

Trend Micro
The Current Security State of Private 5G Networks
Private 5G networks offer businesses enhanced security, reliability, and scalability. Learn more about why private 5G could be the future of secure networking.


Trend Micro
Private 5G networks offer businesses enhanced security, reliability, and scalability. Learn more about why private 5G could be the future of secure networking.


SC Magazine
Cloud computing improves scalability and may cut costs, but network-security practitioners may have difficulty adjusting. Here are some challenges and solutions of cloud-based network security.

Cyber Security News
Resecurity, Inc. (USA) noticed a spike in phishing content delivered via Azure Front Door (AFD). Azure Front Door is a modern cloud content delivery network (CDN) service that delivers high performance, scalability, and secure user experiences for your content and applications.


Trend Micro
Discover how Trend is strengthening its endpoint solutions to detect fileless attacks earlier. By leveraging Intel Threat Detection Technology, Trend enhances the scalability and resiliency of its solutions.


Security Affairs
Understanding cybersecurity aspects addressed by Cloud Access Security Broker (CASB) and Secure Access Service Edge (SASE) In an increasingly digital world, where businesses rely on cloud services and remote access, cybersecurity has become paramount. As organizations strive to safeguard their data, applications, and networks, two prominent concepts have emerged as vital components of modern cybersecurity: […]


The Cyber Express
by Shrikant Navelkar, Director, Clover Infotech The need for hybrid data centers is closely tied to the growing adoption of


The Hacker News
Data privacy and compliance are paramount in the cloud era! Explore how businesses can ensure regulatory adherence while leveraging the benefits.


The Cyber Express
By Shrikant Navelkar, Director, Clover Infotech Due to the significant advancements in the IT industry, the adoption of cloud computing

.webp)
Cyber Security News
Secure Network As a Service for MSP: 1. Perimeter 81 2. Cloudflare 3. Netskope 4. VMware 5. Palo Alto Networks 6. Aarna Networks.


The Hacker News
Protect your organization from security nightmares. Learn how modern API management with Gloo Gateway can fortify your defenses against data breaches


Bleeping Computer
How do you choose between Penetration Testing as a Service (PTaaS) or traditional web application pen testing? Learn more from Outpost24 on the differences between both pentesting methods.


The Hacker News
Cyber threats are escalating, making Privileged Access Management essential. Meet One Identity PAM Essentials: a cloud-based solution prioritizing sec


The Cyber Express
By Shrikant Navelkar, Director, Clover Infotech In today’s digital era, data holds immense significance. Database management traditionally was considered the


The Cyber Express
By Neelesh Kripalani, Chief Technology Officer, Clover Infotech In 2024 and beyond, the IT industry is poised for innovation and


Bleeping Computer
There are seven main stages of a complex pen testing process that must be followed in order to effectively assess an application's security posture. Learn more from OutPost24 about these stages and how PTaaS can find flaws in web applications,


The Hacker News
Wazuh Offers XDR Functionality at a Price Enterprises Will Love — Free!


SecurityWeek
Radiant Security gets $15 million in new financing as investors double down on early stage companies experimenting with AI technology.


Bleeping Computer
Open source software hosting provider Fosshost will no longer be providing services as it reaches end of life. Fosshost project volunteers announced the development this weekend following months of difficulties in reaching the leadership including the CEO.


SecurityWeek
Nexusflow scores funding to build an open-source LLM that can deliver high accuracy when retrieving data from multiple security sources.

Cyber Security News
Network as a Service for MSSP : 1. Perimeter 81 2. Cloudflare 3. Prisma Cloud 4. Megaport 5. Akamai 6. Aryaka 7. Converged Cloud.

SecurityWeek
SecurityWeek will host its 2022 Cloud Security Summit, Presented by Palo Alto Networks, as a virtual event on June 15, 2022.


The Cyber Express
by Puneet Gupta, VP & MD, NetApp India/SAARC In the current landscape of technological prowess, businesses are rapidly moving to


HACKRead
Protect your clients' businesses from cyber threats with Cybersecurity Management Software. Explore the unified control panel, real-time threat detection, and


The Cyber Express
By Puneet Gupta, Vice President and Managing Director, NetApp India/SAARC Propelled by the evolving trends in data, data virtualization is


HACKRead
Protect your clients' businesses from cyber threats with Cybersecurity Management Software. Explore the unified control panel, real-time threat detection, and


SecurityWeek
The open source platform Tazama provides cost-effective monitoring of digital financial transactions to prevent fraud in real time.


