating in the development and distribution of the TrickBot malware.


The Hacker News
Russian national Vladimir Dunaev sentenced to 5 years and 4 months for TrickBot malware involvement.


DataBreaches
Following up on the case of Vladimir Dunaev, a Russian national who was extradited to the U.S. from Korea in 2021 and pleaded guilty in December 2023 for his...


Bleeping Computer
Russian national Vladimir Dunaev has been sentenced to five years and four months in prison for his role in creating and distributing the Trickbot malware used in attacks against hospitals, companies, and individuals worldwide.


The Record
A Russian developer of Trickbot malware has been sentenced to five years and four months in prison, the U.S. Department of Justice said on Thursday.


The Record
Kansas State University and a large community college near Portland, Oregon, each spent this week overcoming IT problems linked to cyberattacks.


Cyber Security News
Security analysts at Intrinsic recently discovered ThreeAM (aka 3 AM, ThreeAMtime) ransomware which has been actively attacking small and medium companies.


SecurityWeek
US charges Russian cybercriminals, including man allegedly involved in hacking of Neiman Marcus and Michaels Stores in 2013.


The Hacker News
Microsoft takes action against malware threat: disables ms-appinstaller protocol handler by default.


Ars Technica
Microsoft has honed its strategy to disrupt global cybercrime and state-backed actors.


SecurityWeek
Russian threat actor APT28 has been exploiting a no-interaction Outlook vulnerability in attacks against 14 countries.


The Cyber Express
A particularly nefarious Banking Trojan, TrickBot, has reemerged, this time with an Android variant named "TrickMo" - a reference to


SecurityWeek
Vladimir Dunaev pleads guilty to his involvement in the development and deployment of the notorious TrickBot malware.


Infosecurity News
40-year-old was extradited from South Korea


The Hacker News
Microsoft Warns of New CACTUS Ransomware Threat. Malvertising used to deploy DanaBot as initial access. Learn more about this evolving cyber threat.


DataBreaches
In October 2021, Russian national Vladimir Dunaev, was extradited to the U.S. from Korea. On November 30, he pleaded guilty. From the Department of Justice...


The Hacker News
Russian national Vladimir Dunaev found guilty for developing TrickBot malware, facing up to 35 years in prison.


Bleeping Computer
On Thursday, a Russian national pleaded guilty to charges related to his involvement in developing and deploying the Trickbot malware, which was used in attacks against hospitals, companies, and individuals in the United States and worldwide.


The Record
According to court documents, Vladimir Dunaev, 40, was a member of a cybercriminal organization that deployed Trickbot to steal money and install ransomware on victims’ computers.


The Record
The Ukrainian government has appointed Yury Myronenko, a decorated serviceman and air defense commander, as head of one of its main cybersecurity agencies amid a corruption probe.


The Record
The U.S. partnered with several nations in the Pacific to hand down sanctions on North Korea — particularly the country’s Kimsuky cyber espionage group — after the country launched a surveillance satellite last week.


SecurityWeek
US Treasury sanctions Sinbad, saying the cryptocurrency mixer is laundering funds for North Korean hacking group Lazarus.


Security Affairs
An international law enforcement operation dismantled the core of a ransomware group operating from Ukraine.


PCMag
The gang allegedly attacked targets, including large corporations, in 71 countries.


SecurityWeek
Police from several countries have dismantled a major Ukraine-based ransomware operation and arrested its alleged ringleader.


The Hacker News
A coordinated effort led to the arrest of key figures in Ukraine linked to various ransomware attacks, involving LockerGoga, MegaCortex, and Dharma.


Infosecurity News
Affiliate deployed LockerGoga, MegaCortex, Hive and Dharma


Bleeping Computer
In cooperation with Europol and Eurojust, law enforcement agencies from seven nations have arrested in Ukraine the core members of a ransomware group linked to attacks against organizations in 71 countries.


The Record
The international operation, centered on Kyiv, essentially neutralized a group known for deploying variants of LockerGoga, MegaCortex, Hive and Dharma ransomware, authorities said.

The Record
A Moldovan national has been extradited from the United Kingdom to face charges related to allegedly running an online marketplace selling access to compromised computers.


