

The Hacker News
How to Apply MITRE ATT&CK to Your Organization
Discover the power of MITRE ATT&CK framework in defending your organization against cyber threats. Build a robust security strategy.


The Hacker News
Discover the power of MITRE ATT&CK framework in defending your organization against cyber threats. Build a robust security strategy.

The Hacker News
Results Overview: 2022 MITRE ATT&CK Evaluation – Wizard Spider and Sandworm Edition


The Hacker News
Wazuh is an open source unified XDR and SIEM platform. Wazuh comes with the MITRE ATT&CK module out-of-the-box and threat detection rules.


SecurityWeek
MITRE announces the release of ATT&CK v14, which brings enhancements related to detections, ICS, and mobile.


DarkReading
Enables enterprises to operationalize MITRE ATT&CK and build a multi-layered, threat-informed defense to eliminate gaps based on organizational risk and priorities.


The Hacker News
How to Interpret the 2023 MITRE ATT&CK Evaluation Results | Read more hacking news on The Hacker News cybersecurity news website and learn how to protect against cyberattacks and software vulnerabilities.


Bleeping Computer
The U.S. Cybersecurity & Infrastructure Security Agency (CISA) has released 'Decider,' an open-source tool that helps defenders and security analysts quickly generate MITRE ATT&CK mapping reports.


DarkReading
The Decider tool is designed to make the ATT&CK framework more accessible and usable for security analysts of every level, with an intuitive interface and simplified language.


Trend Micro
In our study, we relied on the tactics, techniques, and procedures of MITRE ATT&CK to define the malware capabilities and characteristics of IoT Linux malware. We describe our findings and how IoT malware has been evolving.


DarkReading
Red Canary, a leader in Managed Detection and Response (MDR), is one of 15 providers that participated in the first-ever MITRE Engenuity™ ATT&CK® Evaluations for Managed Services.


Trend Micro
Trend Micro Vision One achieved a protection score of 100% in this year’s evaluation, proving once again that it is an invaluable tool that provides higher confidence detections for security operations teams.


DarkReading
Organizations are largely deluded about their own security postures, according to an analysis, with the average SIEM failing to detect a whopping 76% of attacker TTPs.


Cyber Security News
In the ever-evolving landscape of cybersecurity, the need for advanced tools to simulate and test incident response is critical.

.webp)
Cyber Security News
Independent tests are a vital resource as cybersecurity leaders and their teams evaluate vendors’ abilities to guard against increasingly.


CSO
Expel MDR for Kubernetes addresses three core layers of Kubernetes applications: configuration, control panel, and run-time security.


DarkReading
A cheat sheet for all of the most common techniques hackers use, and general principles for stopping them.


CSO
The OSC&R Framework aims to help security professionals better understand and measure software supply chain risk.

DarkReading
EMB3D, like ATT&CK and CWE, seeks to provide a common understanding of cyber-threats to embedded devices and of the security mechanisms for addressing them.