Cyber Security News
WAF solutions or Web Application Firewall solutions are indispensable today in ensuring round-the-clock, proactive security against a wide range of threats – known and emerging.


Bleeping Computer
Organizations commonly change their pen test providers annually. Learn more from Outpost24 about the drawbacks of rotating pentest providers and the benefits of the Penetration Testing as a Service (PTaaS) model.


The Cyber Express
Choosing the right SOC as a Service (SOCaaS) is crucial for businesses aiming to strengthen their cyber defenses. This decision


The Hacker News
Cyber threat landscape is evolving at a rapid pace, and defending against these modern cyber threats is a monumental challenge.


CSO
New program provides managed service providers dedicated, enterprise-level threat prevention, detection, and response capabilities.


Bleeping Computer
Bitwarden, the maker of the popular open-source password manager tool, has released 'Secrets Manager,' an end-to-end encrypted secrets manager for IT professionals, software development teams, and the DevOps industry.


SecurityWeek
Threat detection and response firm SecureWorks is laying off 15% of its staff (roughly 300 people) in the second round of firings this year.


Security Affairs
Cisco warns of a critical unauthenticated REST API access vulnerability, tracked as CVE-2023-20214, impacting its SD-WAN vManage. Cisco addressed a critical unauthenticated REST API access vulnerability, tracked as CVE-2023-20214 (CVSS Score 9.1), impacting its SD-WAN vManage. An unauthenticated, remote attacker can exploit the vulnerability to gain read permissions or limited write permissions to the configuration […]


Infosecurity News
The UK’s National Cyber Security Centre wants to help organizations migrate their SCADA systems to the cloud


Cyber Security News
In a groundbreaking revelation, Google has ushered in a new era of artificial intelligence with the introduction of Gemini, its most formidable and sophisticated AI model to date.


Bleeping Computer
Microsoft has announced that Window Server 2022, a Long Term Servicing Channel (LTSC) release with ten years of support, is generally available starting today.


Bleeping Computer
The DevOps Foundation & Professional Bundle helps you dive into this exciting field, with two beginner-friendly courses working towards EXIN certification, and you can get it today for only $49.


Latest Hacking News
Researchers have reported multiple bugs dubbed “ExtraReplica” affecting Microsoft Azure. Exploiting the vulnerabilities could allow an adversary to access user databases. Microsoft patched the bugs in time following the bug report. Microsoft Azure ExtraReplica Bugs Researchers from


SecurityWeek
Enterprise vs. Open Source: When putting a platform into production, an enterprise-ready solution will ensure you can keep up with business demands.


SecurityWeek
The latest wave of SD-WAN transformation involves integrating SD-WAN with a converged security stack via SSE or SASE architectures.


CSO
Data security and protection are the main upside for IBM’s upcoming storage offering, which combines the company’s own products with those from third parties.


Cyber Security News
Cisco introduced its latest innovation, Cisco Hypershield, marking a significant milestone in the evolution of cybersecurity.


CyberNews
Billionaire's Twitter takeover prompts many to seek out alternative social media outlet, which runs on an open-source platform.


Infosecurity News
The breach, which unfolded on September 28, compelled ESO to shut down systems temporarily


Cyber Security News
A new incorrect access control vulnerability has been discovered in Apache Kafka that could allow threat actors to compromise the CIA

SecurityWeek
Researchers have published full technical details on a high-severity remote code execution vulnerability addressed in the latest version of Apache Cassandra.

The Hacker News
Microsoft's Patch Tuesday updates for the month of April have addressed a total of 128 security vulnerabilities.


ZDNet
Two of the vulnerabilities have a remediation date of March 1.


Cyber Security News
SDP vs VPN - Software-Defined Perimeter (SDP) and Virtual Private Networks (VPN) are two of the most extensively used security solutions.


Cyber Security News
Best SASE Solutions & Vendors (Secure Access Service Edge): 1. Perimeter81 2. Cisco Umbrella 3. Zscaler 4. Palo Alto 5. Prisma Access.


CyberSecurity Dive
Long before a data breach, well-prepared companies set up incident response teams with workers from multiple departments.