DarkReading
A literal seven-nation (cyber) army wasn't enough to hold back the famous initial access broker (IAB) for long — it's been chugging along, spreading ransomware, despite a massive takedown in August.


CSO
Researchers from Group-IB believe it's likely the group is an independent affiliate working for multiple ransomware-as-a-service operations


Cyber Security News
A new Ransomware-as-a-service (RaaS) provider has been discovered by researchers, which notably uses multiple ransomware families and is found to have links with several ransomware attacks since July 2022.

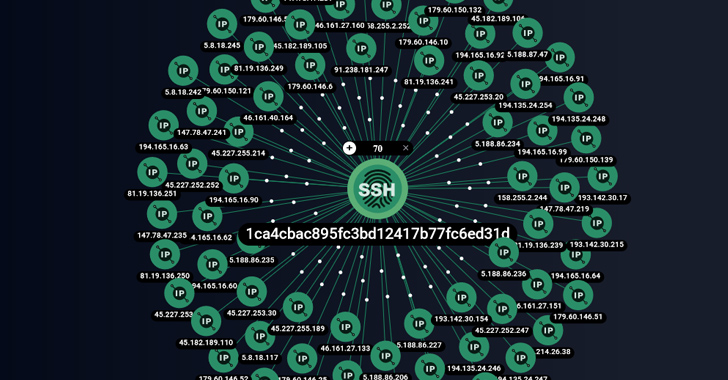
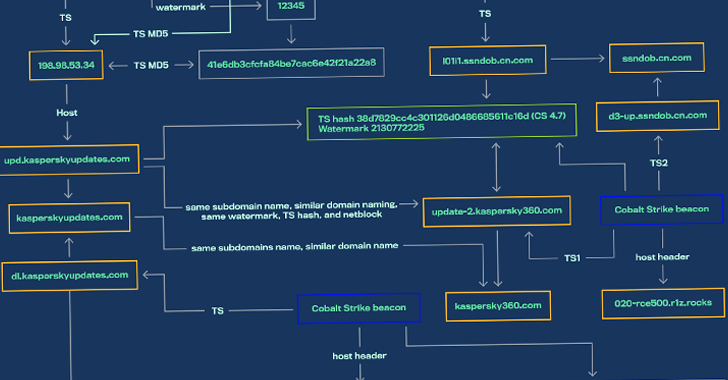
The Hacker News
Cyber experts uncover a new threat: ShadowSyndicate. Explore their connections to ransomware and the latest findings from cybersecurity experts.


Bleeping Computer
Security researchers have identified infrastructure belonging to a threat actor now tracked as ShadowSyndicate, who likely deployed seven different ransomware families in attacks over the past year.

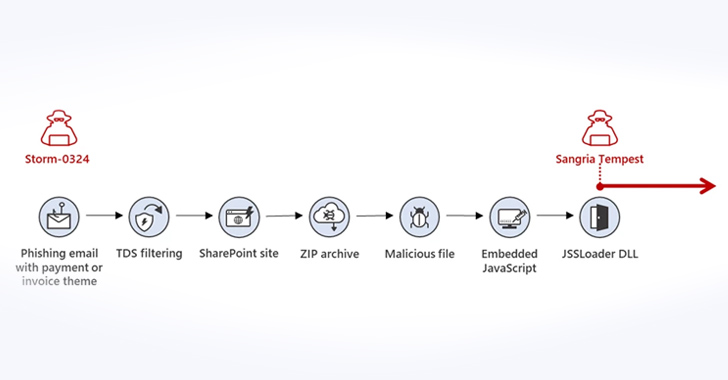
The Hacker News
Microsoft sounds the alarm on Storm-0324's tactics, luring its prey through Teams messages to breach corporate networks.


DataBreaches
On September 7, the U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC), in coordination with the United Kingdom, sanctioned 11...


Bleeping Computer
It started as a slow ransomware news week but slowly picked up pace with the Department of Justice announcing indictments on TrickBot and Conti operations members.


The Hacker News
U.S. and U.K. governments have jointly imposed sanctions on 11 individuals connected to the Russia-based TrickBot cybercrime group.


DarkReading
US Treasury officials said the sanctions move is part of its effort to combat Russian state-sponsored cybercrime.


