

SecurityWeek
University System of Georgia Says 800,000 Impacted by MOVEit Hack
University System of Georgia says Social Security numbers and bank account numbers were compromised in the May 2023 MOVEit hack.


SecurityWeek
University System of Georgia says Social Security numbers and bank account numbers were compromised in the May 2023 MOVEit hack.


Infosecurity News
CrushFTP is urging customers to download v11 of its file transfer platform, with attackers actively exploiting a vulnerability that allows them to download system files


The Hacker News
CL0P ransomware emerges as a major player in the cybercrime world! From "bed bug" beginnings to a global threat, this group's aggressive tactics are r


SecurityWeek
CISA and the FBI issue a secure-by-design alert on eliminating SQL injection vulnerabilities from software.


CyberSecurity Dive
Recorded Future observed an approximately threefold increase in actively exploited high-risk vulnerabilities in enterprise software and network infrastructure, such as VPNs.

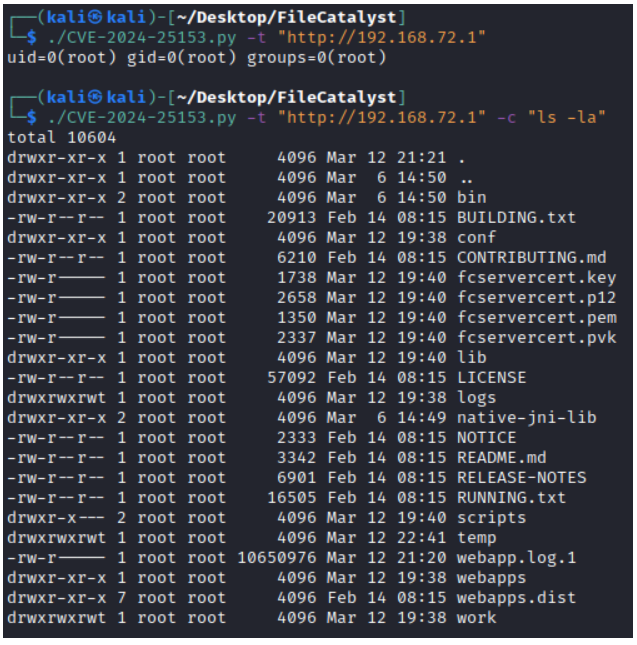
Security Affairs
Fortra addressed a critical remote code execution vulnerability impacting its FileCatalyst file transfer product.


The Hacker News
Fortra patches critical flaw in FileCatalyst transfer tool. Vulnerability allows remote code execution via directory traversal.


SecurityWeek
A critical directory traversal vulnerability in Fortra FileCatalyst Workflow could lead to remote code execution.


SC Magazine
First patched in August, the critical vulnerability enables unauthenticated web shell deployment.

Infosecurity News
Tracked as CVE-2024-23917, the flaw carries a CVSS rating of 9.8


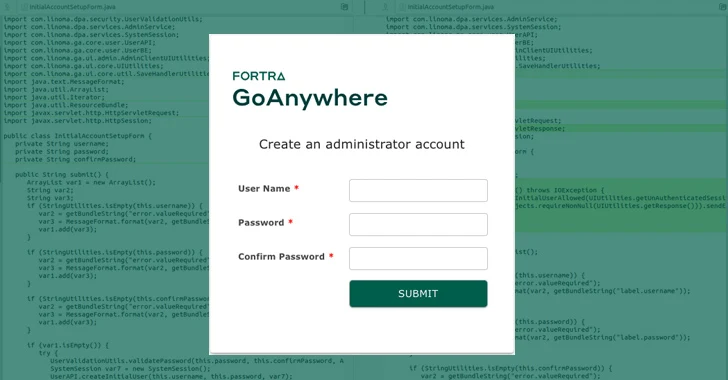
Latest Hacking News
A severe authentication bypass security flaw riddled the GoAnywhere MFT that could allow creating rogue admin accounts. While the developers patched the vulnerability already, researchers could still develop a working exploit for it, urging users


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


CyberSecurity Dive
Although patching lags, the number of hosts with publicly exposed and vulnerable admin interfaces are limited.