Cyber Security News
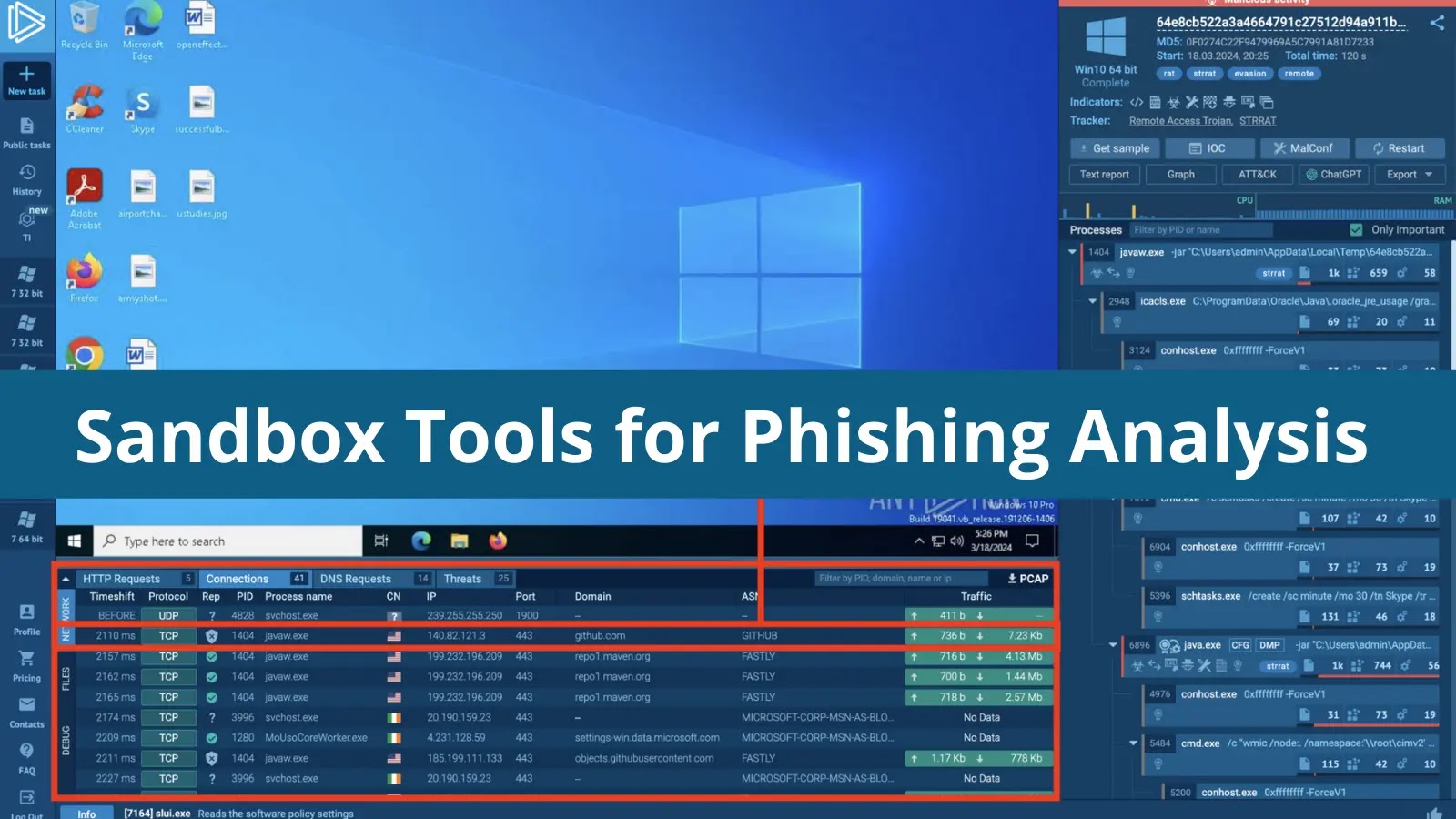
Sandbox Tools for Phishing Analysis 2024: 1. Interactivity 2. RSPAMD Integration 3. Suricata Rule Engine 4. MITRE ATT&CK 5.Matrix 6. Phishing Tag.


Trend Micro
In part two of our three-part series, we continue to analyze vulnerabilities using MITRE ATT&CK. We also look into the sectors affected and their risk levels.


Trend Micro
In this blog series our team examined various ICS vulnerabilities using the MITRE Adversarial Tactics, Techniques, and Common Knowledge (ATT&CK) for ICS.


Trend Micro
This year, the MITRE Engenuity ATT&CK evaluation tested cybersecurity vendors against simulated attack scenarios mimicking the adversary group “Turla.” Learn about Trend Micro's 100% successful protection performance.


DarkReading
The irony is lost on few, as a Chinese threat actor used eight MITRE techniques to breach MITRE itself — including exploiting the Ivanti bugs that attackers have been swarming on for months.