SecurityWeek
The US and UK have announced sanctions against 11 more alleged members of the Russian cybercrime group Trickbot.


Trend Micro
Discover what the increased regulatory risk due to recent US and UK sanctions imposed on TrickBot and Conti cybercriminals mean for CISOs and board members.


DataBreaches
WASHINGTON — Today, the United States, in coordination with the United Kingdom, sanctioned eleven individuals who are part of the Russia-based Trickbot...


Infosecurity News
These new sanctions follow a first wave in February 2023, where seven Russians involved with Trickbot and Conti were also sanctioned

Bleeping Computer
The USA and the United Kingdom have sanctioned eleven Russian nationals associated with the TrickBot and Conti ransomware cybercrime operations.

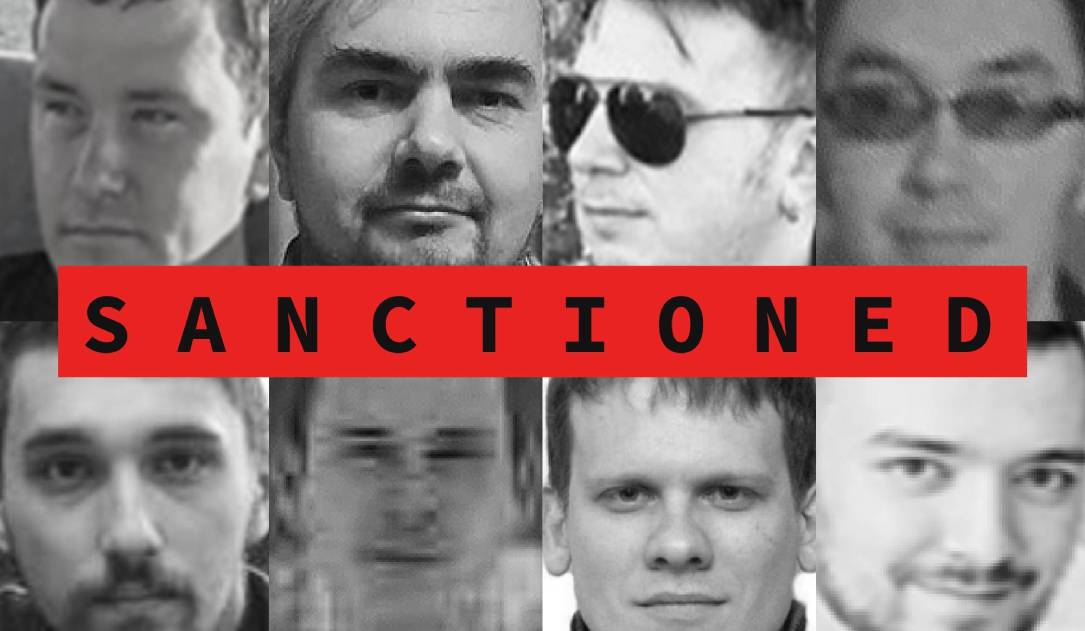
The Record
Eleven Russian nationals alleged to have been part of the criminal group operating the Trickbot malware and Conti ransomware schemes were sanctioned by authorities in the United States and United Kingdom.

The Record
The indictments are the latest example of a more aggressive U.S. law enforcement strategy to battling cybercrime.


DarkReading
"Operation Duck Hunt" is not likely to eliminate the initial access botnet forever, but the proactive removal of the malware from victim machines by law enforcement is one of the largest and most significant efforts of its kind.


Infosecurity News
SonicWall’s report finds that ransomware rebounded in Q2 2023 following a major reduction in Q1


DarkReading
Researchers have delivered working exploits for RouterOS, which when combined with default admin passwords can be a recipe for cyber disaster.


The Hacker News
BlackCat ransomware now spreading via malvertising! Watch out for rogue installers disguised as legitimate apps like WinSCP.


The Hacker News
New JavaScript Dropper PindOS delivers dangerous payloads like Bumblebee and IcedID, acting as loaders for ransomware and other malware.


Cyber Security News
Implementing a ransomware attack prevention plan can provide businesses with the necessary tools to protect your organisation.