SC Magazine
Fortra recommends security teams patch critical CVE immediately. Security pros say hackers with even moderate skills can exploit bug.


DarkReading
PoC exploit code for flaw is publicly available, heightening breach risks for users of the managed file transfer technology.

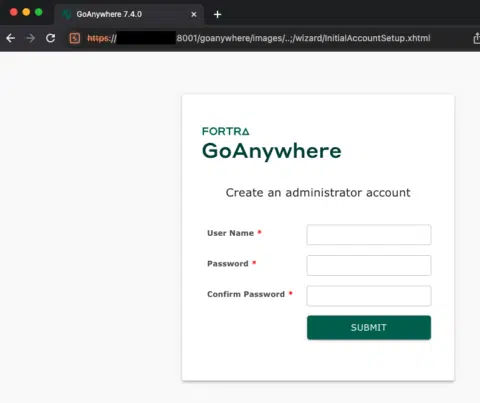
Security Affairs
Researchers released PoC exploit code for a recently disclosed critical authentication bypass flaw in Fortra's GoAnywhere MFT.


SecurityWeek
PoC code exploiting a critical Fortra GoAnywhere MFT vulnerability gets published one day after public disclosure.


Cyber Security News
Fortra-owned GoAnywhere MFT (Managed File Transfer) has been discovered with a new vulnerability that could allow an threat actor.


CyberSecurity Dive
File-transfer services, including GoAnywhere, were widely exploited by ransomware threat groups in 2023.


Infosecurity News
Researchers have released exploit code for a critical bug in managed file transfer software Fortra GoAnywhere

The Hacker News
GoAnywhere users, listen up! Critical bug (CVE-2024-0204) lets anyone become admin. Update to 7.4.1 immediately.


SC Magazine
With a PoC for exploiting the file sharing software already available, users are urged to patch immediately.


Bleeping Computer
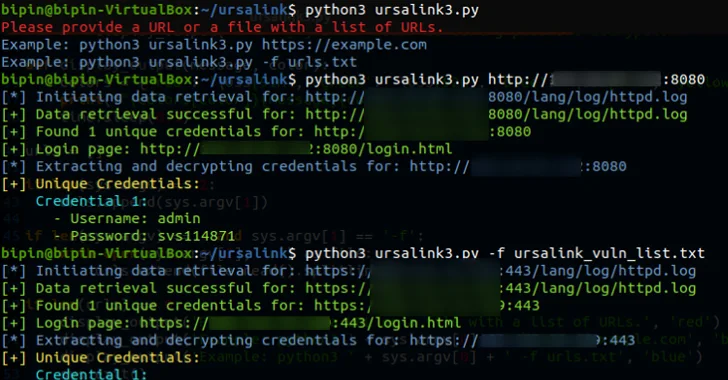
Exploit code is now available for a critical authentication bypass vulnerability in Fortra's GoAnywhere MFT (Managed File Transfer) software that allows attackers to create new admin users on unpatched instances via the administration portal.


Security Affairs
Fortra addressed a new authentication bypass vulnerability impacting GoAnywhere MFT (Managed File Transfer) product


Bleeping Computer
Fortra is warning of a new authentication bypass vulnerability impacting GoAnywhere MFT (Managed File Transfer) versions before 7.4.1 that allows an attacker to create a new admin user.

Security Affairs
Merck has resolved a dispute with insurers regarding a $1.4 billion claim arising from the NotPetya malware incident


Bleeping Computer
2023 was a big year for cybersecurity, with significant cyberattacks, data breaches, new threat groups emerging, and, of course, zero-day vulnerabilities.


Infosecurity News
The Qualys report also showed over 7000 vulnerabilities had proof-of-concept exploit code


Ars Technica
Easy-to-exploit flaw can give hackers passwords and cryptographic keys to vulnerable servers.