The Hacker News
A critical flaw in the hugely popular LiteSpeed Cache plugin for WordPress is being exploited in the wild to create rogue admin accounts, granting att


CyberScoop
A new report evaluates an end-to-end cyberattack on industrial control systems and offers solutions for threat detection capabilities.


Trend Micro
In this blog entry, we shine a spotlight on some of the most critical cybersecurity concerns of 2022, which we discuss in full in our annual cybersecurity report, “Rethinking Tactics: 2022 Annual Security Report.”


Infosecurity News
The average malware variant now utilizes 11 TTPs

CSO
Malware authors and cybercriminal groups are making sophisticated techniques practical for threat actors to use more widely, changing threat models.


Trend Micro
We examine the campaigns of the cyberespionage group known as Turla over the years, with a special focus on the key MITRE techniques and the corresponding IDs associated with the threat actor group.


CSO
Adversaries step up attacks that disable enterprise defenses.


The Hacker News
Think you're protected from cyber attacks? Hackers are always finding new ways to exploit vulnerabilities. Learn to think like a hacker and stay ahead


DataBreaches
The versatility of the latest malware is demonstrated by the fact that a third of the total sample analyzed by Picus Labs is capable of exhibiting more than...

SecurityWeek
XDR architecture must be broad and deep so that organizations can get the most value out of their existing best-of-breed security solutions, including their free, open-source tools.


SecurityWeek
A malware tactic dubbed ‘hunter-killer’ is growing and may become the standard approach for advanced attacks.


Infosecurity News
The Qualys report also showed over 7000 vulnerabilities had proof-of-concept exploit code


Bleeping Computer
Wazuh is a free and open source security platform that provides unified SIEM and XDR protection. It protects workloads across on-premises, virtualized, containerized, and cloud-based environments. Wazuh is one of the fastest growing open source security solutions, with over 10 million downloads per year.


Bleeping Computer
The U.S. Cybersecurity & Infrastructure Security Agency (CISA) has released a new open-source incident response tool that helps detect signs of malicious activity in Microsoft cloud environments.

The Hacker News
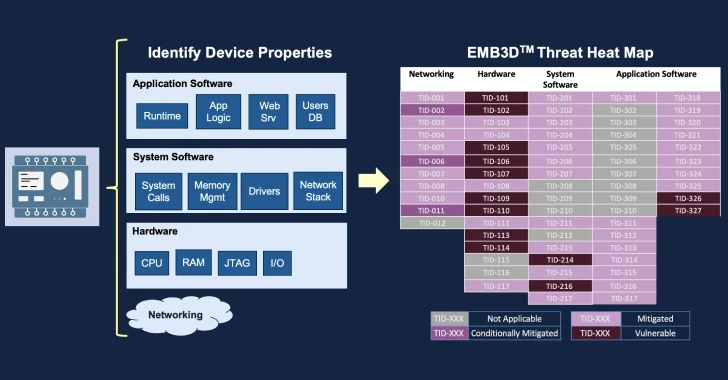
MITREcorp has launched EMB3D, a new threat-modeling framework for embedded devices used in critical infrastructure.


Bleeping Computer
The FBI and CISA revealed in a joint advisory published today that an unnamed Iranian-backed threat group hacked a Federal Civilian Executive Branch (FCEB) organization to deploy XMRig cryptomining malware.


SecurityWeek
CISA and the NSA are urging network defenders and software developers to address the top ten cybersecurity misconfigurations.


SecurityWeek
US and Australian government agencies warn organizations of the Play ransomware group’s double-extortion tactics.


CyberScoop
Despite growing cyberattacks on satellite networks, efforts to protect communication systems in space remain nascent.


DarkReading
MITRE's hackers made use of at least five different Web shells and backdoors as part of their attack chain.