Cyber Security News
Best Software Define Perimeter Tools & Software : 1. Perimeter 81 SDP 2. Good Access 3. Twingate SDP 4. NetMotion SDP 5. Appgate SDP and more.


CyberSecurity Dive
Threat actors used the W3LL phishing kit to target more than 56,000 accounts, ultimately compromising 14% of them since last October, Group-IB found.


The Cyber Wire
In the dynamic landscape of cybersecurity, the automation of routine tasks emerges as a transformative force, driving substantial cost reductions in security operations. AI plays a pivotal role in diminishing the reliance on manual intervention on tasks such as log analysis, vulnerability and risk assessments thereby conserving valuable time and human resources. Human error, a significant factor in generating false positives and overlooking potential threats, can lead to unnecessary expenditure of time and resources in investigating non-existent issues while potentially neglecting real security incidents. By leveraging the power of AI to alleviate the burden of manual intervention, businesses can not only optimize time and resources but also fortify their defenses against potential threats, marking a crucial stride towards a more resilient and secure digital environment.


CSO
Critical Start’s new offering is designed to handle security teams with specialized detection and response tooling for operational technology systems.


Cyber Security News
Parrot OS 5.1 is released after six months of Parrot 5.0 and it’s powered by Linux kernel 5.18 which reached end of life in August. Nevertheless, the new kernel comes as a major update from Linux kernel 5.16 used in the previous release.


The Cyber Express
The notorious LockBit has claimed an alleged cyberattack on Allied Telesis, Inc., a prominent American telecommunication equipment supplier. The purported


The Cyber Express
The significance of cloud security has risen dramatically in the past few years. As businesses move towards digitalization, safeguarding applications

.webp)
Cyber Security News
NCSC has recently published guidelines designed to assist organizations in securely transitioning their SCADA systems to cloud environments.


The Record
Policymakers must do more to confront the increasing vulnerability critical infrastructure sectors face due to their growing reliance on cloud computing, a new Atlantic Council report urges.


SecurityWeek
Organizations must rethink ways to jointly achieve both visibility and security for networks that are not one-size-fits-all.

HACKRead
British Virgin Islands, 26 February 2024 - Friendzone, the sustainable and scalable Web3 platform redefining Social Finance (SocialFi) on the blockchain, has


HACKRead
It is essential to be knowledgeable about security fundamentals and stay up-to-date with emerging technologies and methodologies.

ZDNet
Adobe ended support for the Magento 1 e-commerce platform in 2020 but hundreds of companies still use it.


Trend Micro
Cloud object storage is a core component of any modern application, but most cloud file storage security is insufficient.


Cyber Security News
The emergence of Large Language Models (LLMs) is transforming NLP, enhancing performance across NLG, NLU, and information retrieval tasks.


The Cyber Express
A critical security vulnerability(CVE-2024-4323) referred to as "Linguistic Lumberjack," has been found within Fluent Bit, a widely-used logging and metrics


Cyber Security News
Best Cloud Service Providers: 1. AWS 2. Google Cloud 3. Azure 4. Oracle Cloud 5. VMware 6. DigitalOcean 7. Rackspace 8. IBM Cloud.


The Hacker News
Creating a malware analysis lab doesn't have to be complicated or expensive. Explore different options like virtualization, dedicated hardware.


Bleeping Computer
A threat actor is selling on hacking forums what they claim to be a new UEFI bootkit named BlackLotus, a malicious tool with capabilities usually linked to state-backed threat groups.