Bleeping Computer
A proof-of-concept exploit was publicly released for a critical remote code execution vulnerability in the CrushFTP enterprise suite, allowing unauthenticated attackers to access files on the server, execute code, and obtain plain-text passwords.


Cyber Security News
SysAid disclosed a zero-day which was affecting on-premises SysAid servers. The vulnerability was found to be a path traversal vulnerability.


Bleeping Computer
Threat actors are exploiting a zero-day vulnerability in the service management software SysAid to gain access to corporate servers for data theft and to deploy Clop ransomware.


Cyber Security News
Multiple vulnerabilities have been discovered in Titan MFT and Titan SFTP servers owned by South River Technologies.

The Hacker News
Milesight's industrial routers risk unauthorized web interface access, while Titan MFT and Titan SFTP servers face remote


The Hacker News
Ransomware attacks have evolved in Q3-2023, employing new techniques to bypass defenses. Discover the strategies ransomware groups have been adopting.


SecurityWeek
Progress Software confirms the SEC has launched its own investigation into costly ransomware zero-days in the MOVEit file transfer software.


SecurityWeek
Sony shares information on the impact of two recent unrelated hacker attacks carried out by known ransomware groups.


Bleeping Computer
Progress, the maker of the MOVEit Transfer file-sharing platform recently exploited in widespread data theft attacks, warned customers to patch a maximum severity vulnerability in its WS_FTP Server software.


Bleeping Computer
U.S. educational nonprofit National Student Clearinghouse has disclosed a data breach affecting 890 schools using its services across the United States.


Infosecurity News
The malware researchers' collective Vx-underground claimed that ALPHV/BlackCat was behind the attack against the casino giant


SecurityWeek
Nearly 1,000 organizations and 60 million individuals are impacted by the MOVEit hack, and the Cl0p ransomware gang is leaking stolen data.


DarkReading
It's not going anywhere: Easy-to-exploit bugs like MOVEit, leaks of stolen data, and rapid-fire escalation are keeping ransomware attacks as painful as ever.


The Hacker News
Citrix ShareFile under attack! Learn about ongoing exploitation of CVE-2023-24489 and how to defend your systems.


Bleeping Computer
CISA is warning that a critical Citrix ShareFile secure file transfer vulnerability tracked as CVE-2023-24489 is being targeted by unknown actors and has added the flaw to its catalog of known security flaws exploited in the wild.


SecurityWeek
Colorado’s health programs administrator says the personal information of 4 million individuals was compromised in the recent MOVEit hack.


Bleeping Computer
Ransomware gangs continue to prioritize targeting VMware ESXi servers, with almost every active ransomware gang creating custom Linux encryptors for this purpose.


Bleeping Computer
Serco Inc, the Americas division of multinational outsourcing company Serco Group, has disclosed a data breach after attackers stole the personal information of over 10,000 individuals from a third-party vendor's MoveIT managed file transfer (MFT) server.


SecurityWeek
Maximus Inc says that the personal information of 8 to 11 million individuals was stolen in the MOVEit cyberattack.


CyberSecurity Dive
Threat actors have been leveraging a known vulnerability in Netwrix Auditor to exfiltrate data from targeted entities since May.


SecurityWeek
Shell confirms that employee personal information has been stolen after the Cl0p ransomware group leaked data


DarkReading
The ransomware group shows an evolution of its tactics with MOVEit zero day — potentially ushering in a new normal when it comes to extortion supply chain cyberattacks, experts say.


CSO
For the research, Trustwave implemented a network of honeypots located in multiple countries including Russia, Ukraine, Poland, the UK, China, and the United States.


Bleeping Computer
Censys researchers have discovered hundreds of Internet-exposed devices on the networks of U.S. federal agencies that have to be secured according to a recently issued CISA Binding Operational Directive.


