

Infosecurity News
NCSC’s New Mobile Risk Model Aimed at “High-Threat” Firms
The UK’s National Cyber Security Centre claims its AMS model will protect firms from state-backed mobile threats


Infosecurity News
The UK’s National Cyber Security Centre claims its AMS model will protect firms from state-backed mobile threats


Bleeping Computer
Microsoft has fixed a known issue causing incorrect BitLocker drive encryption errors in some managed Windows environments.


The Hacker News
Unlock Endpoint Security with our top 10 must-know tips! From MFA to EDR, discover how to protect your digital kingdom.


SecurityWeek
Ivanti releases patches for 27 vulnerabilities in the Avalanche MDM product, including critical flaws leading to command execution.

Security Affairs
Ivanti addressed two critical flaws in its Avalanche mobile device management (MDM) solution, that can lead to remote command execution.


Infosecurity News
Ivanti has fixed two critical vulnerabilities in its Avalanche MDM product which could lead to remote code execution


Bleeping Computer
Ivanti has released security updates to fix 27 vulnerabilities in its Avalanche mobile device management (MDM) solution, two of them critical heap overflows that can be exploited for remote command execution.


Security Affairs
Apple is warning iPhone users in over 90 countries of targeted mercenary spyware attacks, Reuters agency reported.


Computerworld
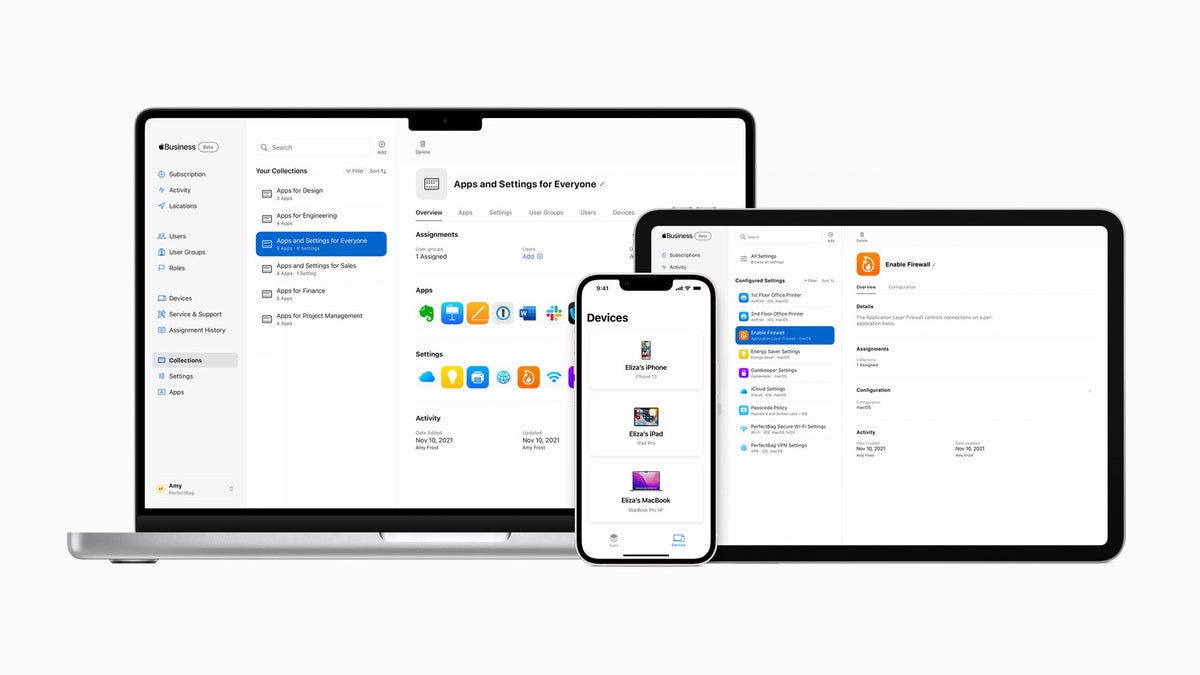
Unified endpoint management software lets IT manage all endpoint devices — smartphones, laptops, desktops, printers, IoT devices, and others — from a single management console. Here’s what to look for in a UEM platform and key vendors to consider.