The Hacker News
AceCryptor: the crypter malware that packs a punch! Since 2016, it's been hiding numerous strains of malware under its cloak


Cyber Security News
A malware attack is a cyber-attack using malicious software to gain unauthorized access to a computer system or network.

Cyber Security News
Bridewell's Cyber Threat Intelligence (CTI) team has discovered previously undetected Ursnif infrastructure used in 2023 campaigns, suggesting that the malware operators have not yet utilized this highly elusive infrastructure.


DataBreaches
Lawrence Abrams reports: Ex-Conti ransomware members have teamed up with the FIN7 threat actors to distribute a new malware family named ‘Domino’...


Security Affairs
A new malware, dubbed Domino, developed by the FIN7 cybercrime group has been used by the now-defunct Conti ransomware gang. IBM Security X-Force researchers recently discovered a new malware family, called Domino, which was created by developers associated with the FIN7 cybercriminal group (tracked by X-Force as ITG14). FIN7 is a Russian criminal group (aka Carbanak) that has […]


Bleeping Computer
Ex-Conti ransomware members have teamed up with the FIN7 threat actors to distribute a new malware family named 'Domino' in attacks on corporate networks.

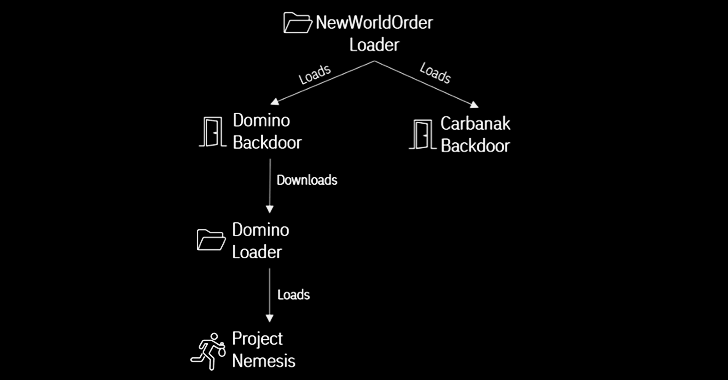
The Hacker News
Cybercriminal syndicates FIN7 and ex-Conti members have teamed up to launch Domino malware attacks.


Security Affairs
The infamous Emotet malware is back after a short hiatus, threat actors are spreading it via Microsoft OneNote email attachments. The Emotet malware returns after a three-month hiatus and threat actors are distributing it via Microsoft OneNote email attachments to avoid detection. The Emotet banking trojan has been active at least since 2014, the botnet is operated by a threat actor tracked […]


The Hacker News
Emotet is back, now hiding in Microsoft OneNote email attachments to bypass macro-based security restrictions and compromise systems.


Bleeping Computer
A decryption tool for a modified version of the Conti ransomware could help hundreds of victims recover their files for free.

The Hacker News
Threat actors from Chinese and Russian cybercriminal ecosystems have been observed using a new malware designed to load Cobalt Strike.

CSO
Akamai report highlights how widespread malware threats remain, noting the dangers of threats specific to DNS infrastructure.


Ars Technica
Quoting Herman Melville is only one of Emotet's latest innovations.


DarkReading
More than two years after a major takedown by law enforcement, the threat group is once again proving just how impervious it is against disruption attempts.