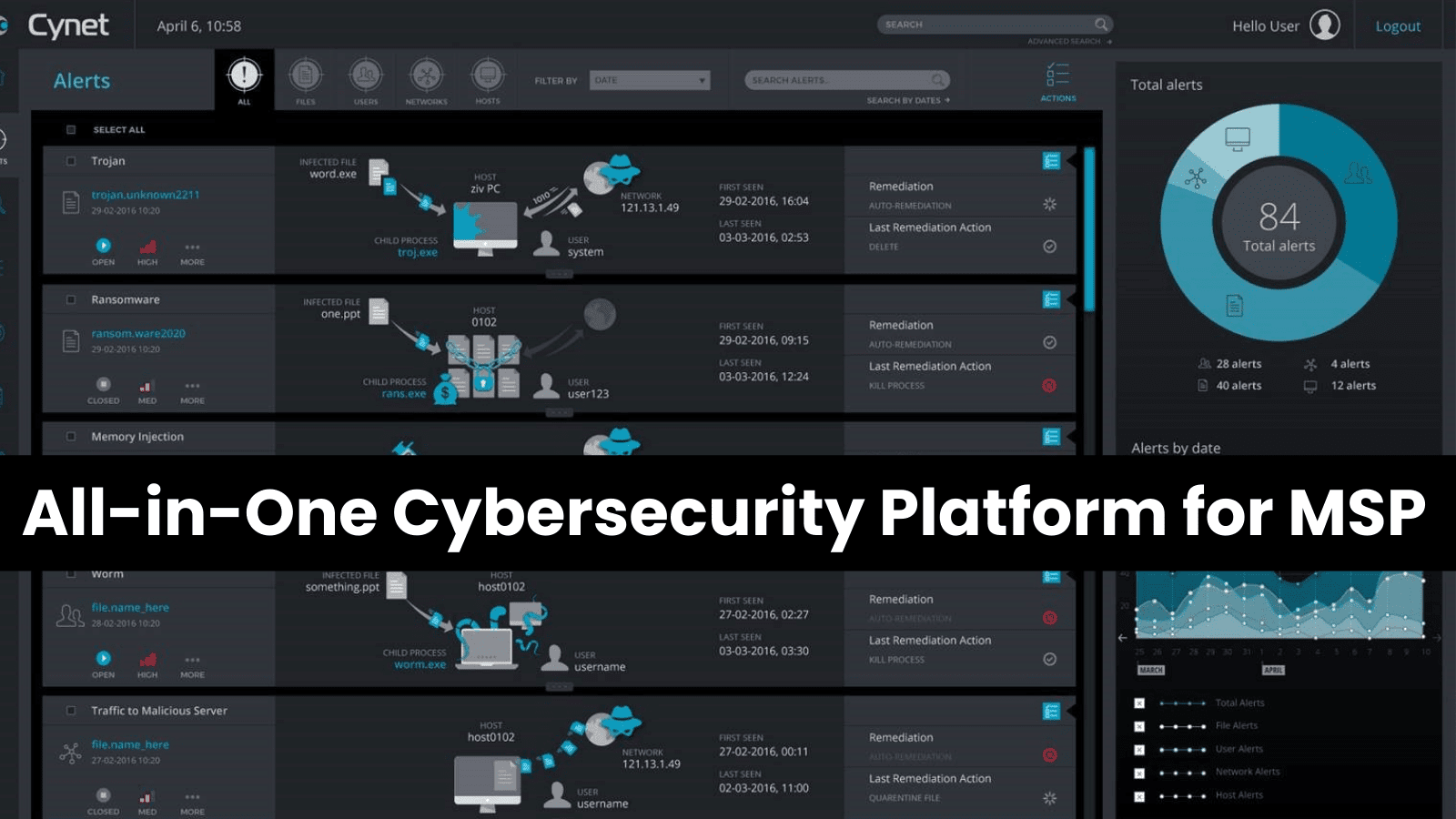
Cyber Security News
Managed service providers (MSPs) are on the front lines of soaring demand for cybersecurity services as cyberattacks increase in volume and sophistication.


The Cyber Express
In an era defined by rapid technological advancements and evolving cyber threats, the outsourcing of IT security services has emerged

SecurityWeek
A lobbying outfit representing big tech is calling on the Office of Management and Budget (OMB) to "discourage agencies" from requiring SBOMs, arguing that “it is premature and of limited utility.”


Cyber Security News
Multiple vulnerabilities have been discovered in Titan MFT and Titan SFTP servers owned by South River Technologies.

.webp)
Cyber Security News
Microsoft launched Copilot for Security, marking the advent of the first generative AI security product designed for widespread application.


CSO
DDoS IP Protection for SMBs is designed to provide enterprise-grade distributed denial of service protection at a price that's attractive to small and medium-size companies.


CSO
Technology reduces risks of data exposure and can be used with AWS Key Management Service, Microsoft Azure Key Vault, and Google Cloud Key Management Service.


CSO
The SaaS offering is specifically targeted at providing organizations visibility and protection over third-party and homegrown generative AI tools.