Bleeping Computer
Microsoft has released the KB5036892 cumulative update for Windows 10 21H2 and Windows 10 22H2 with twenty-three changes and two new features.


Bleeping Computer
Microsoft has released the KB5036893 cumulative update for Windows 11 23H3, which includes 29 changes and fixes and enables the Moment 5 features for every user.


Bleeping Computer
Microsoft has released the optional KB5035941 preview cumulative update for Windows 10 22H2, introducing widgets on the lock screen, Windows Spotlight on the desktop, and 21 other fixes or changes.


SecurityWeek
Leen Security, a new startup building technology to help reduce chaos in the data security space, has banked a $2.8 million pre-seed funding.


Computerworld
Many of the buzziest IT trends — low-code automation, digital employee experience, and yes, even generative AI — are making their way into the major mobility management platforms. Here’s what to look for in 2024 and beyond.


Computerworld
Unified endpoint management (UEM) platforms now dominate the enterprise mobility space. Our chart lets you quickly compare features and functions from eight top vendors.


SecurityWeek
Chinese hackers use Android and iOS trojans to obtain information needed to steal money from victims’ bank accounts.


HACKRead
Group-IB has discovered a new iOS Trojan, dubbed GoldPickaxe.iOS designed to steal facial recognition data, ID documents, and intercept SMS.


Infosecurity News
Group-IB warns of new Trojan GoldPickaxe designed to bypass banking facial recognition with deepfakes


The Hacker News
Chinese-speaking cybercrime group behind sophisticated banking trojans like GoldPickaxe is targeting iOS and Android users.


Bleeping Computer
A new iOS and Android trojan named 'Gold Pickaxe' employs a social engineering scheme to trick victims into scanning their faces and ID documents, which are believed to be used to generate deepfakes for unauthorized banking access.


The Record
Researchers at Group-IB detected new but familiar activity by suspected China-based cybercriminals. The campaign included requests for victims to record videos that were used for identity fraud.


Bleeping Computer
Microsoft has released the KB5034765 cumulative update for Windows versions 23H2 and 22H2 to fix several bugs in the OS, including an issue that causes problems with the Start menu.


SecurityWeek
Ivanti is struggling to hit its own timeline for the delivery of patches for critical -- and already exploited -- flaws in VPN appliances.


SecurityWeek
Goldman Sachs leads wireless threat intelligence firm Bastille Networks’ $44 million Series C funding round.


Bleeping Computer
Microsoft released the January 2024 preview update for Windows 11 versions 22H2 and 23H2, which comes with Bluetooth audio bug fixes and addresses 24 known issues.


Bleeping Computer
Microsoft has released the January 2024 preview update for Windows 10, version 22H2, which adds Digital Markets Act (DMA) compliance in the European Economic Area (EEA) to allow European users to uninstall all apps in Windows by March 6.


SecurityWeek
The US government’s cybersecurity agency CISA ramps up the pressure on organizations to mitigate two exploited Ivanti VPN vulnerabilities.


Computerworld
Microsoft is easing its way into 2024 with a low-key update for Windows and its other apps and platforms.


SecurityWeek
Ivanti confirms active zero-day exploits, ships pre-patch mitigations, but says comprehensive fixes won't be available until January 22.


SecurityWeek
CVE-2023-39336, a critical vulnerability in Ivanti EPM, may lead to device takeover and code execution on the server.


The Hacker News
Ivanti releases updates for a critical remote code execution security flaw in Endpoint Manager.


Bleeping Computer
Ivanti fixed a critical remote code execution (RCE) vulnerability in its Endpoint Management software (EPM) that can let unauthenticated attackers hijack enrolled devices or the core server.


SecurityWeek
Ivanti has patched 20 vulnerabilities in its Avalanche MDM product, including a dozen remote code execution flaws rated critical.


Infosecurity News
Ivanti releases updates to fix 22 vulnerabilities in its Avalanche mobile device management product


Bleeping Computer
Ivanti has released security updates to fix 13 critical security vulnerabilities in the company's Avalanche enterprise mobile device management (MDM) solution.