Infosecurity News
Picus Security sees huge uptick in malware designed to detect and disrupt security tooling


ThreatPost
Expect many more zero-day exploits in 2022, and cyberattacks using them being launched at a significantly higher rate, warns Aamir Lakhani, researcher at FortiGuard Labs.


DataBreaches
Report: 202309291200 Executive Summary Active since 2015 and among the most prevalent and persistent strains of malware families since 2018, LokiBot has...


DataBreaches
November 1, 2023 TLP:CLEAR Report: 202311011500 Executive Summary A recent attack on a U.S.-based medical facility in October 2023 highlights the potential...


DataBreaches
Alert (AA22-294A) #StopRansomware: Daixin Team Download the PDF version of this report: pdf, 591 KB Technical Details Note:...


Bleeping Computer
Last year, a U.S. federal agency's Microsoft Internet Information Services (IIS) web server was hacked by exploiting a critical .NET deserialization vulnerability in the Progress Telerik UI for ASP.NET AJAX component.


Bleeping Computer
The National Security Agency (NSA) and the Cybersecurity and Infrastructure Security Agency (CISA) revealed today the top ten most common cybersecurity misconfigurations discovered by their red and blue teams in the networks of large organizations.


DarkReading
As the second Kaminsky Fellow, Dr. Andrews will study the use of threat intelligence to track campaigns against the human rights community.


The Hacker News
Wazuh open-source platform combines XDR & SIEM capabilities to protect businesses from evolving threats.

Cyber Security News
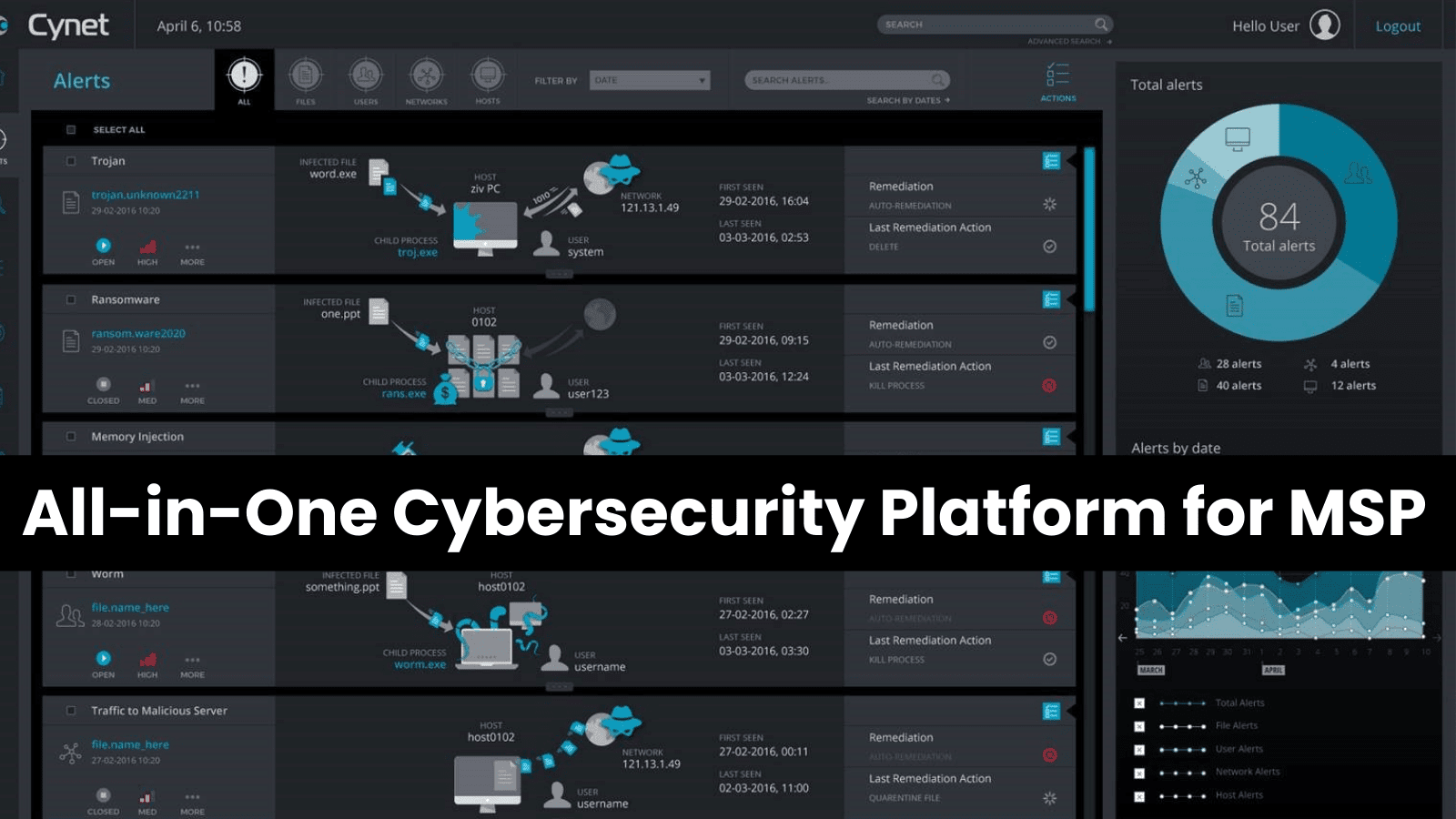
Managed service providers (MSPs) are on the front lines of soaring demand for cybersecurity services as cyberattacks increase in volume and sophistication.