The DFIR Report
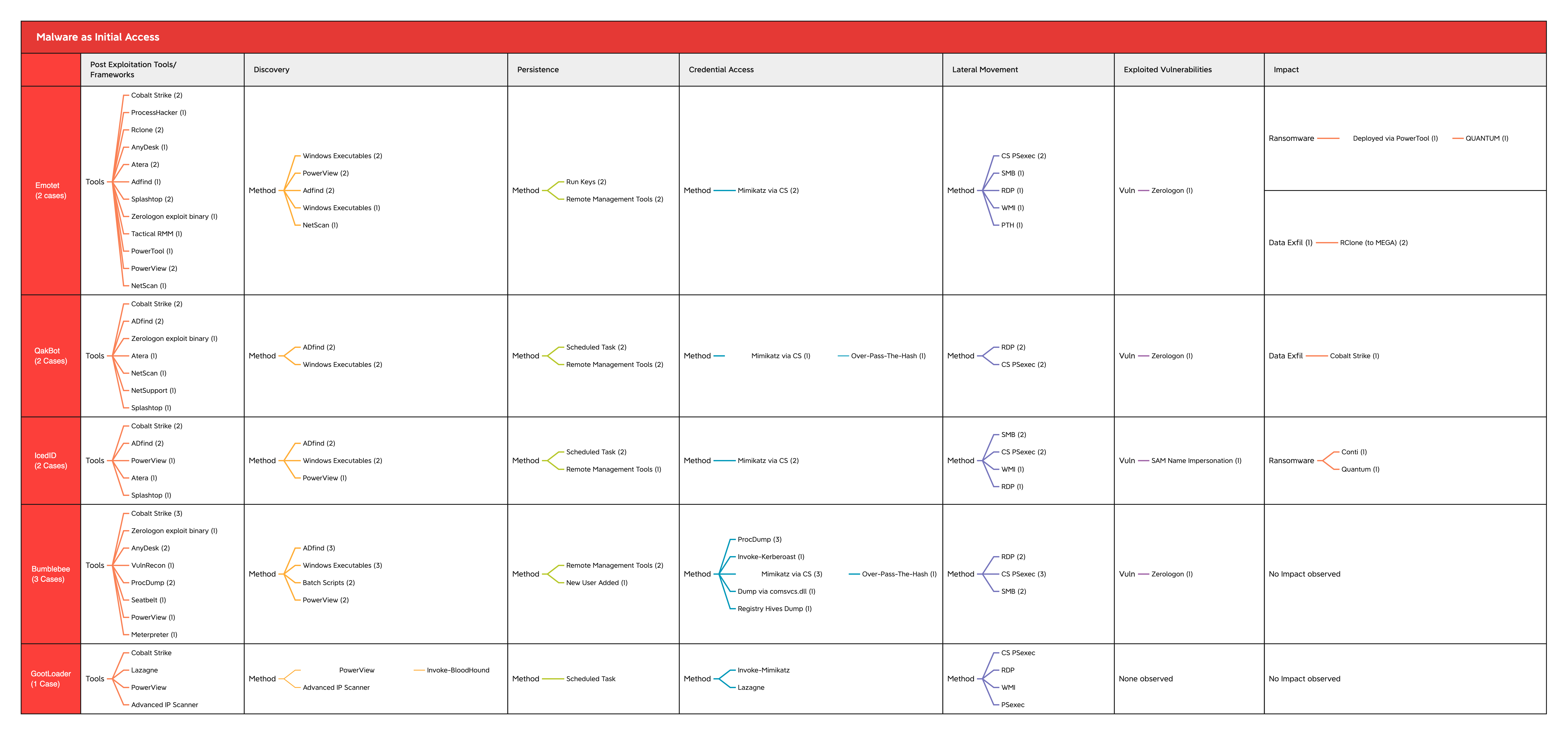
As we move into the new year, it’s important to reflect on some of the key changes and developments we observed and reported on in 2022. This year’s year-in-review report … Read More


DarkReading
Mobile malware developers were busy bees in 2022, flooding the cybercrime landscape with twice the number of banking trojans than the year before.


Infosecurity News
Recorded Future claims war in Ukraine is having a major impact


CSO
Study and prepare for these five threats and you will be well on your way to protecting your network, assets, and employees.


CSO
Study and prepare for these five threats and you will be well on your way to protecting your network, assets, and employees.


The Hacker News
Russia's cyber attacks against Ukraine surged by 250% in 2022, according to a report by Google's Threat Analysis Group and Mandiant.


The Record
Deputy Attorney General Lisa Monaco said the feds will continue to use sanctions and hacking operations as tools against ransomware groups.


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. If you want to also receive for free the newsletter with the international press subscribe here. Clop ransomware claims the hack of 130 orgs using GoAnywhere MFT flaw CISA adds Fortra […]


Bleeping Computer
From ongoing attacks targeting ESXi servers to sanctions on Conti/TrickBot members, it has been quite a busy week regarding ransomware.


Cyber Security News
Seven members of the Trickbot cybercrime gang, which has its base in Russia, have been designated by the US and UK.

The Hacker News
Seven Russian nationals have been sanctioned by the governments of the United Kingdom and the United States for their involvement in the TrickBot.
Loading more articles....