Computerworld
Microsoft this month delivered a seriously light set of updates on Patch Tuesday, perhaps the lightest I have ever seen. There are no zero-days, for instance, which is a great way to end the year.


Computerworld
The new protection follows incidents in which criminals apparently spied on users to get passcodes before stealing their iPhones.


Cyber Security News
A post-exploitation tampering technique has been discovered that allows the malware to visually trick the user into thinking their iPhone is in Lockdown Mode.


SecurityWeek
iVerify, a seed-stage startup spun out of Trail of Bits, ships a mobile threat hunting platform to neutralize iOS and Android zero-days.


Computerworld
Microsoft's Patch Tuesday release for November delivers 63 updates, with three zero-day flaws affecting Windows and Office. That makes quick patching a must.


The Hacker News
Novel attack methods targeting Google Workspace & Cloud Platform could enable ransomware and data breaches.


Bleeping Computer
Microsoft has released the KB5032189 cumulative update for Windows 10 21H2 and Windows 10 22H2, which contains eleven fixes for various issues.


Computerworld
Microsoft has brought biometric sign-in to Windows 10 business and enterprise users with Windows Hello for Business. Here’s how it works and how to deploy it to your users.


Cyber Security News
SaaS Security Admin Guide: 1. Encryption 2. Backup and Recovery 3. Data Residency 4. Regular Audits 5. Data Privacy 6. Least Privileges.


Bleeping Computer
Microsoft says a new known issue is causing desktop icons to behave erratically on systems with multiple displays when using the Windows Copilot AI-powered digital assistant.


Cyber Security News
App management encompasses each of these stages, ensuring a seamless experience for both users and admins. Let's explore how app management,


Bleeping Computer
Microsoft has released the optional KB5031445 Preview cumulative update for Windows 10 22H2 with nine improvements or fixes, including a fix for a memory leak in ctfmon.exe.


CSO
Zero-trust adoption is growing according to a recent report from Okta that found 61% of organizations have already implemented a zero-trust initiative.


Bleeping Computer
Microsoft warned customers this week of incorrect BitLocker drive encryption errors being shown in some managed Windows environments.


Computerworld
Over half the Macs in use today may not yet have installed the latest security software upgrades, warns a Qualys survey. You should take stock of your deployments.


CyberSecurity Dive
How to Guard Against SMS Phishing In Your Organization with Secure Service Desk Verification.


Cyber Security News
Best Software Define Perimeter Tools & Software : 1. Perimeter 81 SDP 2. Good Access 3. Twingate SDP 4. NetMotion SDP 5. Appgate SDP and more.


Infosecurity News
Jamf suggested firms enroll employees in a BYOD or Mobile Device Management (MDM) program


Computerworld
Apple's expansion of managed IDs for business users opens the door to helpful features such as iCloud backup and syncing — but beware of increased data sprawl and siloes.


The Hacker News
Surveyed leaders are confident in their SaaS security, yet 79% reported SaaS incidents in the last year.


SecurityWeek
A critical-severity vulnerability in the Ivanti Sentry (formerly MobileIron Sentry) product exposes sensitive API data and configurations.


Bleeping Computer
US-based IT software company Ivanti warned customers today that a critical Sentry API authentication bypass vulnerability is being exploited in the wild.

The Record
The bug occurs in Ivanti Sentry, formerly known as MobileIron Sentry, but “does not impact other Ivanti products, the company said.


SecurityWeek
Jenkins has announced patches for high and medium-severity vulnerabilities impacting several of the open source automation tool’s plugins.


Naked Security
Celebrating the true crypto bros. Listen now (full transcript available).


Naked Security
Apps on your iPhone must come from the App Store. Except when they don’t… we explain what to look out for.


SecurityWeek
Ivanti has patched critical- and high-severity vulnerabilities with the latest release of Avalanche enterprise MDM solution


Security Affairs
Threat actors rely on the ‘versioning’ technique to evade malware detections of malicious code uploaded to the Google Play Store. Google Cybersecurity Action Team (GCAT) revealed that threat actors are using a technique called versioning to evade malware detection implemented to detect malicious code uploaded to the Google Play Store. The technique is not new […]

The Hacker News
Malicious actors are using sneaky techniques like versioning to bypass Google Play Store's malware detection.