Security Affairs
Researchers at Censys have identified hundreds of devices deployed within federal networks that have internet-exposed management interfaces. Researchers at Censys have analyzed the attack surfaces of more than 50 Federal Civilian Executive Branch (FCEB) organizations and sub-organizations and discovered more than 13,000 distinct hosts across 100 autonomous systems. The experts focused on roughly 1,300 of […]


Bleeping Computer
The New York City Department of Education (NYC DOE) says hackers stole documents containing the sensitive personal information of up to 45,000 students from its MOVEit Transfer server.


DarkReading
The ransomware landscape is energized with the emergence of smaller groups and new tactics, while established gangs like LockBit see fewer victims.


Cyber Security News
Recently, the US govt offers a $10 million bounty on Info About Cl0p ransomware gang exploiting the MOVEit transfer application.


The Hacker News
🚨 Alert: Progress Software has disclosed a 3rd critical flaw in MOVEit Transfer app—an SQL injection—allowing unauthorized access.


Bleeping Computer
Progress warned MOVEit Transfer customers to restrict all HTTP access to their environments after info on a new SQL injection (SQLi) vulnerability was shared online today.


Bleeping Computer
The Clop ransomware gang has started extorting companies impacted by the MOVEit data theft attacks by listing them on a data leak site, a common extortion tactic used as a precursor for the public leaking of stolen data.


DataBreaches
Alexander Culafi reports: Illinois, Minnesota and Missouri state governments are among a growing list of organizations attacked via a critical flaw in Progress...


The Hacker News
LockBit ransomware scheme extorts $91 million from U.S. organizations in a series of devastating attacks since 2020.


Security Affairs
Security firm Horizon3 released proof-of-concept (PoC) exploit code for the remote code execution (RCE) flaw CVE-2023-34362 in the MOVEit Transfer MFT. MOVEit Transfer is a managed file transfer that is used by enterprises to securely transfer files using SFTP, SCP, and HTTP-based uploads. The vulnerability is a SQL injection vulnerability, it can be exploited by […]


Security Affairs
Intellihartx is notifying about 490,000 individuals that their personal information was compromised in the GoAnywhere zero-day attack in January. The Clop ransomware group has stolen stole personal and health information of 489,830 individuals as a result of a ransomware attack on the technology firm Intellihartx. The attack took place earlier this year, the attackers have […]


Bleeping Computer
Horizon3 security researchers have released proof-of-concept (PoC) exploit code for a remote code execution (RCE) bug in the MOVEit Transfer managed file transfer (MFT) solution abused by the Clop ransomware gang in data theft attacks.

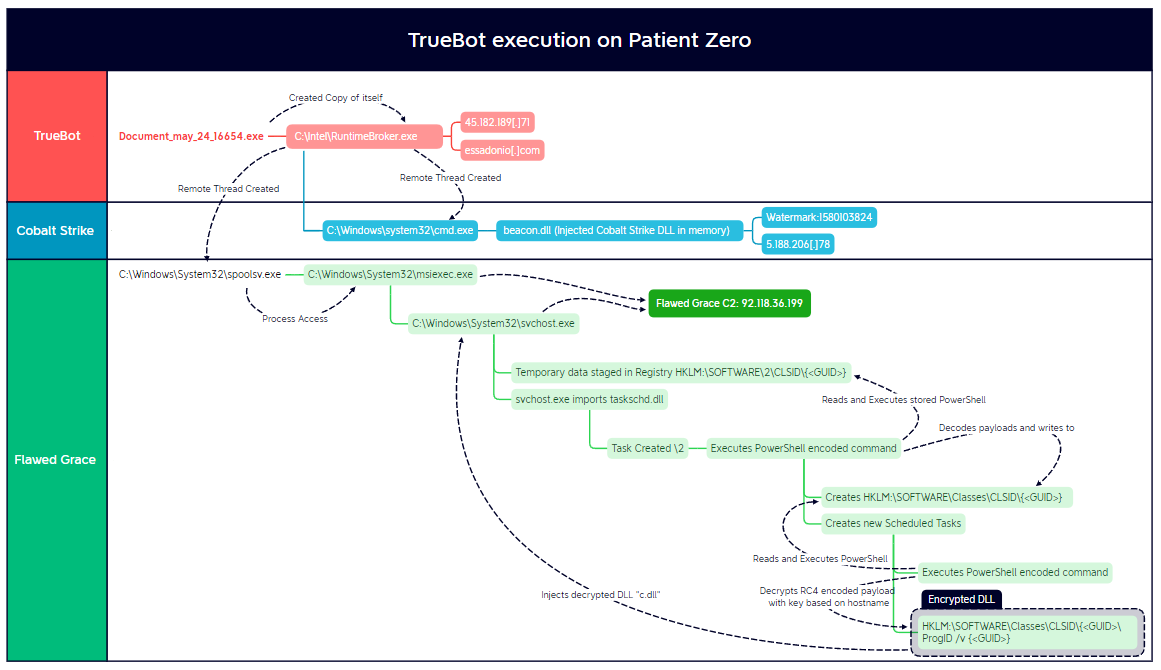
The DFIR Report
In this intrusion, dated May 2023, we observed Truebot being used to deploy Cobalt Strike and FlawedGrace (aka GraceWire & BARBWIRE) resulting in the exfiltration of data and the deployment … Read More