SecurityWeek
Cybersecurity training firm Cybrary has secured $25 million in a Series C funding round, and announced that Mandiant CEO Kevin Mandia will join its board of directors.


CyberScoop
New report offers insights on CHERNOVITE and the PIPEDREAM malware that threatens industrial control systems.


Infosecurity News
The Cyber Threat Intelligence Summit discussed how automation and generative AI could help CTI practitioners tackle the overload of data they have to process

SecurityWeek
Analyzing the attack goals of adversaries is important to be able to better align defenses against the speed of changing attack techniques.


The Hacker News
Learn how SecurityHQ's innovative SHQ Response Platform is revolutionizing risk management, with insights from Deodatta Wandhekar.


DarkReading
ThreatConnect announced today the release of ThreatConnect Platform v7.0, the industry's first threat intelligence platform designed specifically for TI Ops.

SecurityWeek
MITRE announced the public availability of the EMB3D threat model for embedded devices used in critical infrastructure.


Security Affairs
Matanbuchus malware-as-a-service (Maas) has been observed spreading through phishing campaigns, dropping Cobalt Strike beacons. Threat intelligence firm Cyble has observed a malware-as-a-service (Maas), named Matanbuchus, involved in malspam attacks dropping Cobalt Strike beacons. Matanbuchus is a malware loader that first appeared on the threat landscape in February 2021, when it was offered for rent on Russian-speaking […]


DarkReading
Training and crisis scenarios find that defenders take months, not days, to learn about the latest attack techniques, exposing organizations to risk.


DarkReading
Cybereason announces additional funding led by Softbank Corp.


Cyber Security News
Microsoft has taken another step towards security which has revolutionized the way security professionals use Microsoft 365 Defender across devices as well as cloud applications.


DataBreaches
November 6, 2023 TLP:CLEAR Report: 202311061700 Executive Summary A relatively new ransomware group and strain known as BlackSuit, with significant...

SecurityWeek
MITRE and partners unveil EMB3D, a new threat model designed for critical infrastructure embedded devices.


SecurityWeek
MITRE and CISA introduce Caldera for OT, a new extension to help security teams emulate attacks targeting operational technology systems.