Cyber Security News
A critical vulnerability in Ivanti's MobileIron Core 11.2 version. This flaw can be exploited by a malicious actor to gain unauthorized access to restricted functions.


Bleeping Computer
IT software company Ivanti disclosed today a new critical security vulnerability in its MobileIron Core mobile device management software.


Infosecurity News
Agency says two bugs are being chained in attacks


Security Affairs
US CISA added a second actively exploited Ivanti ‘s Endpoint Manager Mobile (EPMM) vulnerability to its Known Exploited Vulnerabilities catalog. US Cybersecurity and Infrastructure Security Agency (CISA) added the second actively exploited Ivanti ‘s Endpoint Manager Mobile (EPMM, formerly MobileIron Core) vulnerability, tracked as CVE-2023-35081, to its Known Exploited Vulnerabilities Catalog. “The Cybersecurity and Infrastructure Security […]


SecurityWeek
The recently patched Ivanti EPMM zero-day CVE-2023-35078 has been exploited to hack the Norwegian government since at least April 2023.

The Hacker News
APT actors exploiting a dangerous zero-day vulnerability (CVE-2023-35078) in Ivanti Endpoint Manager Mobile


Bleeping Computer
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) warned today of state hackers exploiting two flaws in Ivanti's Endpoint Manager Mobile (EPMM), formerly MobileIron Core.


The Record
Hackers began exploiting a new vulnerability in Ivanti products to target the Norwegian government at least as early as April, according to a new joint advisory from cyber agencies in the U.S. and Norway.


CSO
The former MobileIron Core MDM system has a severe security flaw that could allow remote access, and all users are urged to patch their systems as soon as possible.


Cyber Security News
Endpoint Security Best Practices: Endpoint security serves as the first line of defense against cyberattacks for businesses.


Cyber Security News
Best Mobile app security scanners: 1. Android Debug Bridge 2. SandDroid 3. App-Ray4. Drozer 5. Synopsys 6. Quixxi 7. StacoAn 8. Ostorlab


The Hacker News
JumpCloud reacts to a cybersecurity incident, resets API keys for affected clients.

Infosecurity News
To assist customers in the process, JumpCloud provided a guide for resetting affected API keys


Bleeping Computer
JumpCloud, a US-based enterprise software firm is notifying several customers of an "ongoing incident." As a caution, the company has invalidated existing admin API keys to protect its customer organizations. Headquartered in Colorado, the cloud-based directory-as-a-service platform serves over 180,000 organizations across the world.


Cyber Security News
20 Best Identity Management Solutions - 1. Perimeter81 2. Okta 3. Microsoft Azure Active Directory 4. OneLogin 5. Ping Identity 6. SailPoint.


Computerworld
At this year's WWDC, the company introduced a raft of new capabilities related to Managed Apple IDs and to user identity as a whole.


Computerworld
Apple is focused on providing industry-leading privacy features and the best data security in the world. What did it announce at WWDC 2023?


Computerworld
The company's MDM Watchdog Utility monitors the MDM framework on devices and automatically forces the installation of software patches when they have not been put in place.

Computerworld
'I think some of the top people predict that the next big war is fought on cybersecurity,' Apple CEO Tim Cook told Time in 2016. Seven years later, it seems clear the struggle is real.

Cyber Security News
BEST Single Sign-on Solutions (SSO): 1. IBM Security Access Manager 2. RSA SecurID 3. Cisco Secure Access by Duo 4. OneLogin Single Sign-On.


Bleeping Computer
Microsoft has fixed a known issue triggering Windows Security warnings that Local Security Authority (LSA) Protection is off by removing the feature's UI from settings.


Computerworld
Aimed at executives, journalists, governments and other high value targets, Jamf Executive Threat Protection uses system logs and other data to identify if and when devices are attacked.