Bleeping Computer
The week was dominated by fallout over the MOVEit Transfer data-theft attacks, with the Clop ransomware gang confirming that they were behind them.


Bleeping Computer
Progress Software warned customers today of newly found critical SQL injection vulnerabilities in its MOVEit Transfer managed file transfer (MFT) solution that can let attackers steal information from customers' databases.


DarkReading
Over that time, the group carried multiple tests to see if the exploit worked and to identify potential victims. It was like "turning the doorknob" to check for access, a researcher says.


Security Affairs
Researchers discovered that the Clop ransomware gang was looking for a zero-day exploit in the MOVEit Transfer since 2021. Kroll security experts discovered that the Clop ransomware gang was looking for a zero-day exploit in the MOVEit Transfer since 2021. Kroll investigated the exploitation attempts for the MOVEit Transfer vulnerability and discovered that Clop threat […]


Bleeping Computer
The Clop ransomware gang has been looking for ways to exploit a now-patched zero-day in the MOVEit Transfer managed file transfer (MFT) solution since 2021, according to Kroll security experts.


Bleeping Computer
The Clop ransomware gang has been looking for ways to exploit a now-patched zero-day in the MOVEit Transfer managed file transfer (MFT) solution since 2021, according to Kroll security experts.


The Hacker News
New research reveals the Clop ransomware group has silently exploited a critical flaw in Progress Software's MOVEit Transfer since 2021.


Security Affairs
Clop ransomware group claims to have hacked hundreds of companies globally by exploiting MOVEit Transfer vulnerability. The Clop ransomware group may have compromised hundreds of companies worldwide by exploiting a vulnerability in MOVEit Transfer software. MOVEit Transfer is a managed file transfer that is used by enterprises to securely transfer files using SFTP, SCP, and […]


Bleeping Computer
The Clop ransomware gang has told BleepingComputer they are behind the MOVEit Transfer data-theft attacks, where a zero-day vulnerability was exploited to breach multiple companies' servers and steal data.


Infosecurity News
The vulnerability (CVE-2023-34362) can grant escalated privileges and unauthorized access


Bleeping Computer
Microsoft has linked the Clop ransomware gang to recent attacks exploiting a zero-day vulnerability in the MOVEit Transfer platform to steal data from organizations.

The Hacker News
Microsoft reveals critical flaw exploit in Progress Software MOVEit Transfer app, linking it to notorious threat actor Lace Tempest.


Bleeping Computer
CISA has added an actively exploited security bug in the Progress MOVEit Transfer managed file transfer (MFT) solution to its list of known exploited vulnerabilities, warning U.S. federal agencies to patch their systems by June 23.