Cyber Security News
The Computer Emergency Response Team of Ukraine (CERT-UA) warns of massive cyberattacks targeting telecommunication operators. According to the report, CERT-UA received information from a participant in the information exchange on the mass mailing of e-mails among media organizations of Ukraine including radio stations, newspapers, news agencies, etc titled "LIST of links to interactive maps".


Infosecurity News
MITRE’s EMB3D provides industrial manufacturers with a shared understanding to mitigate cyber threats


Infosecurity News
Allied security agencies reveal figure in new advisory


Trend Micro
Explore the world of zero day threats and gain valuable insight into the importance of proactive detection and remediation.


Trend Micro
This blog entry explores the effectiveness of ChatGPT's safety measures, the potential for AI technologies to be misused by criminal actors, and the limitations of current AI models.


Trend Micro
This week, read about Trend Micro’s predictions for security in the coming year. Also, learn about the Biden administration’s latest initiatives for curtailing attacks on the transport infrastructure.

DarkReading
Eighteen companies, led by Amazon and Splunk, announced the OCSF framework to provide a standard way for sharing threat detection telemetry among different monitoring tools and applications.


Bleeping Computer
Microsoft says its cloud-native SIEM (Security Information and Event Management) platform now allows to detect potential ransomware activity using the Fusion machine learning model.


Infosecurity News
Google Cloud figures also point to misconfiguration


Infosecurity News
Acronis EDR is integrated into its Cyber Protect Cloud solution along with backup and data recovery functionalities


CSO
New product and service announcements from Wiz, Palo Alto Networks, Sophos, SecureAuth, Kasada, Lacework, Noname Security, and more.


DarkReading
ThreatConnect, maker of leading threat intelligence operations (TI Ops) and risk quantification solutions, announced today the company's accelerated growth through 2022 and market leading position heading into 2023.


Security Affairs
North Korea-linked threat actor UNC4034 is spreading tainted versions of the PuTTY SSH and Telnet client. In July 2022, Mandiant identified a novel spear phish methodology that was employed by North Korea-linked threat actor UNC4034. The attackers are spreading tainted versions of the PuTTY SSH and Telnet client. The attack chain starts with a fake […]


Cyber Security News
Cyber threat actors that were responsible for over 1000 recorded conti ransomware attacks remain active still. Tricot and Cobalt Strike are the two most significant attack vectors.

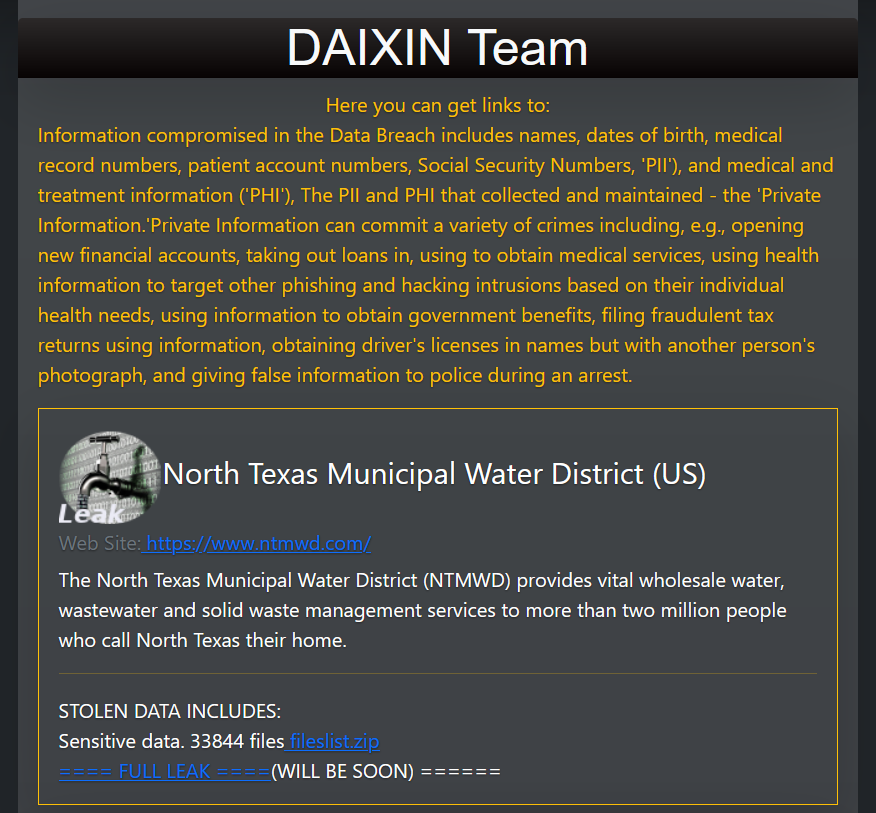
Security Affairs
The Daixin Team group claims to have hacked the North Texas Municipal Water District (US) and threatened to leak the stolen data.