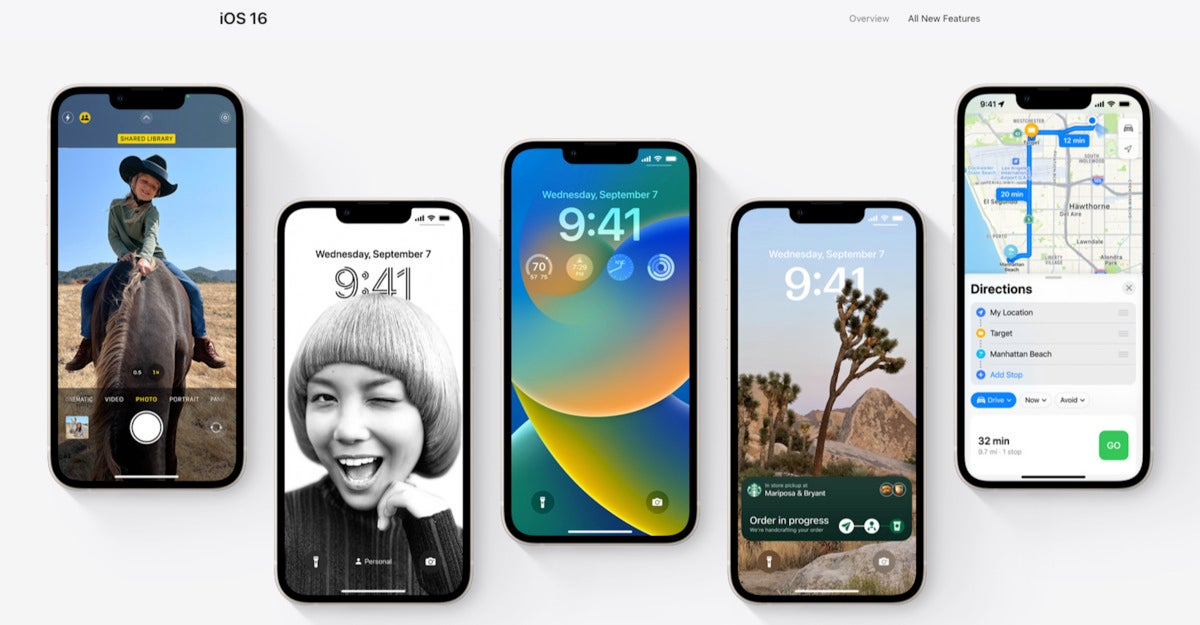
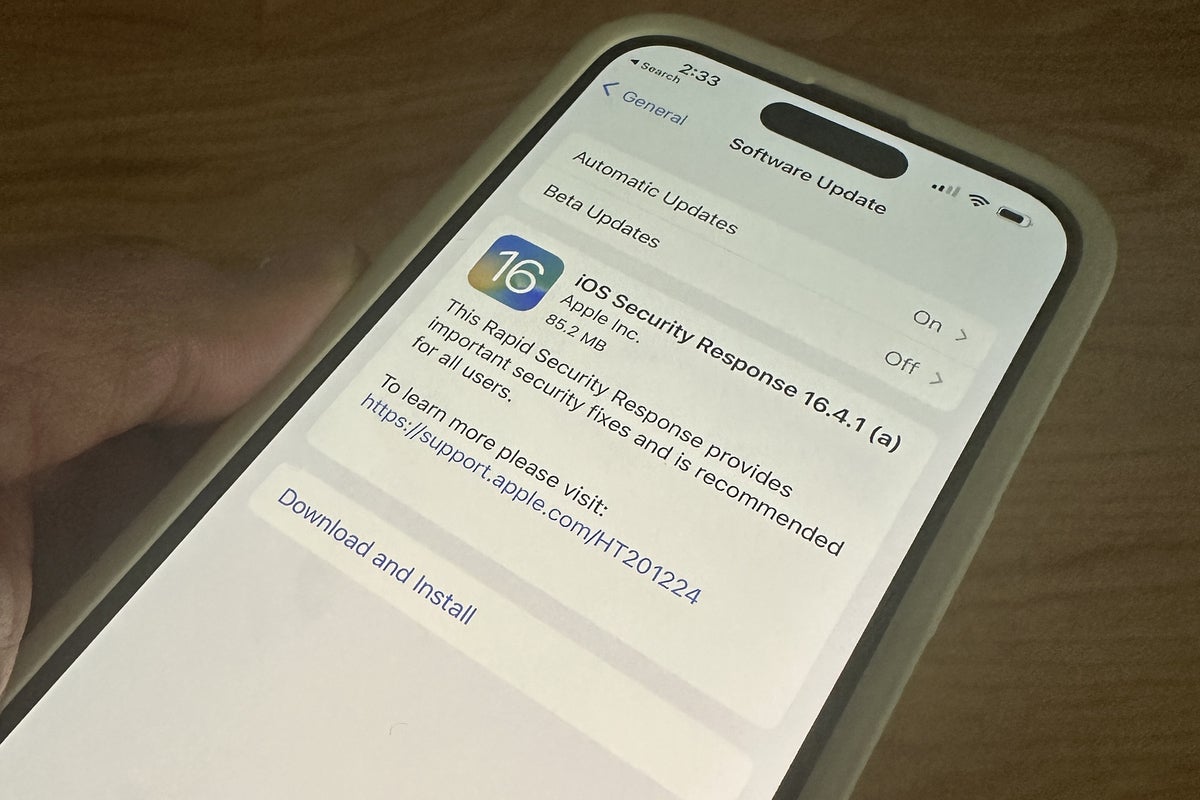
Computerworld
A new Apple feature called Rapid Security Response is aimed at bolstering security for iPhone, iPad and Mac users. Here's what it does and why you should use it.