Bleeping Computer
It has been a fairly quiet week regarding ransomware, with only a few reports released and no new significant attacks. However, we may have a rebrand in the making, and a ransomware operation is likely behind a new zero-day data-theft campaign, so we have some news to talk about.


The Hacker News
A critical flaw in Progress Software's MOVEit Transfer file transfer app is being exploited in the wild!


Bleeping Computer
Hackers are actively exploiting a zero-day vulnerability in the MOVEit Transfer file transfer software to steal data from organizations.


Bleeping Computer
This week's ransomware news has been dominated by a Royal ransomware attack on the City of Dallas that took down part of the IT infrastructure.


Infosecurity News
The attack took down essential services, including some 911 dispatch systems


Infosecurity News
Brightline said the breach was due to a zero-day flaw in Fortra GoAnywhere MFT


Bleeping Computer
Pediatric mental health provider Brightline is warning patients that it suffered a data breach impacting 783,606 people after a ransomware gang stole data using a zero-day vulnerability in its Fortra GoAnywhere MFT secure file-sharing platform.


The Hacker News
Microsoft has confirmed that hackers linked to Cl0p and LockBit ransomware families are actively exploiting PaperCut servers.

Bleeping Computer
Microsoft has attributed recent attacks on PaperCut servers to the Clop and LockBit ransomware operations, which used the vulnerabilities to steal corporate data.

Bleeping Computer
Microsoft has attributed recent attacks on PaperCut servers to the Clop and LockBit ransomware operations, which used the vulnerabilities to steal corporate data.


Bleeping Computer
A lot of news broke this week related to ransomware, with the discovery of LockBit testing macOS encryptors to an outage on NCR, causing massive headaches for restaurants.


The Hacker News
Fortra sheds light on zero-day remote code execution (RCE) vulnerability (CVE-2023-0669) in its GoAnywhere MFT tool, actively exploited by ransomware.


Bleeping Computer
Fortra has completed its investigation into the exploitation of CVE-2023-0669, a zero-day flaw in the GoAnywhere MFT solution that the Clop ransomware gang exploited to steal data from over a hundred companies.


Bleeping Computer
March 2023 was the most prolific month recorded by cybersecurity analysts in recent years, measuring 459 attacks, an increase of 91% from the previous month and 62% compared to March 2022.


DataBreaches
The Fortra/GoAnywhere incident also affected Tasmanian school children. Emily Woods reports: Hackers have released 16,000 Tasmanian education department...


Security Affairs
Australia’s gambling and entertainment giant Crown Resorts, disclosed a data breach caused by the exploitation of recently discovered GoAnywhere zero-day. Australian casino giant Crown Resorts disclosed a data breach after the attack of the Cl0p ransomware group. The group claims to have stolen sensitive data from over 130 organizations by exploiting a zero-day vulnerability (CVE-2023-0669) […]


Infosecurity News
The vulnerability has a CVSS score of 7.2 and was exploited against several companies in the US

DarkReading
After several weeks and more than 130 ransomware victims, GoAnywhere parent company Forta issues a statement.


Bleeping Computer
This week's news has been dominated by the Clop ransomware gang extorting companies whose GoAnywhere services were breached using a zero-day vulnerability.


Security Affairs
Clop ransomware gang added the City of Toronto to the list of its victims, it is another organization compromised by exploiting GoAnywhere zero-day. Clop ransomware gang added the City of Toronto to the list of victims published on its Tor leak site. The City was targeted as part of a campaign exploiting the recently disclosed zero-day vulnerability in […]


Security Affairs
Clop ransomware gang added City of Toronto to the list of its victims, it is another organization compromised by exploiting GoAnywhere zero-day. Clop ransomware gang added the City of Toronto to the list of victims published on its Tor leak site. The City was targeted as part of a campaign exploiting the recently disclosed zero-day vulnerability in the […]
Loading more articles....