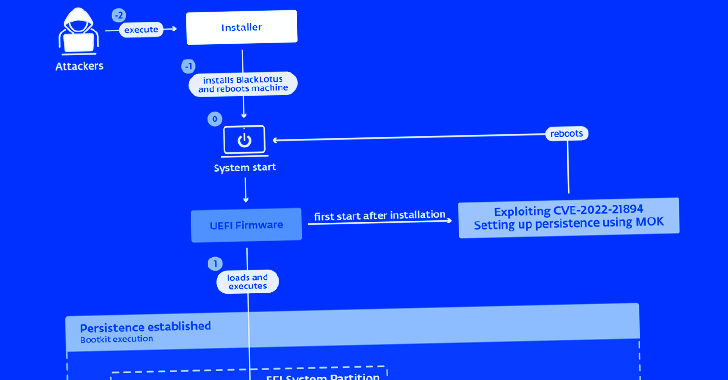
The Hacker News
ESET warns of a new, powerful UEFI bootkit malware called BlackLotus that can bypass Secure Boot protection on Windows 11 systems.


SecurityWeek
Investing in a solution that can integrate with existing infrastructure should give your security team visibility into what's happening on your network


Cyber Security News
Best Web Filtering Solutions: 1. Perimeter81 2. Cisco Umbrella 3. Symantec WebFilter 4. Barracuda Web Security Gateway 5. McAfee Web Gateway


SC Magazine
Zero trust, access certification campaigns and regular AD risk assessments are more critical than ever.


CSO
The access governance capability can allow access risk visibility, attack surface reduction, access right management, zero-trust enforcement, and insider risk mitigation.


Bleeping Computer
Wazuh is a free and open source security platform that provides unified SIEM and XDR protection. It protects workloads across on-premises, virtualized, containerized, and cloud-based environments. Wazuh is one of the fastest growing open source security solutions, with over 10 million downloads per year.

Cyber Security News
When it comes to security on the cloud, the traditional tools and methods are usually not enough to provide you with the needed protection. Namely, establishing perfect cloud identity governance is vital to ensuring your data and digital assets are protected from breaches and leaks. One of the biggest benefits of cloud computing is the […]


CSO
Hyperscalers grapple with Linguistic Lumberjack vulnerability.


The Hacker News
Worried about your organization's security? Managed Detection and Response (MDR) is the key!

Cyber Security News
A software Bill of Materials is based on the concept of a manufacturing Bill of Materials, which is an inventory of all the elements involved in a product. Manufacturers in the automotive industry, for example, keep a thorough Bill of Materials for each vehicle. The parts made by the original equipment manufacturer and parts from […]


CyberSecurity Dive
Cloud-ready Privileged Access Management (PAM) is vital to your cyber defense strategy.


Trend Micro
Trend Micro’s Chief Technology Strategy Officer discusses the biggest cybersecurity trends and what to watch for in 2024.


Computerworld
Apple first introduced declarative device management for MDM systems managing iPads and iPhones at WWDC in 2021.


Security Affairs
ESET discovered a stealthy Unified Extensible Firmware Interface (UEFI) bootkit dubbed BlackLotus that is able to bypass the Secure Boot on Windows 11. Researchers from ESET discovered a new stealthy Unified Extensible Firmware Interface (UEFI) bootkit, named BlackLotus, that is able to bypass Secure Boot on Windows 11. Secure Boot is a security feature of the […]

Cyber Security News
Whether you are a developer or not, we all use APIs (Applications Programming Interfaces). You can use them as a developer, consumer, or end user. For example, let us look at some things you might do in a day. You wake up in the morning and order breakfast online. When it is delivered, you make […]


Bleeping Computer
Pen Testing as a Service and Traditional web application pen testing offers two different approaches to securing your applications. Learn more from Outpost24 on which approach may be best for your business.


SecurityWeek
Framing your cloud security needs around workloads, identity, posture, and enterprise can help you better understand your specific needs.


The Cyber Express
CyberArk, a leading identity security provider announced its definitive agreement to acquire Venafi, a leading machine identity management provider from


The Hacker News
Let’s explore why confidence in security lags infrastructure upgrades and how OPSWAT closes that gap.


Cyber Security News
Best Network Security Solutions for IT Managers : 1. Perimeter 81 2. Palo Alto Networks 3. Cisco 4. Rapid 5. Fortinet 5. Sophos.


CyberSecurity Dive
CVE overload and a lengthy backlog has meant the federal government’s repository of vulnerability data can’t keep up with today’s threat landscape.
Loading more articles....