CSO
Akamai’s latest study finds organizations are not prepared for API-based attacks as most report scant controls.


Infosecurity News
Non-profit MITRE says a sophisticated state group breached its network via two chained Ivanti zero-days


Infosecurity News
The open source tool will enable cyber teams to consistently test and boost the defenses of ICS environments


Security Affairs
A malware campaign tracked as GO#WEBBFUSCATOR used an image taken from NASA’s James Webb Space Telescope (JWST) as a lure. Securonix Threat researchers uncovered a persistent Golang-based malware campaign tracked as GO#WEBBFUSCATOR that leveraged the deep field image taken from the James Webb telescope. The phishing emails contain a Microsoft Office attachment that includes an external reference […]


Infosecurity News
Researchers detail the DLL side-loading technique used to deploy malware that facilitates credential theft and lateral movement


Cyber Security News
Cyber Attack Simulation Tools: 1. BreachLock 2. Foreseeti 3. Infection Monkey 4. AttackIQ 5. XM Cyber 6. Cymulate 7. Randori 8. CALDERA


CSO
CISA advisory includes indicators of compromise and TTPs that can be used for threat hunting.


DarkReading
Goodbye, Phosphorus! Hello, Mint Sandstorm. Microsoft adopts two-word monikers for threat groups, but do we really need more?


CyberSecurity Dive
Exploits of Ivanti VPN products have hit roughly 1,700 organizations. To Mitre, guidance from the vendor and government fell short.


SecurityWeek
New CISA guidance details cyber threats and risks to healthcare and public health organizations and recommends mitigations.


DarkReading
Product enhancements to offer full IT and OT threat intelligence services for OPSWAT customers.


Security Affairs
Qakbot malware operators are using the Windows Calculator to side-load the malicious payload on target systems. Security expert ProxyLife and Cyble researchers recently uncovered a Qakbot campaign that was leveraging the Windows 7 Calculator app for DLL side-loading attacks. Dynamic-link library (DLL) side-loading is an attack method that takes advantage of how Microsoft Windows applications handle DLL […]


Bleeping Computer
U.S. and international cybersecurity authorities said in a joint LockBit ransomware advisory that the gang successfully extorted roughly $91 million following approximately 1,700 attacks against U.S. organizations since 2020.


Cyber Security News
Threat actors exploited an unauthenticated, remote code execution vulnerability to drop these webshells on the environment.


SecurityWeek
FBI and CISA are warning critical infrastructure organizations of ongoing Snatch ransomware attacks, which also involve data exfiltration.


SecurityWeek
MITRE R&D network hacked in early January by a state-sponsored threat group that exploited an Ivanti zero-day vulnerability.


Bleeping Computer
Red Canary intelligence analysts have discovered a new Windows malware with worm capabilities that spreads using external USB drives.

The Hacker News
Unlock the power of Identity Threat Detection & Response (ITDR) to defend against sophisticated SaaS threats.
Loading more articles....