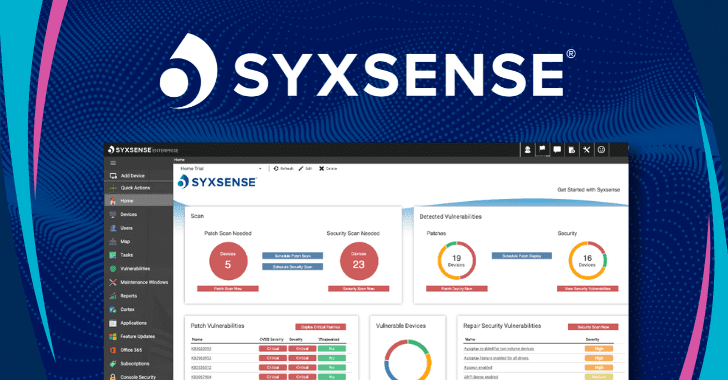
The Hacker News
As threats grow and attack surfaces get more complex, it's crucial for companies to have a clear view of their devices and security posture.


Computerworld
A glance at the Biden Administration’s recently updated National Cybersecurity Strategy document seems, at least on casual reading, to reflect some of the approaches to cybersecurity Apple already follows.

DarkReading
It's 10 p.m. Do you know what your children are playing? In the age of remote work, hackers are actively targeting kids, with implications for enterprises.

Computerworld
"Endpoint management and security has been the most popular security category by number of customers since August 2020," an Okta report explains


Infosecurity News
The recommendations stem from a red team assessment CISA conducted in 2022


Computerworld
Jamf Threat Labs has spotted a family of Mac malware, XMRig, that spreads through pirated versions of Final Cut Pro, Photoshop and Logic Pro X.


CSO
A report from identity and access management (IAM) vendor Okta says that zero trust and new types of security tooling are in increasingly widespread use, as businesses tackle a changing security landscape.


Computerworld
“In the past few years, many of our customers have seen a sharp increase in the number of Mac devices introduced to their environment,” the company says.


Infosecurity News
According to CTO Rob Zuber, the malware was not detected by the CircleCI antivirus program


Bleeping Computer
Hackers breached CircleCi in December after an engineer became infected with information-stealing malware that stole the employee's 2FA-backed SSO session, allowing access to the company's internal systems.


CyberSecurity Dive
An unauthorized actor, after stealing a valid SSO session, was able to exfiltrate data, including customer environment variables, tokens and keys.


Computerworld
Microsoft's extensive insights into Mac ransomware helped explain the nature of threats aimed at Apple's platform, but the post was subsequently removed.


Infosecurity News
Company information was stolen from third-party vendor Teqtivity and posted on a dark web forum
Loading more articles....